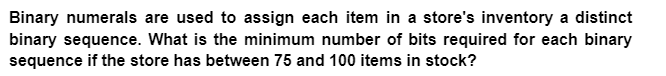
Binary numerals are used to assign each item in a store's inventory a distinct binary sequence. What is the minimum number of bits required for each binary sequence if the store has between 75 and 100 items in stock?
Q: How might a biased exponent be helpful?
A: Here is the explanation regarding the biased exponent:
Q: Please describe the differences between the ARM and core i3 architectures.
A: The ARM architecture is a RISC architecture while the Core i3 is a CISC architecture. This means…
Q: Why does SMF travel farther and faster than MMF?
A: SMF and MMF: SMF (single-mode fiber) and MMF (multi-mode fiber) both transmit light in single and…
Q: What does the phrase "reduced instruction set computer" actually mean when it uses the word…
A: The Reduced Instruction Set Computer, or RISC, is a kind of computer. In comparison to computers…
Q: What benefits might Mercy receive from an enterprise data model? Is Mercy's well-articulated model…
A: The St. Louis Catholic health system Mercy Hospital is utilizing big data to raise the caliber and…
Q: mention the ways in which technological advancement has benefited organizational communication.
A: The use of technological advancement the organizational communication has resulted in corporate…
Q: Think of baking a cake as being comparable to computing three iterations of a loop in parallel. In…
A: Given: The loop estimate will be dependent on the processes involved in the cake's creation. First,…
Q: 3. Describe the two options and their functions on the Fedora Linux launch screen. You will have…
A: Troubleshooting: A methodical method of problem-solving is troubleshooting. The purpose of the…
Q: Which type of program-level parallelism—control or data—is better suited for SIMD? What kind of…
A: SIMD stands for Single Instruction Multiple Data.
Q: This function specifies the number of computer instructions each source-level statement will…
A: Introduction Computer instructions are a bunch of machine language instructions that a specific…
Q: Problems that users have while using a disconnected information system how to clear the problem’s?
A: Answer is
Q: Given a digraph D = (V; A; ') with all but one arc (u; v) having non-negative lengths, explain how…
A: If you're unsure, the breakdown is as follows: A number is positive if it is bigger than zero. A…
Q: Why do we need Inverse Multiplexing?
A: The question has been answered in step2
Q: We recommend raising Flynn's taxonomy by one degree. What sets higher-level computers apart from…
A: The answer to the question is given below:
Q: What influence does the social environment in which you work have on your interaction with the…
A: The environment has a big impact on how you interact with the computer because people need to be…
Q: Why is understanding Boolean algebra essential for computer scientists?
A: Boolean algebra is a branch of math that deals with two-bit logical operations on variables. The…
Q: describe how technology is used in corporate communication.
A: Technology has changed the way we communicate with each other and our businesses.
Q: Your company has chosen to duplicate its product database over multiple servers in order to speed up…
A: When transaction execution: begins, the transaction must be completed in its entirety or it will not…
Q: The error-correcting Hamming codes: is there a method? Explain
A: Answer: Hamming code is an error correction system that can detect and correct errors when data is…
Q: Why does SMF travel farther and faster than MMF?
A: SMF and MMF: SMF (single-mode fiber) and MMF (multi-mode fiber) both transmit light in single and…
Q: The three main cloud computing platforms should be described.
A: Internet of Things: Instead of the programme running on local computing devices like servers, PCs,…
Q: An abstract class's parent class's abstract methods must all be implemented by its subclasses. Is it…
A: Abstract class's parent class's abstract methods: An abstract class is a class that is declared…
Q: Why is it essential to follow a structured cabling standard while building and maintaining
A: Given: we have to discuss why is it essential to follow a structured cabling standard while…
Q: Why does SMF travel farther and faster than MMF?
A: SMF: SMF stands for Signal Mode Fiber. SMF is a kind of optical fiber intended to transmit a single…
Q: When ought to a network upgrade be scheduled?
A: Alteration in the time span of the network The process by which users are moved from an old network…
Q: How long should a network transition last, and when should it happen?
A: Transition Network: Transition networks, often known as TNs, are essentially just a collection of…
Q: What drawbacks of Whetstone, Dhrystone, and Linpack are addressed by the SPEC CPU benchmarks?
