C. Modern technologyc D. Digital divide 5. It is a computer crime to A. Downloadany file Tro B. Copy someone else'
C. Modern technologyc D. Digital divide 5. It is a computer crime to A. Downloadany file Tro B. Copy someone else'
A+ Guide To It Technical Support
10th Edition
ISBN:9780357108291
Author:ANDREWS, Jean.
Publisher:ANDREWS, Jean.
Chapter11: Windows Versions And Customer Service
Section: Chapter Questions
Problem 4TC
Related questions
Question
Answer question 4, 5, 6 showing fully all the steps. Solution should be perfect(very correct), clear, brief and explicit enough!
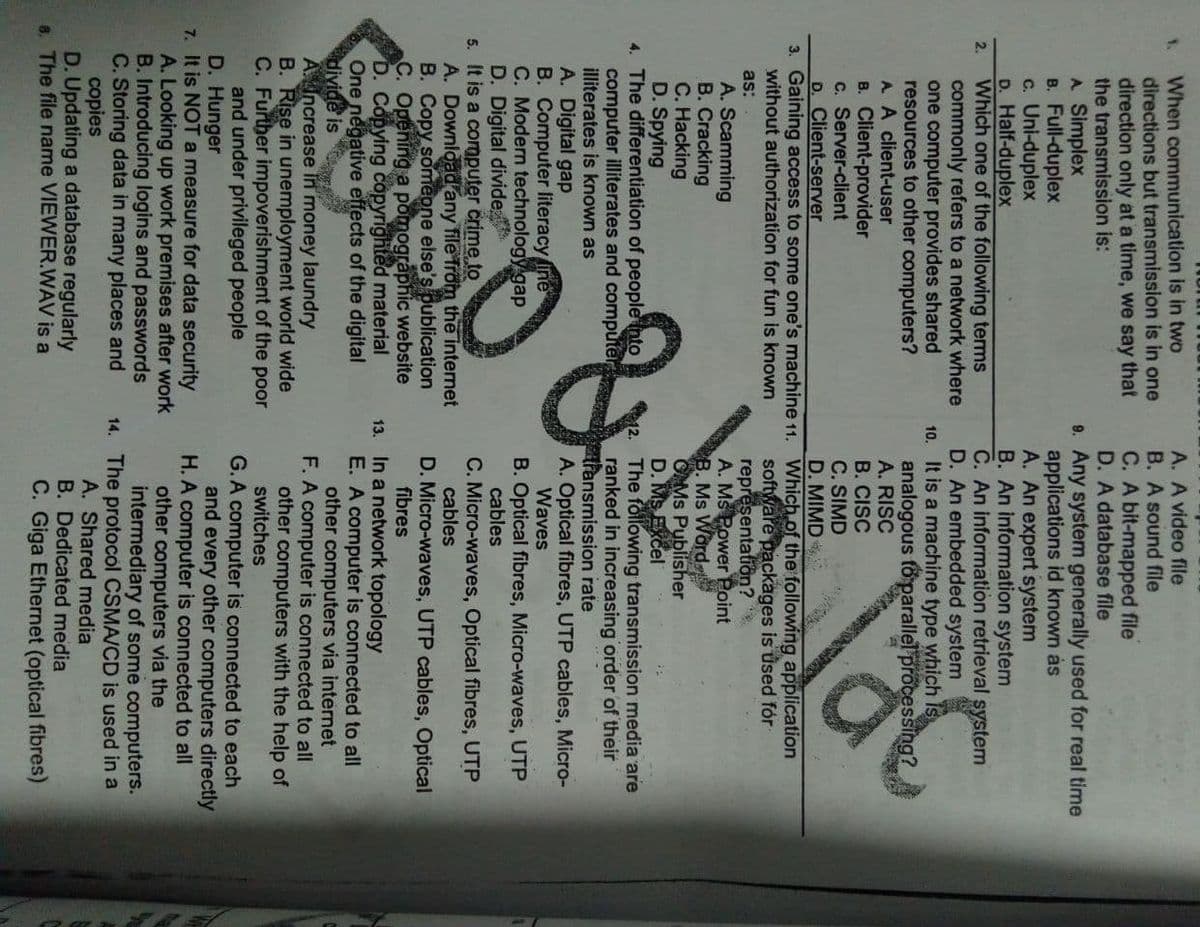
Transcribed Image Text:A. A video file
B. A sound file
When communication is in two
directions but transmission is in one
direction only at a time, we say that
the transmission is:
A Simplex
B. Full-duplex
c. Uni-duplex
D. Half-duplex
Which one of the following terms
commonly refers to a network where
one computer provides shared
resources to other computers?
A. A client-user
1.
C. A bit-mapped file
D. A database file
9. Any system generally used for real time
applications id known ás
A. An expert system
B. An information system
C. An information retrieval system
D. An embedded system
10. It is a machine type which is
analogous fo parallel processing?
A. RISC
B. CISC
C. SIMD
D. MIMD
2.
B. Client-provider
c. Server-client
D. Client-server
3. Gaining access to some one's machine 11. Which of the following application
without authorization for fun is known
software packages is used fór
representatiön?
A. MS Power Point
B. Ms Word
OMs Publisher
D. MS Excel
The following transmission media are
ranked in increasing order of their
transmission rate
A. Optical fibres, UTP cables, Micro-
Waves
as:
A. Scamming
B. Cracking
C. Hacking
D. Spying
4. The differentiation of people nto
computer illiterates and computer
illiterates is known as
A. Digital gap
B. Computer literacy ine
C. Modern technology gap
D. Digital divide
5. It is a computer crime to
A. Download any file Trom the internet
B. Copy someone else's publication
C. Opening a pomographic website
D. Copying copyrighted material
One negative effects of the digital
divide is
AIncrease in money laundry
B. Rise in unemployment world wide
C. Further impoverishment of the poor
and under privileged people
D. Hunger
7. It is NOT a measure for data security
A. Looking up work premises after work
B. Introducing logins and passwords
C. Storing data in many places and
copies
D. Updating a database regularly
6. The file name VIEWER.WAV is a
B. Optical fibres, Micro-waves, UTP
cables
C. Micro-waves, Optical fibres, UTP
cables
D. Micro-waves, UTP cables, Optical
fibres
13. In a network topology
E. A computer is connected to all
other computers via internet
F. A computer is connected to all
other computers with the help of
switches
G.A computer is connected to each
and every other computers directly
H. A computer is connected to all
other computers via the
intermediary of some computers.
14. The protocol CSMA/CD is used in a
A. Shared media
B. Dedicated media
C. Giga Ethernet (optical fibres)
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,