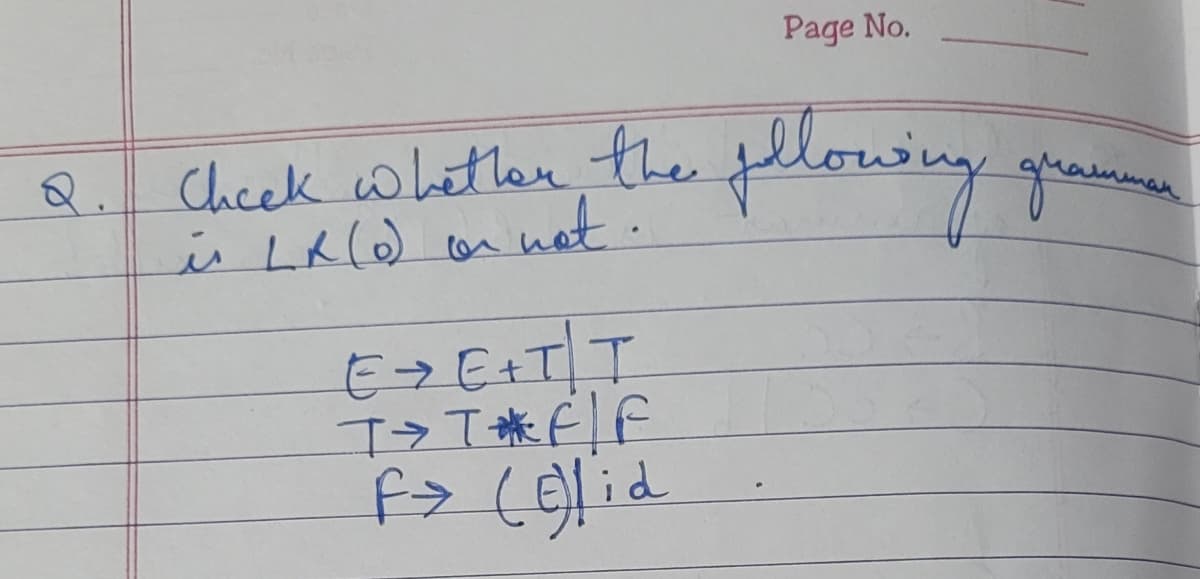
Check whether the following gramm is LX (0) or not. E>E+T\T\ T>TF/F F> (E)lid
Q: I need ideas for a Python programming project that includes the handling of an input file (data or…
A: Python programming for handling input file
Q: Describe how web caching will reduce the time it takes to get a request. Will web caching reduce the…
A: -Web caching is defined as the temporary storage of documents such as images, video files, and HTML…
Q: sorry can you solve this in c++
A: - We have to code for the coin change here. - We have to use c++.
Q: Write a program computing terms of the sequence given by the condition: x_0=1, x_1=1/3,…
A: ----------------------Matlab Code------------------------clc; clear; close all;format shortx(1) =…
Q: Compute data sent for a bit stream of 101011 with CRC using a generator 1010…
A: Answer : 2) Data sent 101011110
Q: Give an example of a drawback of utilizing Flash on a website.
A: Introduction: Flash is a multimedia platform used to add animation, video, and interactivity. Flash…
Q: Determine the time complexity function of the program snippet below, int f1(int n) { if (n <= 1)…
A: These re recursive functions and we have to find their time complexity by recurrence relation. We…
Q: Using a random number generator, create a list of 500 integers in Python. Perform a benchmark…
A: According to the information given:- We have to follow the instruction to generate 500 integers in…
Q: Router R6 is running OSPF. On R6, I set LoopbackO interface IP address to 6.6.6.6/32 and in R6 OSPF…
A:
Q: What are the roles of the approval committee during the different SDLC phases ?
A: answer starts from step 2
Q: Why do you think that the method area of a JVM is shared by all threads running in the virtual…
A: Java Virtual Machine(JVM) => JVM drives the Java Code. => It converts Java bytecode into…
Q: Explain what is meant by the zone routing protocol for advanced routing ?
