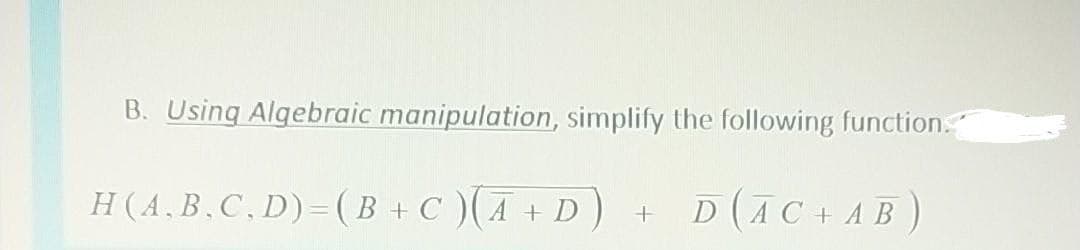
B. Using Algebraic manipulation, simplify the following function." H(A.B.C,D)=(B +C )(A + D) D (AC + AB)
Q: A map interface's list collection views
A: Introduction: A map is a way of storing information in essential and valuable affiliation. Both the…
Q: 2. During the summer months, a rental agency keeps track of the number of speedboats rented each day…
A: I am giving handwritten explanation. See below steps.
Q: It is necessary to explain how DDoS attacks use botnets and how they are built.
A: Intro The points below may be utilized to build a botnet: Prepare host systems to discover the…
Q: The network layer protocol is required to provide packetizing services to the transport layer for…
A: Introduction The purpose of transport layer is to provide communication services between two…
Q: Is it possible to distinguish between on-premises and cloud-based network services and applications?
A: Cloud computing differs from on-premises software in one critical way.
Q: event simulation
A: Discrete event simulation is a strategy used to portray the many kinds of processes in a given…
Q: Why is it advantageous to store and analyze data on the cloud?
A: Store and Analyze data: Data is transported and kept on distant storage systems, where it is…
Q: Compare and contrast a firewall with a stream of packetized data.
A: Firewall: Stateful firewalls may track and protect depending on traffic patterns and flows by…
Q: Computer science What are the Characteristics of the Media Access Control (MAC)?
A: Introduction: What are the Characteristics of the Media Access Control (MAC)?
Q: When you think about email, what images come to mind? What is the path an email takes once it is…
A: Emails are delivered extremely fast when : It is defined as a process of service that allows us to…
Q: You have been asked to write a program that will allow your client Tigger Movie Rentals to keep…
A: #This function lists all the inventory names from the file.def display():with open("movies.txt") as…
Q: Create a c++ program that ask user for a certain number and display all prime numbers from 1 to that…
A: Algorithm: for (initialExpression; testExpression; updateExpression){ // body of the…
Q: A PRIME number is a number whose factors are one and it itself. A COMPOSITE number is a number with…
A: I have provided C CODE along with CODE SCREENSHOT and also provided OUTPUT…
Q: We'll demonstrate how to construct a botnet and how to use it in a DDoS attack in this post.
A: Introduction: The following points may be used in the construction of a botnet:
Q: What are your thoughts on programming in general? Is it pleasurable? Is it a difficult task? Is it a…
A: Summary Programming is fun
Q: Antivirus software is used to keep the computer safe from malicious threats. False or true.
A: Introduction: In order to swiftly discover and destroy malware, antivirus systems and computer…
Q: Computer science Short answer What are Synchronizing transmissions?
A: Introduction: What are synchronizing transmissions?
Q: Why is the foreign key crucial for database integrity? Can you come up with a scenario to…
A: Introduction: Foreign keys are very important in database architecture. Using references to ensure…
Q: In a few words, describe two well-known recommended practices for IP models. Compare these…
A: IP considerations: In today's commercial world, intellectual property has become an increasingly…
Q: Why does an operating system often provide dedicated calls for accessing directory entries?
A: The following are some of the procedures that may be performed on directories: The working directory…
Q: What are the four main reasons why continuous event simulation is so important?
A: Four reasons of importance of continuous event simulation are: -> Helps in smooth flow of…
Q: Create a C++ program that will ask for a certain number and display all prime numbers from 1 to that…
A: In this question we have to display all prime number from 1 to given input number. we know that a…
Q: How are mainframe and laptop operating systems fundamentally different? Do the two have any…
A: Introduction: The mainframe OS is a network operating system that allows a computer to execute…
Q: What are the differences in formation security and risk management between the perimeter network and…
A: Intro Network: A network perimeter is a secure boundary between a network's private and locally…
Q: The DNS is taught in detail, including iterated and united queries, authoritative and root servers,…
A: Introduction: DNS is a global programme that converts IP addresses into human-readable domain names.…
Q: Assume you are a systems analyst tasked with developing a thorough test strategy. Describe the…
A: Intro This question deals with imagination is the key to building a complete test plan. How will…
Q: It is unclear how a single individual might coordinate a distributed denial of service attack.
