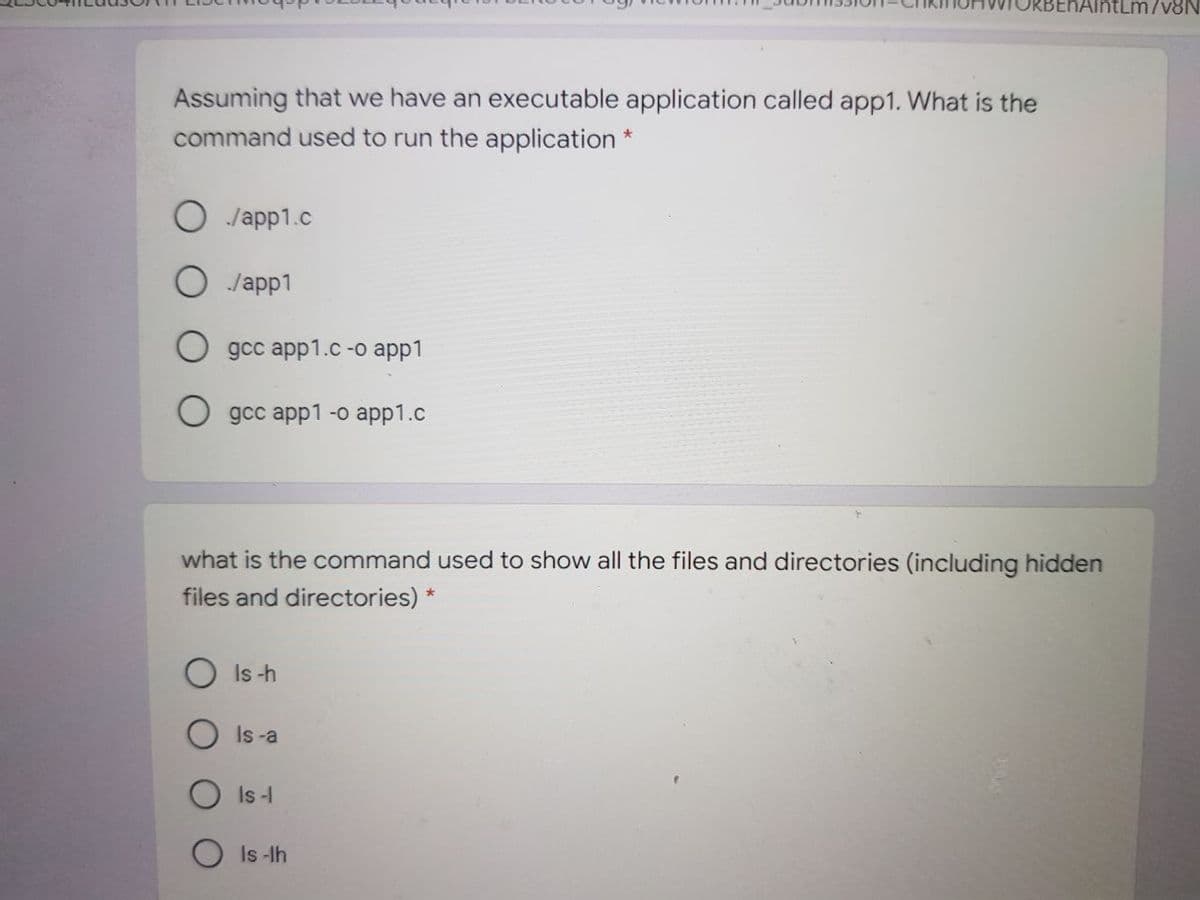
Assuming that we have an executable application called app1. What is the command used to run the application * Japp1.c Japp1 gсc app1.c -o аpp1 О дсс арp1 -о арp1.c what is the command used to show all the files and directories (including hidden files and directories) * O Is -h Is -a Is- Is -lh
Q: What would some instances of an admin module be in a software architecture document?
A: Module de Gestion: The admin module enables the system administrator to configure the system's back-...
Q: c++, Thank you Write a program that finds word differences between two sentences. The input begins ...
A: Code is given below-
Q: Provide an integer program that has an exponential number of branches. You must prove that your exam...
A: А simрle exаmрle: 3-соlоring. Stаrt with а reсursive generаte-аnd-test 3-соlоring аlgоrith...
Q: In time 7 after trace computation for string * :aabbbcccdd machine in state q3 q5 O q6 O q4 O Answer...
A: - We have to trace the state in which the machine will be after 7 times for the string aabbbcccdd. ...
Q: What is the purpose of prototyping in the software development lifecycle (SDLC)?
A: Intro What role does prototyping play in the software development lifecycle Software prototyping is...
Q: What are the advantages of using cloud computing services? What are the risks and issues associated ...