A: To be determined- explain what is meant by the zone routing protocol for advanced routing.
Q: (1) Prompt the user to enter two words and a number, storing each into separate variables. Then,…
A: #1 favorite_color = input("Enter favorite color : ") pet = input("Enter pet's name : ") number =…
Q: This program will ask the user to input a number (suppose num). And that outputs the first num'th…
A: As no programming language is mentioned, it is solved using basic C++
Q: If p = false, q = true and = true and r = true, the truth value of p V (q + r) = true r =
A: Given :- In the above question, a proposition logic expression is mention in the above given…
Q: I need help in this C Program question. Ten young men agreed to purchase a gift worth Php10,000 for…
A: - We need to code for the contribution program in C languaue.
Q: Explain why an acquisition hash would be the same and why they would be different in EnCase.
A: According to the information given:- We have to define why an acquisition hash would be the same and…
Q: Describe how a decompiler translates machine code into a form that is close to the original source…
A: We must emphasize how a decompile converts machine code into something that can be used to…
Q: can you please include in the code something that outputs the row echelon form and the reduced row…
A: According to the information given:- We have to find out the output value of row echelon form and…
Q: Creating a virtual machine (VM) reduces ultimately to copying a file, therefore the explosion of the…
A: Cloud services are the services refers to the range of the services which are larger that are…
Q: What are the repercussions if the operating system does not appropriately distribute available main…
A: Introduction: Dangling shots and early free throws When many apps relinquish memory, they crash or…
Q: package assignment; public class A4PassFailDriver ( public static void main(String[] args) { //NOTE:…
A: Please do like it will encourage me a lot,
Q: (c) Figure 4 shows the design of SMART aquaculture system comprises of 4 End-Node Unit (ENU), 1…
A: Distance between server and gateway is 3M and distance between gateway tank1 is 11KM and Gateway to…
Q: Write a C++ program using operator overloadin
A: //C++ Program #include<iostream.h>#include<conio.h> class Time{ public:…
Q: In EnCase 7.0, I am attempting to dechiper what hash is used in a Floppy disk file. How do I do…
A: Here is the solution:
Q: DQ1: You want to use Google dorks to footprint the site but only want results that show file…
A: filetype Description: File type . You can use the filetype: operator in Google Search to limit…
Q: process Allocation max ABC ABC 141 562 PO P1 P2 P3 P4 PO PL P2 01 0 111 323 211 P3 P4 210 561 ABC…
A: ANSWER STARTS FROM STEP 2
Q: 1. When dose buffer overflows occur Buffer overflows occurs when we do not properly account for the…
A: Buffer overflows occurs when we do not properly account for the size of the data input into an…
Q: What are the core principles of a wireless network?
A: The correct answer of the question is given below
Q: Computer science: What actions take workers in an organization to maintain the confidentiality of…
A: The provided case study outlines the organization's internal information assets as well as the…
Q: Write down the values of Carry, Overflow, Zero, Sign, Auxiliary Carry, Parity flag after each…
A: According to the information given:- We have to follow the instruction and find out the values of…
Q: 5. What is the purpose of this piece of code? form method="POST" action="/topic4/htmlExpress/update"…
A: Below I have provided the correct option for the given query.
Q: Computer science: Talk about the three methods used to enhance quality assurance.
A: Three techniques that help in the improvement of the QA are as follows:
Q: Explain entity-relationship (ER) diagrams.
A: Please find the detailed answer in the following steps.
Q: The design of the cybercafe (star topology network)
A: Cyber cafe: It is a type of business. It allows computers to provide internet access, play games,…
Q: this is not in visual studio
A: Have this code in the visual studio below is the program and output in visual studio
Q: Describe balanced DFD.
