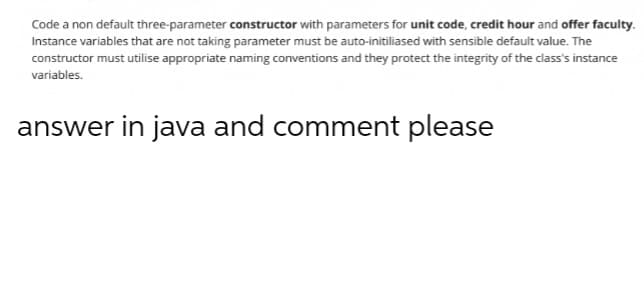
Code a non default three-parameter constructor with parameters for unit code, credit hour and offer faculty. Instance variables that are not taking parameter must be auto-initiliased with sensible default value. The constructor must utilise appropriate naming conventions and they protect the integrity of the class's instance variables. answer in java and comment please
Q: "web application
A: A Web application (Web app) is an application program that is stored on a remote server and…
Q: Design an usecase documentation for any 2 modules .For the same 2 modules prepare testcases for the…
A: User case diagram:
Q: Compare and contrast the Iterative Waterfall Model with its more traditional counterpart, the…
A: Answer: The advantages of the Iterative Waterfall Model over the Classical Waterfall Model. What is…
Q: What methods are used to perform routing in a wide area network?
A: Given: The Internet is a massive collection of systems, switches, and communication links (different…
Q: Why is a destructor function required in classes? Illustrate with the help of an example ?
A: Introduction In this question we will discuss why destructor function is required in classes.
Q: Ql: Write a computer program in F90 to generate a matrix A(n) which contains an integer numbers…
A: Find Your Code Below
Q: Pick a field in which an expert system may be of assistance in the role of assistant, offer at least…
A: Domains in which an expert system may assist: Medical diagnosis (the knowledge base would include…
Q: Is valgrind the same thing as a compiler?
A: Start: Valgrind acts as a CPU simulator, running your programmes (and the libraries it uses) on it.…
Q: What are some of the governance challenges that should be kept in mind throughout the transition…
A: Introduction Cloud technology is useful in this situation, and it is also a secure alternative for…
Q: Draw an FA accepting the language of all strings over {a,b} that start with 'a' AND end with 'b'
A: Given that, Finite automata accepts the language of all strings with 'a' and must ends with 'b'. set…
Q: What are the differences between real-time operating systems and non-real-time operating systems…
A: Introduction: The expression "real-time task" alludes to a task that is combined with a period…
Q: A large number of developers create web-based applications with the help of computer languages. Name…
A: Specify three programming languages in which internet-based applications are described: Multiple…
Q: Explain the process of producing software applications that run on the web in as few words as…
A: Given: the procedure for developing web-based softwarethe technique for programming web-based…
Q: How exactly can authentication assist us accomplish what we set out to do? In this part, we will…
A: Answer: Scalability is good for large setups with many members; you can quickly add more…
Q: Admission to a professional course is subject to the following conditions : (a) Marks in…
A: Checks if the value of left operand is greater than or equal to the value of right operand, if yes…
Q: Keepass is a tool that may be assigned to examine and monitor the goals of a system or a network.
A: Three goals of the KeePass (tool) are allocated to the analysis and monitoring of a system or…
Q: Which factors affected the decision to mandate an object-oriented methodology for the creation of…
A: Start: Give instances of why object-oriented system development was required. The object-oriented…
Q: The transition from servers located on-premise to those hosted in an IaaS architecture, how tough is…
A: IaaS Architecture: In the IaaS model, cloud providers host infrastructure such as servers, storage,…
Q: The "store-and-forward network" approach is no longer employed in general communications, and there…
A: Store-and-Forward Network: Store and forward is a telecommunications strategy in which data is…
Q: What are some of the governance problems that should be watched out for throughout the move from…
A: Start: The infrastructure of the charity's information is managed by the organization's management…
Q: Computer Science 2. Let M be the FA with state diagram b а, b 9o a) Construct the transition table…
A: Let's understand step by step : Answer (a) : Transition table : Transition table contains all…
Q: What exactly is meant by the term "autonomic computing," and how does it contribute to the efficient…
A: Answer:
Q: What components make up a web application?
A: Following are examples of cloud storage programs:
Q: What are the advantages and disadvantages of using a cloud storage application over a traditional…
A: answer is
Q: Represent
A: Problem: Melody is playing an RPG game with grid like world system. Currently, she has 2 goals…
Q: What governance problems should be considered while transitioning from servers located on-premises…
A: Infrastructure as a Service: The charity administration employs the infrastructure as a service…
Q: Does the operating environment come to mind as an example?
