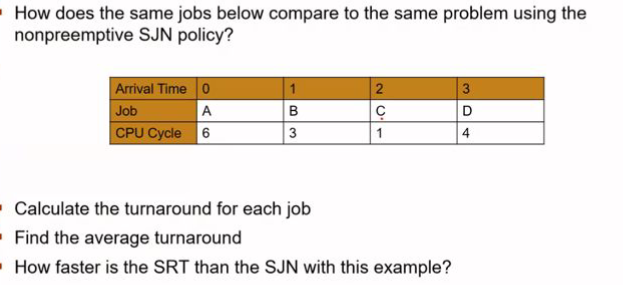
Calculate the turnaround for each job 2.Find the average turnaround 3.How faster is the SRT than the SJN with this example
Q: In c langauge program. Please show the output of the program. Thank you.
A: Code: #include <stdio.h>#include<string.h> //structures struct Date { int year; int…
Q: What are the two operating system modes, as well as the two fundamental functions of an operating…
A: Operating system has different modes of operation and the main functionality of operating system.…
Q: n java Write a method public static ArrayList append(ArrayList a, ArrayList b) that appends one…
A: import java.util.ArrayList; import java.util.*; public class Append { public static…
Q: What is the most important goal of normalization? What part do determinants play in the process of…
A: The process of Normalization: The act of structuring data in a database is known as normalization.…
Q: What are the Python operators?
A: Operators are used for performing various operations on variables and constants. The operators of…
Q: piral Model.
A: The spiral model is a risk- driven programming development process model. In light of the special…
Q: You are tasked with deploying websites on EC2 instances. The solution should be scalable and the…
A: I have provided the solution in step 2.
Q: What are the two most compelling reasons to use layered protocols?
A: Introduction: Layered protocols: These protocols are typically represented as a series of layers,…
Q: What are the two operating system modes, as well as the two fundamental functions of an operating…
A: Operating system can be defined as the communication channel form between user and the system to…
Q: Explain why creating functions is important in programming.
A: Important in programming: The functions are the most significant programming idea since they enable…
Q: What factors go into determining a program's performance? Why compare two separate applications that…
A: Here we have given a brief note related to program performance. You can find the solution in step 2.
Q: nclude the upload a file or picture of your truth table, simplified equation, and logical diagram.…
A: it is simple sum of terms in digital electronics. Basic knowledge of kmap should be enough.
Q: Determine three unique smartphone applications that would be extremely useful in your present or…
A: Statement: There are numerous smartphone applications available nowadays that can help you boost…
Q: In this assignment, you will implement the shell “engine” as the “group” component, where all…
A: Answer : The logic is simple here we have a function called system and then you can pass the input…
Q: What are the most serious threats to the organization's data?
A: Threats The risk of an inadvertent or malicious computer security breach, the lack of secrecy,…
Q: There are several methods for analysing a cybersecurity vulnerability.
A: Introduction: A cybersecurity vulnerability can be analyzed in a variety of ways. Its purpose is to…
Q: 1. Write a function invert_dict to reverse a dictionary, for example: >>> eng2sp = {'one': 'uno',…
A: Hello student Greetings Hope you are doing great. As per our policy guidelines, in case of multiple…
Q: Given the code segment below, what should be the data type of the formal parameter in the function…
A: In this question, we are asked to write the correct data type that needs to be passed in the…
Q: How is the idea of data concealing applied in the OSI model?
A: Introduction: The OSI model indicates that there are numerous places where data can be hidden.…
Q: From the greatest to the tiniest component, describe the AWS Global Infrastructure.
A: INTRODUCTION: Amazon Web Services, Inc. (AWS) is an Amazon company that offers metered…
Q: Consider the following regular expression: E = {a, b, c} RE: (ab)*c*(bc)* Draw the DFA for the above…
A: Below is the answer to above B and C part. I hope this will be helpful for you.
