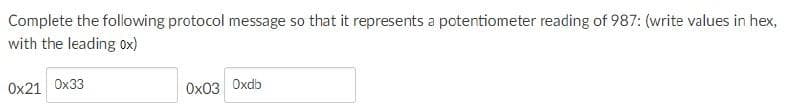
Complete the following protocol message so that it represents a potentiometer reading of 987: (write values in hex, with the leading 0x) Ox21 Ox33 Ox03 Oxdb
Q: For database experts, normalization is a critical topic. It is useful for creating, scenario verific...
A: Introduction Normalization is the process of organizing data in a database that includes creating t...
Q: C++ numbering systems. Covert from octal to decimal.
A: The octal number is expressed in the octal numeral system while the decimal number is in the decimal...
Q: Assume that you are working in a cloud consulting company and part of the team for generating a clou...
A: Cloud computing - Cloud computing technology enables the users access to software, storage, servers,...
Q: In Quick Sort Ascending Order Show the step by step process on how sorting was done such as first p...
A: As the language is not given, So I am solving this problem using C++ language. Implementation of Qui...
Q: Q-1. what is atput gf this logic gati? A F=?
A:
Q: ID: A Name: 3. Consider the following program code. i i +- SUM sum 0 REPEAT UNTIL i = 4 i 1 sum sum ...
A: The answer is
Q: What is the role of current technology in effective communication and how is it used?
A: Introduction Communication is the most important expect of human life. To generate, pass and organiz...
Q: Design a login page including HTML and CSS. Keep following requirements to be covered in your implem...
A: The answer is given below.
Q: In your essay, you should discuss at least two advantages and disadvantages of skipping the skip lis...
A: Introduction: The issue is that there are two distinct sorts of benefits and disadvantages essays, e...
Q: Explain are all types of modern CPU and explain the difference between them advantages and disadvant...
A: Introduction: A processor is the control and processing device that separates the main components ...
Q: One of the benefits of a Hadoop installation is the high level of compute redundancy. Why is this so...
A: Introduction Reason Computing redundancy allows for more tolerance to hardware failure and higher ...
Q: What is the purpose of the identifying value? What will happen if there is no identification number ...
A: Identification Value: It is the unique value given to every packet during transmission. During Tra...
Q: Create a state transition diagram that describes booking’s state in the above booking system, by pro...
A: State in a state transition diagram: Governmental diagrams show every one of the modes that an item ...
Q: Problem 4. For the RSA cryptosystem pick two prims p 29 and q 53 so N = pq = 1537. (1) Calculate o(N...
A: In RSA cryptosystem, given p=29 and q=53, we have Euler totient function φ(N) = (p-1)(q-1)=(29-1)(53...
Q: Essentially, computer viruses are malicious software programs that are difficult to detect and that ...
A: Introduction: When a computer virus is run, it replicates itself by altering other computer programs...
Q: What are the benefits of utilizing cloud computing services? What are the dangers and concerns relat...
A: Introduction: Cloud computing is like catch-all word for anything involving the delivery of hosted s...
Q: a.) Explain three reasons why modern operating systems are more robust and efficient than earlier on...
A: Here is the detailed explanation of the solution
Q: 1a.) Explain why an operating system is regarded as a resource manager; and give two examples of Ope...
A: The operating system acts as a manager of the above resources and allocates them to specific program...
Q: Discuss the purpose and importance of mathematical writing.
A: Perusing, composing, and arithmetic are, or ought to be, indivisible. Involved math can invigorate i...
Q: 1. Consider the Canadian Provinces and Territories: Nunavut, Saskatchewan, Manitoba, Ontario, Prince...
A:
Q: You have many filesystems on your hard drive, each of which is mounted to a different directory in t...
A: Introduction: You have many filesystems on your hard drive, each of which is mounted to a different ...
Q: What type of storage typically shares files utilizing standard network protocols, such as Server Mes...
A: According to our guidelines, we are allowed to solve only the first question. Please post the other ...
Q: The population of the five most populous Australian cities at the last three census is recorded in t...
A: Since no programming language is mentioned, I am using Matlab. Code: cities=categorical({'Sydney...
Q: vi. Explain the distinction between authorization and authentication in web testing.
A: Introduction difference between Authorization and Authentication in Web testing: Authorization: Auth...
Q: What is the purpose of TCP's Reliable service?
A: Introduction TCP : Transmission Control Protocol is a standard that defines how to establish and m...
Q: 3. The C++ statement that displays the values of two float numbers x and y, each in a field length o...
A: the function setw is used to set the field width to be used for output operations. It takes paramete...
Q: What exactly is an operating system? Only explain the batch operating system?
A: Operating system:- An OS is an interface between hardware compliers and the user. An OS is a device....
Q: Discuss how the darknet and deep web have made it more difficult to investigate and prosecute cyberc...
A: Introduction: The "darknet" is a subset of the "deep web," where the material is inaccessible throug...
Q: Who is in charge of the post-implementation review? When should it be done? Would a post-implementat...
A: Intro Who is in charge of the post-implementation review? When should it be done? Would a post-imple...
Q: Give at least two (2) examples of IT tasks that should be separated and explain why they should be s...
A: Introduction Give at least two sets of IT functions that should be segregated and explain the reason...
