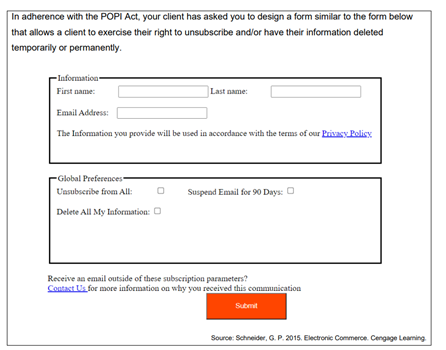
Build the above form by incorporating PHP & HTML and also ensure that successful completion of the form’s actions will result in a personalised confirmation message stating actions performed. Unsuccessful completion should also be acknowledged.
Q: Find the sum-of-products expansions of these Boolean functions. a) F(x, y, z) = x + y + Z b) F(x, y,…
A:
Q: What is blockchain technology? Give at least 3 advantages and disadvantages of blockchain…
A: Introduction: A blockchain may be thought of as a secure database that also functions as a ledger…
Q: Write a pseudocode to find the average value in a list has 10 integer values. Write a pseudocode to…
A: a) The average of 10 numbers is defined as sum of 10 elements divided by 10. So, the pseudo-code is…
Q: 1) Exhibit responsibility within your Information Security team and develop the Information Security…
A: According to the Bartleby guideline we are suppose to answer only one question at a time. Kindly…
Q: Explain why HTTP and DNS, respectively, require TCP and UDP.
A: why HTTP and DNS, respectively, require TCP and UDP
Q: 28. In a linear linked list, a. the next pointer of each node has the value NULL b. the last node…
A: Introduction to Linear Linked List: Linear Linked list is the default linked list and a linear data…
Q: Cyberbullying is a crime in what jurisdictions and in what ways?
A: Introduction: The Internet is a network of computers that connects them and allows them to…
Q: What happens during the fundamental machine cycle of a computer?
A: Introduction: An instruction cycle, also known as a Machine cycle, is used to carry out each and…
Q: Explain the purpose of the Properties window in a few words.
A: The following types of user interfaces are referred to as property windows: Property inspector.…
Q: Examine the ways in which different organisations make use of information technology.
A: Organizations: how different businesses employ information systems An overview of a In the corporate…
Q: section .data msg db "Hello world!". section .text global _start start: mov rsi, msg mov rdx, 13…
A: Below the assembly program resolve the error with output
Q: C program to take two numbers from user and printing lesser number from both numbers
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH IT THANK YOU
Q: ASSEMBLY LANGUAGE 1.. Create at least 3 to 5 questions for concepts or combination of concepts of…
A: Describe declaration and program of assembly arithmetic instruction.
Q: What are the various logical layers in a distributed client–server architecture application?
A: Logical layers: The most prevalent distributed system design is the client-server architecture,…
Q: Handshaking is a programmable .interface technique True False
A: Find the answer with reason given as below :
Q: Match each of the following with their appropriate pair, with regards to the TCP/IP model A. Network…
A: The Department of Defense (DoD) designed and developed it in the 1960s, and it is based on…
Q: How to find Lexers in Racket when each rule is trigger and an action (lexer [trigger action].)?
A: Given: How to find Lexers in Racket when each rule is trigger and an action (lexer [trigger…
Q: What does it imply when the Internet is called a "Network of Networks" now and then?
A: Introduction: "The network of networks" is the simplest way to describe the Internet. It's the…
Q: Describe a suitable method for handling the issue of missing values in decision tree learning
A: Please find the answer in the following steps. Decision tree: => It is a decision support…
Q: What is a model in System Analysis? Differentiate between logical and Physical model.
A: model in system analysis can be used for The design, specification, and analysis support connecting…
Q: Is try-catch exception applicable in Arduino? why or why not? in 5 sentences
A: Is try-catch exception applicable in Arduino?
Q: Examine the Data Base Envirormind's use of the Access language and associated processes.
A: Answer :
Q: a) Describe with the aid of a schematic diagram about the JPEG Encoder.
A:
Q: You may take advantage of Hadoop's high degree of computational redundancy when you utilise it.…
A: Yes, you may take advantage of Hadoop's high degree of computational redundancy when you utilize it…
Q: Explain why memberwise assignment in a class with a pointer member may cause problems.
A: The Answer is in step-2.
Q: Which encoding method is the best ? and which one is currently using with high data rate ? Computer…
A: Introduction: We must find the optimal encoding technique with a high data rate in order to answer…
Q: What is the significance of cloud security? What steps may be taken to strengthen cloud security?…
A: Cloud security refers to the provision of security for cloud-based services and protection from…
Q: c# code with comment for two-dimensional array with two (2) rows and three (3) columns. Then,…
A: As per the requirement program is completed. Algorithm: Step 1: Write the main() method Step 2:…
Q: (a) negate (succ (if x == 0 then 1 else 0))
A: divide :: Int -> Int main = do let var n if var 'rem' 7 == 0 then putStrLn "Number is divisible…
Q: What kind of wireless local area network connection is being used?
A: Various Network Types: A computer network is a network configuration in which two or more computers…
Q: What are the ramifications of insider threats to cloud security, as well as some potential…
A: Answer : If any threats happen with inside to the cloud then it will effect the cloud overall data…
Q: What is regression testing?
A: Introduction: In this instance, regression refers to a previously fixed software bug that has…
Q: Is there a problem with your information system that you should be aware of, and how can you…
A: In organisation there are the major problem in areas that we can design, data, cost and operations.…
Q: Describe the newline character in detail.
A: A newline (often referred to as a line ending, end of the line (EOL), following line (NEL), or line…
Q: Q3/ Suppose a movie theater has 36 seats, laid out in a rectangular six rows by six seats. Let the…
A: Algorithm 1.Include header files 2.Intialize variables and declare a two dimensional array 3.use a…
Q: With the help of a rudimentary diagram, explain Error Detection and Correction bits (EDC) in the…
A: The Data Link Layer uses error checks to ensure that frames, bit data streams, are transmitted with…
Q: The three basic components of the CPU are the control unit, registers, and primary memory. (Is this…
A: please see the next step for solution.
Q: What is the name for a little "switch" that can be turned on or off?
A: The answer of this question is as follows:
Q: Program in python There is function F Give an integer n (n 2 2), consider the prime factorization…
A: python code is given below
Q: Explain two computer breakthroughs that have contributed to the increased efficiency of e-commerce.
A: Introduction: Companies that use this distribution channel can grow into new markets. E-commerce…
Q: use pythone language and inheritance to solve this. Thank you
A: class Product: def __init__(self,id,title,price): self.__id = id self.__title = title…
Q: Which is the object in the statement p.getX() getX() the dot none of the above
A: Find the answer with explanation given as below :
Q: What strategic choices do you have for legacy system evolution? When would you replace all or part…
A: A legacy system is a working system that was developed, implemented, and deployed in a completely…
Q: Should software engineers who work on safety-related system definition and development be…
A: Software engineers who work on the definition and implementation of safety-related applications…
Q: C program for array manipulation take 10 array input from user and print sum of it
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH IT THANK YOU
Q: Why would you want to include javadoc comments in your packages?
A: Introduction: Computer programming is creating and executing a computer programme to achieve a given…
Q: --Problem -3 -Create a flowchart design that depicts the solving of the following problem: Asks user…
A: The Answer is in step2
Q: Even if a programmer already understands a range of programming languages, why is it useful for him…
A: Origination: "When you join an open-source project or begin a new employment, the person who…
Q: Consider the following program written in AC language discussed in the class. The tokens and grammar…
A: Below are the solutions:
Q: Consider the language L= {a, bc } over E= {a, b, c}. Find: (а) L° (b) L'
A: L0 = { a null string} L2 = {aa, abc, bca, bcbc}
Build the above form by incorporating PHP & HTML and also ensure that successful completion of the form’s actions will result in a personalised confirmation message stating actions performed. Unsuccessful completion should also be
acknowledged.
