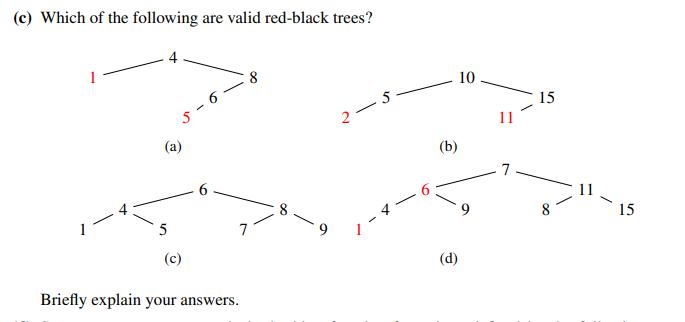
(c) Which of the following are valid red-black trees? 1 5-6 (a) 5 (c) 6 8 7 Briefly explain your answers. 2-5 (b) (d) 10 11 7 15 8 15
Q: Write a MATLAB program to design the state feedback matrix of the la 5 G(s) = s(s+4)(s+6) Using a…
A: State feedback is a control technique that involves designing a linear feedback controller based on…
Q: Given a graph G (N, A) on which each arc (i, j) E A has an associated value rij, which is a real…
A: We are given a graph G(N,A) and each arc has an associated value rij. To find the shortest path…
Q: Prove that the following problem, given a set S of integers and a number t, is of the NP class. Is…
A: A decision issue may be verified in polynomial time by a deterministic Turing machine, but there is…
Q: The worst case situation for quick sort is when
A: Quick sort: Quick sort is a popular comparison-based sorting algorithm that follows a…
Q: Exercise 2 - Hashing a String 2 Apply your hash function to anagrams, e.g., cat, tac • Will they be…
A: In this exercise, we will explore how to hash a string, focusing on the issue of anagrams. Anagrams…
Q: util.Iterator; public class MySet { // implements a set using a separate chaining hash table…
A: 1. MySet test=new MySet(6);2. test.addElement(1);3.test.addElement(3);4.test.addElement(8);…
Q: Pairing heap data structure questions What is the basic operation performed in a pairing heap?…
A: b) Deletion: While deletion is an important operation in many data structures, it is not the basic…
Q: If you were to name the three most important tasks of a database administrator, what would they be?…
A: Which three aspects of database administration are absolutely necessary?If you have any questions,…
Q: 6. Give an algorithm that determines whether or not a given undirected graph contains a cycle. Your…
A: One common algorithm to determine whether or not an undirected graph contains a cycle is the…
Q: When the user to selects the "view_mine" option, the program does not work as expected. It prints…
A: Hello student. Greetings Hope you are doing great. Thank you!!! The modification in the code is in…
Q: Use the given Fibonacci heap in the figure and solve the following question. It’s a heap with a…
A: - We need to provide the step by which the fibonacci heap could be created from an empty heap.
Q: The AVL Tree starts empty. Order 50, 25, 10, 5, 7, 3, 30, 20, 8, 15 into this AVL tree. Draw each…
A: Hello student Greetings An AVL tree is a self-balancing binary search tree that maintains a…
Q: Based on an array implementation of a binary tree, construct an array version of a binary search…
A: To implement an array version of a binary search tree using the simulated link approach, we can use…
Q: Graph theory: Show that there is a graph G with exactly 5 nodes where both G and its complement,…
A: Graph theory: Show that there is a graph G with exactly 5 nodes where both G and its complement,…
Q: Hard computation. How hard is it to compute nl-n(n-1)(n-2)... (2)(1)? Do you think there is a…
A: Hello student Greetings Hope you are doing great. Thank You!!!
Q: Identify the correct rotation to maintain the height balance of the AVL tree. D 2 5 5 4 8 ... ...…
A: Identify the correct rotation to maintain the height balance of the AVL tree.
Q: e() removes an element from Q. following procedure whose input is an undirected grap LIST. weight…
A: Let Q be an implementation of some data structure where: • Q.Initialize() and Q.IsNotEmpty() take…
Q: Calculating the Minimum Sum Path in a Triangle (LeetCode Problem) Given a triangle array, return the…
A: The JAVA code is given below with output screenshot
Q: Assume this tree is a binary search tree How many more nodes, can we add to this tree without…
A: In this question we have been given a binary search tree and we have to determine how many nodes can…
Q: Case Study 3 Part 1 - Euclidean Algorithm 1. Use the Euclidean Algorithm to find the greatest common…
A: Given Integers are: 396 and 480 To find the greatest common divisor (GCD) of 396 and 480, we can use…
Q: Demonstrate that the following issue falls within the NP class: A set S of integers and an…
A: In this question we have to demonstrate that the given statement falls under NP class A set S of…
Q: Explain post order traversal and find the post order traversal for the following:
A: The post order traversal is one of the ways to traverse the tree data structure and is used for…
Q: ALGORITHM Selection Sort(A[0..n - 1]) //Sorts a given array by selection sort //Input: An array…
A: Here is your solution -
Q: Given two sorted sequences with m, n elements, respectively, design and analyze an efficient…
A: One approach to find the kth element in the merge of two sorted sequences is to use a modified…
Q: Given the code below you need to answer several questions about white box testing techniques, which…
A: In this question we have to provide answer about the white box testing for a given code, where a…
Q: Write a technique that quickly identifies whether two nodes u and v in a tree T whose root node is s…
A: The answer is given below step.
