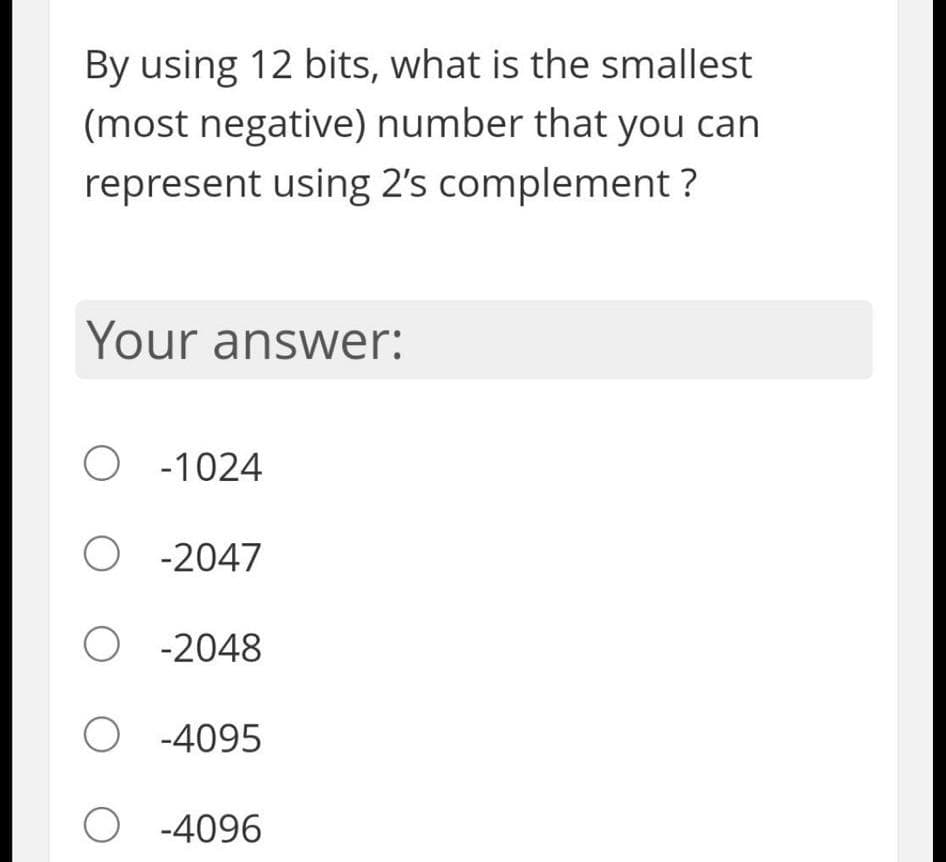
By using 12 bits, what is the smallest (most negative) number that you can represent using 2's complement ?
Q: Imagine that you have configured the enable secret command, followed by the enable password command,...
A: We use the enable password command to set a local password to control access to various privilege le...
Q: Session Hijacking assaults and how to defend yourself are taught. Examine possible retaliatory actio...
A: Session hijacking is a kind of online assault that involves the destruction of ongoing web sessions....
Q: What exactly do you mean when you say "network security"? Describe the functioning of the data encry...
A: Introduction: The term "network security" refers to a number of different strategies, tools, and pro...
Q: What is the decimal equivalent of the binary number 1100110110110100 written in excess-15 notation? ...
A:
Q: What is the default location of the system's logs?
A: The answer is given below.
Q: Explain the distinction between Type 1 and Type 2 hypervisors. Microsoft Virtual PC, Oracle Virtual ...
A: Introduction: Hypervisors that operate on real hardware are also extremely secure. Because each gues...
Q: How have media and technology been used in the classroom?
A: Introduction: The widespread availability of student databases that can track individual progress, t...
Q: Q4. Apply the dynamic programming which studies in the class to make change for an amount N=10 using...
A: Introduction: Here we are required to Find the minimum number of coins to make change for the given ...
Q: In order to get into your secret club, someone needs to know the password! Write a program that asks...