Step by step
Solved in 2 steps

- Question 6 This is a multiple choice question. Once you have selected an option, select the submit button below 'Cryptocurrencies are handled on a centralized exchange.' Is this statement true or false? True False Question 7 This is a multiple choice question. Once you have selected an option, select the submit button below 'After a data breach, it’s important to educate employees, partners and customers on how to prevent future breaches.' Is this statement true or false? True False Question 8 This is a multiple choice question. Once you have selected an option, select the submit button below An employee points out a design flaw in a new product to the department manager. Is this employee’s behavior ethical or unethical? Ethical Unethical Question 9 This is a multiple choice question. Once you have selected an option, select the submit button below 'Cybersecurity certifications are a way…13. _________ is the practice of identifying a user name. Group of answer choices Account harvesting Password cracking Authentication Authorization A functional access control An intrusion detection system 14. When performing security tests for an e-commerce website, which of the following are examples of structural security risks? Choose ALL which apply. Group of answer choices account harvesting password cracking SQL injection buffer overflow encryption levels 19. Fill in the blank for the secure coding practice provided below: Proven session management _____________________ are used to create random session identifiers.Which of the following offenses are not punishable under Section 5 of RA 10175? Data InterferenceChild pornographyIllegal AccessAll of the aboveOnline libel
- Q(6) Hi there, Please answer all the two multiple choice questions. No written explanation needed for all the questions. Thank you in advance. [31] A security administrator is responsible for performing periodic reviews of user permission settings due to high turnover and internal transfers at a corporation Which of the following BEST describes the procedure and security rationale for performing such reviews? A. Review all user permissions and group memberships to ensure only the minimum set of permissions required to perform a job is assigned. B. Review the permissions of all transferred users to ensure new permissions are granted so the employee can work. C. Ensure all users have adequate permissions and appropriate group memberships, so the volume of help desk calls is reduced. D. Ensure former employee accounts have no permissions so that they cannot access any network file stores and resources. [32] A security manager requires fencing around the perimeter, and cipher locks on…Which of the following is a risk of perpetrating doxxing? A) legal penalties B) malware C) surveillance D) data breachesQuestion 1 Which of the following correctly describes the difference between privacy and security? Privacy is about the individual's control over sensitive information pertaining to the individual; security is about the methods used to provide control over information. Privacy is about controlling access to personal information; security is about controlling access to company information. None of the listed choices are correct. Privacy and security refer to the sets of controls used to protect information. Question 2 Extended service agreements which run for 3 more years require that Sifers-Grayson provide software maintenance and patches for SCADA systems sold more than fifteen years ago. The engineering workstations used to provide this support take up 500 sq ft of space in the R&D lab and, due to their reliance on Windows XP, present security vulnerabilities which need to…
- q10C- Consider this scenario: A nurse in the hospital has been assigned to provide daily care to her patients. She has been given an access right to view/update the daily medical record of those patients. However, she accidentally accessed some sensitive patients’ record and breached the privacy policy of the hospital. Q- Propose and describe appropriate cryptographic controls (to ensure data confidentiality/integrity/authenticity) to mitigate the identified threats/attacks.Please give full explaination with why other options are incorrect There are many reasons to use a complex and unique password but individuals and corporations still risk exposure by using some variation of the word "password" on newly created accounts. While users are then encouraged to change the password to something more secure, they often fail to do so. One of the major risks of using this standard password or some variation (ex. "p4ssw0rd") is that the account could become the target of a brute-force attack called ___. piggybacking spamming hijacking credential recyclingAssignment Requirements:For this assignment read the articles, “IoT Security Breaches: 4 Real-WorldExamples” and “IoT security issues in 2021: A business perspective”provided in the links below:https://www.conosco.com/blog/iot-security-breaches-4-real-world-examples/https://www.thalesgroup.com/en/markets/digital-identity-and-security/iot/magazine/internet-threatsAnswer the following questions and provide examples to support youranswers. Be specific as there is a lot of information available to you on theInternet:1. Of the IoT security breaches, which one concerned you the most?2. Do you own or know anyone who owns these devices?3. What affect did the breach have? (Examples: Monetary, strategic,backdoor, scanning for weakness, etc.)4. Was the hacker(s) identified?5. What challenges do you think manufacturers of IoT devices face withthe development of new devices and upgrading existing devices?6. Do you think we need all these devices to make our lives morecomfortable and are useful?
- Which of the following statements best describes your attitude toward data security while it is being transmitted or stored: Which of these options will produce the best results, both in terms of data integrity and user authentication?1. What is essential for protecting against an SQL injection attack? Question 1 options: a. Restricted Language b. Guarding External Systems c. Guarding User Output d. Scrubbing User Input 2. True or False: When law enforcement gets involved, intellectual property can be taken away from an organization. 3. Where should a session be managed? Question 3 options: a.Front-end b.Back-end c.Client Side d.User Side 4. True or False: HIPAA does not provide for specific circumstances in which law enforcement officers can access PHI 5. True or False: Object privileges allow you to add and drop users 6. True or False: Typically, a user logs directly in to the database. 7. What is the ultimate goal of incident response? Question 7 options: a. Mitigate the damage b. Secure the database c. Minimize the damage d. Eliminate the threatWhich of the following statements best describes how you feel about the safety of data while it is being sent or stored: Which of these choices will provide the best results, both in terms of the integrity of the data and the authentication of the users?

