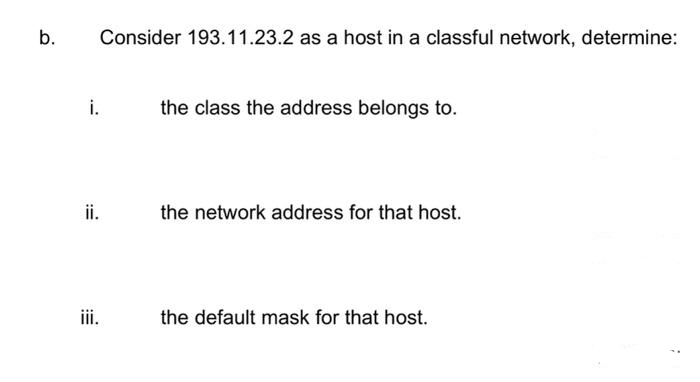
b. i. Consider 193.11.23.2 as a host in a classful network, determine: ii. the class the address belongs to. the network address for that host. the default mask for that host.
Q: The first stage is to identify a process inside an organisation that ha space for improvement.…
A: Defining, Measuring, Analyzing, Improving, and Controlling. A technique for improvement is DMAIC.…
Q: write a python function that replaces the None values with the average from that column. example:…
A: Step 1: In this function, I have created a list to store the result. Step 2: Next, I have iterated…
Q: HW12_4: Solve the system of nonlinear equations over the interval 0 ≤ t ≤ 0.03 using ode 45. Display…
A: Below I have provided a matlab program for the given question. Also, I have attached a screenshot of…
Q: Running in a x86 32bit machine, assume the values of register %ebp is 2076 and register %esp is 1028…
A: Below I have provided the solution to the given question
Q: What is an Azure Domain and how does it work? What precisely distinguishes the World Wide Web from…
A: The protection of people, hardware, software, networks, and data from physical actions and events…
Q: What other means of communication are there amongst people? Open a channel of communication. a…
A:
Q: What technical, organisational, and administrative challenges must be overcome during the creation…
A: Changes to the business's goals and metricsThe company must change its business goal and business…
Q: As a computer manufacturer, one of your key goals should be to create machines that are of great…
A: Introduction: A costly pre-made computer may frequently be built at home for a lot less money than…
Q: Explain how technological advancements have made it simpler for workers to interact inside…
A: Introduction: Internal communication refers to an organization's deliberate efforts to inform and…
Q: What benefits can clicks stream analysis provide to other businesses?
A: Due to utilisation, businesses may increase the advantages of clickstream analysis. Companies that…
Q: What is the precise purpose of the canvas element inside the HTML5 standard?
A: The CANVAS element is described as "...a resolution-dependent bitmap canvas, which may be used for…
Q: To be effective, a user interface (UI) must possess the following functional characteristics: Which…
A: Designing User Interfaces An element of a system where people and computers communicate is called a…
Q: What do you mean when you say "objectives of authentication"? Contrast the advantages and…
A: A server uses authentication to determine who is accessing their data or website when they need to…
Q: What role does contemporary technology play in the process of successful communication, and how is…
A: Introduction: The ability to communicate is the single most important factor in human life. A…
Q: please show work and explain how you did this
A: (pvq)^(!rv!q) is the given equation. Here we need to convert each Boolean operator into its…
Q: Why does Microsoft Access manage data more effectively than Microsoft Excel?
A: Microsoft Access manage data ; Microsoft Access is a database management system (DBMS) that combines…
Q: "Why are authorisation lists so susceptible to unauthorised modification that they must be encrypted…
A: Lists of authorizations are encrypted The user and the hardware are connected via the operating…
Q: How should businesses react when a security breach occurs?
A: Security lapses: An unrecognized and unauthenticated source might pose a hazard to an online…
Q: Problem: Conditional Create an algorithm that will display the average of all numbers divisible by 3…
A: We need to write flowchart and paeudo-code for given scenario.