A: I have provided PYTHON CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT------------
Q: How can the video capabilities of a smartphone be used to collect data?
A: Intro The data captured or recorded using smartphones can be transferred or shared by MMS, Bluetoot...
Q: What is the best way for a server to notify its clients when something goes wrong?
A: Introduction: We're having a service outage, and certain services are being disrupted. Our staff is ...
Q: 06...
A:
Q: Short answer What is the reason for the need to rearrange databases? Computer science
A: Introduction: A database is a logically ordered collection of data saved on a computer that may be a...
Q: 10, and 1. Suppose that a1 = 5, a2 ak = ak-1 + ak-2 for k = 3, 4, . . Use strong induction to prove ...
A: Please upvote. I am providing you the correct answer below.
Q: Find the articulation points of the following graph using the Tarjan/Hoperoft algorithm: 2 5 7 8 (а)...
A: Dear learner , hope you are doing well , I will try my best to answer this question. Thank You!!
Q: Ten signals, each requiring 4000 Hz, are multiplexed onto a single channel using FDM. What is the mi...
A: The answer as given below:
Q: For an object to be writable to an ObjectOutputStream, the object should be an instance of a class t...
A: I have given answer in next step.
Q: Consider the non homogeneous ODE with a nonlinear term called b: dy + 2Aw- dt2 dy + w?y (1+ by²) = f...
A: Matlab Code: clear; clc; close all; % Description: Solves forced damped motion using ode45 w = 3; ...
Q: Consider the non homogeneous ODE with a nonlinear term called b: dy + 2Aw- dt dy + w?y (1 + by²) = f...
A: Matlab Code: clear; clc; close all; % Description: Solves forced damped motion using ode45 w = 3; ...
Q: Problem 4. Let G = (V,E) be an undirected connected graph with maximum edge weight Wmax. Prove that ...
A: Introduction: Here we are required to prove that if an edge with weight Wmax appears in some MST of...
Q: 16. Exception Project This assignment assumes you have completed Programming Challenge 1 of Chapter ...
A: As i have read guidelines i can provide answer of only 1 part of questions in case of multiple Quest...
Q: It is critical to compare and contrast single- and multi-processor systems. Computers are available...
A: INTRODUCTION: Models with Multithreading: A system's kernel and user threads must be handled.Kernel ...
Q: Numerous multithreading algorithms are evaluated for uniprocessor and multiprocessor systems running...
A: Introduction: On a multiprocessor system, several threads may execute on multiple CPUs at the same t...
Q: How does a Computer affect our day-by-day tasks?
A: -> Computer brings tremendous progress in health care sector, we can take appointments with docto...
Q: What exactly is data analytics? What is the goal and motivation for having data analytics now?
A: Intro Data is very useful in businesses to better understand their customers, improve their adverti...
Q: Joe’s Catering Service provides meals for a few local hospitals. They would like an internal compute...
A: The Unified Modeling Language (UML) is a normalized displaying language that permits programming eng...
Q: Let's say a top secret user wishes to utilise a file existence covert channel to leak the PIN number...
A: Introduction: A database with multilevel security has data that has been categorise and, as a result...
Q: What exactly is personalization? What are some examples of tailored information services that did no...
A: Introduction: Personalization (often referred to as customization) is the process of adapting a serv...
Q: Every binary tree is a binary search tree. O True False
A: Definition : A binary tree is a tree in which every node has 0, 1 or 2 children. A binary search ...
Q: How and why do the four most significant security breaches in buying and merchandising systems occur...
A: Introduction: When an attacker obtains unauthorized access to an organization's secured systems and ...
Q: Provide at least five rules for the knowledge base and one fact for working memory in a topic where ...
A: Introduction: The data received from the user during the expert system session is stored in working ...
Q: Give an example of a data structure for which no plausible array- or link- based solutions exist. Wh...
A: Introduction: To keep track of all possible moves in a chess game. To maintain track of a fixed key ...
Q: Distinguish between application virtualization and virtualization of applications.
A: Introduction: Virtualization, as the name implies, is a programme that enables several operating sys...
