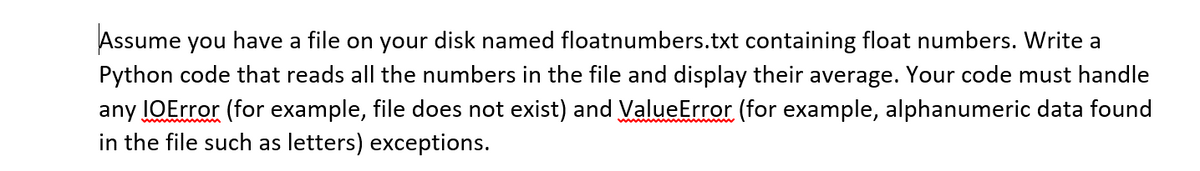
Assume you have a file on your disk named floatnumbers.txt containing float numbers. Write a Python code that reads all the numbers in the file and display their average. Your code must handle any IOError (for example, file does not exist) and ValueError (for example, alphanumeric data found in the file such as letters) exceptions.
Q: Just need SQLs * Single tables Display the information (name, position, salary) about a person…
A: As per the bartleby guide lines we need to answer only three subquestion so i am answering first 3…
Q: What is the distinction between a firewall and an intrusion detection system (IDS)? Contrast…
A: Intro Both firewalls and intrusion detection systems significantly impact many users' security…
Q: 8. Let W(x, y) mean that student x has visited website y, where the domain for x consists of all…
A: solution for the above question is solved in below step 2:- answer for a) a website present which…
Q: Consider a full-duplex 256 Kbps satellite link with a 240 millisecond end-to-end delay. The data…
A: Given:
Q: Explain in fully the benefits and drawbacks of machine learning in decision support systems.
A: Intro Machine learning (ML) Machine learning is the study of computer algorithms that improve…
Q: The following actions must be taken by an attacker to ensure the success of a sniffer attack. If an…
A: Intro The main question is, how may an attacker take use of the sniffer system if they have network…
Q: How has routing and switching technology progressed over time?
A: The advancement of routing technologies through time: Early routing systems were primarily…
Q: Describe a Turing machine which decides the language {0 i1 j | i 2 = j}
A: Turing Machine: Alan Turing designed the Turing Device in 1936, which is used to accept Nonlinear…
Q: Is or can any of the business be put up as a SaaS?
A: Disclaimer: “Since you have asked multiple questions, we will solve the first question for you. If…
Q: xplain what a TCP connection is. Is the concept of a TCP connection incompatible with the fact that…
A: TCP (Transmission Control Protocol): This is a connection oriented protocol and is used at the…
Q: Inserting and deleting nodes from a heap takes?
A: Heap is a data structure that is a complete binary tree and it satisfies the properties of heap. All…
Q: (BP) = 1000H , (SP) = 1020H , (SI) = 0400H , %3D %3D
A: The answer is
Q: MOV M,C STA 2000H IDAY D
A: In 8085 Instruction set, this instruction MOV M, r will copy 8-bit value from the register r to the…
Q: Discuss how selecting the pivot and the cut-off value affects the quicksort's performance.
A: Pivot The pivot value is the value that is chosen to partition the array into sub-arrays. Now,…
Q: lp with its development?
A: Expert System is an intuitive and trustworthy PC based dynamic system that addresses confounded…
Q: What is the link between telecommunications and data communications? What happens if one of them is…
A: Introduction: Telecommunications are the electrical method of transmitting information across long…
Q: For this question, you will be required to use the binary search to find the root of some function…
A: The objective is to write the code using binary search to find the root of some function on the…
Q: Consider the following function: int enigma(NodeInt32* node) { if(node == NULL) return 0; else…
A: Recursive Function In programming, a recursive function is a function that executes itself. Simple…
Q: Linear Data Structures Given a list of X objects, you want to create a program that performs the…
A: since we cannot change size of list we cannot use remove, pop, delete in list. Also we can not…
Q: How many license plates of the format LDDLDD are there where L is a letter and D is a digit. How…
A: The Answer is in Below Steps
Q: discuss the difference between relational database and NoSQL and in each case, give an example of…
A: SQL stands for Structured Query Language that is manage as the homogenized language as the…
Q: 1. Explain the meanings of the words "Software Requirements and Specifications" and "Software…
A: Intro: 1. Explain the meanings of the words "Software Requirements and Specifications" and "Software…
Q: Describe the use of technology in a new business.
