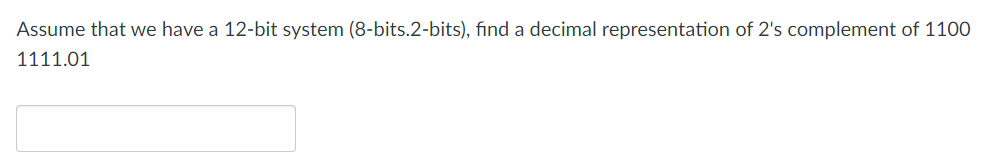
Assume that we have a 12-bit system (8-bits.2-bits), find a decimal representation of 2's complement of 110 1111.01
Q: What are the most effective cloud-based data backup procedures?
A: Let's discuss most effective cloud based data backup procedures.
Q: A convenient method or instrument for providing computer-generated charts, diagrams, drawings, and…
A: Answer: Computer graphics deals with the generation of images using computers. Today, computer…
Q: Give examples of the three most popular file management techniques
A: In the below step we have discussed the 4 most popular file management techniques. You can pick any…
Q: Internet users get two unique types of services through programmes. Following is a list of the major…
A: Internet users get two unique types of services through programmes. Following is a list of the major…
Q: EXPLAIN. DESCRIBE OTOP AND YEFFP.
A: The One Town One Product (OTOP) – is a priority program of President Gloria Macapagal – Arroyo to…
Q: What substitutions are there for message authentication?
A: There are many techniques that can be alternative for message based authentication , Message based…
Q: (a) Write an 8085 assembly language program to solve the following equation. X=(PxQ) + (R x S)…
A: Below I have provided assambly language for the given question. Also, I have attached a screenshot…
Q: Write a getMatching() method for the MyLinkedList class. The method receives a linked list as…
A: Linked List which refers to the part of the collection framework and it is present in utility…
Q: Compile and present a list of the most urgent security problems specific to cloud computing, as well…
A: Interpretation: Here, the primary security flaws specific to cloud computing are described, along…
Q: The concept of authenticating a user with two distinct elements is novel to me. What impact does…
A: Before granting access to secured networks and systems, a registered user or process must first have…
Q: Describe TCP/function. IP's
A: TCP/IP is discussed in the below step
Q: Do you have any knowledge of the most popular host software firewall programmes? Explain
A: Given: On a single machine, a host software firewall filters both incoming and outgoing traffic. It…
Q: While you're at it, how about bringing up the idea of "Reuse" and the "host-target" phenomenon?
A: Two perspectives on reuse have been considered: reuse without modification and reuse with…
Q: Internet is used for research purposes. Mafiaboy's activities How did he get access to the websites…
A: answer is
Q: Clarifying firewalls' function in network security and protection is crucial. Don't forget to make…
A: answer: The significance of a firewall First, let us consider why we need a firewall. I have a pc…
Q: Assess the risks and benefits of cloud security from a security standpoint. Transitioning from…
A: Cloud brings advantages such as flexibility and scalability cloud computing security risks are seen…
Q: A. test plan B. 【】 Set the correct order of the process of testing D. C. test requirement E. test…
A: The above question that is the correct order of testing is answered below step
Q: Can the kernel components of a standard operating system be summed up in a single sentence?
A: The main processing component of an operating system is called the kernel (OS) for a computer. It is…
Q: Will you, as an IT manager, assign new systems analysts maintenance tasks? Why do you feel that way?
A: Answer: Yes, as an IT manager, assign new systems analysts maintenance tasks because the Systems…
Q: Firewalls, which are essential to network protection, are strongly reliant on network security and…
A: A firewall is software or firmware which are used that in order to prevents the unauthorized access…
Q: How does one compress an encrypted file system on a computer?
A: A computer's encrypted file system must be determined here: Microsoft Windows multiple kinds of OS…
Q: Please explain the benefits of employing user-defined functions as opposed to predefined ones.
A: Definition: 1. Users develop user-defined functionalities in accordance with their needs. 2. In…
Q: What options are there in computer science for maintaining data integrity?
A: Introduction: The data developer is in charge of including components that raise the reliability and…
Q: Write a java program to create a file called password.txt
A: Java Program: // importing Fileimport java.io.File; class Files{ public static void main(String[]…
Q: could someone show me a simple chen style erd? please dont make it about money.
A: Developed by computer scientist Peter Chen, the Chen ERD notation is considered a more detailed way…
Q: How and to what extent is physical security distinct from other forms of security? We must be aware…
A: Physical security is the protection of personnel, hardware, software, networks, and data from…
Q: "An important question: what is the magic behind ML, and the answer is mathematics." What Math…
A: Answer: It is widely used in almost every area of the real world, from Google Assistant to…
Q: methods for hijacking a session. Exist possible countermeasures to this onslaught, and if so, what…
A: Session Hijacking Session hijacking is basically a web attack that is carried out by destroying…
Q: e some strategies for session theft. Can anyt stop this from occurring?
