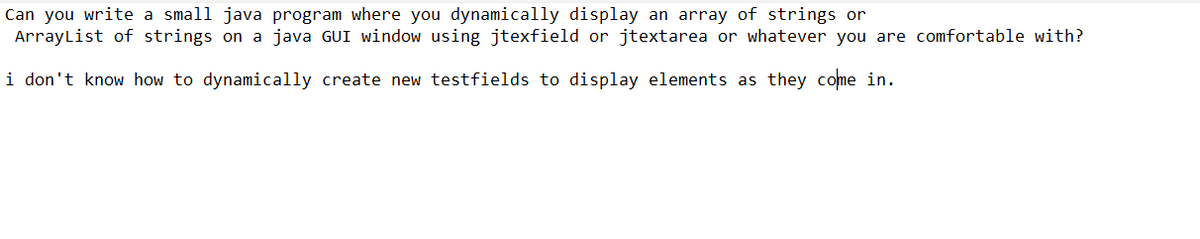
Can you write a small java program where you dynamically display an array of strings or ArrayList of strings on a java GUI window using jtexfield or jtextarea or whatever you are comfortable with? i don't know how to dynamically create new testfields to display elements as they come in.
Q: Think about how important wireless networks are in modern developing countries. In many…
A: Think about how crucial wireless networks are in today's developing nations. LANs and physical…
Q: /Assume that the microprocessor can directly address 64K with a R/W' and 8 data pins The memory map…
A: Given that, a microprocessor can directly address 64K with a R/W and 8 data pins. That means it…
Q: Examples may be used to differentiate between the scalar and superscale CPUs. The complexity of the…
A: A scalar processor runs concurrently on a single data item. A vector processor processes many bits…
Q: Here are some examples of the many programming languages: Give a brief explanation of each one
A: Types of programming languages: These languages concentrate more on what to do than how to do it.…
Q: Q2 Subtract the following numbers using 2's complement: i) 01110101 iii) 01101111 - 00010001 -…
A:
Q: The services and functions provided by an operating system can be divided into two main categories.…
A:
Q: Library Management system: This system allows the students to search books,request books etc.…
A: Below I have provided the solution of all the case study of the given application.
Q: Suppose nodes A and B are on the same 10 Mbps broadcast channel, and the propagation delay between…
A: The question has been answered in step2
Q: In the Backtracking algorithm, you are allowed to use Depth-first search. True or false
A: Backtracking: Backtracking is a method for problem-solving based on an algorithm. It constructs a…
Q: Why is it necessary to create a program specifically for debugging in order for the debugger to…
A: The above question is solved in step 2 :-
Q: How many internal and external computer components, including with their power sources, are directly…
A: External of Computer: A hardware component that is placed outside of the computer is referred to as…
Q: What different types of technical solutions are used in the process of detecting network intrusions?
A: Network Intrusions: Systems for detecting network intrusions are strategically positioned throughout…
Q: What is meant by the term "debugging"?
A: Institution: Finding and fixing weaknesses in software code, sometimes referred to as "bugs," that…
Q: What are the Page-table requirements in particular?
A: Page table has page table entries where each page table entry stores a frame number and optional…
Q: C Program to print half pyramid pattern using numbers Output should like this. 5 1 12 123 1234 12345
A: All Pyramid patterns are in a polygon structure.
Q: Make sure to distinguish between validation and verification. Provide detailed examples.
A: Verification Verification is a procedure that assesses the software's quality. All of the tasks…
Q: Which two technological subcategories are present in almost all current wireless networks?
A: Given Question: Which two technology subcategories can be found in nearly all modern wireless…
Q: The structural elements of Ven Neumann are explicable.
A: Ven Neumann architecture's main components are: Both information and instructions are kept in main…
Q: neither one of them. -3m-4m.-3m...... ..3m....... AP₁ STA 5,3m-- AP₂ -1,2m- --1,2m--
A: 241/500 Words) EN WiFi6 enterprise path loss model : The WiFi6 enterprise path loss model…
Q: What features do all Agile frameworks share? Next, click Send. a certain number of iterations A…
A: Self-Organized Teams: Every Scrum project has to have teams that can organize themselves. According…
Q: Consider a variant of the RR scheduling algorithm where the entries in the ready queue are pointers…
A: a) The process would be run twice as many times Explanation: In effect, that process will have…
Q: We have a hash map that wasn't made very well since all the values were dumped into the same bucket…
A: Given: Hash tables are groups of arranged things that make it possible for them to be readily found…
Q: This is partly because of the remarkable potential that modern computers have.
