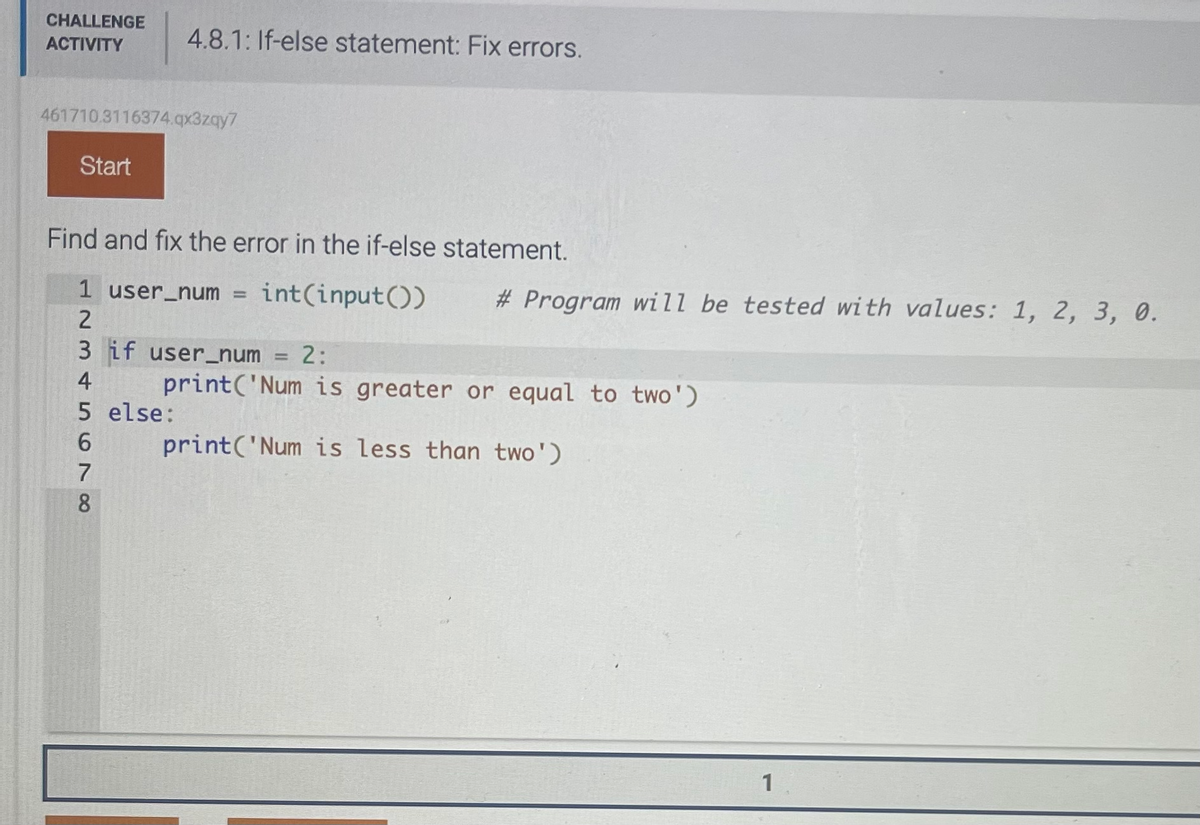
CHALLENGE ACTIVITY 461710.3116374.qx3zqy7 Start 4.8.1: If-else statement: Fix errors. Find and fix the error in the if-else statement. 1 user_num = int(input()) # Program will be tested with values: 1, 2, 3, 0. 2 3 if user_num 2: 45678 print('Num is greater or equal to two') print('Num is less than two') 5 else:
Q: 1. Create an array named arr1 with 20 random numbers between 1 and 10(inclusively). Then produce a…
A: The answer is (the output differ because we use random number)
Q: In terms of efficiency, user-created functionalities much surpass those of the system.
A: User-defined capabilities A function is an encapsulated set of instructions for doing a certain job.…
Q: Evaluate and assist company decision makers in understanding the importance of database…
A: Data definition language (DDL): Data Definition Language (DDL) is a type of language used to define…
Q: What takes happen if a stack resource generation fails?
A: In this question we have to understand what takes happen if a stack resource generation fails? Let's…
Q: Could you kindly go through the fundamentals of how a cache hierarchy is set up and how it works?
A: How would you characterize the hierarchy of a legitimate cache? The cache hierarchy is as follows:…
Q: A challenge-and-response authentication system is described (CRAS). Can you explain why this…
A: Introduction: In today's digital world, authentication systems play a crucial role in ensuring the…
Q: Define a file manager. Define the Windows Explorer program. Include areas for storing items and…
A: A file manager is a software program that helps a user manage files and folders on their computer.…
Q: How can I avoid being a phishing victim?
