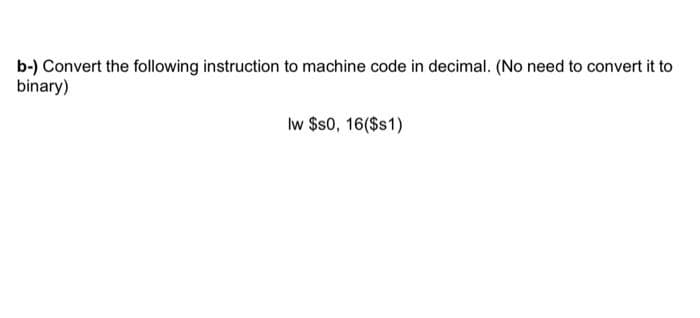
b-) Convert the following instruction to machine code in decimal. (No need to convert it to binary) Iw $s0, 16($s1)
Q: A common bus system which is capable of transferring 2 bits at time with number of registers are 4 e...
A: We understand that the Boolean expression for this 4-to-1 Multiplexer with the inputs A to D and da...
Q: Answer the following 4 questions with step by step explanations : Convert 870678(9) = x(27) Convert ...
A: Number Representation: Numerous number base systems exist, each of which determines which digits are...
Q: Write a class called TwoDArray that has the following behaviors for an array of ints. getTota...
A: Answer the above question are as follows:
Q: Given a JSON document below: "firstName": "John", "lastName": "Smith", "age": 25, "address": "street...
A: Since you have asked multiple questions, we will solve the first question for you. If you want any s...
Q: Create the code or a C program and generate the output. The perimeter of rectangle twice as long as...
A: C code to find the area of the rectangle is detailed below.
Q: Consider the above rooted tree. 1. Which vertex is the root? 2. Which vertices are internal? 3. Whic...
A: Here, we are going to find out different nodes as per asked in questions. A rooted tree have a root ...
Q: 10. Sanguine (symbol Sa) is a fictional name for one of the halogens. According to the naming rules ...
A: The answer of the following according to me is (E).
Q: Given a list of values l = [ao, a1, a2,..., an] , we can construct a continued fraction: 1 ao + 1 a1...
A: Program Explanation:- Python function to compute the continued fraction. The base case, when list l...
Q: B. Native apps have push notifications sent by an application to a user when the applications are no...
A: NOTE: ACCORDING TO COMPANY POLICY WE CAN SOLVE ONLY 1 QUESTION. YOU CAN RESUBMIT THE QUESTION AGAIN ...
Q: names, four Write a single c++ program code that employs * -Uwing: 1- Define a two-dimensional array...
A: Code: #include<iostream>using namespace std; int main(){ int x[3][4]; for (int i = 0; i &l...
Q: With the ECB mode, if there is an error in a block of the transmitted ciphertext, only the correspon...
A: Answer:
Q: Properties of U, 12, 6 Let f, g, h: N →R*. Then, P1: (Transitivity) fe O(g) and g e O(h)=fe 0(h) How...
A: Transitivity of all notation: (n) = Ο(g(n) ) and g(n) = Ο(h(n) ) ≈ f(n) = Ο(h(n) ) f(n) = Ω(g(n) ) a...
Q: Two stacks of the same kind are the same if they contain the same number of elements and have the sa...
A: Introduction: In this question, our goal is to check whether the two stacks are the same or not. Fir...
Q: What portion of the computer processor is responsible for floating-point arithmetic
A: In Computer architecture we have CPU, which has so many hardware components to perform operations f...
Q: Write a program in CORAL to accept a series of positive integers in a loop and then terminate the lo...
A: Answer
Q: We want to emulate that, too! Using a recursive function, make it so that we print the number we are...
A: #include <stdio.h>int n = 1; // global variablevoid snake_ladder(int start, int stop);int main...
Q: have a question about python turtle. My turtle is covering the first circle. How do I move the turtl...
A: I'm giving my solution for starting at the top left of the window and then you can adjust it to you...
Q: input1="12345" input2="abcde" output="1a2b3c4d5e" in c++
A: we have to write C++ code to concatenate given two string as follows input1="12345" input2="abcde" ...
Q: With explanation please 1) Find the largest positive number that can be represented in n-bit 2’s co...
A: Concept of the range integers that can be represented by n-bit 2's complement: In 2's complement for...
Q: . Draw a circuit diagram using appropriate logic gates to implement a 3-bit comparator. Identify the...
A:
Q: What data type may a 32-bit signed integer be stored in?
A: Please find the detailed answer in the following steps.
Q: neering (IT)
A: given - Explain risk exposure with an example in software engineering (IT)
Q: Write a java program to print the numbers from a user entered number till 0 using recursion.
A: Given :- Write a java program to print the numbers from a user entered number till 0 using recursio...
Q: debugg help def print_categories(main_list): if id not in main_list: print("There...
A: def print_categories(main_list): # checking main_list is empty if main_list==None or len(ma...
