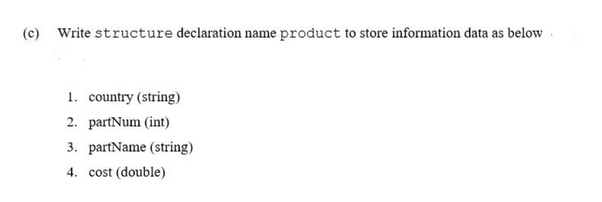
(c) Write structure declaration name product to store information data as below 1. country (string) 2. partNum (int) 3. partName (string) 4. cost (double)
Q: Explain why performance is only anticipated to improve by a factor of 50 but the cost-performance…
A: In economics and engineering, the term "price–performance ratio" refers to the ability of a product…
Q: bes a software project need to explain its needs for any particular reason?
A: The answer of this question is as follows:
Q: Look at the various information management techniques used by various businesses.
A: Introduction : Data driven firms need information management to make better decisions and accomplish…
Q: Databases may be configured to only utilize the outer tracks of magnetic disks, leaving the inside…
A: The above question is solved in step 2 :-
Q: Investigate the problems that data systems face using data and technology.
A: Introduction The data system is a term utilized to allude to a coordinated assortment of images and…
Q: Make a list of all the many ways that a network may help companies save money. Along with other…
A: The answer for the above motioned question is given in the following steps for your reference.
Q: Where OID refers to Owner's ID, OLname and OFname refers to the last and first name of customers,…
A: Tables are database objects that contain all the data in a database. In tables, data is logically…
Q: Installing a disconnected information system might result in a number of issues.
A: Given: To gather, process, store, and disseminate data, a structured, sociotechnical organizational…
Q: What precisely are the distinctions between backup and cloud storage when it comes to online…
A: To guarantee that your database is intact after a disaster, you should regularly do a backup. You…
Q: What exactly does it mean to have a virtual drive? When does it occur, and what triggers it? Please…
A: Given : - [6/2/2022, 2:15] shaikmabula163: Virtual drive question. A virtual drive emulates an…
Q: solid-state disk
A: A solid-state drive can have its data recovered in a variety of legal ways. Utilizing a data…
Q: Think about how a packetized data flow and a firewall vary from one another.
A: Firewall: A firewall is a type of network security device that keeps track of incoming and outgoing…
Q: Is it important to promote both the benefits of cloud storage and the need of data backup in…
A: Data is the most important thing , even person identity is data, bank details are data . These all…
Q: Describe the use of iterators, generators, lists, and dictionaries in your own words
A: The above question is solved in step 2 :-
Q: Describe the reasons behind the following URLs' insecurity and what you propose to do to make them…
A: The purpose of routing protocols is to build steering tables, make steering decisions, and become…
Q: What actions are taken in the forensic data recovery procedure from a solid-state drive?
A: While the forensic recovery procedure differs from standard recovery methods, it may provide…
Q: The most important challenges in information technology are covered in this part, along with the…
A: Two of the most significant problems that have been found in information systems are ethics and…
Q: Please provide the names and short descriptions of 10 international organizations that are involved…
A: To Do: List the names of 10 international organisations that are related to computer science and…
Q: How you can have multiple computers on your LAN and make all of them access the Internet behind a…
A: Introduction : Personal computers and workstations can share information, resources, and software…
Q: What role does a security key, sometimes referred to as a trusted platform module (TPM), play in the…
A: Introduction: Full disc encryption is the technique of encrypting every piece of information on a…
Q: Databases may be configured to only utilize the outer tracks of magnetic disks, leaving the inside…
A: Introduction: A magnetic disc is a storage device that writes, rewrites, and accesses data via…
Q: What applications are there now and where did the idea of the internet of things originally appear?
A: Encryption: The Internet of Items (IoT) is a network of physical things that are combined with…
Q: 19) We can connect upto i. 0 ii. 2 iii. 112 iv. 2048 devices using I2C protocol.
A: Answer..