A: John von Neumann was born in 1903 in Hungary, and he is known to be the inventor of Computers, or…
Q: Program to print inverted full pyramid pattern using stars
A: As language is not provided doing it in multiple languages:
Q: Implementations of database systems often employ strict two-phase locking. Why is this technique so…
A: We need to provide reasons for employing strict two-phase locking in database systems.
Q: How is software maintenance evaluated?
A: Software maintenance is a process of changing, modifying and updating the software based on the…
Q: Answer the following three questions about Bash scripting: 1. What are the variables $1, $2, $3,…
A: 1) In bash scripting, positional parameters passed to the script from either the command line or a…
Q: How do an embedded system, an embedded control system, and an instruction set processor vary from…
A: Introduction: Computer systems that are part of larger mechanical or electrical systems are known as…
Q: (2) Compute U = SHA(S) SHA ((S+ 1) mod 28), where SHA is the Secure Hash Algorithm (see Section…
A: comparesion for given function to secure hash algo is:
Q: What attributes are necessary for software test engineers to succeed?
A: For software testers, imagination is crucial. They can use it to create testable mental prototypes…
Q: 3. Write a function TrapezoidalRule.m which takes three input arguments f, a and b and returns one…
A: function [I] = TrapezoidalRule(f, a, b)% This function calculates the integral of a function, f,…
Q: Are you in agreement with Mukherjee's assertion that a human rights-centered approach to…
A: Answer : - yes
Q: On the other hand, fewer layers than required by the OSI model are used by the vast majority of…
A: Definition: The TCP/IP protocols offer the foundational principles upon which the Internet was…
Q: Suppose nodes A and B are on the same 10 Mbps broadcast channel, and the propagation delay between…
A: Suppose nodes A and B are on the same 10 Mbps broadcast channel, and the propagation delay between…
Q: What is computer science, and how is it unique from other disciplines? How exactly do they operate?
A: Information technology: It is a sort of research that examines computer hardware and software. It…
Q: What is an object graph in core data? collection of objects that are connected with one…
A: The correct answer for the above mentioned question is given in the following steps for your…
Q: Each of the three user processes that make up an operating system utilizes a total of two units of…
A: Introduction An operating system is programming that plays out every one of the essential errands…
Q: Have you ever seen someone being bullied or harassed online by another person? What did you feel…
A:
Q: Separate frequency from temporal division multiplexing (According to commuter communication network)
A: The solution to the given question is: Multiplexing is the sharing of media or bandwidth. A process…
Q: One of the criteria used to classify the various kinds of computers is the quantity of processors…
A: Based on their computer architecture, computer systems are divided into the following groups:…
Q: Why is it important for the scheduler to distinguish I/O-bound programs from CPU-bound programs?
A: Answer:
Q: What distinguishes software development from web design?
A: reasons that distinguishes software development from web design is:-
Q: Why is it important for people to be adept with spreadsheets in the current environment? Please…
A: Except for email, spreadsheet programs may be the most popular business applications in use today,…
Q: How do the methods for preventing deadlock and avoiding it differ from one another?
A: Introduction: A deadlock arises when group of processes in which each process has a resource and…
Q: When did someone become computer literate?
A: computer literate : Frequently, this phrase is used to denote the most fundamental abilities…
Q: Are there any governance issues arising from the switch from on-premise servers to an IaaS…
A: Introduction: Are there any issues with the governance of moving from on-premise servers to an IaaS…
Q: Subject: programming language C++ Q1.Write a simple program that overload + operator for…
A: Below I have provided C++ Programming. Also, I have attached the screenshot of the code and output…
Q: What are the advantages and disadvantages of manual walkthroughs over print statements for…
A: The above question is solved in step 2 :-
Q: What purpose does debugging serve, and how? What relevance does this have to testing?
A: Debugging objectives: The source code of a programme should be examined to ascertain what happens in…
Q: A specific class of C++ variable is a pointer variable. Do you understand how to utilize it?