A: Dhrystone is a synthetic computing benchmark designed to be representative of system programming,…
Q: Only one-third of mobile development projects successfully met project criteria in terms of budget,…
A: When creating and delivering a mobile app on a tight FIMC timeframe, the company faces the following…
Q: Give justification for why MATLAB is being used to tackle computational geometry problems.
A: MATLAB is a proprietary multi-paradigm programming language and environment for numerical…
Q: What methods can be employed to lessen the overhead that page table shadowing causes?
A: Shadow page table The shadow page table is only a pseudo page table that lives in the primary page…
Q: Data protection types accessible in MS-Excel are explained. Give instances to back up your…
A: To safeguard data, MS-Excel provides the following forms of protection: File Level Workbook Level…
Q: What advantages and disadvantages come with employing decimal data types?
A: Decimal Data type: Decimal (4,2), for example, implies that the number will have 2 digits before and…
Q: What weaknesses in the router layer 2 protocol have been found? Why does the ICMP request still…
A: ICMP Request : In a PPP, the ICMP request image result still works. When network issues prohibit the…
Q: How do you gather data for a thorough operations manual? How many things will be evaluated at once…
A: Introduction The Sequential Search is a technique for searching that involves checking the item…
Q: What drawbacks of Whetstone, Dhrystone, and Linpack are addressed by the SPEC CPU benchmarks?
A: The SPEC CPU suites measure the efficiency of a computer's central processing unit (CPU) by timing…
Q: We recommend raising Flynn's taxonomy by one degree. What sets higher-level computers apart from…
A: The acceptance of Flynn's taxonomy on a broad scale is based on two criteria. These include: The…
Q: Is it possible for an application to use UDP and still have reliable data transmission? If so, what…
A: ANS: - Yes, even while using UDP for data transport, an application can still benefit from…
Q: What obstacles must be overcome by an assembler in order to produce all of the binary code in a…
A: Functioning of Pass-2: By transforming symbolic machine-opcodes into the corresponding bit…
Q: What are the advantages and disadvantages of disk write caching?
A: Writing data to the disc cache: The practise of retaining files in a storage area that is only…
Q: In light of the existence of on-chip L3 caches, discuss the benefits and drawbacks of shared vs.…
A: Start: A single set of the instructions is carried out in a single thread. In other words, each…
Q: The Ubuntu Linux distribution's basis is based on which Linux distribution?
A: Ubuntu is a Debian-based distribution designed to have regular releases, a consistent user…
Q: Why is IoT-A significant, and what is its purpose
A: Answer:
Q: What other components might be changed to keep the page size the same (and avoid having to…
A: When the system slows down, the price of memory, such as DRAM (Dynamic Random Access Memory), rises…
Q: How do you typically get permission to change the network at a large company?
A: Answer:
Q: Daemon processes must be viewed using the -e option in conjunction with the ps command because they…
A: Daemon processes: A daemon is a long-running background process that responds to service requests.…
Q: A downgrade assault is what?
A: Downgrade attack: It is a kind of cryptographic attack that may be launched against the computer…
Q: What use do Microsoft Office apps serve in a blended learning setting?
A: Definition: In response to your query There are several terms used to characterize various learning…
Q: You should use an Oracle function to determine how many days have transpired between your birthday…
A: Oracle functions can be accessed through different SQL queries built within the Oracle Database.…
Q: hich argument supports shifting data to the cloud the most? What security issue is most important to…
A: Cloud computing is the provision of computer system resources, especially data storage and computing…
Q: What influence does the social environment in which you work have on your interaction with the…
A: An electronic device for storing and processing data, typically in binary form, according to…
Step by step
Solved in 2 steps

- Binary numerals are used to assign each item in a store's inventory a distinct binary sequence. What is the minimum number of bits required for each binary sequence if the store has between 75 and 100 items in stock?A store uses binary numbers to assign a unique binary sequence to each item in its inventory. What is the minimum number of bits required for each binary sequence if the store has between 75 and 100 items in the inventory.- 5- 6- 7- 8What are binary values?
- Given that a computer uses 4-bit ones’s complement numbers, what value will be stored in the variable j after the following code segment terminates? j = 1 k = -2 while(k != 0) { j = j + 1; k = k + 1; }How many bits of memory are required for storing 100 names of a group of people assuming that no name occupies more than 20 characters (including space) ? Assume 7-bit ASCII code with parity bit. Incorrect answer will be downvoted multiple timesThe inventory of a shop is represented in binary by a series of numbers that are each unique. How many bits in each binary sequence are required if the store stocks between seventy-five and one hundred items?

