B O The basic tasks of defining the needs, configuring system capabilities in support of those needs, and then operationally deploying the VM are conceptually the same as when deploying the same OS and apps on a desktop or laptop. You use many of the same tools, OS features, and utilities. D O с O O VMs cannot run without some kind of software-defined network and a hypervisor, which bring many more complex security concerns that administrators need to deal with to achieve required information security performance. VMs can access any resource on the bare metal machine that is hosting them through the hypervisor, which requires administrators to take many extra precautions to prevent security breaches. The bare metal server, host OS (if used), and hypervisor provide none of the security features you'll need to configure to keep other system users, processes, and data, and those in each VM, safe, secure, and protected from each other.
B O The basic tasks of defining the needs, configuring system capabilities in support of those needs, and then operationally deploying the VM are conceptually the same as when deploying the same OS and apps on a desktop or laptop. You use many of the same tools, OS features, and utilities. D O с O O VMs cannot run without some kind of software-defined network and a hypervisor, which bring many more complex security concerns that administrators need to deal with to achieve required information security performance. VMs can access any resource on the bare metal machine that is hosting them through the hypervisor, which requires administrators to take many extra precautions to prevent security breaches. The bare metal server, host OS (if used), and hypervisor provide none of the security features you'll need to configure to keep other system users, processes, and data, and those in each VM, safe, secure, and protected from each other.
Chapter13: Internet And Distributed Application Services
Section: Chapter Questions
Problem 1RP
Related questions
Question
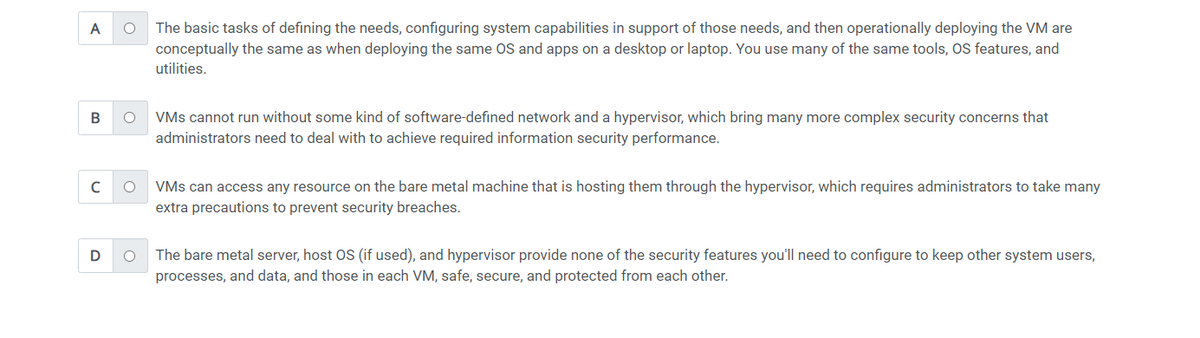
how does securing a virtual machine differ from securng a physical computer system? ( choose all that apply)
Transcribed Image Text:A
B
с
D
O The basic tasks of defining the needs, configuring system capabilities in support of those needs, and then operationally deploying the VM are
conceptually the same as when deploying the same OS and apps on a desktop or laptop. You use many of the same tools, OS features, and
utilities.
O VMs cannot run without some kind of software-defined network and a hypervisor, which bring many more complex security concerns that
administrators need to deal with to achieve required information security performance.
O
O
VMs can access any resource on the bare metal machine that is hosting them through the hypervisor, which requires administrators to take many
extra precautions to prevent security breaches.
The bare metal server, host OS (if used), and hypervisor provide none of the security features you'll need to configure to keep other system users,
processes, and data, and those in each VM, safe, secure, and protected from each other.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning