Capital - Small = ? Code in C language
Q: Define the number of CPU clock cycles.
A: The number of CPU clock cycles is the number of clock cycles the CPU needs to execute a single instr...
Q: Help please! I need my code to use an exception handling method to check if the user entered a corre...
A: #include<bits/stdc++.h>using namespace std; // This Function Generate All Possible Word Who Ma...
Q: A superscalar computing system with the 2nd degree of Superscalar and with 3 processing units. The i...
A: Let's see the solution in the next steps
Q: Provide short answers to the following: How do you determine whether an IP address is a multicast ad...
A: Introduction: AS PER OUR POLICY “Since you have posted a question with multiple sub-parts, we will s...
Q: 1- Compute the subnet mask, subnet address, broadcast address and the IP host ranges of 192.168.3.55...
A:
Q: Draw a sequence diagram for the following case. The H. I. Topi School of Business operates interna...
A:
Q: WHAT IS CRYPTOCURRENCY AND HOW DOES IT WORK?
A: the answer is
Q: To check the memory state, what command is used?
A: Introduction: To check the memory state, what command is used? It's the same thing that happens on ...
Q: (Memory Interface) A read-only memory and a microprocessor need to communicate asynchronously. The p...
A: Given The answer is given below.
Q: Is it still necessary to maintain information security today?
A: Introduction: Organizations may safeguard both digital and analogue information by converting the or...
Q: item. This operator can be used anywhere you can use an unsigned integer, including in mathematical ...
A: Please find the answer below :
Q: Describe how a packet will be processed at a router that is configured with ACLs (Access Control Lis...
A: Users and systems may be permitted or refused access to an object or system resource using an access...
Q: What is the difference between Latency Based R outing and Geo DNS?
A: Intro The question is about difference between Latency Based R outing and Geo DNS and here is the so...
Q: Use the "uniq -c" command to sort and summarize the total occurrences of sudo access by month and us...
A: use of uniq -c for display number of repetitions for each lines. if we assume given file name datafi...
Q: Suppose LENGTH is defined as in the program of Fig. 2.9. What would be the difference between the fo...
A: Given: LDA LENGTHSUB #1 LDA LENGTH - 1
Q: Inside most wireless networks, a collision management is required. Please name the most frequently u...
A: Wireless network is the network in which the data transmissions are done without use of any wired co...
Q: Explain how inline style sheets overrule the HTML document's style.
A: What is a Style Sheet: A Style Sheet is a collection of style rules that advises a browser on how to...
Q: Python question Write a program that calculates the average word length in a sentence entered by the...
A: THIS PYTHON PROGRAM TAKES A SETANCE AS USER INPUT AND PRINT THE AVERAGE WORD LENGHT def average(...
Q: What exactly is ethical system theory?
A: Intro the question is about What exactly is ethical system theory and here is the solution in the ...
Q: Using the Java programming language write a program that takes an email address as an input from the...
A: Please refer below commented code with output screenshot: import java.util.*;class Valid_email { ...
Q: ar a grinding noise as the printer attempts to move the carriage, what should you do
A: Printer cart is a combination of holding ink cartridges and slide back and forth to transfer ink t...
Q: Imagine that you are putting in place for your university's first time a new room reservation system...
A: Introduction: The conversion technique that we will employ will be as follows:
Q: umber of images to download. It will also have a button that when clicked will download the images. ...
A: It is defined as an API feature that is available in Elasticsearch helps in taking care of giving an...
Q: Q#02 Make following design in HTML using Flexbox and Grid both designs should be on same HTML page a...
A:
Q: It's important to know what two types of software are. In what ways are they different?
A: INTRODUCTION: We need to tell different types of software.
Q: Design a complete GUI Application with as many components as possible with combination of different ...
A: To design the GUI Application with the combination of different layout managers.
Q: Why would a systems analyst be required to perform the role of translator? What types of organisatio...
A: A systems analyst must function as a translator to interpret technical difficulties into understanda...
Q: This program intends to display the user's favorite food. Declare String favoriteFood Display "What ...
A: Given: To write a program that displays users favorite food. Program is written in Java.
Q: Write a program that removes all non alpha characters from the given input. Ex: If the innut is:
A: Note: Code works perfectly. I have attached a screenshot of the source code and output for your refe...
Q: n° +3 For the function ƒ defined by f(n) = for n e N, show that f(n) e O(n²). n3 + 9 (Use the Ad-hoc...
A: The function f defined byf(n)=n5+3n3+9 for n E N
Q: What are the challenges that cloud computing faces?
A: Introduction: Confronting the complexities that come with traditional data.
Q: What exactly is an operating system? Name a few popular operating systems.
A: Operating System: The operating system (OS) is a graphical interface that connects a computer user t...
Q: How blockchain could allow transferability?
A: Introduction: Blockchain is a safe technology that allows you to send and receive digital data via a...
Q: Explain in detail what the collision domain and broadcast domain of a switch and a router are and ho...
A: Answer: The collision domain and broadcast domain both are very important for networking. A collisio...
Q: What is the output of following code segment ? int[] a = { 9, 16, 25, 1, 4}; Array...
A: Intro The given code segment: int[] a = { 9, 16, 25, 1, 4};Arrays.sort(a);System.out.print( Arrays....
Q: (a) Choose a number between 60 and 80. This will be numberA. Choose another number between 25 and 50...
A:
Q: This is very confusing for me; we cant use import statements; Please create code for me with the f...
A: Given :- MCS Roast Being tired of the challenging assignments given by the MCS Professors, students ...
Q: bisimulation
A:
Q: What was ICT in the past? What is ICT in the present scenario? What are the features of ICT?
A: ICT stands for Information and Communications Technology. It contains the technical tools and the se...
Q: 1. Given the linear combination below, try to create a corresponding matrix representing it. Use col...
A: .As per bartleby guidelines for multiple questions asked, I am allowed to answer only first question...
Q: What is embedded Linux?
A: INTRODUCTION: We need to tell what is Embedded Linux.
Q: What are the key advantages and disadvantages of cloud-based data storage?
A: Intro Cloud-Based Data Storage is basically a data storage method that is based on cloud computing a...
Q: Write a program that takes website names as keyboard input until the user types the word stop and co...
A: Given :- Write a program that takes website names as keyboard input until the user types the word st...
Q: What's the difference between soft and hard links, and how do you explain it?
A: Introduction: It is regarded as a mirror image of the original file. It's regarded as a symbolic lin...
Q: When compared to relational databases, hierarchical databases have several advantages. Positive or n...
A: The primary distinction between relational and hierarchical databases is that relational databases a...
Q: what is the coding for panel data for fixed effects in stata?
A: use xtset industryvar in Stata to indicate that you want fixed effects for each unique value of ind...
Q: Question No.6: Construct PDA for the following languages. a) L= {a"b"c*+" | m, n € N} b) L= {a"b"+l ...
A:
Q: Please explain the difference between programmed I/O and interrupt-driven I/O.
A: Logic:- reading data from device , processing it and again getting back processed data to output i...
Q: Write a function square in RISC-V that takes in an integer n ad returns its square. If n is not posi...
A: a function square in RISC-V that takes in an integer n ad returns its square. If n is not positive, ...
Q: Explain briefly what Software Outsourcing and Cloud Services are for.
A: Introduction: It is necessary to make a decision on software outsourcing and cloud computing.
Capital - Small = ?