A: A distributed denial of service (DDoS) assault is one in which a gang utilizes numerous hacked…
Q: The statement [ Dim a (20) As String] its mean in visual basic .net
A: In step 2, I have provided answer ... In further steps , I have provided a visual basic…
Q: Create a 4-bit adder that includes: 1. Truth Table 2. Block diagram 3. IC used 4. Final Circuit…
A: 4 bit adder: 1.truth table: carry in A B sum carry out 0 0 0 0 0 0 0 1 1 0 0 1 0 1 0 0 1…
Q: yberloafing?
A: Cyberloafing is customarily likened to with nothing to do at work or dawdling, consequently it is…
Q: What can you do to avoid a repeat of this situation in the future?
A: A situation is a combination of circumstances At a particular point in time. In other words, it can…
Q: This DDoS attempt will be examined using security engineering techniques.
A: Introduction: Engineering for security: The act of integrating security measures into an information…
Q: How do you envision email in your mind? What's the best way to move an email around? Write down what…
A: When it comes to corporate communication, email is a vital tool since it is quick, inexpensive,…
Q: message with a secret code (integer number) is passed to the higher official in Army to intimate a…
A: Answer :
Q: Contrast a firewall with a packetized data flow.
A: Beginning: A data packet is a unit of data that is compressed into a single package and sent through…
Q: When connecting a phone line to a communication adapter, why do you need a modem?
A: Modem A modem consists of just two parts: a modulator and a demodulator. It converts digital signals…
Q: What instruction format is this? (one letter) Write out the full instruction in MIPS assembly…
A: What instruction format is this? (one letter) --> There are three instruction categories:…
Q: Give an example of a Named Entity Recognition application. In the context of the reference…
A: Information extraction systems: Named entity recognition focuses on determining the specific meaning…
Q: service (SaaS
A: Software as a service (SaaS) is a software authorizing and conveyance model in which software is…
Q: Is it good or damaging to use a peer-to-peer network?
A: Introduction: A peer-to-peer network is scalable because the addition of a new user has no effect on…
Q: Computer science Shrot answer What is User Datagram Protocol (UDP)?
A: Intro User Datagram Protocol (UDP) is a connection-less protocol where there is no connection is…
Q: What is an artificial neural network, and how does it work?
A: Origination: They are designed to digitally replicate the human brain. These networks may be…
Q: Summarize the following in three lines: Manchester codes (what/why/advantages/disadvantages)
A: Introduction WHAT ARE MANCHESTER CODES: Manchester codes are basically the line codes in which the…
Q: What do you think computers' function in the economy will be? What are the economic consequences of…
A: The phrase "cloud computing" (sometimes spelled "cloud computing") refers to a kind of…
Q: Demonstrate that if a relation contains no property that is functionally determined by all of the…
A: Introduction Show that if a relation has no attribute that is functionally determined by all the…
Q: A phone line is connected to a communication adapter through a modem. To what end is this equipment…
A: Communication: A modem sends data by modulating one or more carrier wave signals to encode digital…
Q: Is it Possible to Define System Characteristics?
A: Start: The system is a linked and designed collection of interdependent components that work…
Q: Computer sciencei.Explain the three persistence protocols that can be used with CSMA.
A: The Answer is in Below steps
Q: Explain the notion of Instruction Set Architecture (ISA) in detail.
A: Answer :
Q: Computer Rev
A: The Industrial Age is a time of history that incorporates the progressions in financial and social…
Step by step
Solved in 2 steps

- What is wrong with the following C++ function? void Maximum(int a, int b, int& max) { if (a > b) max = a; else max = b; return max; }Problem 3. write a C++ function that finds as many primes of the form 2n + 1, where n is a positive integer, as you can.-Functions Write a function int nth_Prime(int x) in C++ that takes a parameter x and returns nth prime number.
- Complete the C++ Function as per the question soon as possible.3. When using an ellipsis in a function (i.e., x <- function(...), how can you compare the lengths of the arguments? I'm having difficulty formulating this code in a simple way. I want the function to print "TRUE" if the arguments are the same length.Answer the given question with a proper explanation and step-by-step solution. This code it good but I have to use the def pig7 function...
- program demonstrates how this function works.Write a C++ function to find nth term of sequence given below, n is passed as argument to the function and function prints the nth term in output. Sequence: 1,4,9,16,25,........n2Write a c++ function to find a digit whose frequency is maximum.Function Prototype: void maxFrequencyOfNumber(int num,int & digit, int &maxFreq); Take input of number from user and output the digit and maxFreq.
- write this using javascript and arrow functionsWrite a function that gets two integer parameters between 1 and 100 and prints their common factors (divisors). need urgent answer.. in c++Write a C function that returns the sum of the following series for n terms ( x ( double ) and n ( int ) are function parameters