Q: I'm not familiar with routing or how it works. It's crucial to the differences between two common…
A: In order to transport the packet by selecting the best way from one network to another, layer 3…
Q: What if a virus was present on your tablet or smartphone? Identify the kind of malware you may be…
A: Malware is a file or piece of software that is intended to do harm. computer code that is generally…
Q: List all basic relational algebraic operations. (Advance HTML formatting is enabled for your answer…
A:
Q: How will the framework for ethical reasoning be used in the workplace moving forward?
A: Given: What professions will employ the ethical reasoning framework in the future? Decisions on…
Q: What actually serves as the remote interface's function in the RMI implementation? What…
A: Introduction to Remote Method Invocation An API called RMI (Remote Method Invocation) gives Java…
Q: Look at the various information management techniques used by various businesses.
A: how different businesses use information systems. A summary of an Information systems, in the…
Q: Name three different types of semiconductor memory and briefly describe each one's key…
A: RAID(Redundant Array of Inexpensive Disks) Redundant Array of Inexpensive Disks, or RAID, is an…
Q: You may find out more information about the metrics used in the software development process if…
A: The Answer is in given below steps
Q: What modifications may be made to computer networks in order to keep them from being infected with…
A: One, get anti-virus software. Installing and utilizing antivirus software is crucial if you want to…
Q: Examine the value of and the degree to which interpersonal skills were used in the preparation for…
A: It is the ability we use to communicate daily, such as speaking, listening, walking, observing,…
Q: You have heard the expression about something being in the eyes of the beholder. This is true in…
A: We are now exploring a number of ways to describe ours virtual camera. Along the way we explore…
Q: For the language L = {anbm:n,m ≥ 0, n ‡ m} a) Generate CFG grammar for L b) convert the grammar from…
A: Below I have provided the solution to the given grammar
Q: What are some of the most recent technological developments in the field of information technology?
A: Introduction: Information technology (IT) is the security, creation,storage, processing, and sharing…
Q: There are several methods for achieving forensically sound data recovery from a solid-state disk.
A: Following is the process for forensically sound data recovery from a solid state drive. The term…
Q: Whoever can inspire and encourage technical people to reach their full potential is referred to be a…
A: Required: Why are you regarded as explain when you have the ability to motivate technically minded…
Q: what is Identity-Based Public-Key Cryptography? explain with example
A: Identity-based cryptography is a type of public-key cryptography that uses a publicly known string…
Q: Installing a disconnected information system might result in a number of issues.
A: Information system (IS). A coordinated, authoritative structure that is utilized to accumulate,…
Q: Please elaborate on why smartphones and PCs do not match the requirements for changes. Check to…
A: Introduction: As students rely more on their smartphones, they become less attentive and productive…
Q: Information systems that are fragmented may have a variety of drawbacks and issues.
A: Computer failure and loss: A failure is a problem with a computer or equipment that prevents it from…
Q: Which forensic recovery techniques are available for data saved on solid-state drives?
A: The answer for the above question is given in the below steps for your reference.
Q: These red flags may indicate that a software project is doomed to failure. To what purpose?
A: The warning signs that a software project is going to fail are as follows: The necessary software is…
Q: Where can I get information about the newest advancements in information systems, information…
A: This is a reference to a certain development in information systems technology that many IT experts…
Q: Study the many ways that information systems are being used in different industries.
A: Information system which refers to the system which is the an integrated the set of components which…
Q: What is the most effective way to backup user data? Your solution has to be proficient, quick, and…
A: It describes the process of digitally capturing information and documents and then putting those…
Q: Prove ¬(3x € X : (Vy € Y : E(x, y))) = \x € X : (‡y ≤ Y : ¬E(x, y)) ¬(Vx € X : (³y € Y : E(x, y))) =…
A: Answer: We have to prove the quantifier so we will see in the more details with proper explanation
Q: What sets networked computers different from other computers connected to the same network?
A: Utilizing the cloudA firm may utilise software, hardware, and platforms as a service provided by a…
Q: Do you believe that the production of the final product is the most crucial step in software…
A: No, As First For building software requirements are to be clearly understand and what and how that…
Step by step
Solved in 2 steps with 3 images


