B3 A3 B A Cin Full Adder Cout S B₂ A₂ B A Cin Full Adder Cout S B₁A₁ B A Cin Full Adder Cout S Во A B A Cin Full Adder Cout S Cin 40
Q: When it comes to cloud security, what is the "shared responsibility" paradigm like?
A: Answers:- Cloud security:- The Cloud security is a refers to the technologies and policies to the…
Q: State applications of deep learning.
A: Lets see the solution.
Q: In a three-tier design, the intermediate layer between the database and the client servers is…
A: Introduction: This question tells about The most appropriate option is to use an application server.
Q: When it comes to cloud security, what is the "shared responsibility" paradigm like?
A: Answer: The industry has coined the term "Shared Responsibility" to describe the tasks and…
Q: What kind of worries and challenges arise from the use of an unintegrated information system?
A: These question answer is as follows,
Q: Apex Assignment: Create a apex class called addition and then create a method to add the 2 integer…
A: What exactly is Apex in Salesforce? Salesforce Apex is an object-oriented and strongly…
Q: Detail the components of the spheres of security paradigm. The document must have a sufficient…
A: Introduction: Information security is primarily concerned with preventing unauthorized access to…
Q: What is the catastrophe recovery process's principal objective?
A: Introduction: Catastrophe recovery/ Disaster recovery: Disasters such as fire, flooding, terrorist…
Q: What is the process through which a virtual network interface card (VNIC) obtains a MAC address?
A: According to the question advanced organization interface playing a card game (vNICs) are virtual…
Q: What measures should be followed to assure the stability and availability of a local area network?
A: Introduction: In computing, a local area network (LAN) collects small computers or other workstation…
Q: Write a complete C++ program that asks the user to input information for at least 10 students. Use…
A: Solution: Given, Write a complete C++ program that asks the user to input information for at…
Q: 1. Truth Table Construct a truth table for the following: a) F(X,Y,Z) = Y'Z + XZ + XOO O OLL 0 0 0 1…
A: Truth Table:-A truth table deconstructs a logic function by enumerating all potential values it…
Q: create a new database (named MyUniversity), the creation (using the CREATE command) should be done…
A: Code: create database MyUniversity; use MyUniversity; create table Student ( sid int PRIMARY KEY,…
Q: Which of the following will produce a series of integers ranging from 2 to 9 and output them to the…
A: 1) Using for loop and range function To loop through a set of code a specified number of times, we…
Q: Which of the following will be considered "true" in an if statement? Select one or more: O a. -1 O…
A: If statement is an example of conditional structures in any programming language.
Q: Full explain this question and text typing work only thanks Show that the language is context…
A: Context-free grammar:- To create every conceivable string in a given formal language, context free…
Q: When it comes to cloud security, what is the "shared responsibility" paradigm like?
A: 1) Cloud security is a responsibility that is shared between the cloud provider and the customer. 1)…
Q: Prove that any LP optimization problem can be transformed into the following form: minimize 0 ·…
A: Duality is the most important concept in linear programming. Duality makes this possibleprovide a…
Q: Directions: • Create a C++ program for the case problem below. • Encode and run the program in Dev…
A: C++ program to solve the given problem is below.
Q: Typically, a BUS consists of multiple communication paths or lines. Each line is capable of…
A: A bus is collection of wires that connects computer components. Buses carries information in form of…
Q: --Problem -3 -Create a flowchart design that depicts the solving of the following problem: Asks user…
A: Step-1: Start Step-2: Declare variables a,b and c, and take input from the user Step-3: If a is…
Q: Assume a computer has two network interface cards, NIC1, a Wifi USB, and NIC2, an on-board Ethernet.…
A: Your answer is given below.
Q: Insertion Sort Original Array = {150,8,55,78,91,10} iCE) && (k >=0) list[k+1]=list[klist[k+1]=CE;…
A: Insertion sort:- It is the simple sorting algorithm in which the arrays are virtually split into…
Q: Assign a name to the graphics processing unit.
A: Introduction: A graphics processing unit -GPU is a computer processor specifically designed to…
Q: The several methods of file access are listed here. I'm wondering about the benefits and drawbacks…
A: Introduction: The most basic file access method is: File organization is nothing more than gathering…
Q: When it comes to cloud security, what is the "shared responsibility" paradigm like?