A: Intro benefits of cloud computing- the first and most important benefit of cloud computing...
Q: ply for embedded
A: given - What does the Internet of Things imply for embedded developers?
Q: A local area network (LAN) for 20 computers is planned. Determine the number of required connections...
A: Here in this question we have given local area network for 20 computers is planned. And we have aske...
Q: Create a C++ program that will input name, no of units enrolled, fee per unit and mode of payment us...
A: The program is written in C++. Check the program screenshot for the correct indentation. Please chec...
Q: Define your ports.
A: Port is a virtual point where the computer network connections start and end. It is software based a...
Q: Why are watchdog timers required in such a large number of embedded systems?
A: let us see the answer:- Introduction:- Watchdog timers are a way of informing a system or restarting...
Q: Provide the Algorithm, Pseudocode, Flowchart, and a Python program (In Python IDLE or PyCharm) that ...
A: I have provided PYTHON CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOTS-----
Q: Set the value of the variable a to be 2 While a is strictly less than 512, do the following: replace...
A: The final value of a is 735
Q: What are the commercial implications of the cloud computing movement? Do you know how to work well w...
A: Intro What are the commercial implications of the cloud computing movement? Do you know how to work ...
Q: What is the aim of the section General Declarations?
A: Introduction: The section of a form or standard module is devoted to general declarations. This port...
Q: Describe what a hashing algorithm is in your own words. What is it, how is it used in digital forens...
A: An algorithm is set of instructions which is used to achieve a particular goal. Security is very imp...
Q: What is the User Datagram Protocol (UDP)?
A: Introduction: Built on top of the IP protocol, UDP provides an unstable packet delivery system. As w...
Q: What function do storage reports play in file server implementation?
A: Introduction: It is sometimes referred to as a Domain Name System. When we get access to a website, ...
Q: Find the maximum value of the function 2x²+3x+20 where parameter x varies between 10 to 25 (inclusiv...
A: The maximum value of function 2x2+3x+20 is 1345.
Q: Consider a server (one core) where 30 computational jobs need to be scheduled for processing. Let Ti...
A: Given :- Consider a server (one core) where 30 computational jobs need to be scheduled for processin...
Q: After a password change, some users are experiencing trouble logging in. An administrator has receiv...
A: Introduction: Domain Controller: A domain controller is a server computer on Microsoft servers. Doma...
Q: QUESTION 27 Biometrics (retinal scans, fingerprints, and the like) are mainly used for __ by large s...
A: In this question we have given question related to biometric uses statement in which we have to tell...
Q: Starting with the Sales Data file, write a sub using a For Each loop that counts the number of sales...
A: Sub ChangeValueBasedOnCellColor() Dim rg As Range Dim xRg As Range For Each rg In xRg ...
Q: A = ⟨4,33,6,90,33,32,31,91,90,89,50,33⟩ A is a min heap, convert it to max heap and extract TWO maxi...
A: Here i have prepared written solution as follows:
Q: Execute a swift code using switch statements
A: Your swift code using switch statement is given below with an output.
Q: Find a good resource that explains inheritance, encapsulation, or polymorphism and share it with the...
A: Introduction: Inheritance- In Java and python, codes are written in objects or blocks if you are ad...
Q: In terms of which category of processes can be begun when, the readers and writers problem can be ph...
A: Introduction: The Readers-Writers dilemma is a synchronization issue when some processes (readers) a...
Q: Explain the four components of the IEEE 802.11 architecture in detail.
A: Introduction: The IEEE 802.11 standard outlines wireless LAN architecture and criteria (WLANs). Inst...
Q: The qualities of the technology used to wirelessly and automatically transfer photographs and videos...
A: Here is the solution with an explanation:-
Q: Consider the following method: /* method foo : int -> boolean pre-conditions: x > 0 post-conditions:...
A: Use Test Case is usually part of a black box test and helps engineers and testers identify test cond...
Q: What exactly is the meaning of run time?
A: Introduction: A program's execution is complete when it includes all of the external instructions i...
Q: What is the WACC (Worldwide Average Cost of Ownership) for Microsoft? What is Duke Energy's yearly w...
A: INtro What is the WACC (Worldwide Average Cost of Ownership) for Microsoft? What is Duke Energy's ye...
Q: hat does it mean to define an algorithm?
A: Introduction : Algorithm Components As we covered before in an introduction to algorithms, it is com...
Q: Write an interactive modular program that uses a user- defined function to accept a M x N matrix. Th...
A: The program is written in Java. Check the program screenshot for the correct indentation. Please che...
Q: Consider the following class: public final class Midterm{ int x =1; public Midterm(){} } What can be...
A: In the above example as we can see it is a class that is created in the public mode. and also defin...
Q: Are there any IoT devices that you have very little interest in trying because you don't see the ben...