Q: The value of p after this command: A = [1:4; 5:8; 9:12]; p = size(A); O will be 12 will be a 3-by-4 ...
A: Below is the answer to above query. I hope this will be helpful for you...
Q: When a stalemate is identified, the required resources are made available to those who are unable to...
A: Introduction: We must now recover the deadlock after it has been found. There are generally two ways...
Q: What development model makes use of the waterfall model?
A: Intro The waterfall model is used under the SDLC models. This model enables the developers to develo...
Q: What are the benefits of utilizing cloud computing services? What are the dangers and concerns relat...
A: Introduction : Here's everything you need to know: There are various benefits to storing data over t...
Q: Write a python program with two or more functions that uses three or more paramters and arguments in...
A: 1)Declare one function display_state_details with arguments state code and district code and display...
Q: Discuss how multimedia is beneficial in our daily lives. ii. What would life be like without multime...
A: Introduction: Everything you see and hear in the form of text, images, audio, video, and other forma...
Q: yntaxError: EOL when scanning strin reral
A: Given:
Q: Given tle following Floyd Warshall algorithm, prove that there exists a vertex x with dist[x][x] < 0...
A: There are two ways to check this: 1. Check the main-diagonal entries of the result matrix for a nega...
Q: Explain how to give a text box keyboard access.
A: Introduction: To offer keyboard access to a text box, we must first do the following steps:
Q: Explain the difference between cyberbullying and cyberstalking using a real-world example?
A: Cyberstalking and cyberbullying are terms that are frequently interchanged and refer to the use of t...
Q: Compare and contrast cache memory and magnetic disk storage in a computer system with respect to the...
A: Please find the detailed answer in the following steps. Note: As per the Bartleby guideline I can...
Q: Minicomputer, mainframe and supercomputer are the three different kinds of computers available in th...
A: MINICOMPUTER: A minicomputer is a computer that is smaller, cheaper, and less powerful than a mainf...
Q: The house was hot because I had turned on the heating earlier correct O not correct The postman coul...
A: The answer of the following is given below.
Q: Describe how the three characteristics of big data are related to data collected by healthcare provi...
A: Introduction: The first stage is to acquire big data, which can come from a variety of sources, incl...
Q: O 5 O 2
A: Answers Number of times is the function wordScramble() called in the given program is 5 So, answ...
Q: In terms of machine learning or deep learning algorithms, how has artificial intelligence (AI) evolv...
A: Introduction: The last decade witnessed the phenomenal rise of Artificial Intelligence. The impact o...
Q: What are some examples of potential applications for cloud-based collaborative tools? Employees' abi...
A: Introduction: A cloud-based collaboration tool isn't only for communication; it also serves a variet...
Q: With the aid of an example and a diagram, show how internal fragmentation happens in fixed memory pa...
A: With the aid of an example and a diagram, show how internal fragmentation happens in fixed memory pa...
Q: hat will use the ls -la command to show the contents of your home directory. Use the above example i...
A: Given : Write a program that will use the ls -la command to show the contents of your home directory...
Q: Determine the current network environment's benefits and drawbacks.
A: Introduction: A computer network is a collection of computers that are linked together to share reso...
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 1 images

- UDP and TCP use one’s complement for the checksum. Suppose you have the flowing four 8-bit data in a datagram: 10011011, 01011100, 11001101. 10101001 a) What is the one’s complement of the sum of the four? Show your work. b) Is it possible that a 1-bit error will go undetected? Is it possible that a 2-bit error will go undetected?The following questions are true or false, and you should explain your answer to them in a few words: In this case, the alternating-bit protocol is the same as the SR protocol if both the sender and receiver window sizes are 1.Tell us if you think the following statements are true or incorrect and provide a short explanation for your vote. When both the sender's and receiver's window widths are 1, the alternating-bit protocol and the SR protocol are equivalent.
- Justify your answer with a short explanation if you think it's false or true. When the window sizes of the transmitter and receiver are both 1, the SR protocol and the alternating-bit protocol are equivalent.Do you have any thoughts on the issues I've posed below? What do you think? This is because the alternating-bit protocol is equivalent to the SR protocol when both the sender's and receiver's window sizes are 1.The following is a TCP (tranmission control protocol) header. How do I read it? What does each bit mean? c62800163d36b20c05087f6e7002ffff7bb70000
- The following statements may be answered with a "true" or "false" and a short explanation of your choice is also requested When the window widths of both the sender and the receiver are 1, the alternating-bit protocol is equivalent to the SR protocol.Elaborate the procedure involved in the implementation of pure aloha protocol with the help of thefollowing terms: T fr: Average Transmission TimeT B: Back off time: R* T p or R * T frR: Random Number: 0 to 2 k -1Give a trace of the operation of protocol rdt3.0 when data packets and acknowledgment packets are garbled.
- Draw the FSM for the receiver side of protocol rdt3.0 .Computer Science With the CBC/OFB/CFB/CTR mode: (a) if there is a single bit transmission error in block C3 of the ciphertext, which plaintext blocks are affected? CBC and CTR (b) Suppose that there is a bit error in the source version of P1. Through how many ciphertext blocks is this error propagated? What is the effect at the receiver?(a) If the second segment arrives before the first segment, in the ACK of the first arriving segment, what is the ACK number? (b) Draw and explain the 3-Way Handshake in TCP protocol.