A: Cloud Security: Cloud security, often referred to as cloud computing security, is a group of…
Q: an by digital envelop
A: Solution - In the given question, we have to tell what is mean by digital envelope and also explain…
Q: What is the catastrophe recovery process's principal objective?
A: Introduction: Catastrophe recovery/ Disaster recovery: Disasters such as fire, flooding, terrorist…
Q: How do i grab specific bits from a 32 bit nu
A: The answer is
Q: Could you please assist me with this problem? Thank you.
A: In the above program, in the "first" module, the "second" module has been imported. In the "main"…
Q: Project 2: You have to create a program in C language in which the user enters the mass M and length…
A: The moment of inertia of a rod about an axis through its center and perpendicular to it is =…
Q: Step 5: Write a function that takes two dictionaries as arguments. The function should determine if…
A: As per our company's policy, we are supposed to answer only the first question. However, I have…
Q: 1. Truth Table
A: the answer to the following question:-
Q: 1. In a BST, if the right sub tree is not empty, then the successor is The maximum in the left sub…
A: Basically, we find the successor of any node in the Binary Search Tree then we find a just larger…
Q: Provide me with the Matlab code to swap the second and third rows of the matrix given below, m=987…
A: Requirement: Write a MATLAB program to swap the second and third rows of the matrix given below, m =…
Q: Write detailed code for Fibonacci sequence number print in go programming language code and give…
A: Logic:- define a function for Fibonacci series display. Set p=0, q=1 and r=q
Q: Explain what Unix data structures are affected when an open() call is used on a device file. How is…
A: The question is on what Unix data structures are affected when an open() call is used on a device…
Q: Define a function with the prototype void show_binary(int); that consumes a positive integer and…
A: These question answer is as follows,
Q: Write a C program using switch statement. The program will read a character (op) and will calculate…
A: Explanation 1) Below is C Program using switch statement to read a character(op) and calculalate and…
Q: Write a JAVA program in which the user enters the initial velocity u, time of travel t, and the…
A: Code and output is in next step:
Q: What are the applications of Subneting?
A: Subnetting is a process of separating a single physical network into several logical subnetworks.
Q: Question 1: Building a simple personal profile HTML page Specifications: 1. Your personal profile…
A: The answer is given below.
Q: Include the header file fstream in the program.2.Declare file stream variables.3.Associate the file…
A: ALGORITHM:- 1. Take input from the user and store it in the file using ofstream object. 2. Then read…
Q: How crucial is software development? Four more characteristics, in your opinion, should be…
A: Introduction: Software development's ability to create and provide value to its users cannot be…
Q: Specify the architecture of a computed unified device.
A: Specify the architecture of a computed unified device.
Q: Write a PHP code to the total current for the intrinsic semiconductor after taking current due to…
A: Required:- Write a PHP code to get the total current for the intrinsic semiconductor after taking…
Q: 1.Data pre processing 2.Data visualization 3. Machine learning
A: dtailed answer is given in next steps:
Q: Write a PHP code to the total current for the intrinsic semiconductor after taking current due to…
A: Introduction: In this question, we are asked to write a PHP program to print the total current.
Q: What measures should be followed to assure the stability and availability of a local area network?
A: Introduction: In computing, a local area network (LAN) collects small computers or other workstation…
Q: Write a Python program to read input an integer z and then generate a random value r in the range…
A: Hi. Let's move on to the code in the next step. I have included comments in the code that will help…
write a DETAILED (about a paragraph or two) description of the circuit function, Circuit diagram. *picture provided*
explain whats happening, and why (if possible). include what toggling means, and where it's happening as well as what it's causing. also include what the carry out/in are doing.