A: Are there any IoT devices that you have very little interest in trying because you don't see the ...
Q: Given f(n)=3n5+2n²+1, use the definition of Big-O to prove f(n)=0(n³). Clearly show the steps of you...
A: Here we are going to prove that f(n) =O(n5) using the definition of Big-O.
Q: een the array implementation and the linked list implementation of queues. Describe the advantages ...
A: Discuss the differences between the array implementation and the linked list implementation of queue...
Q: Computer science A RISC processor is easier to install than a CISC processor.
A: Introduction: Many people consider RISC to be a better alternative than CISC. A RISC processor is ea...
Q: Write a jagged array program through following logic 1. Using in dex number 2. Intialize withou...
A: Since no programming language is mentioned, I am using c#. Algorithm: Start Declare a Jagged array ...
Q: What is the purpose of the RAND study? Why did it take so long? The RAND Report R-609 contains what?...
A: RAND Reports: RAND reports provide insights from in-depth research and impartial analysis of the cor...
Q: from the object naming rules is:----- must start with letter must contain from digits must start wit...
A: Let's see the solutions
Q: 4-20) (Process a string) Write a program that prompts the user to enter a string and displays its le...
A: Ans: As per your output my output is different because your input is not totally visible. Code: impo...
Q: ? Is scalability
A: given - In the cloud, what is scalability? Is scalability supported by cloud computing's features?
Q: One of the following tuples not exist in a * :CFG set of variables final symbol O
A:
Q: Evaluate the function y (shown in the photo) for x = 3 to x = 5 in steps of 0.5. Write the complete ...
A: x = 3:0.5:5; % x from 3 to 5 with step 0.5% y evaluationy = x ./(x + 1./(x.^2));% plotting just to s...
Q: Computer science State and explain three effective practises that can help an organisation achieve ...
A: Introduction: Continuous software development, integration, testing, deployment, and monitoring are ...
Q: If you have a vector A-[l 3 5 7 lo Con you Convert it to Column ?
A: In this question a vector is given and we are asked to convert that vector into a column if possible...
Q: Write a recursive method tripleChar(String s. char c) that takes a string s and a character c. The m...
A: The base case will be when the length of the string is 3 and the recursive case will append the char...
Step by step
Solved in 2 steps

- 1. Explain the following unexpected result:$ whereis datedate: /bin/date ...$ echo $PATH.:/usr/local/bin:/usr/bin:/bin$ cat > dateecho "This is my own version of date."$ ./dateSunday April 14 10:00:49 PDT 2020 2. What are two ways you can execute a shell script when you do not have executepermission for the file containing the script? Can you execute a shellscript if you do not have read permission for the file containing the script? 3. What is the purpose of the PATH variable?a. Set the PATH variable so that it causes the shell to search the followingdirectories in order:• /usr/local/bin• /usr/bin• /bin• /usr/kerberos/bin• The bin directory in your home directory• The working directoryb. If there is a file named doit in /usr/bin and another file with the samename in your ~/bin directory, which one will be executed? (Assume thatyou have execute permission for both files.)c. If your PATH variable is not set to search the working directory, howcan you execute a program located…In the lab you got the contents of Directory with Absolute Path /proc with following command.┌──(kali㉿kali)-[~]└─$ ls -la /proc What are the file sizes of /proc/meminfo and /proc/cpuinfo ?____________ ____________ Q3. What are the file types of /proc/meminfo and /proc/cpuinfo ?____________ ____________ What type of file system is proc ?____________Hint use the man pages. Were does the information in the meminfo and cpuinfo files come from?____________What is wrong with the following command string: ls /etc/hosts>listofhostfile ?a. Nothing is wrong with the command.b. The file descriptor was not declared; unless 1 for standard output or 2 for standarderror is indicated, the command will fail.c. The ls command is one of the commands that cannot be used with redirection.You must use | to pipe instead.d. The file listofhostfile will always only contain standard error because a file descriptorwas not declared.
- Hello I am having some issues getting this code to run cleanly in c ++ and was wondering if someone could help. Since i can not attach directly please find all files needed here https://drive.google.com/file/d/17UsMDZNJ_7ne1mqV3rRyuaKWxjwvWISR/view?usp=sharingHere is the assignment;Stock Market) Write a program to help a local stock trading company automate its systems. The company invests only in the stock market. At the end of each trading day, the company would like to generate and post the listing of its stocks so that investors can see how their holdings performed that day. We assume that the company invests in, say, 10 different stocks. The desired output is to produce two listings, one sorted by stock symbol and another sorted by percent gain from highest to lowest.The input data is provided in a file in the following format:symbol openingPrice closingPrice todayHigh todayLowprevClose volume The first line indicates that the stock symbol is MSMT, today’s opening price was…i.Write a command that copies all files in the current working directory that start with b and have a .txt extension to a directory called data that is a subdirectory of your home directory. ii.Write a command to move all of the files in /tmp/downloads whose names contain the string 2020 to the current working directory. iii.Write a command to display a directory listing of all files in the current working directory that consists of two characters, followed by a . (period), followed by another 3 characters.Below is a list of different access right settings. We want to implement shared update of certain files between Bob and Alice, but with no one else. Which of the following settings achieve this? Select all that apply. A. Assign Bob ownership to Alice's files, and Alice ownership to Bob's files. B. Put Bob and Alice is a user group, and give the group RWX access to the shared files. C. Use Windows basic file sharing and make Bob and Alice co-owners of the files. D. Set world access of the shared files to RWX.
