Create an Java Postfix converter using the algorithm provided. Thank you
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter18: Stacks And Queues
Section: Chapter Questions
Problem 15SA
Related questions
Question
100%
Create an Java Postfix converter using the
Thank you
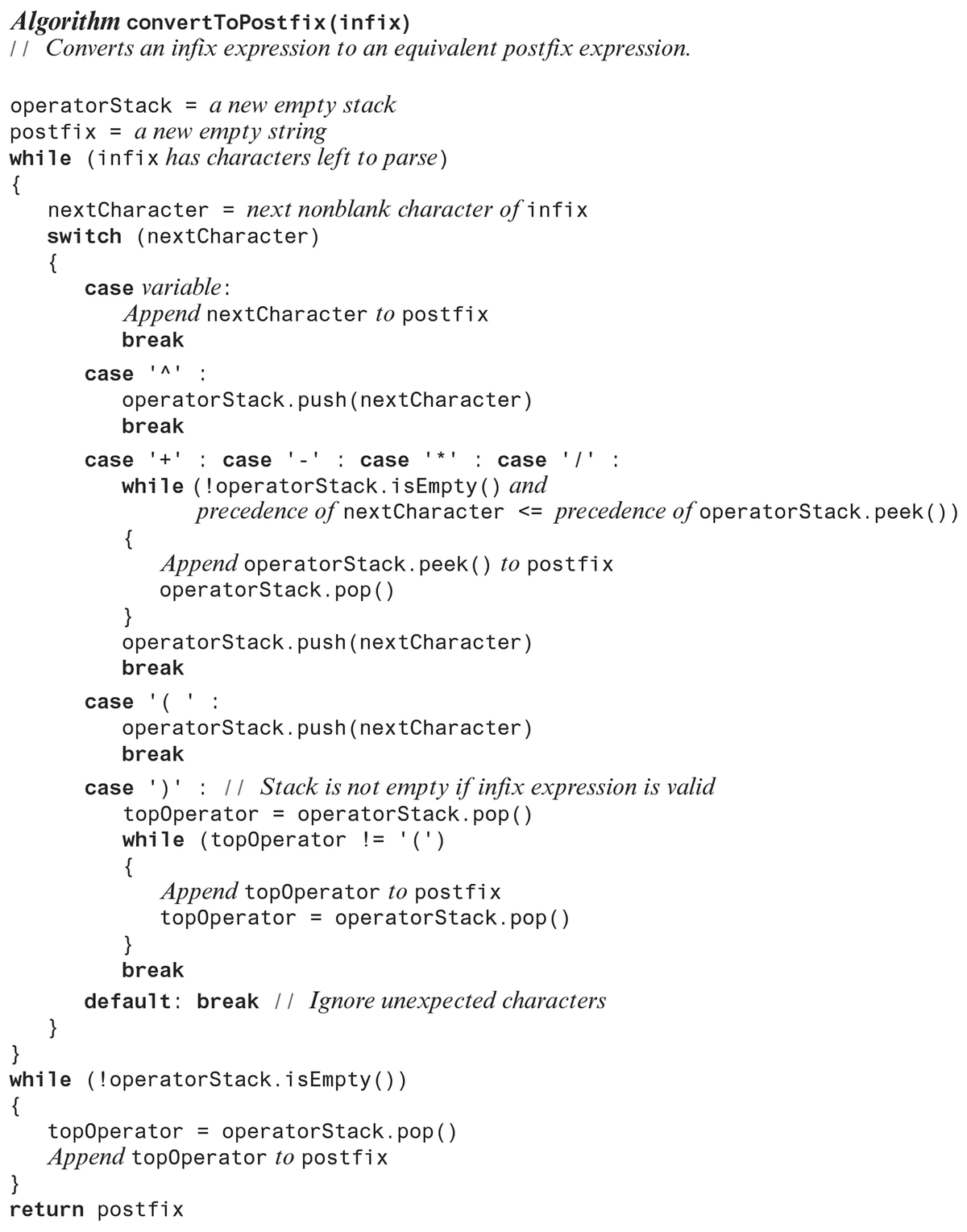
Transcribed Image Text:Algorithm convertToPostfix (infix)
11 Converts an infix expression to an equivalent postfix expression.
operatorStack = a new empty stack
postfix = a new empty string
while (infix has characters left to parse)
{
nextCharacter = next nonblank character of infix
switch (nextCharacter)
{
}
}
while
{
case variable:
Append nextCharacter to postfix
break
case 'Λ'
operatorStack.push(nextCharacter)
break
case '+': case
: case
while (!operatorStack.isEmpty() and
precedence of nextCharacter <= precedence of operatorStack.peek ())
Append operatorStack. peek () to postfix
operatorStack.pop()
{
}
break
case '(':
I
operatorStack.push(nextCharacter)
I* I
operatorStack.push(nextCharacter)
break
case ')': // Stack is not empty if infix expression is valid
operatorStack.pop()
=
topOperator
while (topOperator != '(')
{
: case '/' :
Append topOperator to postfix
topOperator = operatorStack.pop()
(!operatorStack.isEmpty())
}
break
default: break // Ignore unexpected characters
}
return postfix
topOperator = operatorStack.pop()
Append topOperator to postfix
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 3 images

Follow-up Questions
Read through expert solutions to related follow-up questions below.
Follow-up Question
Can you provide further comments explaining the functionality of what each line of code is doing? I know its a lot but it helps me learn.Thank you
Solution
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning