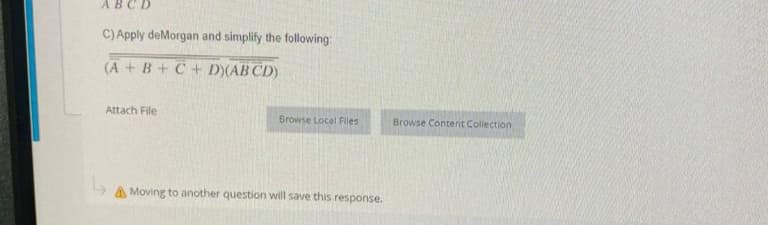
C) Apply deMorgan and simplify the following (A+B+C+D)(ABCD)
Q: Investigate the graph coloring problem. Compare greedy and backtracking algorithms to solve the…
A: Actually, an algorithm is a methodical procedure. Backtracking Algorithm: Place the monarchs in the…
Q: Can you use VoIP while you're abroad? When you make a call using WhatsApp, how does it influence the…
A: Over-the-top (OTT) services, such as WhatsApp Voice, provide cell carriers with both a challenge and…
Q: Hd.1 Determine an equation of the osculating plane of the curve x=sin(2t), y=t,z=cos(2t) at the…
A: To find the equation of the osculating plane, we need to find the normal vector and a point on the…
Q: In Java code: A company pays its employees on a weekly basis. The company has three types of…
A: Dear student, the answer is provided below. Please note I have provided the java code and and a…
Q: Closure Property of Regular Languages Prove that the set of regular languages is closed for the O P…
A: We have to prove that the set of regular languages is closed for the O P 3.
Q: What people did in the past may help explain the current status of computer security. Explain.
A: This question implies whether or not certain actions were required to bring about the current state…
Q: Provide your answers based on your chosen reading material(s) such as books, magazines, and journals…
A: According to Bartleby Guidelines we need to answer only one question so I have answered first…
Q: Do you have any advice on the management of firewalls? Explain.
A: The answer is given in the below step
Q: Is there anything a consolidated database might provide Mercy? Is it more important, now that Mercy…
A: The answer's below: Mercy Hospital, a St. Louis Catholic health institution, uses big data to…
Q: Create a Java class Recursive Methods.java and create the following methods inside: ALL THE METHODS…
A: Here is your solution -
Q: Question 1 The binary byte-length 2’s complement representation of the decimal number -25 Group…
A: Rules: Convert the decimal number to binary number Invert the digits. And add one. Two's…
Q: The expansion of the Internet and World Wide Web has been more rapid. Provide an explanation for…
A: Internet: The Internet is a global network of computers and servers that are connected to each…
Q: Wheels & Tyres Inc. is a leading Australian producer of high-quality tyres. There are several types…
A: Introduction:- A context free diagram helps to obtain the brief overview of the interaction…
Q: To what extent does networking play a role in IT?
A: Networking is a crucial aspect of information technology (IT) that allows different devices,…
Q: Why, in your opinion, is requirements discovery necessary for a system in development? Provide an…
A: It is imperative that the significance of requirements discovery for a system that is currently in…
Q: you wanted to find out who tried and failed to log in to a computer, which log in event viewer would…
A: To find out who tried and failed to log in to a computer, we can use the Security event viewer. The…
Q: Write a program that simulates flipping a coin to make decisions. The input is how many decisions…
A: Answer:
Q: In the field of computer science, there are several options for how files should be stored.
A: File organising system 1) The method that is used to both represent and store the data that are…
Q: Were you manage to send all five pieces of data in a timely manner?
A: In order to complete this task, we need to write down the name of the protocol that transmits all…
Q: Can you explain what a design workstation is and how it's set up? Provide a rundown of the topic by…
A: Here is your solution -
Q: How do you safeguard a workplace printer that is used by several people?
A: We have to provide some points regarding safety of the workplace printer that is used by several…
Q: How do transaction processing, CRM, and supply chain management systems function, and what are their…
A: Transaction processing systems, customer relationship management systems, and supply chain…
Q: Is there a tried-and-true method for efficiently managing firewalls? Explain.
A: Given: Which firewall management techniques are the most effective? Explain. Answer: Best Firewall…
Q: An informative essay about the role of networking in IT growth would be a great assignment.
A: Introduction: Write an essay on networking's role in information technology growth. IT helps…
Q: When I was compling my code this is the output I got. yes) Enter cList data (int): Add more cList…
A: Following is the implementation of the cnPtrQueue class: File name: cnPtrQueue.cpp #include…
Q: The government central bank requires you to modify the system's new interest rate as a banking…
A: Given: If you work in a bank's information system, you'll need to do routine maintenance to reflect…
Q: What is data profiling, and how does it fit into the bigger picture of data quality assurance?
A: A approach known as data profiling is one that examines the information that is used in an existing…
Q: V2 Question 41 Write an assembly program (Data and Code) that uses loop to read 10 numbers and…
A: Solution: Given, Write an assembly program (Data and Code) that uses loop to read 10 numbers and…
Q: Describe what the distinctions are between multicore, manycore, and clusters, and provide an…
A: High performance computing (HPC) requires advanced processors that can perform complex calculations…
Q: Write Python code that will find the reflexive-transitive closure of a matrix. Make sure to test the…
A: According to the information given:- We have to follow the instruction in order to get desired…
Q: Do you think you have enough knowledge to create an essay about the role of networking in the…
A: Given: Write an essay on the value of networking in the advancement of information technology.
Q: Can an efficient firewall be maintained?