A: In pc package, AN operative surroundings or integrated applications surroundings is the surroundings…
Q: Write a program to generate the following pyramid
A: No programming language is specified so using c++. I have provided the code and output in step2.
Q: It was devised to deal with two major concerns, one being the distribution of the keys. Give an…
A: Cryptography: The development of public-key cryptography was motivated by a need to overcome two…
Q: Ql: Write a computer program in F90 to generate a matrix A(n) which contains an integer numbers…
A: First, we will create the 1d array. Now we will fill all the array elements after entering the size…
Q: Give an example of a cloud storage application and describe the advantages and disadvantages that it…
A: Introduction: I am a proponent of the ease and value that cloud technology provides, since I…
Q: Provide and explain the pros and downsides of magnetic secondary storage systems against solid-state…
A: ANSWER:-
Q: What are the main differences between physical location exchanges and computer/telephone networks?
A: Intro The following are the distinctions between physical location exchanges and computer/telephone…
Q: Based on the output attached, write a program that prints out “C S !” in large block letters inside…
A: C++ Program: #include <iostream> using namespace std; int main(){ //border of * followed by…
Q: Write a java program for the following pattern [code & output screenshots are mandatory].
A: ALGORITHM:- 1. Set the number of rows to 5. 2. Pass it to the function. 3. Display the result using…
Q: and word size i: processor is 3:
A:
Q: Give some instances of internet entities that need to communicate securely.
A: Intro Please find the instances of internet entities that need to communicate securely with one…
Q: The "store-and-forward network" approach is no longer employed in general communications, and there…
A: Store And Forward: Store and forward is a telecommunications strategy in which data is transferred…
Q: Give some instances of internet entities that need to communicate securely.
A: Network Entity any Person that may be formed in which the Borrower holds a direct or indirect equity…
Q: What is the function of design patterns in software engineering? Is there a specific pattern you'd…
A: Software engineering is a systematic engineering approach to software development.
Q: if you have H as array shown below: 33 5 5 12 8 7 77 99 14 find the summation result of rows element…
A: This product takes 3 number qualities from the text box, adds them together and shows the outcome in…
Q: If you have an example of sensitive data that has to be secured in a short length of time, such as…
A: Sensitive data: The definition of sensitive data is any information that is secured against…
Q: What are the benefits of establishing information security using a methodology? What are some of the…
A: Introduction: When it comes to data security, refers to safeguarding information from illegal access…
Q: Write a programme to determine the sum of the following harmonic series for a given + 1/n teh value…
A: Introduction In this question we have to write a programme to determine the sum of the harmonic…
Q: Describe TWO (2) typical examples of problems solved by a systems analyst and the steps that he/she…
A: The answer is given in the below step
Q: What exactly does it imply when people talk about "virtualization"?
A: Virtualization: Virtualization is the architecture of anything, such as an operating system (OS),…
Q: Science of computers When will the machine be able to process these transactions?
A: Introduction: A transaction's operations are the things it performs. For further processing, the…
Q: What kind of experience do you have dealing with computer networks? Explain the differences between…
A: All computer network connects in different form ,some geographically ,some within limited area and…
Q: Normally, how do an untrusted network, a firewall, and a trusted network relate to one another and…
A: In this context, the only restriction on data is imposed by firewalls through designated places…
Q: What are the advantages of having servers automatically supplied and configured rather than having…
A: Given: benefits of providing and configuring servers automaticallyTime is saved – Significant time…
Step by step
Solved in 2 steps with 1 images

- If class A is a subclass of class B, then A has access to all of B's instance variables, including private ones. True FalseGiven the following class, I need help writing a constructor that initializes all instance variables using appropriate parameters. I need to make sure it enforces the preconditions public class BrowserTab {private String title;private int id;/*** Creates a BrowserTab* @precondition title != null && id >= 0*/}(Java) Identify the true statements, select all that apply: -Setters and getters are not required for public instance variables -Every private instance variable in a class definition must have a mutator method -A getter method has the same return-type as the field it retriees and takes no paramaters -A setter method is a return-type void and takes a parameter of tehe same type as its field