Q: The string field [Commission] contains the value 3414.9658. What expression in the Formula tool will…
A: Consider the number which is given in the question 3414.9658 Now we have to convert this number…
Q: For each of the following program fragments: Give an analysis of the running time (Big-Oh). Justify…
A: Let's consider the program A given above . As mentioned in the comments we can see that the program…
Q: Given the tree bellow 5 9 3 8 12 146 (10) what is the preorder? (11) 20 9531486 20 12 10 11 30 21 31…
A: Tree Traversal: It is the process to visit all nodes of binary tree and print their values too.…
Q: When we created a Mongo database on a server, one way to access that database from another computer…
A: SSH tunneling method SSH tunneling involves creating a secure encrypted tunnel between the local…
Q: We want to determine whether an unsorted array A of n entries has duplicates. These integers are…
A: Given unsorted array is A and it contains n entries which has duplicates. These entries in the array…
Q: Determine if the number is odd or even. Add to a counter for each type, i.e. an even counter and an…
A: The question provides an integer array of positive numbers, and asks to process the array and do the…
Q: You will implement some methods in the UndirectedGraph class. The UndirectedGraph class contains two…
A: Breadth-first search (BFS) is a graph traversal algorithm that explores all the vertices of a graph…
Q: USD hosts a networking event for student clubs. There are 4 student clubs, each with a different…
A: Sudoku is a popular puzzle game that involves filling a 9x9 grid with digits from 1 to 9 so that…
Q: If L: R² R³ be defined by L(x, y) = (x, y, 1), show that it is a linear transformation.
A: The problem asks us to determine whether the transformation defined by L(x,y) = (x,y,1) is a…
Q: Assume that A is a n by n matrix with 1000 entries with the entries A(i, i) = i, A(i, i + 1) = A(i +…
A: To create the heap, we start at the last non-leaf node (index 3) and perform a heapify operation on…
Q: 11. Compute the number of different customers who have an order. 12. Compute the average age of a…
A: distinct keyword in sql gives the unique values. avg function gives the average of values.…
Q: Question 5: Rebalance the following AVL Tree using appropriate Rotation technique. Write the steps…
A: - We need to perform rotations on the AVL tree to rebalance the complete tree.
Q: Q1. Consider the following sequence of numbers: 15, 20, 24, 10, 13, 7, 30, 36, and 25. Insert these…
A: Sure, let's build the red-black tree step by step while inserting the given sequence of numbers.…
Q: Create an implementation of a binary tree using the recursive approach introduced in the chapter. In…
A: Binary tree: It is a data structure which is used to represent or store hierarchical data. A…
Q: 5. 6. Given an undirected graph with n vertices and m edges, find an O(n+m) time algorithm that…
A: We are asked to create to algorithms that satisfies the requirements. Both of these are graph…
Q: Create a text file called question2.txt and populate it with random characters, numbers, and…
A: Here's the algorithm of the Java program that reads the contents of a text file, stores them in an…
Q: Run the depth-first search algorithm on the following graph with the vertex list and all adjacency…
A: Depth-first search (DFS) is a graph traversal method that evaluates all of the vertices of a graph…
Q: 9. Represent the following statements using syntax in C programming language. s=n k=n while (k> 1) k…
A: The C code is given below including the code snippet given in the question.
Q: 4. Assume that: • Problem Q₁ reduces to problem Q2 in polynomial time, and ● problem Q2 reduces to…
A: Given, Assume that: Problem Q1 reduces to problem Q2 in polynomial time, and problem Q2 reduces to…
Q: Change the code in Program 4 to let the program change any decimal num- ber to its equivalent octal…
A: In this question we have write a C++ code for the conversion of decimal number into its equivalent…
Q: Discover a gap in the current Malaysian economic landscape.
A: Malaysia is an emerging economy that has experienced significant growth in recent years. However,…
Q: (a) Is 2"+1=0(2")? Explain why.
A: To prove that 2^(n+1) = O(2^n), we need to show that there exist constants c and n0 such that for…
Q: ou will implement some methods in the UndirectedGraph class. The UndirectedGraph class contains two…
A: An undirected graph is a graph where each edge does not have a direction. This means that if there…
Q: Make a detailed Hashing note. (Hash table, collision detection techniques, temporal complexity, and…
A: Hashing is a data structure that is used to store and retrieve data efficiently. It involves mapping…
Algorithms & Data Structures
Step by step
Solved in 3 steps