A: Phishing is a popular cyberattack : They victimize many people each year, profiting cybercriminals.…
Q: What is the definition of a system model? What should be taken into account while developing the…
A: The word "system model" is used in many contexts, areas of application, and circumstances, each with…
Q: ect the Big-O perfor
A: Introduction: The value of huge O is used to figure out how complicated the space-time equations are…
Q: What is meant by the term "literature research" and how does it fit into the process of designing an…
A: Definition: Software development models relate to the many procedures or techniques that are…
Q: Please elaborate on the function of design patterns in the larger field of software engineering. In…
A: 1. Programming is the process of creating a set of instructions that tells a computer how to perform…
Q: Rule-based, model-based, and case-based reasoning models may be separated from one another. Give an…
A: Rule-based reasoning, model-based reasoning, and case-based reasoning are three different approaches…
Q: What kind of activity must an attacker exhibit for a sniffer attack to be deemed successful? How…
A: INTRODUCTION: Sniffing or snooping refers to intercepting or collecting data while it is being sent…
Q: To what end does a firewall serve the greatest purpose? I was wondering if someone could give me…
A: Specify the objective of the firewall system. NOTE: Because you have posed many inquiries, we will…
Q: To what end does authentication serve? Assess the pros and cons of various verification strategies.
A: Security:- Computer security is the protection of computer systems and networks from unauthorized…
Q: Recent advancements in technology have allowed almost all modern home appliances to wirelessly…
A: Introduction Increased advancements in communication and information technology have increased the…
Q: Checkpoint A For Checkpoint A, you will need to demonstrate a program that does the following: 1.…
A: Note :- You have not mention the language of the program so I'm answering your question in C++. Your…
Q: The processes of building and assessing information systems are independent but connected tasks that…
A: process of building and assessing information are independent but the interlinked tasks that must be…
Q: Why is the World Wide Web regarded distinct from the rest of the Internet?
A: Given: The World Wide Web, abbreviated as "WWW," is a network of websites that may be navigated to…
Q: hich two kinds of technologies are virtually always present in wireless networks today?
A: Wi-Fi and Bluetooth are the two technologies that are virtually always present in wireless networks…
Q: *o=3, yo points BG R(x () [0 2
A: DDA Algorithm: DDA (Digital Differential Analyzer) algorithm is a simple incremental method to…
Q: To what end does a firewall serve the greatest purpose? I was wondering if someone could give me…
A: A firewall serves the greatest purpose to secure a network from external threats by controlling…
Q: Testing at the unit level, testing at the integration level, and testing at the system level are…
A: In this question we have to understand and discuss what distinguishing characteristics distinguish…
Q: Why is there a limit on the number of iterations that may be done while implementing the waterfall…
A: The answer for the above question is given in the following step for your reference
Q: Explain why you choose to utilize user-friendly wording. What precisely do people mean when they…
A: Software life cycle models provide graphical representations of the software life cycle (sometimes…
Q: The Internet's transport layer ensures that data may be sent from one network to another. This layer…
A: Introduction: The fourth layer of the OSI model of network connections is the transport layer. As…
Q: When creating an information security strategy for a medium-sized company, at least three other…
A: An information security strategy for a medium-sized company should involve multiple departments to…
Q: How can we guarantee that our anonymity when using the Internet is protected?
A: Anonymity refers to the state of being unknown or unacknowledged, especially in the context of…
Q: Write an if-else statement for the following: If num_difference is not equal to -15, execute…
A: Algorithm Steps to solve the given Problem: Start Take input from the user and store it in a…
Q: Inquire about and compare the significance of cloud computing to mobile devices. Cloud computing…
A: The relevance of computing to mobile devices is as follows: mobile computing enables us to access…
Q: Give an example of a hypothetical login management scenario. Write down as many unique…
A: Login management is process of verifying an identity of a user, who attempts to access a system or…
Q: What are some of the applications that are used almost often for host software firewalls, and what…
A: A host-based firewall is a software firewall that is installed on an individual device or computer,…
Q: Differentiate between caches that are totally associative and those that are directly mapped.
A: In this question we need to explain the differences between totally associative caches and directly…
Q: Examine the systems' benefits and drawbacks in relation to the organization's use of information and…
A: Information and Communication Technology (ICT) It describes how information is accessed, processed,…
Q: Describe the problems that may arise in a wireless network if only one of the stations is visible…
A: The term "wireless networking" refers to a kind of network in which the transfer of data from one…
Q: Explain the significance of each of the three reasons why the spiral model is superior than the…
A:
Q: How do the characteristics of a computer's central processing units exhibit themselves, and how may…
A: Introduction: The central processing unit, sometimes known as the CPU, may be found in every kind of…
Q: How does the idea of "acceptable" apply to coding?