Q: The objective of Electronic Data Interchange in a fictional supply chain. Three instances of…
A: Interchange of Electronic Data The goal of EDI is to guarantee that business papers are sent between…
Q: What exactly do the terms static media and dynamic media mean? Please offer at least two examples of…
A: Intro Static Media: - It refers to the media which does not change. In reference to websites,…
Q: Explain the 3 types of control transfer structures in programming
A:
Q: Explain why pro fessional software designed for a customer isn't just a collection of programs…
A: Since professional software is nearly often packed with accompanying documentation such as…
Q: rements of
A: Power is Joules per second. SI Unit of Power is Watts. Joules is the SI unit of Energy. Second is…
Q: What if VoIP suffers from the same challenges with the firewall that streaming audio does?
A: Introduction: Voice over Internet Protocol (VoIP) is frequently known as IP communication, is a…
Q: From the greatest to the tiniest component, describe the AWS Global Infrastructure.
A: Global Infrastructure on AWS AWS is a globally accessible cloud computing platform. AWS is located…
Q: What is the time complexity for the given recurrence relation: 9 T(n/3) + ca > 1 cb…
A: Please refer below for your reference: I have solved using both methods and got as n^2 and for…
Q: FP programming
A:
Q: In a website or online service, what are the advantages of utilising async and await?
A: Introduction: Actually, a website asked a question about using async and await.
Q: 3. Write an Octave program to a. Read a complex number from the user b. Display its magnitude and…
A: Answer : Program :
Q: From the greatest to the tiniest component, describe the AWS Global Infrastructure.
A: Global Infrastructure AWS AWS is a global cloud computing platform. Global infrastructure is a term…
Q: The number of general-purpose processors does not need to be specified when categorising computer…
A: Introduction: Based on their computer architecture, computer systems are classified into the…
Q: When it comes to cloud computing, what role does autonomous computing play?
A: According to the question the cloud computing provides the easy way to access the servers, storage,…
Q: Java program Conditional Statements You have $12,000 to buy a car. You're given a program which…
A: CODE: import java.util.Scanner; public class Main { public static void main(String[] args) {…
Q: Explain what causes a system to become stuck in a stalemate.
A: The following situations need a systemic deadlock: Condition of Circular Delay The case of Hold and…
Q: 2. Develop a JAVA program which performs all basic arithmetic operations. 3. Present type casting in…
A: Code: public class Main{ public static void main(String[] args) { //Varibles of…
Q: tes are stored in memory locations from 8050h to 805Fh. Write 8085 ALP to transfer the the locations…
A:
Q: What is the problem domain of The workflow management system
A: The workflow management system A workflow management system is a piece of software that aids in…
Q: Explain the concerns with ISPs limiting Internet usage.
A: Provider of Internet Services (ISP): The internet service provider assists the user in connecting…
Q: Python Create a program in python whereas: Given a list ot X objects, u want to perform:…
A: I give the code in Python along with the output and code screenshot
Q: 1. You are a computer systems manager. An employee is out sick and another employee requested that…
A: The answer is given below.
Q: What are the advantages of having a working knowledge of computers?
A: Introduction: If you have the fundamental computer abilities, you open yourself up to a world of…
Q: Write a program which reads the information from the file and outputs the same information to…
A: C++: C++ is a general purpose high level programming language. It was developed by Bjarne Stroustrup…
Q: Create a display of link list
A: Answer:
Q: Explain the benefits and downsides of both write-through and write-back cache modification in shared…
A: Write-through: The memory content is updated as soon as the cache contents are adjusted concurrently…
Q: # Python program to find sum of elements in list total = 0 # creating a list list1 = [11, 5, 17, 18,…
A: Code Explanation
Q: In what ways has the Electronic Transaction Act of 2008 boosted the chances of convicting people who…
A: Ghana has improved it heir laws for persons carrying out ICT frauds by listed some ways:- The Act…
Step by step
Solved in 2 steps with 4 images

- a Using the following Test Metrics calculate (i) Test coverage & No. of user stories (ii) Defect density No. of test cases for all user stories Average noof test cases per story 150 640 12.8 600 510 No. of defects identified by QA 29 No. of defects identified by Client 3 Total no. of test cases executed No. of test cases passedThe goal of redundancy is to reduce what variable? mean time to recovery median time between failures average time between failures median time to recoveryWhich one of the answer below is NOT part f IAM best practices? Have a strong password rotation policies Use access keys for programmatic access Use roles to access services Always use ROOT account to login
- Based on the following System log at time of system crash, answer the questions that follows: What are the recovery actions in each of the following recovery techniques? a. Deferred Update b. Immediate update (Undo/Redo)24) Which of the following is not correct about DLP(Daa Loss Prevantion) when a policy violation is detected by the D.L.P agent a) It is reported back to the D L P server b) It Quarantine the data until later C) It Alert a supervisor of the request d) It desen't take any actionWhich of the following internal control procedures would safeguard against the aforementioned dangers? An employee conceals the theft of future cash payments from a client by writing off the accounts receivable amount as uncollectible.
