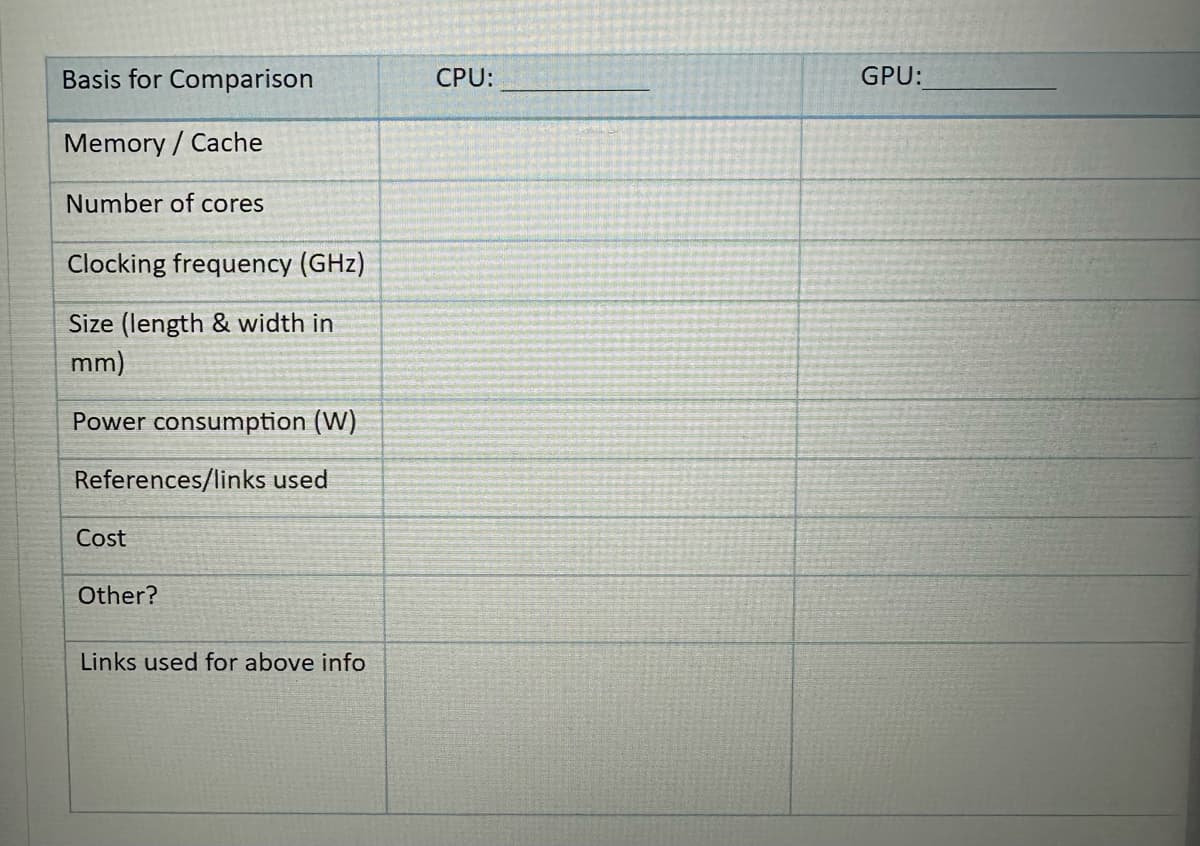
Basis for Comparison Memory / Cache Number of cores Clocking frequency (GHz) Size (length & width in mm) Power consumption (W) References/links used CPU: GPU:
Q: Which information system at your school irritates or challenges you the most? Describe a system that…
A: Introduction: Yes, I like taking long road trips. I thus employ various information technologies,…
Q: Contrast the dangers and attacks that may be encountered in the realm of information security. Give…
A: Information security refers to the protection of sensitive and confidential information from…
Q: how do i zip a folder with code in python?