A: The solution to the given question is: In C++ , a pointer is a variable (also called a locator or…
Don't want copy paste answer want unique answer
Step by step
Solved in 3 steps with 1 images

- Using the draw.io site or a flowcharting tool of your choice, create a flowchart that models a complete Java program called StringSlicer that uses methods to: Get a String from the user at the command line Populate an ArrayList of Character data (the wrapper class), with each char in the String represented as a separate Character element in the ArrayList Output each Character to the command line, each on a separate lineThe Character class is provided in the Javalibrary. Provide your own implementation for this class. Name the new classMyCharacter.Write a painting Program that allows the user to paint shapes and lines in many defrent colors here's using Java language for github
- Look at the API of the Point class and find out how to construct a Point object. Write a Java program “PointTester”, that constructs two points with coordinates (3, 4) and (–3, –4). Find the distance between them, using the distance method. Print the distance, as well as the expected value. (You may draw a sketch on graph paper to find the value you will expect.) - Update your program so it randomly select coordinate points (x,y), where −50 ≤ ? ≤ 50 ??? ? ∈ [−90, 90].Write JavaFX code with an intuitive GUI design that can generate a Fibonacci number sequence of a certain length (e.g., 30-50 numbers) via pressing a ‘Fib Gen’ button. The program should have at least two filtering functions on the generated number sequence.What must be done to get images to show up in a Java jFrame
- Create a JavaFX GUI with a GridPane of Labels with eight rows and nine columns. Remember that the row and column indices are zero based, and that GridPane's setters use the column index first and the row index second. Set the text of each Label to the *sum* of the row number and the column number. For example, the text of the label at row 3, column 2, should be "5." Set the text for the Labels in the same nested loops you use to create the Labels. If you write 72 different lines of code to set the text, you are doing it wrong! You do not need to use event handlers in this checkpoint. Write a .css file that gives the labels a color scheme you like. Remember the odd syntax for linking stylesheets to JavaFX GUIs. Where sc is a reference to the Scene:sc.getStylesheets().add(getClass().getResource("application.css").toExternalForm());Write a main application called yupi.java, and a GUI (that extends JFrame) called VowelGUI.java.The main program should open a file called “input.txt” which will contain a paragraph.Read the lines from the file until there are no more. For each line, count the number of individualvowels in that line, using a counter for the vowels ‘A’ and ‘a’, a counter for the vowels ‘E’ and ‘e’, and soforth.The GUI should have a grid layout of one row and two columns (column 0 and 1). Column 0 shouldcontain the original text from the file. Column 1 should contain 5 lines displaying the count of each ofthe vowels.Create a gui in Java using swing or jframe Sample example is here
- What is a HashMap? What is its purpose and how do you use it? Answer these questions in writing, and use the Java library documentation of Map and HashMap for your responses. Note that you will find it hard to understand everything, as the documentation for these classes is not very good. We will discuss the details later in this chapter, but see what you can find out on your own before reading on.Using the draw.io site or a flowcharting tool of your choice, create a flowchart that models a complete Java program called StringSlicer that uses methods to: Get a String from the user at the command line Populate an ArrayList of Character data (the wrapper class), with each char in the String represented as a separate Character element in the ArrayList Output each Character to the command line, each on a separate line The flowchart should be sufficiently detailed and follow the standards we've showcased in our course.Write an application that displays a JFrame containing the opening sentence from A Christmas Carol. Add a button to the frame in the JBookQuote program. When the user clicks the button, display the title of the book that contains the quote in the available JLabel using the setText() method. import javax.swing.*; import java.awt.*; import java.awt.event.*; public class JBookQuote2 extends JFrame implements ActionListener { FlowLayout flow = new FlowLayout(); JLabel msg1 = new JLabel("To begin with,"); JLabel msg2 = new JLabel("Marley was dead."); JButton button = new JButton("Click for source"); JLabel msg3 = new JLabel("** A Christmas Carol **"); public JBookQuote2() { // Write your code here } @Override public void actionPerformed(ActionEvent e) { // Write your code here } public static void main(String[] args) { JBookQuote2 aFrame = new JBookQuote2(); aFrame.setSize(260, 150);…