A: The Coding which refers to the one it creates a set of instructions for computers to follow. These…
Q: Describe the complications in wireless networking that exist when one station is invisible and…
A: The term "wireless networking" refers to a kind of network in which the transfer of data from one…
Q: Explain how cloud computing is being used and how it has contributed to the global advancement of…
A: Cloud computing is the delivery of computing services—including servers, storage, databases,…
Q: Why is it better to hash a password when it must be stored in a file rather than encrypt it? What is…
A: Introduction: It is more secure since hashed passwords are compared with y, and if y = h(x), the…
Q: own words the economic advantages that patent rights may offer to individuals or groups, as well as…
A: According to this question, we need to discuss the economic benefits of patent rights for…
Q: What are some best practices for firewall configuration, and why are they essential?
A: When operating a firewall, it is advised that you follow the practises outlined in the following…
Q: Inquire about and compare the significance of cloud computing to mobile devices. Cloud computing…
A: Mobile computing allows us to access data and information through a mobile device; cloud computing…
Q: 1. Name the stages of the software development lifecycle (SDLC) - Give a short description for each…
A: Introduction:- SDLC(System development life cycle) is a systematic and user friendly technique or…
Q: What factors must be considered before to deciding on a plan for protecting a physical network?…
A: Introduction : A physical network is a type of computer network that has physical connections…
Q: Examine this list of concerns about data backup and recovery: what are the most important factors?
A: Data backup includes the following steps: In the event that we lose all of our original data, we…
Q: how implementing network and IT risk rules may be crucial in keeping staff members from disregarding…
A: Introduction: Implementing network and IT risk rules is an important aspect of ensuring that staff…
Q: In accordance with whatever provisions of the law may a picture, diagram, chart, or the whole of a…
A: In accordance with whatever provisions of the law may a picture, diagram, chart, or the whole of a…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 4 images

- 2.1.3: Basic if-else. Jump to level 1 Write an if-else statement for the following: If userTickets is less than 8, execute awardPoints = 1. Else, execute awardPoints = userTickets. Ex: If userTickets is 3, then awardPoints = 1. import java.util.Scanner; public class TicketCounter { public static void main (String [] args) { int awardPoints; int userTickets; Scanner scnr = new Scanner(System.in); userTickets = scnr.nextInt(); // Program will be tested with values: 5, 6, 7, 8. if (userTickets < 8) { awardPoints = 1; System.out.println(awardPoints); } else { System.out.println(awardPoints); }}Java Program ASAP ************This program must work in hypergrade and pass all the test cases.********** This program down below does not pass the test cases in Hypergrade as shown in the scheenshot. Please modify it. Also I have provided the code instructions. Thank you import java.io.BufferedReader;import java.io.FileReader;import java.io.IOException;import java.io.InputStreamReader;import java.util.regex.Pattern;import java.util.regex.Matcher;public class WordSeparator { public static void main(String[] args) { try (BufferedReader reader = new BufferedReader(new InputStreamReader(System.in))) { String inputFileName; boolean fileNotFound; System.out.print("Please enter the file name or type QUIT to exit:\n"); do { fileNotFound = false; // Reset fileNotFound flag for each iteration inputFileName = reader.readLine(); if (inputFileName.equalsIgnoreCase("QUIT")) {…Java - Help Please How do I output this statement as a horizontal statement with a newline? Everytime I use System.out.println, it makes the entire output vertical instead of horizontal. Program below. import java.util.Scanner; public class LabProgram { public static void main(String[] args) { int x; int y; Scanner scan = new Scanner(System.in); x = scan.nextInt(); y = scan.nextInt(); if(y >= x){ for(int i=x; i<=y; i = i + 5) { System.out.print(i+ " "); (The problem line) } } else{ System.out.print("Second integer can't be less than the first."); } }}
- Define regex. Write java program to demonstrate the use of regex by validating email address. Email should be having following pattern a. Alphanumeric characters b. @ c. Characters d. ‘.’ e. Characters Example of correct emails: asad12@yahoo.com, asad@live.com, ameen@gmail.com Example of incorrect emails: asad@yahoo1.com, numn@live.com1, waleedgmail.comDevelop a Java application to have the user input a positive four-digit integer at the keyboard. The program will then display each digit of number, one per line. No exception handling (error handing, that is). So, assume that the program receives and processes positive four-digit integers only. Input example: Enter a positive 4-digit number: 4876 Sample Output: The number you entered was 4876. It's digits are: 4 8 7 6\I have this code: import java.util.Scanner; public class CalcTax { public static void main(String[] args) { Scanner sc = new Scanner(System.in); // Welcome message System.out.println("Welcome to my tax calculation program."); // Declare the variables int i, pinCode, maxRetries = 3; String choice; // Get the PIN code for (i = 0; i < maxRetries; i++) { System.out.print("Please enter the PIN code: "); pinCode = sc.nextInt(); if (pinCode == 5678) { break; } System.out.println("Invalid pin code. Please try again."); } if (i == maxRetries) { System.out.println("Invalid pin code. You have reached the maximum number of retries."); System.exit(0); } // Get the income, interest, deduction, and paid tax amount double income, interest, deduction, paidTax; do { System.out.print("Please…