A: To compress individual files into a ZIP file, create a new ZipFile object and add the files you want…
Q: Because microprocessor CPUs do not understand mnemonics as they are, they have to be converted to…
A: Microprocessor: A microprocessor is an integrated circuit (IC) that contains the central processing…
Q: Karen Smith is one of those gifted teens with the power of ESPN. For us normal people, this skill is…
A: Two versions of the same code is given below You can use either of them
Q: How would you characterize danger in terms of the software framework? Can you think of anything more…
A: Network operating systems are designed for switches, routers, and firewalls (NOS). It can help you…
Q: An HRD interventionist should educate the school that a training requirements analysis is essential…
A: The following information is presented as given: As an HRD interventionist, you should advise a…
Q: For what reason are databases often called the "grandmother of all software programs"? To what end…
A: Database as the womb of computer programs We deal with a sizable volume of data for all computer…
Q: Write a java application that has three Buttons labeled: Red, Green, and Blue. The java application…
A: Please refer to the following steps for the complete solution to the problem above.
Q: this C++ code is pre-existing and cannot be changed or modified. for it to work, the program has to…
A: Solution: Given, #include <iostream>#include <vector>using namespace std; int main() {…
Q: In Figure 13.8, what are the common subsequence of X and Y having length six? (Select all that…
A: 1. Given X = GTTCCTAATA Y = CGATAATTGAGA We need to find the common subsequence of X and Y having…
Q: IN C# I need to Write a program named InputMethodDemo2 that eliminates the repetitive code in the…
A: - We need to code for the InputMethod and DataEntry functions to accomplish the goals.
Q: How does the FIFO's consistency compare to that of the CPU?
A: Introduction: Each writing task is divided into smaller units so that reading may start…
Q: lid understanding of both the end objective and the processes involved in a release process. What…
A: Version control The ability to handle and trace each version of a file from a centralized location…
Q: If you work for a medium-sized company, you probably have at least three more departments outside…
A: The response is provided below: The purpose of having broad plans in place is to provide clarity to…
Q: How do Boolean expressions work? What are they used for?
A: What does a Boolean expression actually mean? A logical assertion that can only be TRUE or FALSE is…
Q: Describe ebool format.
A: An eBook is a reflowable and non editable book which is converted into the digital format and this…
Q: Deep packet inspection is a feature that is becoming common in contemporary firewalls.
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: Commonly used diagnostic and management tools for networks are available. If a workstation is having…
A: OSI: OSI stands for Open Systems Interconnection. It is a seven-layer model for communication…
Q: Determine the differences between the two kinds of network layer firewalls.
A: A firewall is a network security device that analyses all incoming and outgoing traffic and accepts,…
Q: "What are some of the components of an all-encompassing cyber security strategy?
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: Do you prefer using your computer in batch mode or interactive mode? Clearly describe utilizing…
A: Batch: Comparatively demanding jobs are gathered and moved through the PC as a group by a job…
Q: From what does a firewall protect a network? The process of filtering packets follows certain…
A: A firewall is a security system that monitors and controls the incoming and outgoing network traffic…
Q: The microkernel of the operating system is accessible for any design criteria that may be required.…
A: Microkernel Approach: The microkernel approach is a design strategy that separates the essential…
Q: Using an operating system, you can make, look at, and manage files and directories on a computer's…
A: Introduction: An operating system (OS) is a software program that manages the hardware and software…
Q: Analyze how well and how often your social skills were put to play throughout the preparation and…
A: INTRODUCTION: In daily life, it's how we communicate—speaking, listening, walking, looking,…
Q: It is possible to conduct an evaluation of the usability of the online pharmacy system by employing…
A: Cognitive walkthrough is a technique used in usability evaluation that focuses on understanding how…
Q: Do you believe that improved communication across departments will lead to increased performance in…
A: Reverse logistics can help you identify ways to reuse, resell or recycle materials that would…
Q: What other types of characters and strings are available for use in Java?
A: In Java, the basic data types available for representing characters and strings are: char: A…
Q: As an operating system designer, what should you keep in mind when making a microkernel? How…
A: Introduction: Kernel mode is required for a certain CPU command.Privilege instruction. They allow…
Q: TODO 11 Using the clean_df split our columns into features and labels. Index/slice our…
A: In this task, the goal is to split the clean_df DataFrame into two separate variables y and X: y is…
Q: When a security breach occurs, what measures should be done by an organization?