- A small insurance company has an online application system that allows its customers to interactwith the business (e.g., log claims). Backups of the customers’ details are done on a spreadsheetdocument stored on Google drive. However, anyone who has access to the Google drive link ofthe file can view and modify all the customer details. On the backup, the system administratordoes not have visibility of the modifications made on the file. By analysing the scenario above, use the security design principles to criticise theoperations of the small insurance company and propose any two simple controlsthat could influence a good security program.XACMLThe following represent two examples of XACML 2.0 policies. Which single one of these statements is false:a) An access request from Alice Samson at 14:00 on 01 January 2018 according to the first policy, will failComputer Security Coursework, 2020/2021 Page 11b) Purpose of the last rule in each of the two policies is to deny any requests that are not covered by the previous permitting rules in each of the two policiesc) If the two policies above were combined into one policy set in the order they appear with a policy-combining algorithm “first-applicable”, then the outcome of the request by Alice Samson be at 14:00 on 01 January 2018 to access the “server.acme.co.uk/docsserver” would be accepted when evaluated against the new policy setd) Adding to the AND of the condition a third part with a “anyURI-equal” function applied to an attribute “machine.alice.come” will strengthen the condition by also requiring that Alice’s request arrives from a particular URI address equal to…Classify each of the following vulnerabilities using the PA model. Assume that the classification isfor the implementation level. Remember to justify your answers.(a) The presence of the “wiz” command in the sendmail program (see Section 24.2.9).(b) The failure to handle the IFS shell variable by loadmodule (see Section 24.2.9).(c) The failure to select an Administrator password that was difficult to guess (see Section 24.2.10).(d) The failure of the Burroughs system to detect offline changes to files (see Section 24.2.7) PA : Improper protection domain initialization and enforcement Improper choice of initial protection domain (domain) Improper isolation of implementation detail (exposed representations) Improper change (consistency of data over time) Improper naming (naming) Improper deallocation or deletion (residuals) Improper validation (validation of operands, queue management dependencies) Improper synchronization Improper indivisibility (interrupted atomic…
- Classify each of the following vulnerabilities using the Protection Analysis Mode( PA) model. Assume that the classification isfor the implementation level. Remember to justify your answers.(a) The presence of the “wiz” command in the sendmail program (b) The failure to handle the IFS shell variable by loadmodule (c) The failure to select an Administrator password that was difficult to guess (d) The failure of the Burroughs system to detect offline changes to files Protection Analysis Mode( PA) model: Improper protection domain initialization and enforcementa. Improper choice of initial protection domainb. Improper isolation of implementation detailc. Improper change, consistency of data over timed. Improper naminge. Improper deallocation or deletion2. Improper validation, validation of operands, queue management3. Improper synchronizationa. Improper indivisibility, interrupted atomic operationsb. Improper sequencing, serialization4. Improper choice of operand or operationBetween Full, Incremental, and Differential A.) Which one backs up the things that have been changed or added since the Last Full Back Up? B.) Which one backs up the things that have changed or added since any type of backup.Why would an attacker execute the command “uname –a”. Group of answer choices Find a users name Find a priviledge users name Find an exploit that affects that particular system. Find the name of the system