Q: How to encode a TM in binary
A:
Q: What are computer algorithms used for?
A: INTRODUCTION: ALGORITHM: An algorithm may be thought of as a sequence of planned sequential instruct...
Q: What are five different ways to come up with inferences?
A: Introduction: We've all had to take those standardised tests where you're given a large amount of in...
Q: Get to know the difference between the two types of machines.
A: Introduction: A virtual machine is a virtual environment created on a physical hardware system (off-...
Q: In C programming language
A: Errors in the code has been identified, let us see the details below,
Q: A class called adaptor has been defined. The class has the following attributes: a string called col...
A: First, we define what is a constructor: Constructor is a special function which is automatically cal...
Q: What is the state of the internet of things now, and when and where did it all begin?
A: Introduction: The Internet of Things (IoT) is a network of interconnected computing devices and equi...
Q: Discuss some of the ways through which green computing can be achieved.
A: Green Computing Green computing is the use of computers and their resources in an environmentally s...
Q: What role does the operating system play in processor management ?
A: Introduction: A process is a programme that is executing and is managed by the operating system.
Q: What are phishing attacks and how can you avoid them? Briefly discuss.
A: Introduction: Phishing is the deception and exploitation of people through the illicit theft of sens...
Q: Examine in detail how computer science makes use of integration.
A: Introduction: Integration is the process of deriving a function's inverse, and it is also known as A...
Q: Describe five different types of network topologies. Which one do you believe is the most trustworth...
A: Intro It is the manner in which computer systems or network devices are linked to one another that i...
Q: No, I don't think it was an inside job that caused the current security breach concerning access con...
A: Introduction: When private or protected information is compromised, a data breach occurs. A data bre...
Q: 2. Find the error in each of the following. (Note: There may be more than one error.) c) The followi...
A: c) for(int year = 1; year <= 10; ++year){ double salary += salary * 0.05; } printf("...
Q: Consider diagrams below. List rule violations on these diagrams Context Diagram DF3 Ship Cap & Gown ...
A:
Q: What precisely is a stack? What are some examples of stack applications?
A: Introduction: Stack is a vital data structure that is built on a linear data structure format. An el...
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- How many different values can be represented using 16-bit two’s complement representation? What’s the largest and smallest possible value? Answer the two questions again for n-bit 2’s complement. Please show all steps.How many different values can be represented by 48 bits? Give the answer both as a power of 2 and in decimal.Given the 8-bit binary number: 1 1 0 0 1 1 0 1 What decimal number does this represent if the computer uses signed-2's complement.
- Represent 5 in three ways using only 8 bits: Signed-magnitude (a), signed 1's complement (b), and signed 2's complement (c).One's complement, two's complement and sign & magnitude all have the same 32-bit representation for signed integers in the range ______ to _______. What goes in the blanks to make this true? Please provide explanation as well.If the bit pattern 0xffff_ffff_ffff_ffff_ffff_ffff_ffff_ffbd is used for a 128-bit two's complement integer, what number does it represent? show your answer in base ten.
- Logically bitwise AND these numbers using 12-bit binary 2’s complement numbers 011101111101 AND 010111011011 Logically bitwise OR these numbers using 12-bit binary 2’s complement numbers 010111011011 OR 100001100101 Can you please show the steps and explain how you got the solution.Using 8-bit representation, what is the 2’s complement of the result of ((45 base 10) + (44 base 10))?How does the magnitude of the most positive number compare with the magnitude of the mostnegative number in an N-bit two’s complement number? How many distinct integers can be represented by an N-bit two’s complement representation (i.e.what is the difference between the most positive and the most negative)?
- If we use 5 bits to represent special symbols in a binary coding scheme, how many different symbols can be represented? a. 16 b. 10 c. 25 d. 32Calculate the smallest negative number and the largest positive number that a 24-bit two’s complement number system can encode. Show how you calculated the answers.Using a “word” of 4 bits, list all the possible signed binarynumbers and their decimal equivalents that are representable in:1. a) Signed magnitude2. b) One’s complement3. c) Two’s complement

