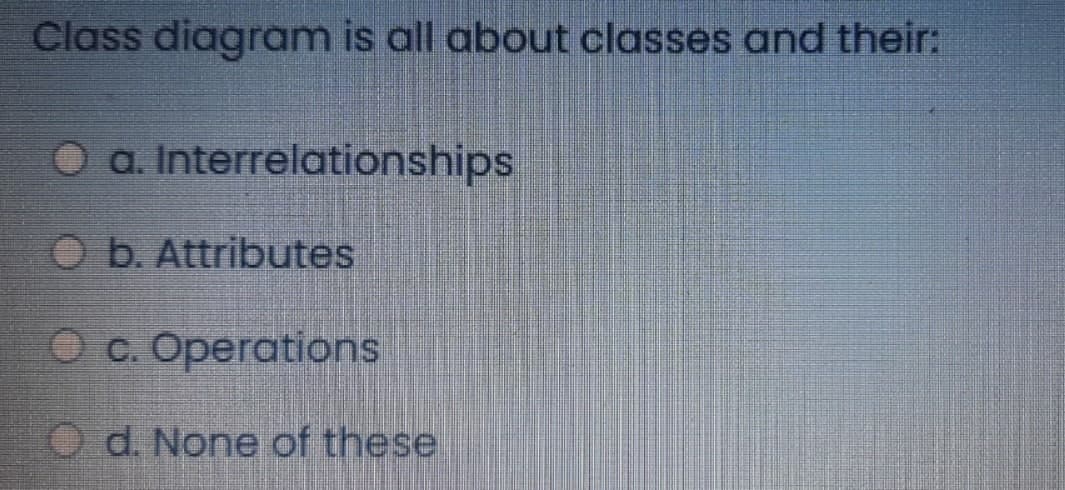
Class diagram is all about classes and their: O a. Interrelationships Ob. Attributes O c. Operations Od. None of these
Q: Which of the following keywords mark the beginning of the class definition? Group of answer choices…
A: Question 1C: classdef, return, and class are all keywords, but class is the only keyword that marks…
Q: Consider a paged virtual memory system with 32-bit virtual addresses and 1K-byte pages. Each page…
A: In the operating systems, the memory paging which refers to the memory management scheme by which…
Q: Write a function that diagonally orders numbers in a n x n matrix, depending on which of the four…
A: Function plan: Create an array, temp of size size. Insert another array of size size for each index…
Q: In CRC, show the relationship between the following entities (size means the number of bits): a. The…
A: The Cyclic Redundancy Checks (CRC) method of error-detection and correction is the most effective.…
Q: It is often argued that weak consistency models impose an extra burden for programmers. To what…
A: Introduction: A consistency model is a contract between a distributed data store and processes in…
Q: hy do we need POP3 or IMAP4 for electronic mo
A: Introduction: POP3 is an abbreviation for Post Office Protocol version 3, which allows access to an…
Q: What is the difference between a port address, a logical address, and a physical address?
A: Definition: The physical address is a location in the memory unit, but the logical address is…
Q: 1. Let's suppose there is an organization with two departments with each department requiring 120…
A: To make routing decisions, a router exchanges information with other routers. Alternatively, the…
Q: There are exactly N people living in a certain parallel universe. The Ith of these NN people claim…
A: Input-Output Format: The first line of input will contain a single integer T, denoting the number…
Q: Write an insert module for a Binary Tree data structure. The module will take two parameters: a…
A: class Node: def __init__(self,key): self.left = None self.right = None self.value = key # A…
Q: Follow-up -Recommend additional security measures without adding additional equipment (the switch…
A: The answer is written in step 2
Q: Performance is inversely related to delay. When you use the Internet, which of the following…
A: Performance of a task, service or application inversely depends upon the delay. Longer delay in any…
Q: 15 Write a C++ program that displays the results of the expressions 3.0*5.0.7.1*8.3- *.2.2, and…
A: #include <iostream> using namespace std; int main(){ float expr1,expr2,expr3; expr1…
Q: Senario Programming Competition System – Schools and Universities always want to participate in a…
A: User requirements for the automated contest system include registration process, online entry…
Q: Big data analytics is used by most corporations today. True false
A: The main reasons that todays corporations use big data analytics is: With the helps of analytics…
Q: In Sammon mapping, if the mapping is linear, namely, g(x|W) = WTx, how can W that minimizes the…
A: Answer is in next step.
Q: 3.Write 4 examples for Web applications.