Q: What type of reaction does the capacity analysis get when many processes are occurring…
A: The type of reaction does the capacity analysis get when many processes are occurring simultaneously…
Q: How far can we advance with the aid of authentication? In this part, we will evaluate the benefits…
A: Introduction: The process by which it is determined if something or someone is who or what they…
Q: Describe the meaning of "motion input" in your own words. Tell us about the many ways that motion…
A: Input based on motion: According to the first part of the question, we are supposed to talk about…
Q: What challenges do companies trying to migrate to a cloud platform face? What are the drawbacks and…
A: In the least difficult of terms, cloud relocation includes the most common way of moving significant…
Q: Let's describe software engineering first, then talk about why it's so important to create new…
A: introduction: Software engineering is a computer science subject that focuses on the design and…
Q: A1. Design a DFA for each of the following languages under the alphabet 2 = (0, 1). a1dfa1.jff = {w…
A: Deterministic finite automata (or DFA) are limited state machines that acknowledge or dismiss series…
Q: Explain how the capacity analysis reacts when a high number of processes are operating concurrently.
A: Introduction: For improved performance, concurrent processing uses many processors to carry out…
Q: Regarding effective communication, what role does modern technology play, and how is it utilised?
A: Introduction: The most crucial aspect of human existence is communication. Person civilization has…
Q: What is the relationship between the area of communications and the world of data communications?…
A: Telecommunication: It refers to the act of communicating with someone from a distance. Electronic…
Q: Compute and plot the derivative of the function f(x) = x³ • Apply the above methodology to compute…
A: Code :-
Q: The following explanation is given to help clarify the distinctions between SLA and HDD:
A: Recognizing SLA Service level agreements, or SLAs, are used. I t is a written agreement between a…
Q: What does it imply when a bit is activated and switched on in relation to a number? What does the…
A: statement: The most basic unit of data that may be stored in a computer is called a bit. The term…
Q: What other browsers have been produced since 1990, in addition to Google Chrome, Internet Explorer,…
A: Web browser: A web browser form enables you to look up and see websites on the Internet.…
Q: Using OOP, create a Python program that should output: Full Name : John Smith Likes : 500 Friends -…
A: Below I have provided a python program for the given question. Also, I have attached a screenshot of…
Q: terms of safety, how can the benefits and drawbacks of different forms of authentication be…
A: Please check the solution below
Q: Is the Internet a good resource for persons with mental or physical disabilities? What new…
A: Inspection: The internet is helpful for those who are blind. They now have access to the following…
Q: What precisely distinguishes the World Wide Web from the Internet?
A: Azure Domain: Azure Active Directory Domain Services (AD DS) provides managed domain services…
Q: a comprehensive explanation of the nature of a data warehouse Why was a data warehouse created in…
A: introduction: How to Avoid a Data Breach Whether or not a data breach has been reported, you should…
Q: Why is it of the utmost importance to guarantee that there are no data input mistakes while…
A: In today's world, data entry has become an important step in the process of streamlining databases.…
Q: What are the most significant advancements in communication technology that have occurred during…
A: Introduction: The development of the internet was the most important technological development in…
Q: Do you know how many steps are involved in creating a website from scratch? Describe the importance…
A: Introduction: In this section, we must describe each stage that makes up web design and why it is…
Q: Q2: Design an interface between 8086 CPU and two chips of 16K X 8 EPROM and two chips of 16K X 8 of…
A: Step 1: Total EPROM required = 64 KB Chip size available = 16 KB ∴Number of chips…
Q: v. Look at the following graph: G V₂ V6 V3 What color would you use for v5 so that it is a…
A: The question is related to graph theory.
Q: Why do people see the Internet as the apex of information and communication technology? Is it…
A: The answer of the question is given below
Q: What is the operation of an Azure Domain?
A: Using an Azure AD DS managed domain, you may run older apps in the cloud that cannot utilise modern…
Q: Include communications, hardware, and software in your discussion of the technological foundations…
A: Introduction: Information technology's foundations. Information technology (IT) is used by the…
Q: Design a Turing machine that will accept language (i) L = L(b* a) (ii) L = L((a+b) * b) (iii)…
A: A Turing machine is a numerical model of calculation portraying a theoretical machine that controls…
Q: 6. Look at the graph below. VI V2 V6 Yo. What is the order and what is the size of this graph? ii.…
A: As per our guidelines, only 3 sub parts will be answered. So, please repost the remaining questions…
Q: Are algorithms and data structures obsolete in the age of machine learning and artificial…
A: Data structures are still relevant today. since it serves as the basis for machine learning. When it…
Q: In consideration of your new system, discuss password management and the need of a strong password.
A: Systems development refers to the process of conceptualising, designing, developing, testing, and…
Q: What may improper indexing decisions result in?