Code in C language
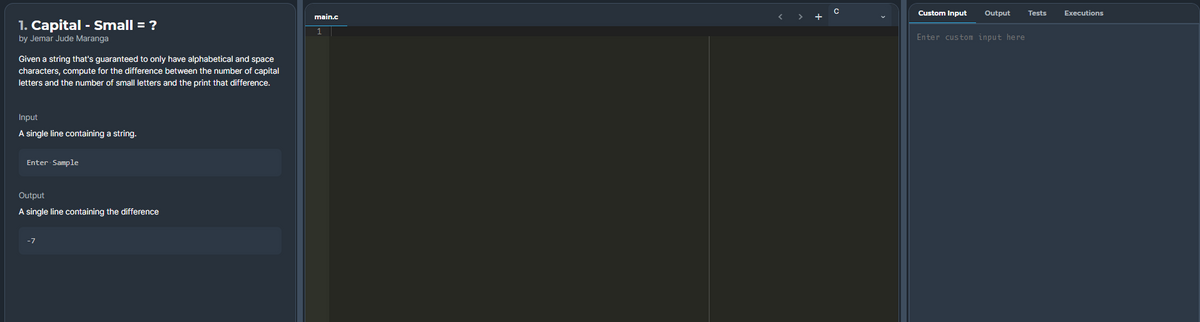
Step by step
Solved in 3 steps with 2 images

- Create a string from two given strings by concatenating common characters of the given strings. Sample Input harry, hermione dean, tom Sample Output hrrhr Nothing in common. Again, you have lost your USIS password!! You went to the registrar office and requested for a new password. This time, you need to follow some rules to set your password. Otherwise, they won't change it. The rules are At least one lowercase letter At least one uppercase letter At least one digit (0-9) At least one special character (_ , $ , #, @) Your task is to find whether a given password follows all those rules. If it breaks any rule, you have to print Lowercase Missing, Uppercase Missing, Digit Missing or Special Missing respective to the missing case. For more than one rule break, print all the rules that were broken (order doesn't matter). If the password is ok, print OK. Sample Input ohMyBR@CU ohmybracu OhMyBR@CU20 Sample Output Digit missing Uppercase character missing,…Write a program that will continually ask the user to enter a string from standard input until user entersQ or q to quit.After reading the user’s input string, the program will count number of characters, vowels, lowercaseletters, uppercase letters, number of digits, number of other characters and number of words from theuser’s input string. You can use getline(cin, inputString) to read entire line. Please refer to my previouslecture on data validation. http://www.cplusplus.com/reference/string/string/getline/Characters: counts everything (user input length)Vowels: a e i o u A E I O ULowercase letters: any characters a-zUppercase letters: any characters A-ZDigits: 0-9Other characters: mean any character that is not alphanumeric.You can use C++ library function to check if a character is:• islower, isupper: - http://www.cplusplus.com/reference/cctype/islower/• Make sure you include#include <ctype.h>please please Here's the python script for the lab. Can you answer only 11.a,b,c,d,e? PLease from scipy import randomimport numpy as npimport matplotlib.pyplot as plt i = 1 # set a value for current in Amperes (A)B = 2 # set a value for magnetic field in Tesla (T)R = 1 # set length of wire in meters (m)a1 = -R # set left end point of straight wireb1 = R # set right end point of straight wirea2 = 0 # set left end point of curved wireb2 = np.pi # set end point of curved wireN = 1000 # set number of intervals N def f(x):return 1 def g(x):return np.sin(x) # generate an array of all zeroesarray1 = np.zeros(N)array2 = np.zeros(N) # change each entry in array to a random number between a and bfor i in range(N):array1[i] = random.uniform(a1,b1)array2[i] = random.uniform(a2,b2) # compute summation over all random numbers in arrayintegral_straight = 0.0integral_semicirc = 0.0 for i in array1:integral_straight += f(i) for i in array2:integral_semicirc += g(i) # compute the average value for…
- Write a program that asks the user to enter a word that contains the letter a. The programshould then print the following two lines: On the first line should be the part of the string upto and including the first a, and on the second line should be the rest of the string. Sampleoutput is shown below:Enter a word: buffalobuffaloCreate a program that takes in an even-sized String and prints out the first half concatenated with original string separated by a single space. Sample run 1: Enter a single string: HelloThere Output: Hello Hello ThereWrite a program that reads a character and a string (an entire line, which may include spaces or tabs), and outputs the number of times the character appears in the string. Hint: use getline(cin, mystring) to read the entire line including spaces. Use mystring.length() to know how many characters. But to avoid a glitch when getline gets an empty string following a cin, do the following sequence: cin >> mychar; /* get character. cin leaves the newline in the input buffer*/ cin.ignore(80,'\n'); /* remove newline from the buffer, which getline would see as empty line*/ cout << "Enter a string: "; //prompt for string getline(cin, mystring); Example program run (the user types only the word "Monday" and the letter "a"): Enter character to count: a Enter a string: Monday count = 1 Example program run: Enter character to count: a Enter a string: Today is Monday count = 2 Example program run: Enter character to count: b Enter a string: Today is Monday count = 0 #include…
