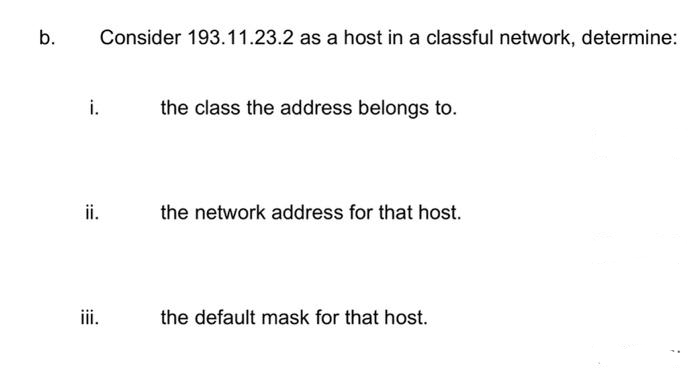
b. Consider 193.11.23.2 as a host in a classful network, determine: i. ii. iii. the class the address belongs to. the network address for that host. the default mask for that host.
Q: Explain the many strategies that may be used when creating applications in a structured,…
A: The answer is given in the below step
Q: Describe the GRANT declaration's potential outcomes and how they relate to the preservation of…
A: It is used to provide permissions to a specific user or role or to all users to conduct actions on…
Q: There are many parallels between the waterfall methodology and the iterative-and-incremental…
A: Waterfall model is a classical model which is used in system development life cycle with sequential…
Q: How can we be sure that while using the internet, our anonymity is protected?
A: Introduction : Users can access the Internet through an anonymity network while keeping their…
Q: Please describe the three guiding principles that govern integrity; I'd really appreciate it. It…
A: A set of integrity constraints or rules are typically used in database systems to guarantee data…
Q: How may the SQL language be used to change a table's structure? Which of these significant changes…
A: SQL stands for the structured query language. It is a database query language used to store and…
Q: How can you protect yourself from falling prey to a man-in-the-middle (MITM) attack? You should…
A: Introduction An assault known as a "Man in the Middle" occurs when an outsider—more specifically, a…
Q: What factors need to be taken into account before choosing a strategy for the protection of a…
A: A capacity to reduce the attack surface is network protection. It assists in preventing employees…
Q: We believe that Flynn's taxonomy should be expanded by one level. What distinguishes a high-level…
A: In parallel computing, tasks are divided into independent components that may run simultaneously.…
Q: If a node has a wireless connection to the Internet, does that node have to be mobile? Explain.…
A:
Q: It would be really helpful if you could explain the difference between integrity limitations and…
A: The problem at hand includes integrity standards and permission restrictions. Integrity restrictions…
Q: A Boolean operator may be used to find information on two different subjects at the same time. Which…
A: Basically there are three boolean Operators, AND (&&) OR (||) NOT (!)
Q: What are the main advantages of reusing application system components in comparison to developing…
A: To begin, we shall familiarise ourselves with both notions.
Q: What measures can you take to ensure that unexpected spikes in the voltage your computer gets don't…
A: SURGES IN POWER: A quick spike in voltage is called a power surge, often referred to as transient…
Q: Consider the following design problem concerning implementation of virtual-circuit service. If…
A: We need to find the costs for virtual circuit and datagram implementation, and suggest better…
Q: Initially, Linux developers chose a non-preemptible kernel because... How does a non-preemptible…
A: One is a DOS-based system with a cooperative, non-preemptive kernel. It was created in this way…
Q: class Animal { public String toString() { return "Animal"; } public String f() { return "Animal f";…
A: The solution is provided in the next step.
Q: R6. Suppose N people want to communicate with each of N-1 other people using symmetric key…
A: Suppose N people want to communicate with each of N-1 other people using symmetric key encryption.…
Q: 39. Find the complement of each of the following graphs. a. b. V1. VI VA V2 V4 V2 V3 V3
A: Complement Graph: A graph with a same set of vertices as the original graph but the edges are the…
Q: What are the three elements that a network must always have in order to function successfully and…
A: Answer :-
Q: Give three arguments in favor of the spiral model over the waterfall strategy, along with…
A: Actually, the SDLC process is a what introduced the spiral and waterfall models. To create a…
Q: How may the SQL language be used to change a table's structure? Which of these significant changes…
A: Table's Structure: Rows and columns are represented by cells in a table's horizontal and vertical…
Q: What inspired the creation of the RISC architectural concept?