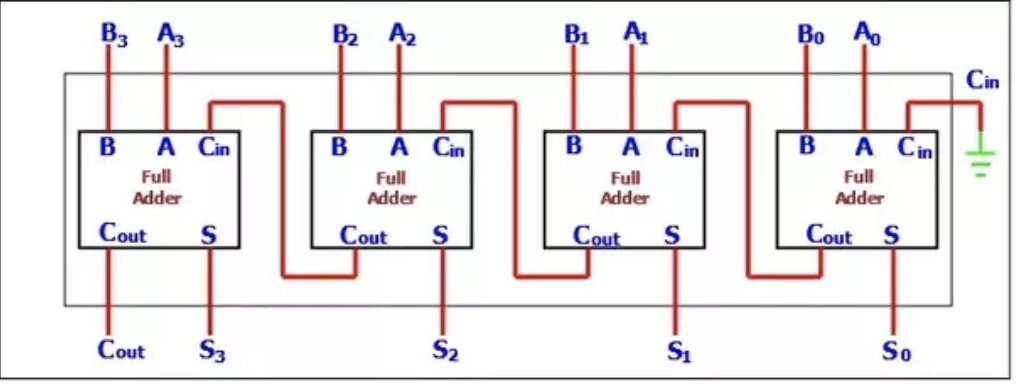
Step by step
Solved in 2 steps

- Correct answer will be upvoted else Multiple Downvoted. Don't submit random answer. Computer science. You have n particular focuses (x1,y1),… ,(xn,yn) on the plane and a non-negative integer boundary k. Each point is a tiny steel ball and k is the draw in force of a ball when it's charged. The draw in power is something very similar for all balls. In one activity, you can choose a ball I to charge it. When charged, all balls with Manhattan distance all things considered k from ball I move to the situation of ball I. Many balls may have a similar facilitate after an activity. All the more officially, for all balls j with the end goal that |xi−xj|+|yi−yj|≤k, we dole out xj:=xi and yj:=yi. An illustration of an activity. Subsequent to charging the ball in the middle, two different balls move to its position. On the right side, the red dab in the middle is the normal situation of those balls. Your errand is to observe the base number of activities to move all balls to a similar…Correct answer will be upvoted else downvoted. Computer science. few dishes go poorly with one another. There are m1 sets of first courses and second courses that go poorly with one another, m2 sets of second courses and beverages, and m3 sets of beverages and pastries that turn out poorly with one another. Ivan needs to purchase precisely one first course, one second course, one beverage, and one pastry so they work out in a good way for one another, and the absolute expense of the supper is the base conceivable. Assist him with tracking down the least expensive supper choice! Input The primary line contains four integers n1, n2, n3 and n4 (1≤ni≤150000) — the number of kinds of first courses, second courses, beverages and treats, individually. Then, at that point, four lines follow. The primary line contains n1 integers a1,a2,… ,an1 (1≤ai≤108), where simulated intelligence is the expense of the I-th kind of first course. Three next lines indicate the expenses of second…A board game has the following layout (see image) a) draw a finite state machine diagram representing the playing of this game for one player. For input, use '1' for heads and '0' for tails. There is no output. b) Construct the corresponding truth table.
- Lesson: Application of Computer Graphics Given an orthographic camera with direction d, up u, and center c properties (size is fixed to 1), show the formula for generating a ray for point (x, y) in the screen (0,0 <= x, y <= 1,1). Remember, a ray has an origin and a direction.Consider the diagram of Figure 2.16. A robot is set up 1 meter from a table. The tabletopis 1 meter high and 1 meter square. A frame o1x1y1z1 is fixed to the edge of the table asshown. A cube measuring 20 cm on a side is placed in the center of the table with frameo2x2y2z2establishedatthecenterofthecubeasshown.Acameraissituateddirectlyabovethe center of the block 2m above the tabletop with frame o3x3y3z3 attached as shown.Find the homogeneous transformations relating each of these frames to the base frameo0x0y0z0.Findthehomogeneoustransformationrelatingtheframeo2x2y2z2tothecameraframeo3x3y3z3. *** Note – Draw the frame rotations wherever necessary from the starting to destination frame.Correct answer will be upvoted else downvoted. Computer science. Homer preferences exhibits a great deal. Today he is painting a cluster a1,a2,… ,a with two sorts of tones, white and dark. A work of art task for a1,a2,… ,an is depicted by a cluster b1,b2,… ,bn that bi shows the shade of simulated intelligence (0 for white and 1 for dark). As indicated by an artwork task b1,b2,… ,bn, the exhibit an is parted into two new clusters a(0) and a(1), where a(0) is the sub-succession of all white components in an and a(1) is the sub-arrangement of all dark components in a. For instance, assuming a=[1,2,3,4,5,6] and b=[0,1,0,1,0,0], a(0)=[1,3,5,6] and a(1)=[2,4]. The number of portions in a cluster c1,c2,… ,ck, indicated seg(c), is the number of components if we consolidate all neighboring components with a similar worth in c. For instance, the number of portions in [1,1,2,2,3,3,3,2] is 4, in light of the fact that the exhibit will become [1,2,3,2] in the wake of combining contiguous…