A: Introduction: In order to keep detrimental traffic from entering the system and endangering its…
Q: Authentication is a complex problem in the modern era of digital technology.
A: The terms "digital authentication" and "e-authentication," which refer to the procedure by which…
Q: please write in C++ using #include using namespace std Define a class called DateYear, that…
A: Here's a possible implementation in C++:
Q: Q.1 Using a dataset us_contagious_diseases compare the rate of Florida, New York and Illinois using…
A: Q.1 Using R, generate a time series plot that compares the disease rates of Florida, New York, and…
Q: Liability in the event of a compromised honeypot used to attack another system is a major legal…
A: This question comes from Computer Security which is a paper of Computer Science. Let's discuss it in…
Q: What kind of website design is best for a social networking platform?
A: Important to prioritize mobile optimization in website design. The design should be responsive and…
Q: Area of a rectangle = length * width Create a Class that calculates and prints out the area of a…
A: Note : You have not mention the language of the program so I'm answering your question in C++. Your…
Q: network with two nodes, A and B, is connected with a 150Mbps link, with a 180ms one-way latency and…
A: Given that, Band width of link= 150 Mbps One way latency= 180 ms Transmission delay= 8 seconds
Q: Please written by computer source Design an NFA over Ʃ = { 0, 1} that accepts language L for which…
A: Given that, Set of input alphabets Ʃ = { 0, 1} The language L contains the strings that starts and…
Q: rite down the various types of characteristics in the Entity-Relationship (ER) model.
A: The Entity-Relationship (ER) model describes the relationships among entities in a database. There…
Q: What kind of website design is best for a social networking platform?
A: Introduction: A website is a group of linked Web pages that anyone can see and share the same domain…
Q: When expanding an unsigned 8-bit integer to a 16-bit one, the first eight most significant bits…
A: Option is the response that is appropriate for the questions ("False") EXPLANATION When the signed…
Q: Why is it crucial for IT to be interconnected in today's world?
A: Here is your solution -
Q: What is data profiling, and how does it fit into the bigger picture of data quality assurance?
A: Introduction Verifying and ensuring the accuracy, completeness, consistency, as well as validity of…
Q: (1) Prompt the user to enter a string of their choosing. Output the string. (1 pt) Ex: Enter a…
A: Coded using Python3.
Q: A complex number is a number of the form a + bi, whereby a and b are constants, and i is a special…
A: Define a function called "add_complex_numbers" that takes two tuples as inputs Extract the real and…
Q: A common year in the modern Gregorian Calendar consists of 365 days. In reality, Earth takes longer…
A: Algorithm: Start by defining the function "days_in_feb()" that takes in a single parameter…
Q: [s158a01@cisweb ex0]$ gcc powers.c In function ' error: ' loop initial declarations are only allowed…
A: Given C program contains declaration of variables and then the print statements. The variables…
Q: Assume that EBX and ECX have the following values EBX: FF FF FF 75 ECX: 00 00 01 A2 After the…
A: 1) The instruction INC ECX increments the value of ECX by 1. 2) After the execution of this…
Step by step
Solved in 2 steps

- HTML passcode issue 79 Online banking security sometimes demands three random passcode characters. If the passcode was 531278, they may request the 2nd, 3rd, and 5th characters and expect 317. Keylog.txt had 50 successful logins. Study the file to get the shortest unknown-length secret passcode.please see attached files C++Python3 | File I/O 1. Reading and Writing to Text Files Create a function access_file(filename) that copies the contents of the file filename and appends the data to the file ‘file_logs.txt’. 2. Loading, Manipulating, and Saving Images Create a function manipulate_image(filename) that opens the image filename, prints the RGB values of each pixel, and saves the image with the blue component of all pixels halved. The image must have the original filename prepended by ‘filtered_’. Assume that all images will be in the RGB encoding.
- 1. Additionally, state briefly what you understand a file extension to be and what its purpose is.Go to any set of files stored on your computer and identify three file extensions that you seeand which software applications may have created them. Hint: By simply right clicking on aselected file and from the pop-up menu selecting properties (Microsoft Windowsenvironment), the file extension for most files should be displayed.C++ question please For below screen shot when using ifstream to read files, how can I display the files first, then choose the option to read one of them?C++ Please Can you show me how to do encryption and decryption using i/o for a text file please?
- Additionally, state briefly what you understand a file extension to be and what its purpose is. Go to any set of files stored on your computer and identify three file extensions that you see and which software applications may have created them. Hint: By simply right clicking on a selected file and from the pop-up menu selecting properties (Microsoft Windowsenvironment), the file extension for most files should be displayedD. Additionally, state briefly what you understand a file extension to be and what its purpose is. Go to any set of files stored on your computer and identify three file extensions that you see and which software applications may have created them. Hint: By simply right clicking on a selected file and from the pop-up menu selecting properties (Microsoft Windows environment), the file extension for most files should be displayed.C++ i want 7 files header,imp,main. Please follow the instructions
- Fill in the blank question- Only answer needed without explanation Q. _____________ format is used to represent device files in redhat server.Furthermore, explain briefly what you believe a file extension is and what it serves. Navigate to any folder on your computer and name three file extensions that you see, as well as the software programs that may have generated them. Most file extensions should be shown by simply right-clicking on a chosen file and choosing properties from the pop-up menu (Microsoft Windows environment).Please do not give solution in image format thanku A number of the networking classes are synchronous in nature. Explain how using multi-threaded programming techniques can make the code behave asynchronously in an application and improve performance. Summarize your answers and rationale in 300 words.