A: The RISC Architectural Concept: The RISC architecture's few straightforward addressing modes and…
Q: What are the main advantages of reusing application system components in comparison to developing…
A: Definition: We will first familiarize ourselves with both ideas. Reusing existing application…
Q: Please provide three convincing justifications for why the spiral model is preferable to the…
A: Waterfall model: The waterfall model is a classical model used in system development life cycle to…
Q: What three requirements must a network meet in order to be successful and efficient? Please provide…
A: Below are three important requirements of a network in order to be successful and efficient.…
Q: What is the minimum number of edges of an undirected simple graph with n vertices? Assume it is…
A: The minimum number of edges of an undirected simple graph with n vertices:
Q: How do clustered systems differ from multiprocessor systems? What is required for two machines…
A: Clustered systems are similar to parallel systems as they both have multiple CPUs.
Q: You must first create a transaction in the database to get started. We're going to concentrate on…
A: With regards to database transactions, a unit of work done inside a data set administration…
Q: The top five network topologies that are most often used should be included. According to your…
A: Star topology is the best geography on the grounds that… Each host of star geography is…
Q: Give instances of these benefits and describe in your own words the financial advantages that…
A: Definition: We must address the economic advantages of patent rights to certain people or groups, as…
Q: Consider two mobile nodes in a foreign network having a foreign agent. Is it possible for the two…
A: A foreign network is the network in which a mobile node is operating when away from its home…
Q: When it comes to sending and receiving email over the internet, what are the three protocols known…
A: IMAP is for the recovery of messages and SMTP is for the sending of messages. That implies IMAP…
Q: Describe the three principles that guide integrity in the workplace. Please provide an explanation…
A: The three integrity rules are: Key Restrictions Domain Constraints The integrity of Reference…
Q: When it comes to sending and receiving email over the internet, what are the three protocols known…
A: Introduction: SMTP is used to transmit emails from the sender's email client to the recipient's…
Q: In a multiprogramming and time-sharing environment, several users share the system simultaneously.…
A:
Q: The top five network topologies that are most often used should be included. According to your…
A: Network topology: The physical and logical arrangements of nodes and connections in a network is…
Q: Examine Ghana's educational information systems, particularly in the context of COVID 19 pandemic,…
A: Benefits: The Ghana Education Service announced the opening of an online learning environment for…
Q: All the concurrent approaches that are being explained here are only available on the Linux…
A: Concurrent Engineering explained: This strategy aims to have the developers think about all aspects…
Q: How specifically can a Demilitarized Zone, or DMZ as it is more often known, add to the overall…
A: Given: If you're looking to safeguard your internal network against unreliable traffic, a DMZ…
Q: Task Given a string str and one of its character ch, the coverage of ch is computed as the number of…
A: The printf() is a library function to send formatted output to the screen.
Q: What do you think are the most important considerations to make while making the switch to an ALL-IP…
A: These three techniques all share the following characteristics: The sender, or message source, is…
Q: All partitions on a hard disk drive must utilize the same filesystem once it has been formatted.…
A: A hard drive needs to be partitioned and formatted before it can be utilised. Your final drive count…
Q: Based on your present thoughts, when do you think it would be suitable to start using brouter on…
A: suitable time to start using brouter on your network is:-
Q: What measures can you take to ensure that unexpected spikes in the voltage your computer gets don't…
A: measures can take to ensure that unexpected spikes in the voltage your computer gets don't damage…
Q: In general, character devices are faster in transmitting data than block devices are. What do you…
A: Character devices and block devices are the two primary categories of devices found in all Unix…
Q: Could you maybe clarify what you mean particularly when you mention "principle of non-repudiation"?
