Based on Figure 10-35 shown on page 793, which of the following statements is NOT true? O Server 2 does not know that /projects has been mounted by Client 1 and Client File "c" on server 2 can be accessed by Client 1 as /usr/ast/work/proj1/c O Although Client 1 mounts the bin directory of Server 1 remotely on its own bin directory, this bin directory is treated as a local directory for Client 1 O File "d" on server 2 can be accessed by Client 2 as /mnt/projects/proj2/d
Based on Figure 10-35 shown on page 793, which of the following statements is NOT true? O Server 2 does not know that /projects has been mounted by Client 1 and Client File "c" on server 2 can be accessed by Client 1 as /usr/ast/work/proj1/c O Although Client 1 mounts the bin directory of Server 1 remotely on its own bin directory, this bin directory is treated as a local directory for Client 1 O File "d" on server 2 can be accessed by Client 2 as /mnt/projects/proj2/d
Chapter13: Internet And Distributed Application Services
Section: Chapter Questions
Problem 4VE
Related questions
Question
Transcribed Image Text:Based on Figure 10-35 shown on page 793, which of the following statements is
NOT true?
O Server 2 does not know that /projects has been mounted by Client 1 and Client
2
File "c" on server 2 can be accessed by Client 1 as /usr/ast/work/proj1/c
O Although Client 1 mounts the bin directory of Server 1 remotely on its own bim
directory, this bin directory is treated as a local directory for Client 1
File "d" on server 2 can be accessed by Client 2 as /mnt/projects/proj2/d
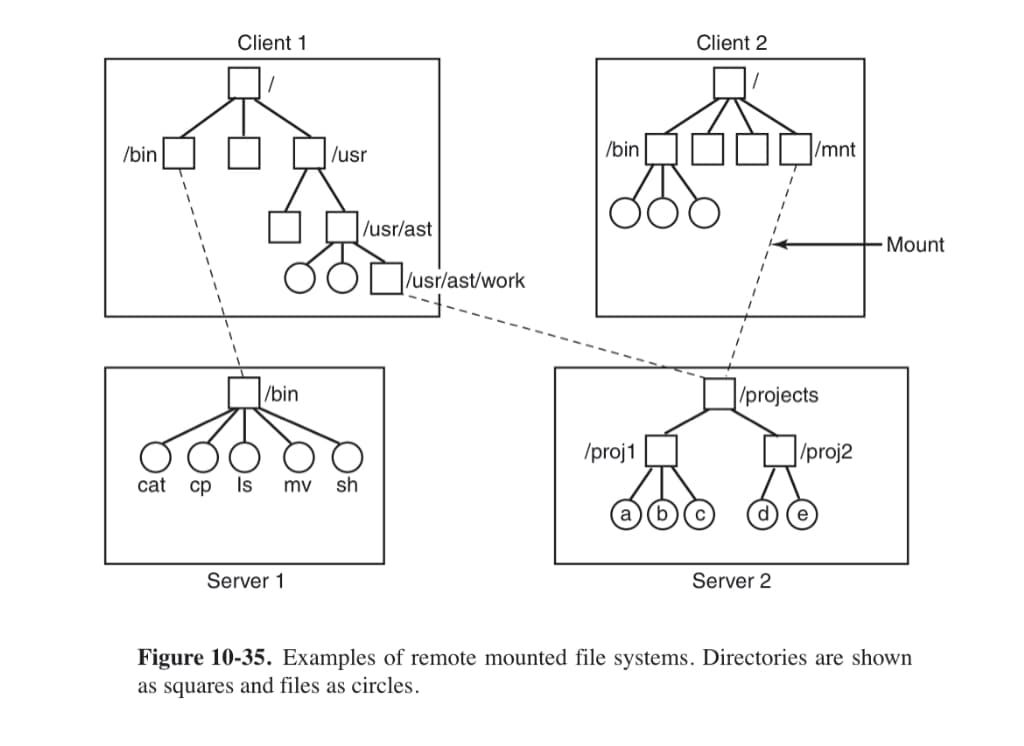
Transcribed Image Text:Client 1
Client 2
/bin
/usr
/bin
/mnt
/usr/ast
Mount
/usr/ast/work
/bin
/projects
/proj1
|/proj2
cat
ср
Is
mv
sh
Server 1
Server 2
Figure 10-35. Examples of remote mounted file systems. Directories are shown
as squares and files as circles.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L