A: Technology can be helped as a powerful competitive strategy, a firm's product that is completely new…
Q: The usage of indices speeds up query processing, but it's typically a bad idea to create one for…
A: Introduction: Indexing in a Database Management System (DBMS): Indexing is a time-saving way of…
Q: What measures are utilized to protect business systems against threats?
A: Following are the controls that are used to mitigate threats to enterprise system: 1. Phishing is…
Q: Please provide an example of how to utilise Goal Seek in Excel.
A: Intro Excel 2016 for Mac users may do what-if analyses by selecting the Data tab and then clicking…
Q: Which of the following interfaces or classes would be the most appropriate structure to store a…
A: Lets see each of them practically in java:- ArrayList :- --->The ArrayList class has a feature of…
Q: In a public key cryptosystem using RSA algorithm, a user uses two prime numbers 11 and 17. He…
A: The solution to the given question is:
Q: wer In HTML, we can add emphasis to inlin
A: Choose the correct answer In HTML, we can add emphasis to inline text using this tag: A. B. All of…
Q: What happens to the rest of the code when the RET instruction is omitted from a procedure?
A: Instruction: Instructions for CALL and RET. The use of assembly-language operations is controlled…
Q: Why isn't Level 3 Application Security Verification required for all applications?
A: An Application An application is a computer software package that performs a piece of specific…
Q: Write an application that accepts from the user the wholesale cost of an item and its markup…
A: The above code in C# is provided below:
Q: When it comes to the creation of software, what function does System Modeling play?
A: As a process-oriented paradigm, the systems model focuses on the flow of information and the…
Q: Explain the key distinction between a telephone network and an Internet connection.
A: This question tells about the key distinction between a telephone network and an Internet…
Q: Describe three different methods for generating signatures. Indicate how one approach differs from…
A: Different approaches to generate signatures Currently different national and international…
Q: What gates are known as universal gates? Why?
A: Intro A gate is critical in boolean algebra, and there are several gates, such as NOR and NAND. The…
Q: Based on Don Norman's idea of user issues, discuss how formative assessment may be used to solve…
A: Introduction: These evaluations occur throughout the redesign process, and the information gained…
Q: What is the physical address of this struction Source operand of MOV BL, [SI +
A: The answer is
Q: The faster memory of the memory hierarchy costs the most amount of money. Given this fact, which of…
A: Task : Given the four sets of memory components. The task is to find the fastest and costliest…
Q: How Boolean logic correlates to the logic gates?
A: Given To know about the Boolean logic correlates to the logic gates
Q: dentitv and describe the eight essential comnonents of communication.
A: Eight essential components of communication are:- 1. Source :- It is the sender who generates the…
Q: A weighted average assigns equal importance to all periods of data. True False
A: A weighted average assigns equal importance to all periods of data is False
Q: You need a pre-written data structure that handles key/value pairs. What data structure should you…
A: Java.util package contains collections frameworks, classes, and so many other things. HashMap is a…
Q: How do the different styles of system units on desktop computers, notebook computers, and mobile…
A: How do the different styles of system units on desktop computers, notebook computers, and mobile…
Q: In modern cryptography, what is Perfect Security?
A: Introduction: The perfect security in modern cryptography is one-time pad, commonly known as OTP,…
Q: dentify and categorize the data on your computer or PDA. What information is confidential, sensitive…
A: Information is defined as news or knowledge that is received or imparted. A piece of information is…
Q: What is the physical address of this instruction Source operand of MOV BL, [SI + BP - 9H], If you…
A: ans is
Q: Assembly language instructions may be optimized by writing compilers and assemblers that rearrange…
A: The answer is
Q: 6. If the starting address location changes, in which of the following cases, the program has to be…
A: D compile time binding is the correct option Explanation:- Because compile time binding describe…
Q: A number 428 in duodenary (base 12) is to be added to C10 in tredinary (base 13). The sum will be s
A: The answer is
Step by step
Solved in 2 steps with 2 images

- Create a program named FileComparison that compares two files. First, use a text editor such as Notepad to save your favorite movie quote. Next, copy the file contents, and paste them into a word-processing program such as Word. Then, write the file-comparison application that displays the sizes of the two files as well as the ratio of their sizes to each other. To discover a files size, you can create a System. 10. Filelnfo object using statements such as the following, where FILE_NAME is a string that contains the name of the file, and size has been declared as an integer: FileInfo fileInfo = new FileInfo(FILE_NAME); size = fileInfo.Length;C2- Write a Python program that reads the contents of a file named ‘Book.txt’ (you must write exception handling if the file doesn’t exist) The program should also determine and print the following: The number of words in the file The number of distinct words (without repetition) The number of uppercase letters in the file The number of lowercase letters in the file The number of digits in the file The number of whitespace characters in the fileCreate a program that calculates a five(5) grades of five(5) students and handles exceptions. It reads the data from a file and writes the output to a file. Send a copy of the following: Softcopy of the running code Screenshot of input file and output file Screenshot of the code