A: "Principle of Non-Repudiation": The inability to deny the veracity of a statement is ensured by…
Q: Wireless networks may have vulnerabilities that cause issues. Describe the effects that three of…
A: Wireless networks can have bugs that cause problems. List three of these issues and describe their…
Q: Consider two mobile nodes in a foreign network having a foreign agent. Is it possible for the two…
A: ANSWER:-
Q: Purchase application development tools from the following suppliers: Please support your answer with…
A: App development software is a tool that facilitates the app development process by offering features…
Step by step
Solved in 4 steps

- 4. [Socket] What is a socket? Suppose a process in Host C has a UDP socket with port number6789. Suppose both Host A and Host B send a UDP segment to Host C with destination portnumber 6789. Will both segments be directed to the same socket at Host C? If so, how will theprocess at Host C know that these two segments originated from two different hosts? 5. [Demultiplex] Define multiplexing and demultiplexing. Briefly explain how TCP demultiplexing isdifferent than UDP demultiplexing. 6. [rdt] Consider a reliable data transfer protocol that uses only negative acknowledgments.Suppose the sender sends data only infrequently. Would a NAK-only protocol be preferable to aprotocol that uses ACKs? Why? Now suppose the sender has a lot of data to send and the end-to-end connection experiences few losses. In this second case, would a NAK-only protocol bepreferable to a protocol that uses ACKs? Why?A classless address is given as 177.200.180.92/27. What will be the total number addresses available? 64 30 62 32 What is the first useable host address of 168.198.171.72/27? 168.198.171.64 168.198.171.94 168.198.171.65 168.198.171.95Consider the following page address stream: 2 1 4 3 5 3 2 4 5 2 1 2 4 3 1 Which of the following causes the most page faults to occur on a machine with 3 frames? Scheme that causes the most faults: a) First in First out b) LRU and FIFO are the same number of faults c) FIFO and Opitimal are the same number of faults d) All have the same number of faults e) Least Recently Used f) No faults occurs g) LRU and Optimal are the same number of faults h) Optimal NUMBER OF FAULTS CAUSED: a)
- ) s ®%74 I, 10.100.100.1is a valid host address * QO Yes O No -4 0 G 9:09 Which is not true about Class C addresses (select more than answer) * the first byte between 192 - 224 the number of hosts is less than subnets Many addresses are wasted the address space is 53687191 address the first byte starts with 110 Map the following addresses to its right class * 192.168.6.7 128.0.10.10 127.0.100.100 O O 'O 190.0.255.255 is a Class B special address * QO True Q False Back Next Never submit passwords through Google Forms, O O © O @) @ This form was created Inside of Alnukhba University College. Report Abuse Google FThe URL Connection class can be used to read and write data: Select one: a.To the specified resource referred by the HttpResponse and the URL b.To the specified resource referred by the URL c.To the specified resource referred by the HttpServer and the URL d.To the specified resource referred by the ServerSocket and the URLSuppose Alice, with a Web-based e-mail account (such as Hotmail or Gmail), sends a message to Bob, who accesses his mail from his mail server using POP3. Discuss how the message gets from Alice’s host to Bob’s host. Be sure to list the series of application-layer protocols that are used to move the message between the two hosts.
- 173. A protocol is a set of rules governing a time sequence of events that must take place a. between peers b. between an interface c. between modems d. across an interfaceSocket programming in c language in windows Implement one server and three clients using multithreaded exchanging messages between them and then doing checksum error detection or parityLet's imagine that a computer on the Internet transmits a packet to another computer at the network layer. The logical destination address of the packet has encountered an issue. What address should I use for the package? How will the original computer know when this happens?
- Consider a web page whose base file is of size S1 = 10 KB. Assume that the web page consists of N = 20 inline objects each of size S2 = 100 KB. Assume that the round-trip time to the web server is T = 100 ms and the bottleneck capacity is C = 10 Mbps. Ignore any packetization delays and header overhead.a. Assuming non-persistent HTTP is used with a single TCP connection, how long does it take to download the web page?b. Assuming non-persistent HTTP is used with 4 parallel TCP connections, how long does it take to download the web page?c. Assuming pipelined, persistent HTTP is used, how long does it take to download the web page? ”Pipelined” means requests for multiple objects can be sent back-to-back on the same connection.d. Assuming non-pipelined, persistent HTTP with 2 parallel TCP connections is used, how long does it take to download the web page? Assume that the 2 parallel connections equally share the total available bandwidth C.Answer the following: a) Rewrite the given IPv4 address using dotted-decimal notation and find the class. 01011110 10110000 01110101 00010101 b) Rewrite the given IPv4 address in binary representation and find the class.Modify the following code to use only ONE message queue for one server and multiple clients Computer Science