A: Intro Security Breach: This occurs when an organization's basic security measures are disregarded,…
Q: Do you have any experience with the concept of "polymorphism"?
A: Polymorphism: An instruction instructs the item to carry out a specific action. On two separate…
Q: Explain to me in detail what the capabilities of the AWS information system are.
A: A wide range of information technology services are offered via the cloud computing platform known…
Q: What exactly is meant when people talk about "release techniques"? What exactly is the big issue…
A: The definition of a release approach is the subject at hand. What use does version control serve?…
Q: Using a combination of popular diagnostic software and troubleshooting resources, network problems…
A: Understand router operation. Routers transport data packets between networks. Wireless access point.…
Q: Is there a particular reason why a release process has to be followed? What exactly is version…
A: What is a release process for, and how does it operate? Why is version control necessary, and what…
Q: To start, what exactly is meant by the term "Software Configuration Management"?
A: Explanation A technique used in software engineering called Software Configuration Management (SCM)…
Q: When it comes to the analytical process, what part does data modeling play, and how significant is…
A: Data modeling makes it easier for developers, data architects, business analysts, and other…
Q: What are three ways to sense check keywords? Ask whether the terms will add commercial value Ask…
A: Please refer to the following step for the complete solution to the problem above.
Q: If the python interperter only calls functions when they are called, and if some functions contain…
A: Yes, calling functions within functions can slow down the performance of executing a program, as…
Q: What are some additional kinds of firewalls besides those that are based on routers?
A: In addition to firewall systems based on routers, there are several other types of firewalls…
Q: Suppose you have a RISC machine with a 2.7 GHz clock (i.e., the clock ticks 2.7 billion times per…
A: Please refer to the following step for the complete solution to the problem above.
Q: List the several subfields that lie under the umbrella of security, and elaborate on each with an…
A: information protection It speaks of safeguarding data from unapproved access, theft, damage,…
Q: Make an algorithm for using an ATM to withdraw money.
A: Money-withdrawal algorithm at an ATM: Let's now examine how to use an ATM to withdraw cash. Put ATM…
Q: TODO 1 Let's load the forestfires.csv by using Pandas read_csv() function. The read_csv() function…
A: Introduction Pandas: Pandas is just a Library for python to manipulating and analyzing the data. It…
Q: Learn the user's habits across mobile and desktop platforms.
A: Introduction: As they collect more and more devices to stay connected, people frequently switch…
Q: Why do we use functions in python?
A: Python: Python is a high-level, interpreted, general-purpose programming language. It was created by…
Q: Which one of these is not a valid SQL query. O SELECT AVG(Price) FROM Products; O SELECT * FROM…
A: Introduction: SELECT - This is the keyword that specifies which columns will be retrieved. In this…
Q: How would you answer the following statement: Context switching and process spawning
A: Technique Spawning Process spawning is a method or technique used by operating systems to produce…
Step by step
Solved in 2 steps

- Just a few lines on what cache coherency is like, please.This header may be used to determine if a cached page has been modified since it was last accessed. Requests may be made for pages that include pictures, sound, video, and other types of media, in addition to HTML. Do you believe that the efficacy of this approach is greater or worse when used to JPEG pictures as opposed to HTML code? Consider the definition of "efficacy" carefully, and then provide an explanation for your choice.A set of web browsers on the institutional network at USC generates an average of 15.0 requests/second for web objects of size 1.0 Mb. The access link to the public Internet is 15 Mbps. USC’s LAN operates at 1 Gbps. Assume LAN delay and internet delay are negligible. Suppose you installed a web cache and found that access link utilization was reduced to 9.0 Mbps. From your findings, what is the cache hit rate that resulted in this reduction in access link utilization?
- What exactly is a fully associative cache and how does it work?Subject: Computer Networks Note: Please answer in own words. copy from internet will very unhelpful for me. Question: Describe the following buffering mechanism in a reliable transport protocoli. Chained variable-sized buffersii. One large circular buffer per connectionWhat is the difference between clear and completely associative cache? concepts.p