- Hi can you assist me on the problem below for a class and a test class that conforms to the following specifications: 1. The name of the class is RightTriangle 2. The class has member variables base and height 3. The class has a constructor that initializes base and height 4. The class has accessors and mutators for base and height 5. The class has a toString method that produces String representation of a RightTriangle like the following example for a triangle with base 12 and height 10. Base : 12 Height 10 6. The class has a method called findArea to compute the area of the right triangle. Here is a suggested implementation. public double findArea() { return 0.5* this.base*this.height; } 7. The class using proper naming conventions Write a test class called RightTriangleTest that conforms to the following: 1. Create an object with base = 10 and height = 20, for example myTriangle. 2. To print the toString for myTriangle. 3. To print the area of myTriangle. System.out.println(“The…Write down code that can declare a class of an employee with the properties, name and salary, and the methods, getSalary and getName, that return the salary and name of the employee respectively. Function members should be declared as prototypes only andinclude a parameterised constructor prototype to initialise with the name and salary.Consider a class BankAccount that has • Two attributes i.e. accountID and balance and• A function named balanceInquiry() to get information about the current amount in the account Derive two classes from the BankAccount class i.e. CurrentAccount and the SavingsAccount. Both classes (CurrentAccount and SavingsAccount) inherit all attributes/behaviors from the BankAccount class. In addition, followings are required to be the part of both classes• Appropriate constructors to initialize data fields of base class• A function named amountWithdrawn(amount) to withdraw certain amount while taken into account the following conditionso While withdrawing from current account, the minimum balance should not decrease Rs. 5000o While withdrawing from savings account, the minimum balance should not decrease Rs. 10,000• amountDeposit(amount) to deposit amount in the accountIn the main() function, create instances of derived classes (i.e. CurrentAccount and SavingsAccount) and invoke their respective…
- All vehicles used for transportation in the U.S. must have identification, which varies according to the type of vehicle. For example, all automobiles have a unique Vehicle Identification Number (VIN) assigned by the manufacturer, plus a license plate number assigend by the state in which the auto is registerd. Modify the Auto class to include an instance variable for the license plate number. Implement the constructor so that an Auto can be constructed with a VIN and a license plate number. Override the getID() method to return the id of the auto as shown in this format: VIN=1234567890,plate=ABC123 (without any spaces). ** Represents an automobile.*/public class Auto // TODO: Inherit from Vehicle{ // TODO: Declare instance variables public Auto(String vin, String plate) { // TODO: Complete the constructor } // TODO: implement the getID() method for autos}Implement the following concepts by constructing suitable classes in Java -a. Constructorsb. Constructor Overloadingc. Function Overloadingd. Function Overridinge. InheritanceCreate a class Person - Field - Name, Birthdate, Contact no and Mail idMethods - Constructor, accept and displayClass Employee - Inherits the Person classFields : Emp ID, grade, basic salary, Gross Salary, HRA (House Rent Allowance), TA (TravelingAllowance), DA (Dearness Allowance)Given:Grade Basic TAA 8000 2000B 7000 1500C 6000 1000D 5000 500Calculate Gross Salary :Gross Salary = Basic + HRA (20% of Basic) + DA (50% Basic) + TAe.g if Basic = 8000TA = 2000HRA = 20% of 8000 = 1600DA = 50 % of 8000 = 4000Gross = 8000 + 2000 + 1600 + 4000 = 15600Optional : you can implement increment function in which you can change grade of an employee andrecalculate salary with new gradeQ# Which of the following might have only method signatures? Group of answer choices 1. An interface 2. An abstract class and a concrete class 3. An abstract class 4. An interface and an abstract class 5. None of these, they all require the implementation. 6. A concrete class
- What does the super keyword represents and where can it be used? Give an example of a superclass and subclass. Be sure to make all the instances variables of the super class private. Include at least one constructor in each class and ensure that the constructor of the subclass calls the constructor of the superclass. Also include a toString method in both classes that returns the values of the instance variables with appropriate labels. Ensure that the toString method of subclass calls the toString method of the superclass so that the string returned contains the values of all the inherited instance variables.Consider the following program which contains a class definition currently missing one line of code: class Pokemon: def __init__(self, pokemon_name): ██████ pikachu_name = 'Pikachu' pikachu = Pokemon(pikachu_name) print(pikachu.name) Suppose that we want the constructor of this class to initially set the value of the instance variable name based on its arguments. This implies that the expected output of the program is 'Pikachu'. What should the missing line of code be? a. name = pokemon_name b. name = pikachu_name c. pikachu.name = pikachu_name d. self.name = pokemon_name e. pikachu.name = pokemon_name f. self.name = pikachu_nameThis chapter uses the class rectangleType to illustrate how to overload the operators +, *, ==, !=, >>, and <<. In this exercise, first redefine the class rectangleType by declaring the instance variables as protected and then overload additional operators as defined in parts 1 to 3. Overload the pre- and post-increment and decrement operators to increment and decrement, respectively, the length and width of a rectangle by one unit. (Note that after decrementing the length and width, they must be positive.) Overload the binary operator – to subtract the dimensions of one rectangle from the corresponding dimensions of another rectangle. If the resulting dimensions are not positive, output an appropriate message and do not perform the operation. The operators == and != are overloaded by considering the lengths and widths of rectangles. Redefine the functions to overload the relational operator by considering the areas of rectangles as follows: Two rectangles are the…