- Correct answer will be upvoted else downvoted. Computer science. Michael is blamed for disregarding the social removing rules and making a danger of spreading Covid. He is currently shipped off jail. Fortunately, Michael knows precisely what the jail resembles from within, particularly since it's actual straightforward. The jail can be addressed as a square shape a×b which is separated into stomach muscle cells, each addressing a jail cell, normal sides being the dividers among cells, and sides on the border being the dividers prompting opportunity. Prior to condemning, Michael can ask his companions among the jail representatives to make (all around stowed away) openings in a portion of the dividers (counting dividers among cells and the furthest dividers). Michael needs to have the option to escape the jail after this, regardless of which cell he is set in. Be that as it may, he likewise needs to break as couple of dividers as could be expected. Your assignment is to…1. What symbol is not recognized in base 7? a. 4 b. 5 c. 6 d. 7 2. Which case uses deductive reasoning? (A)Tell me who your friends are and I will tell you who you are (B) Tell me who you are and I tell you who your friends are (C) That male ape is from the Amazon. He is intelligent. All male apes fromthe Amazon jungle are intelligent. (D)Allan is intelligent. He belongs to De La Cruz clan. All members of the De La Cruz clan are intelligent. 3. Statement that is derived from axioms by strict logical proof a. axiom b. conjecture c. theorem d. numeracyComputer science. Correct answer will be upvoted else downvoted. Phoenix can pay one dollar to the sock store to all things considered: recolor a sock to any tone c′ (1≤c′≤n) transform a left sock into a right sock transform a right sock into a left sock The sock store might play out every one of these progressions quite a few times. Note that the shade of a left sock doesn't change when it transforms into a right sock, as well as the other way around. A coordinating with pair of socks is a left and right sock with a similar shading. What is the base expense for Phoenix to make n/2 coordinating with sets? Each sock should be remembered for precisely one coordinating with pair. Input The input comprises of numerous experiments. The principal line contains an integer t (1≤t≤1000) — the number of experiments. The primary line of each experiment contains three integers n, l, and r (2≤n≤2⋅105; n is even; 0≤l,r≤n; l+r=n) — the all out number of socks, and the number…
- Acne is a very common skin disorder ___ most young people get in early adolescence a) O for which b) O when c) O in which d) O that e) O whereCorrect answer will be upvoted else Multiple Downvoted. Computer science. Petya coordinated a peculiar birthday celebration. He welcomed n companions and relegated an integer ki to the I-th of them. Presently Petya might want to give a present to every one of them. In the close by shop there are m one of a kind presents accessible, the j-th present expenses cj dollars (1≤c1≤c2≤… ≤cm). It's not permitted to purchase a solitary present more than once. For the I-th companion Petya can either get them a present j≤ki, which costs cj dollars, or simply give them cki dollars straightforwardly. Assist Petya with deciding the base all out cost of facilitating his get-together. Input The originally input line contains a solitary integer t (1≤t≤103) — the number of experiments. The main line of each experiment contains two integers n and m (1≤n,m≤3⋅105) — the number of companions, and the number of interesting presents accessible. The accompanying line contains n integers…Correct answer will be upvoted else Multiple Downvoted. Computer science. There is an endless 2-dimensional framework. The robot remains in cell (0,0) and needs to arrive at cell (x,y). Here is a rundown of potential orders the robot can execute: move north from cell (i,j) to (i,j+1); move east from cell (i,j) to (i+1,j); move south from cell (i,j) to (i,j−1); move west from cell (i,j) to (i−1,j); stay in cell (i,j). The robot needs to arrive at cell (x,y) in as couple of orders as could really be expected. In any case, he can't execute a similar order at least twice in succession. What is the base number of orders needed to reach (x,y) from (0,0)? Input The main line contains a solitary integer t (1≤t≤100) — the number of testcases. Every one of the following t lines contains two integers x and y (0≤x,y≤104) — the objective directions of the robot. Output For each testcase print a solitary integer — the base number of orders needed for the robot to…