- Program10.java Write a Java program that prompts the user to enter a security code that matches a specific pattern. Your program must approve the user's entry. The pattern consists of these characters in this sequence: A lower case character, two upper case characters, two or three digits, two lower case characters, an upper case character, 2 or 3 lower case characters, 2 digits.Refer to Appendix H beginning on pages 1176.Example Run Enter the code patternbHT482haQmo82Yes, bHT482haQmo82 matches the pattern Recheck the requirements before you submit!Program10.java 1. Write a Java program that prompts the user to enter a security code that matches a specific pattern. Your program must approve the user's entry. The pattern consists of these characters in this sequence: A lower case character, two upper case characters, two or three digits, two lower case characters, an upper case character, 2 or 3 lower case characters, 2 digits.Refer to Appendix H beginning on pages 1176. Example Run Enter the code patternbHT482haQmo82Yes, bHT482haQmo82 matches the pattern Recheck the requirements before you submit!Java - How do I output this statement as a horizontal statement with a newline? Everytime I use System.out.println, it makes the entire output vertical instead of horizontal. Program below. import java.util.Scanner; public class LabProgram { public static void main(String[] args) { int x; int y; Scanner scan = new Scanner(System.in); x = scan.nextInt(); y = scan.nextInt(); if(y >= x){ for(int i=x; i<=y; i = i + 5) { System.out.print(i+ " "); (The problem line) } } else{ System.out.print("Second integer can't be less than the first."); } }}
- (Python) Please write a program that creates steps. You are expected to take in a single positive integer which will be used as the number of steps in your staircase. The program only accepts integers greater than 0 and less than 500. If 0 is entered a message stating "Your staircase has no steps." and if the user enters a value greater than or equal to 500, a message stating "I can't build a staircase that tall." For all other values not within the valid range or not integers an "Invalid staircase size provided." will be displayed to the user. The program will always run only once for each user input. One thing to note, the messages should be the return string from your createSteps() function and printed from the calling function. Additional Requirements: 1. The very first step in the stair case will be left aligned and for each subsequent level the step will move above and to the right of the prior step. 2. There are no spaces after the right of any of the steps. 3. The bottom most…(Python) Please write a program that creates steps. You are expected to take in a single positive integer which will be used as the number of steps in your staircase. The program only accepts integers greater than 0 and less than 500. If 0 is entered a message stating "Your staircase has no steps." and if the user enters a value greater than or equal to 500, a message stating "I can't build a staircase that tall." For all other values not within the valid range or not integers an "Invalid staircase size provided." will be displayed to the user. The program will always run only once for each user input. One thing to note, the messages should be the return string from your printSteps() function and printed from the calling function. Additional Requirements: The very first step in the staircase will be left-aligned and for each subsequent level, the step will move above and to the right of the prior step. There are no spaces after the right of any of the steps. The bottom-most row ends…PROBLEM: I need to make an ATM program that allows the user to check his or her balance after entering his or her correct PIN and the maintaining balance is Php 8000. A message is shown when the balance is below PHP 8,000 for withdrawal and its remaining balance. Another message is shown when the balance is PHP 8,000 and above for deposit and its updated balance. The code: import random import sys class ATM(): def __init__(self, name, account_number, balance = 0): self.name = name self.account_number = account_number self.balance = balance def account_detail(self): print("\n----------ACCOUNT DETAIL----------") print(f"Account Holder: {self.name.upper()}") print(f"Account Number: {self.account_number}") print(f"Available balance: Nu.{self.balance}\n") def deposit(self, amount): self.amount = amount self.balance = self.balance + self.amount print("Current account…