- Write a program that will read from a text file and display onscreen only the odd number lines i.e. the first, third, fifth etc. lines from the file will be displayed while the even numbered lines will be skipped (not displayed)as. The program will always read from the same text file "input.txt", don't have your program prompt the user for a file name. Your program does not have to handle file input problems with exception handling. Nor does your program have to close the file. Finally you can assume that the file will consist at least one line of text, it won't be empty. In python plsThis class prints the first several lines of a file. The default is to print 5 lines, but the -n flag can specify a different number. If no file is specified on the command line, read from standard input. The code bekoow is to help get started. #include <stdio.h> #include <stdlib.h> // You may assume that lines are no longer than 1024 bytes #define LINELEN 1024 static void usage (void); int main (int argc, char *argv[]) { return EXIT_SUCCESS; } static void usage (void) { printf ("head, prints the first few lines of a file\n"); printf ("usage: head [FLAG] FILE\n"); printf ("FLAG can be:\n"); printf (" -n N show the first N lines (default 5)\n"); printf ("If no FILE specified, read from STDIN\n"); }Write a program that writes a series of random numbers to a file. Each random number should be in the range 1 through 500. The application should let the user user specify how many random numbers the file will hold. Use an exception to make sure that an integer was typed in by the user for the #to generate. If not reask the user for input in the except clause until they input the correct number. You should do this in one function named main
- create a java method named clearDirectory(String name)a. This method should delete all of the files in the directory with the specifiedname. Hint: read the java.io.File documentation to see how you might list the files in a directory and then delete them.b. If a file cannot be deleted for some reason, throw an IOException with anappropriate message including the absolute path to the file.c. Rethrow any exceptions that might occur.Write a python program that will :a. Open the file data.txtb. Create a second file named processed.txtc. Read the numbers from the first file one at a time. For each number write into the second file, if possible, itsi. square ii. square root.iii. reciprocal (1/number) Use a math module function for the square root.Use exception handling to trap possible errors. d. Report the number of items in the original file and the number that were successfully stored in the second file.e. Report the number of each type of error: ValueError, ZeroDivisionError, TypeError. these are the numbers in file data.txt : 26O76-9185-4485-95-3483-64-76-4189083-99-698-790-32-49-898579-285619-93-21-238251-80l62-78-87128-730-45-7328-5O-7063-36-720-76-24-590-548335-388-1429-351727-61-424983Assume that a file containing a series of integers is named numbers.txt. Write a program that calculates average of all thernumbers stored in the file and prints the average on the screen. The code that does not work. How can I add try except ZeroDivision Error into the code? file=open("numbers.txt", "r");count=0sum=0content=file.readlines()for nums in content: num=nums.split("") for i in num: sum=sum+int(i) count=count+1print("Average:"+str(sum/count))
- 1. Modify exampleSix to read file tooutfile2.txt compute and display the total; then write the total to a file named tooutfile2A.txt exampleSix This program creates file tooutfile2.txt and stores 10 integers in it Please verify that the file was created along with the content package pwriter2; import java.util.Scanner; import java.io.*; public class Pwriter2 { public static void main(String[] args) throws IOException { PrintWriter tofile2 = new PrintWriter( "tooutfile2.txt" ); int i = 0; while (i < 10){ tofile2.println( i ); i = i + 1; } tofile2.close(); } }Assume that there is a data file named as “data.txt”. This data file contains integer values in multiple lines, as shown below. You are asked to write statements in the main() method to open the file, read and print out the total of all the values (should be 55). Place your code into try-catch block so that the FileNotFoundException will be caught and an error message will be printed if no such file exists. data.txt1 2 34 5 67 8 9 10 import java.util.*;import java.io.*;public class ReadAndPrint {pubilc static void main() {Write a program to create a file named RandomNums.txt if it does not exist. Write 100 integers created randomly into the file using textI/O. Integers are separated by spaces in the file. Read the data back from the file and display the data in increasing order. - Next, add a feature to the existing code that finds the number with the highest number of occurrences. - Write your results to a file. - Print the output to the console for verification and debugging. - Use OOP design. - Use exception handling as necessary. - Use comments accordingly. The program must be OOP in design and implement a test class. use of Collections .frequency() to pull number counts