A: ANSWER:
Q: What is the difference between voting and stacking using a linear per ceptron as the combiner…
A: INTRODUCTION: Stacking It is possible to define it so that the generalization of various…
Q: What is printed by the function foo5()? class Point: def __init__(self, x, y): self.x = x self.y = y…
A: In this problem we need to show the what will be the output of the above code. Need to call the…
Q: count=readFile(); CODEChecker (0,count); } else { printf("\nVaccine Name: "); fflush(stdin); gets…
A: Note: The definition of count and vacc is not given so count is considered as a variable, and vacc…
Q: What kind of arithmetic is used to add data items in checksum calculation?
A: Introduction: IT experts employ checksums, values representing the number of bits in a transmission…
Q: The formula that will add the value of cell D4 to the value of C2 and then multiply by the value in…
A: Option A is incorrect since there is a syntax error. This is because it is missing a closing…
Q: Performance is inversely related to delay. When you use the Internet, which of the following…
A:
Q: As per our discussion in class in the past few days, students are expected to write a PHP c that…
A: Please find the answer below :
Q: Problem 1. Assume we have an array A = {a1,...,an) of n elements, where it is guaranteed a majority…
A: The answer is given in the below step
Q: Problem 1. Assume we have an array A = {a₁,...,an) of n elements, where it is guaranteed a majority…
A: Answer is
Q: 58. define a multivariate bernoulli mixture where inputs are binary and derive the em equations.
A: The solution for the above-given question is given below:
Q: After the SHR instruction is executed in the code sequence below, what is the final value for AL?…
A: Correct Option is B⇒ 0010_1011
Q: 1a.Suppose P is a false statement. Is it ever possible for P ⇒ Q to be false? Explain your answer.…
A: According to the question, we have to answer and explain three subparts. 1a.Suppose P is a false…
Q: Q2/Write c# program To print a prime numbers using random numbers, for outer loop use (for) and for…
A: Algorithm/Program Plan: Create a public class named newClas Create a main method Declare a bool…
Q: Consider a paged virtual memory system with 32-bit virtual addresses and 1K-byte pages. Each page…
A: Virtual memory Virtual memory is a memory-the-board strategy where optional memory can be utilized…
Q: What happens if an attacker attempts to alter the Tag (the MAC) and the ciphertext in transit while…
A: Tag is another name for MAC. Both the sender and the recipient use it as information to ensure the…
Q: 2. Write a program that generates a two-column table showing Fahrenheit temperatures from -40F to…
A: The given program is in java.
Q: BCD Find (49.3)10 - (00110110.0010), = (?)вср, with BCD weight (8421) ВСD
A: Hello student I will write this solution as per my best of knowledge.
Q: Create a function using currying that will add a car maker name as a property to the carLot object…
A: In this problem, we need to design the code in the java Script programming language. Input -…
Q: In symmetric-key cryptography, if every person in a group of 10 people needs to communicate with…
A:
Q: Create a function that returns an Earned Run Average (ERA). An ERA is calculated by multiplying 9 by…
A: /*Step-1: StartStep-2: function era(er, ip) Step-2.1:Declare variable ERA and initialize with (er…
Q: What happens if an attacker attempts to alter the Tag (the MAC) and the ciphertext in transit while…
A: The answer is
Q: . Do port addresses need to be unique? Why or why not? Why are port addresses shorter than IP…
A: IP address An IP address is a progression of numbers that recognizes any gadget on a network. PCs…
Q: Create a function that takes a string and replaces every nth instance of oldChar with newchar. Your…
A: Step-1: Start Step-2: function replaceNth(str, n, oldChar, newChar) Step-2.1: if n is less than…
Q: What are headers and trailers, and how do they get added and removed?
A:
Q: Discuss the three types of mobility in a wireless LAN.
A: "The capacity for movement or the ease with which one can relocate from one location to another are…
Q: Note: Find the minimum number of operations required by Rajesh to accomplish his task using Java…
A: Algorithm: The first line of input will contain a single integer T, denoting the number of test…
Q: What does the term “boundary testing” mean? If your program was doing calculations and took in…
A: What is Boundary Testing? Boundary testing also known as boundary value analysis. In boundary value…
Q: 7. Q: Assume a client calls an asynchronous RPC to a server, and subsequent waits until the server…
A:
Q: you run the netstat command on a Windows machine, you may get results like the ones shown below. TCP…
A: netstat command displays the active TCP connections, ports on our computer is working, Ethernet…
Q: Create a function that outputs the result of a math expression in words. Examples wordedMath("One…
A: const calc = { zero: 0, one: 1, two: 2, 0: 'Zero', 1: 'One', 2: 'Two', plus(n1, n2) { return…
Q: If your cell shows 100, then the formula bar could show A: Nothing B: =50*2 C: 50x2 D: one hundred
A: Option A is incorrect since the Formula Bar contains either a value or an expression if a cell shows…
Q: What is the difference between voting and stacking using a linear per ceptron as the combiner…
A: The difference between voting and stacking using a linear per ceptron as the combiner function are:-…
Q: Discuss the three types of mobility in a wireless LAN.