A: Introduction: Session hijacking is exactly what the name implies. An attacker can hijack a user's…
Q: Give examples of the three most popular file management techniques.
A: Provide examples for the three primary file management techniques. Ordinary files, also known as…
Q: Consider the potential and security risks of cloud computing. When examining the hazards and risks…
A: Let's discuss some of the risk and threats of Cloud computing , when you are thinking of shifting to…
Q: In Python. Ask user to enter two float numbers. Using an infinite loop, ask the user whether they…
A:
Q: Do you feel that persons who are physically or mentally handicapped may benefit in some way from…
A: The TCP/IP protocol stack is used by the worldwide network of linked computer networks known as the…
Q: Consider a two-link network where Host A is connected to the router by a 1 Mbps link with 10 ms…
A: We need to find the transmission delay of the packet from host A to router.
Q: What is the operation of the intrusion detection system?
A: Answer: Intrusion detection system An intrusion detection system (IDS) is a system that monitors…
Q: The following code is supposed to compute the sum S = when M = 100: I need a python code for this…
A: Here is the python code. See below step for code.
Q: A programme slice: what does that mean? discussion of programme segmentation, both static and…
A: Programme Segmentation: Computer memory is often composed of many segments, which are specialized…
Q: provide a list of all the components after describing each component of a typical operating system…
A: It's an OS's core: The Kernel is an OS's core PC software. Since the OS has influence over the…
Q: Which regions and zones can assist in enhancing the robustness, performance, availability, and…
A: Please find the answer below :
Q: What is wrong with my code, why is my if statement not working Public Class Form1 Function…
A: The error is because the usage of the Mod operator is wrong. Mod operator required two operands for…
Q: What are the advantages and disadvantages of using a service like Gmail for email? improving and…
A: Introduction In this question, we are asked What are the advantages and disadvantages of using a…
Q: How may interface designers do a hierarchical task analysis? Describe the seven-step procedure.
A: Analysis of Hierarchical Tasks By taking a formal objective approach to the way users define task…
Q: How can I get access to Application Software? The most effective technique to convey your point is…
A: Application software assists with various functions, including resource coordination, data…
Q: Projectised structure - Briefly describe at least 3 pros and 3 cons of this setup.
A: The solution to the given question is: PROJECTISED STRUCTURE THIS TYPE OF STRUCTUE IN AN…
Q: What advantages do both vertical and horizontal partitioning offer?
A: A horizontal division: Each division in this technique serves as a distinct data store, but they all…
Q: The process model for RAD Software is rapid development of software applications. Application…
A: Concept The life cycle of software development is a technique that outlines a series of procedures…
Q: What distinguishes vertical and horizontal partitions?
A:
Q: There are several methods for hijacking a session. Exist possible countermeasures they? to this…
A: Please find the answer below :
Q: What are the most effective cloud-based data backup procedures?
A: You obviously need backups, if you ask the question. But it is advisable to create duplicates of…
Q: Give specific instances of session hijacking techniques. Such attacks require a robust defence.
A: Start: Taking possession of a vehicle you don't own, such an aero plane, ship, or bus, is called…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- A(n) __________ is an integer stored in double the normal number of bit positions.A(n) _____ operation transforms a 0 bit value to 1 and a 1 bit value to 0.Data represented in ________ is transmitted accurately between computer equipment from different manufacturers if each computer’s CPU represents real numbers by using an IEEE standard notation.
- Assume that we have a 12-bit system (8-bits.2-bits), find a decimal representation of 2's complement of 1100 1111.01Assume that we have a 13-bit system (8-bits.3-bits) system, find a decimal representation of 2's complement of 1101 1010.001Assume we have 16-bit (2 bytes) 2's complement system with a 2-bit fractional. Find a decimal representation of 2's complements number 1111 1111 1110 0111.11 \
- Assume we have an 8-bit (1 byte) 2's complement system. Find a decimal representation of 2's complements binary number 1101 0011Assume we have 8 bit (1 byte) 2's complement system with a 3-bit fractional. Find a decimal representation of 2's complements binary number 1010 0111.101Assume we have 16-bit (2 bytes) 2's complement system with a 2-bit fractional. Find a decimal representation of 2's complements number 1111 1111 1110 0111.11 It will display your answer with commas every third digit No hand written and fast answer with explanation
- Find the two's complement representations, using bit strings of length six, of the following integers. a)22 b)31 c) -7 d) -19Show the binary representation of the following decimal numbers in (i) 2’s complement, (ii) 1’s complement, using 20 bits: a) 133,089 b) -138,989 c) - 7Obtain the 1’s and 2’s complements of the following binary numbers: 88 (a) 10010000 1’s comp.= 2’s comp.= 2.(e) 10100101 1’s comp.= 2’s comp.=