- Write a program that takes a **string** as input and outputs “Binary Number” if the string contains only 0s or 1s. Otherwise, outputs “Not a Binary Number”. ===================================================================== **Sample Input 1:**\01101101101 **Sample Output 1:**\Binary Number ===================================================================== **Sample Input 2:**\12344ab0 **Sample Output 2:**\Not a Binary Number ===================================================================== **Sample Input 3:**\10127490111 **Sample Output 3:**\Not a Binary Number ===================================================================== **Sample Input 4:**\Binary Number **Sample Output 4:**\Not a Binary Number #todo#assign the result string to variable "out_str"def task3(in_str): # YOUR CODE HERE return out_strWrite code and output screenshot. Correct answer will upvoted else downvoted. Winter occasion will be here soon. Mr. Chanek needs to enliven his home's divider with decorations. The divider can be addressed as a double string an of length n. His #1 nephew has one more double string b of length m (m≤n). Mr. Chanek's nephew adores the non-negative integer k. His nephew needs precisely k events of b as substrings in a. Be that as it may, Mr. Chanek doesn't have a clue about the worth of k. Thus, for every k (0≤k≤n−m+1), track down the base number of components in a that must be changed to such an extent that there are by and large k events of b in a. A string s happens precisely k occasions in t in case there are actually k various sets (p,q) with the end goal that we can get s by erasing p characters all along and q characters from the finish of t. Input :The primary line contains two integers n and m (1≤m≤n≤500) — size of the double string an and b separately. The subsequent line…Go to https://www.gutenberg.org and find any book of your choice. Select the option "Plain Text UTF-8", to open the book in the browser. An example: https://www.gutenberg.org/ebooks/244 Copy a few lines or short paragraph from the book of your choice and store it in a variable. Using the string methods and loop, print the following: a. The length of the string b. Number of uppercase letters in the entire string c. Number of lowercase letters in the entire string d. Number of digits (if any) e. Number of spaces **** SCRIPT FROM BOOK*** Snow and ice on that mountain. Nothing but snow. The wind drove it with a howl against the windows, where it stuck on the warm panes. Sometimes I could just make out the blur of the semaphore lights and sometimes I couldn’t. All day the blizzard had dumped its swirling load about us, and now, when night closed down, the storm took the tower in its teeth, shaking it like you’ve seen a dog shake a rat.
- 1. Given the following code, determine its output.StringTokenizer st = new StringTokenizer(“ABC 55*975/%”, “ +-*/%” , true);while (st.hasMoreTokens( )){System.out.println(st.nextToken( ));} 2. Write the Java statements to split the string:May I ask , , , , , , , has anyone altered the algorithm today?into tokens using the letter a as a delimeter.Print each token on a separate line. Use the String class split method, not Stringtokenizer.Show what the output is.Here is the code i have written so far, please finish it #include <stdio.h>#include <cstack.c> int i=-1;int nextstate=0;cstack top; init_cstack(&top);while(1) switch{ case 0: i++; if (is_open(my_input[i])) nextstate= 1; else if (is_close(my_input[i])) nextstate= 2; else if (my_input[i] == '\0') nextstate= 3; else nextstate= 4; break; case 1: if(!is_cfull()){ cpush(&top, my_input[i]); nextstate= 0; } else{ printf("Error! Stack is full\n"); exit(0); } break; case 2: if (!is_cempty(top)){ if(is_brother(cpop(&top), my_input[i])){ nextstate= 0; } else{ printf("Error! Delimiter do not match\n"); return FALSE; } } else{ printf("No open delimiter to compare to\n"); return FALSE; } break; case 3: if…Write a program that reads the user's first name and last name, and then use them to create a UPM email for the user. If the total number of characters in the user's full name, (first name + last name), is less than 10 letters, you should use the full name to create the user’s email. The general format of the user’s email should look like this: firstName.lastName@upm.edu.sa For example: First name = Ali Last name = Omar Total number of letters in both first and last names = 7 letters (<10 letters) Output = omar.ali@upm.edu.sa If the number of characters in the user's full name, (first name + last name), is greater than or equal to 10 letters, you should only use the first character in the user’s first name, and the whole last name to create an email. For example: First name = Abdullah Last name = Omar Total number of letters in both first and last names = 12 letters (>=10 letters) Output = a.omar@upm.edu.sa Note: you can assume the user will always enter lowercase letters