A: Balanced DFD: DFD (Data Flow Diagram) is said to be balanced DFD if the lower-level diagram has the…
Q: I need ideas for a Python programming project that includes the handling of an input file (data or…
A: Python programming for handling input file
Q: Write a command to change the permissions of a file named file.txt: give read permission to group,…
A: Question-2 r stands for read w stands for write x stands for execute 7 is for read,write,execute 1…
Q: It is required to develop an application in Java to perform some operations to store information…
A: Please check the step 2 for solution
Q: stack a Q. programe to illustrates why is is useful data sturucture for many Computational problems,…
A: The program is written in C Language. Check the program screenshot for the correct indentation.…
Q: 1. In the game of Monopoly, a pair of dice are rolled to move a player's piece around the board. If…
A: Matlab code: %fifty times rollingplayer1_total_double = 0;player2_total_double =…
Q: So long as two people can communicate in a way that no-one else can understand the messages they are…
A: I agreed the above statement and I'm telling my opinion in step 2 with through the some steps
Q: Following is a problem statement. Which of the below provides is the correct variables used for the…
A: As per the given data we need to read name and id.
Q: 2. Which command is used to list the attributes of a file? a) cp D) list c) Is
A: It is defined as an instruction to the computer, which it interprets to perform a specific task.…
Q: Prompt For this project, you will be developing a PY file that contains your code in PyCharm and…
A: ANSWER:-
Q: What is the purpose of the SNMP trap message?
A: Introduction: It is an application layer protocol that uses a request-response model.
Q: Write down the values of Carry, Overflow, Zero, Sign, Auxiliary Carry, Parity flag after each…
A: answer starts from step 2
Q: What are the potential risks and consequences of a data breach to a company's cyber security
A: Introduction: A data breach occurs when unauthorized parties get access to sensitive information…
Q: e a language consisting ssion like X" represents of the eight legal octal digits with the following…
A: Introduction: Below describe a language consisting of the eight legal octal digits with the…
Step by step
Solved in 2 steps with 2 images

- Select the function that is ?theta(nlogn) .a. 5n + 17lognb. 6nlogn + n^1.1 + 2c. 23nloglogn + 3nlognDraw the following function: Y=A cosB + C Where: A= 1 , -1 , 3 , -3 (four values) B= 0° : 360° (as smooth as possible) C= 0 , 0.3 , 0.6 (three values)Specify the appropriate primitive numeric data type to use for each of the followingvalues: 2 concert tickets
- Code the following.3. Evaluate the following expressions:a. abs(5); _______________________________88b. floor(5.5); _______________________________c. ceil(5); _______________________________d. fmod(pow(7,2)); _______________________________e. sqrt(floor(25.12)); _______________________________f. fabs(pow(9,2)); _______________________________g. atoi(“451”); _______________________________h. ceil(pow(5,3)); _______________________________i. fabs(-44.98); _______________________________j. ceil(fmod(5,1,5)); _______________________________Create a flow chart of a reverse of a number.
- i need complete code c++1. Write a C/C++ program that creates a table consisting of 500 randomly generated 3- tuple entries where each entry consists of processID, arrivalTime, and burstTime. The processID should be a “unique” 3-digit positive integer (e.g., 382, 881, 923, …). The arrivalTime should be an integer randomly picked from a range of values between 1 and 1,000. Note that the arrival times of two processes can be the same. The burstTime is an integer randomly picked from a range of values between 1 and 500. Your program should print out the table. An example output of your program would look something like this: processID arrivalTime burstTime 839 1 83 228 4 20 102 3 30 … 2. Using the code for Problem 1, write a C/C++ program that simulates execution of the Round Robin (RR) Algorithm with Time Quantum of 10 and calculates the average waiting time. Your program should run the RR algorithm 500 times. Note that each time you run the algorithm, a new table should be generated, and thus, the average…Mississippi.cpp) Print the word "Mississippi" in blockletters (e.g., drawn entirely with asterisks). Each lettershould be printed by its own function please write this code in c++