Q: main.c 9. Character Count by Jay Vince Serato Given a string of both uppercase and lowercase letters...
A: Please refer below for your reference: #include <stdio.h> #include <string.h> int main...
Q: Can E-learning be defined as an e-business activity? Does it qualify as e-commerce activities?
A: Given: Is it possible to classify e-learning as an e-business activity? Does it fall within the cate...
Q: Describe how LDAP may be used to give numerous hierarchical data views without having to duplicate t...
A: Introduction Describe how LDAP may be used to give numerous hierarchical data views without having ...
Q: Using an embedded assembler, write a C-program with a function to convert a digit (0 - 15) to the ap...
A: using System; class Dec { // Function to convert // hexadecimal to decimal static int hexad...
Q: Write a PowerShell (.ps1) script that performs the following (make sure the output is in human-reada...
A: Write-Output "First Name Last Name" #Prints out your first and last name. Get-Date -Format "MM/dd/yy...
Q: Exercise 5. (Transpose) Write a program called transpose.py that accepts m (int) andn (int) as comma...
A: code is an given below
Q: How can one identify the real-world identity associated with a certain user ID on a public blockchai...
A: How can one identify the real-world identity associated with a certain user ID on a public blockchai...
Q: ou can use C++ as a procedural, as well as an object-oriented, language A. True B. False
A: You can use C++ as a procedural, as well as an object-oriented, language A. True B. False
Q: What is one of the most important applications of pre-order traversal in binary search trees?
A: Introduction: The binary search tree is a sophisticated algorithm that analyses the node, its left a...
Q: Problem Description Using the binary search tree (BST) data structure, we can sort a sequence of n e...
A: the code is an given below :
Q: 8. Create one or more Use cases to describe the process of withdrawing cash from an ATM
A: explain uses cases process of withdraw cash from atm.
Q: 19. Completion. Let (2, B, P) be a probability space. Call a set N null if = 0. Call a set BC2 negli...
A:
Q: Please compare and contrast (Difference) from application software and system software. Give your co...
A: Software is a collection of instructions that tell a computer how to work. Computer software is typi...
Q: ggplot(data = filter(starwars, species != "Hutt")) + geom_point(aes(height, mass, facet_wrap(~ gende...
A: what is missing from the blank in the following
Q: 1. What is the running time of the following algorithm. for i = 1 ton for j = n to i j = j - 2 for j...
A: Given:
Q: Write c++ program to input six number from the keyboard. Find the smallest and largest of the six nu...
A: Program Explanation:- Using the header file. Using the standard namespace input/output function. In...
Q: Edit the class diagram to include a Teaching group- add the attributes name, room number and subject...
A:
Q: In this assignment, you will create a very particular calculator that works with up to 3 integer num...
A:
Q: What is the function of the WORD type?
A: Below is the complete explanation about WORD and it's functions in detail.
Q: What exactly is the notion of privacy in terms of information security? What distinguishes this defi...
A: Intro Security is all about protecting the data and privacy is safeguarding the user identity. Infor...
Q: tips for network repair
A: Introduction the question is about tips for network repair and here is the solution in the next st...
Q: Define the type of security attack in each of the following cases: A student breaks into a professor...
A: A student breaks into a professor’s office to obtain a copy of the next day’s test. Ans :- Confident...
Q: Describe the MIDI port. What functions can a MIDI-equipped system unit perform?
A: Introduction : MIDI port: Hence, the MIDI-Port is the principal mechanism by which MIDI-sequencers a...
Q: Build an ER model to manage an airport with the following requirements: • A flight consists of o...
A: Build an ER model to manage an airport with the following requirements: • A flight consists of one...
Q: Professor Mikka Singh of Harvard University has proposed a new atomic instruction named “Gurru”. The...
A: A semaphore is a variable that represents the number of resources available in a system at a given p...
Q: Someone tries to fix the stack based buffer overflow problem as follows, is it secure now? why? Are ...
A: We need to check if the given solution is secure, if yes then why, and find if there any other issue...
I need only correct answer. I'll give upvote for correct one. Please fast. I have very less time. Don't give me wrong answer.
Step by step
Solved in 2 steps with 1 images

- Need help in Python1. Enter the for condition that should replace R12. Enter the instruction that should replace R2Q 4. State whether the following instructions are valid or not. If valid then define properly, if not, then state the reason of their invalidity: MOV [BX + SI + 2], AL XCHG AL, CX ADD 23H, ALPlease answer the question below alongside the following; Describe what you expect the instruction to do.
- please read the instruction carefully and answer the questionQ2) (a) For the expression given ( An + B’n ) * ( C’n + Dn ) , you should write Zero-Address instructions to compute the same expression? Also mention what type of computer organization will use these instructions.Question 13 sum.mov AL,7ah mov BL,AL and AL,0fh and bl,0f0h What will be the values of AL and BL registers when the above program runs and terminates? Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this line