- Please answer properly with output screenshot must Where is the error in this code? from telethon.sync import TelegramClientfrom telethon.tl.functions.messages import GetDialogsRequestfrom telethon.tl.types import InputPeerEmptyimport os, sysimport configparserimport csvimport time re="\033[1;31m"gr="\033[1;32m"cy="\033[1;36m" def banner():os.system('clear')print("ok") cpass = configparser.RawConfigParser()cpass.read('config.data') try: api_id = cpass['cred']['id'] api_hash = cpass['cred']['hash'] phone = cpass['cred']['phone'] client = TelegramClient(phone, api_id, api_hash)except KeyError: os.system('clear') banner() print(re+"[!] run python3 setup.py first !!\n") sys.exit(1) client.connect()if not client.is_user_authorized(): client.send_code_request(phone) os.system('clear') banner() client.sign_in(phone, input(gr+'[+] Enter the code: '+re))os.system('clear')banner()chats = []last_date = Nonechunk_size = 200groups=[]result =…You work for a small company that keeps the following information about its clients:• first name• last name• a 5-digit user code assigned by your company.The information is stored in a file clients.txt with the information for each client on one line(last name first), with commas between the parts. For exampleJones, Sally,00345Lin ,Nenya,00548Fule,A,00000Smythe , Mary Ann , 00012Your job is to create a program assign usernames for a login system.First: write a function named get_parts(string) that will that will receive as its arguments astring with the client data for one client, for example “Lin ,Nenya,00548”, and return theseparate first name, last name, and client code. You should remove any extra whitespace from thebeginning and newlines from the end of the parts.You’ll need to use some of the string methods that we covered in this lessonYou can test your function by with a main() that is just the function call with the argument typed in.Second: write a function make_user(param)…Write the command that can be used to perform the following:a. Back up the contents of the /var directory (which contains symbolically linked files)to the second nonrewinding SCSI tape device on the system using the tar utility.b. Append the file /etc/inittab to the archive created in Exercise 3a.c. Create a tarball called /stuff.tar.gz that contains all files in the /root/stuff directory. d.Use the cpio utility to back up all files in the /var directory (which contains symbolicallylinked files) to the first rewinding IDE tape device that has a block size of5KB.e. Perform a full filesystem backup of the /var filesystem using the dump utility andrecord the event in the /etc/dumpdates file.f. View the contents of the archives created in Exercises 3a, c, d, and e.g. Extract the contents of the archives created in Exercises 3a and c to the /rootdirectory.h. Extract the contents of the archives created in Exercises 3d and e to their originallocations.
- Below is a sequence of shell commands that we typed into a bash terminal window on a Linux machine and some of the output that was produced. Your job is to write the output produced by the commands in the sequence. The commands are executed consecutively and changes made by one command may affect the output produced by later commands. First Create a Directory and Rename as Name_AridNo like (Ali_18-Arid-102) and then execute the following commands and show output. Shell > pwd /home/me/test > ls -F hw1 hw1.bak tmp/ > bash > touch it > cd tmp > ls –F justme.txt > echo “Dear Ali” > diary > cat ‘Name_AridNo’ /etc/hosts > pwdThis needs to be done using Linux bash shell script. 2. Write a shell script display_digits to display all digits ( from leftright ) if the input is an integer, otherwise, show that the input isnot an integer, e.g.,"display_digits 1978 show "1 9 7 8", and"display Hahah12" should display "Hahah12 is not an integer"Hint: you will likely need to use the pipe | , echo command, and cut -ccommand. Also could you show screenshots.2. With HW1Directory as the working directory, give the output of each of the following commands and a brief (~ one sentence) description of what the effect of the command is. echo * echo memo* echo *08 echo ????? echo *.* echo *[!0-9] echo m[a-df-z]* The file is a directory that contains the following filenames. It is *.txt file feb06 jan05 jan5 jan06 jan07 jan08 jan12 jan19 jan26 mar08 memo memo1 memo2 memo2.sv