A: What is improper indexing ? Improper indexing also referred to as Poor indexing is any SQL Server…
18
Step by step
Solved in 4 steps

- 4. [Socket] What is a socket? Suppose a process in Host C has a UDP socket with port number6789. Suppose both Host A and Host B send a UDP segment to Host C with destination portnumber 6789. Will both segments be directed to the same socket at Host C? If so, how will theprocess at Host C know that these two segments originated from two different hosts? 5. [Demultiplex] Define multiplexing and demultiplexing. Briefly explain how TCP demultiplexing isdifferent than UDP demultiplexing. 6. [rdt] Consider a reliable data transfer protocol that uses only negative acknowledgments.Suppose the sender sends data only infrequently. Would a NAK-only protocol be preferable to aprotocol that uses ACKs? Why? Now suppose the sender has a lot of data to send and the end-to-end connection experiences few losses. In this second case, would a NAK-only protocol bepreferable to a protocol that uses ACKs? Why?A classless address is given as 177.200.180.92/27. What will be the total number addresses available? 64 30 62 32 What is the first useable host address of 168.198.171.72/27? 168.198.171.64 168.198.171.94 168.198.171.65 168.198.171.95Consider the following page address stream: 2 1 4 3 5 3 2 4 5 2 1 2 4 3 1 Which of the following causes the most page faults to occur on a machine with 3 frames? Scheme that causes the most faults: a) First in First out b) LRU and FIFO are the same number of faults c) FIFO and Opitimal are the same number of faults d) All have the same number of faults e) Least Recently Used f) No faults occurs g) LRU and Optimal are the same number of faults h) Optimal NUMBER OF FAULTS CAUSED: a)
- ) s ®%74 I, 10.100.100.1is a valid host address * QO Yes O No -4 0 G 9:09 Which is not true about Class C addresses (select more than answer) * the first byte between 192 - 224 the number of hosts is less than subnets Many addresses are wasted the address space is 53687191 address the first byte starts with 110 Map the following addresses to its right class * 192.168.6.7 128.0.10.10 127.0.100.100 O O 'O 190.0.255.255 is a Class B special address * QO True Q False Back Next Never submit passwords through Google Forms, O O © O @) @ This form was created Inside of Alnukhba University College. Report Abuse Google FThe URL Connection class can be used to read and write data: Select one: a.To the specified resource referred by the HttpResponse and the URL b.To the specified resource referred by the URL c.To the specified resource referred by the HttpServer and the URL d.To the specified resource referred by the ServerSocket and the URLSuppose Alice, with a Web-based e-mail account (such as Hotmail or Gmail), sends a message to Bob, who accesses his mail from his mail server using POP3. Discuss how the message gets from Alice’s host to Bob’s host. Be sure to list the series of application-layer protocols that are used to move the message between the two hosts.
- 173. A protocol is a set of rules governing a time sequence of events that must take place a. between peers b. between an interface c. between modems d. across an interfaceSocket programming in c language in windows Implement one server and three clients using multithreaded exchanging messages between them and then doing checksum error detection or parityLet's imagine that a computer on the Internet transmits a packet to another computer at the network layer. The logical destination address of the packet has encountered an issue. What address should I use for the package? How will the original computer know when this happens?
- Consider a web page whose base file is of size S1 = 10 KB. Assume that the web page consists of N = 20 inline objects each of size S2 = 100 KB. Assume that the round-trip time to the web server is T = 100 ms and the bottleneck capacity is C = 10 Mbps. Ignore any packetization delays and header overhead.a. Assuming non-persistent HTTP is used with a single TCP connection, how long does it take to download the web page?b. Assuming non-persistent HTTP is used with 4 parallel TCP connections, how long does it take to download the web page?c. Assuming pipelined, persistent HTTP is used, how long does it take to download the web page? ”Pipelined” means requests for multiple objects can be sent back-to-back on the same connection.d. Assuming non-pipelined, persistent HTTP with 2 parallel TCP connections is used, how long does it take to download the web page? Assume that the 2 parallel connections equally share the total available bandwidth C.Answer the following: a) Rewrite the given IPv4 address using dotted-decimal notation and find the class. 01011110 10110000 01110101 00010101 b) Rewrite the given IPv4 address in binary representation and find the class.Modify the following code to use only ONE message queue for one server and multiple clients Computer Science