A: The question has been answered in step2
Step by step
Solved in 2 steps

- Describe the main steps performed in a class-based paradigm to identify classes. The response is accurate. just using bullets Don't skip any steps.Define / describe class, attributes and methods and how they work with eachother. What is the relationship between them all?Complete the following • Joseph is a doctor. • He works at the Chris Hani Baragwanath Academic Hospital in Soweto. • He is responsible for the “Voice of Cancer Anti-Stigma Project”. Create a class diagram that will accurately depict the class described in the scenario above. Your diagram should demonstrate the following:• At least three attributes;• A getter and setter method for each attribute;• Access specifiers.
- At what time(s) can a class diagram change? How is it changed?Create your own UML diagram — similar to the above UML diagram — for a Pet class that meets thespecification below.1. Create the fields indicated below. Use these names exactly as given for your fields. Define them inexactly this order.• name — The name of the pet, e.g., “Rufus”, “Mittens”, “Smelly”, etc.• animal — The type of pet, e.g., “dog”, “cat”, “asparagus”, etc.• age — The (integer) number of years the pet has been alive, e.g., 1, 2, 3, etc.2. Create a mutator for each of the above in the order listed. Use the standard Java naming conventionfor mutators.3. Create an accessor for each of the above in the order listed. Use the standard Java naming conventionfor accessors.Example: Suppose you are taking the question for the example Car UML above instead of your Pet UML.Don’t enter any spaces at all.When the question asks: Enter line 1:You would enter: CarWhen the question asks: Enter line 2:You would enter: -make:StringWhen the question asks: Enter line 3:You would enter:…Create your own UML diagram — similar to the below UML diagram — for a Pet class that meets thespecification below.1. Create the fields indicated below. Use these names exactly as given for your fields. Define them inexactly this order.• name — The name of the pet, e.g., “Rufus”, “Mittens”, “Smelly”, etc.• animal — The type of pet, e.g., “dog”, “cat”, “asparagus”, etc.• age — The (integer) number of years the pet has been alive, e.g., 1, 2, 3, etc.2. Create a mutator for each of the above in the order listed. Use the standard Java naming conventionfor mutators.3. Create an accessor for each of the above in the order listed. Use the standard Java naming conventionfor accessors
- This graded activity has two parts.Part 1: Answer the Module Review Questions listed below. These questions were chosen to demonstrate your understanding and help you assess your progress.Contrast the items in the following sets of terms:Object; class; instance; entity relationship diagram (ERD) entityProperty; method; attributeState; behaviorSuperclass; subclassConcrete class; abstract classMethod; messageEncapsulation; inheritance; polymorphismStatic binding; dynamic bindingHow is the object approach different from the data and process approaches to systems development? And how can the object approach improve the systems development process?Describe the main building blocks for the sequence diagram and how they are represented on the model.Describe the steps used to create a sequence diagram.Part 2: Module Practice:Draw the associations that are described by the following business rules. Include the multiplicities for each relationship.A patient must be assigned to only one doctor…Answer the given question with a proper explanation and step-by-step solution. please help! using the class diagram (which is provided below) you need to provide a detailed design using pseudcode representation. thank youGive examples of the most important traits of classes and constructors to keep in mind.
- Using Visual Paradigm create a Design class Diagram of a Car Sharing IS When creating the diagram create classes such as Customer, Vehicle, Reservation, Billing, and Membership. Be sure to add method signatures and any controler classes required. The diagram should look similer to the image.Make an interaction diagram for the parking office class below. We have included the class code below. Use the class diagram to better understand all classes in our systemFor this project, you will implement an email client-server simulator using the object-oriented design diagramed below. The class diagram above shows class attributes (members) and methods (operations). Operations are denoted with a plus. The diamonds indicate an aggregation relationship between the connected classes. For example, a mailbox list can have one or many mailboxes. A Mailbox can have one or many messages. You will therefore need data structures container objects (lists) to contain these types of objects, as we have seen in previous exercises. All class attributes are private unless denoted otherwise and therefore must be accessed with constructors. getters, ord setters. Constructors are a preferred way to set class attributes. Constructors, setters, getters, and toString methods can be generated by IntelliJ. Check the IntelliJ documentation for how to use the Generate feature. Messages are simultaneously sent and received. Therefore, a Message is…

