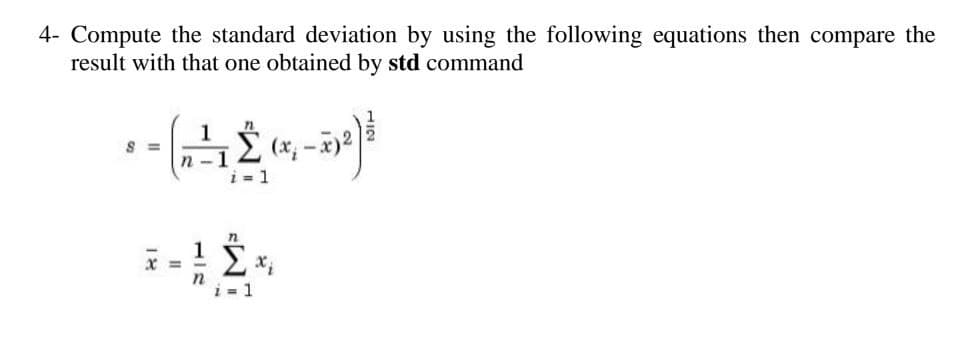
Compute the standard deviation by using the following equations then compare the result with that one obtained by std command (205) (x₁ - x)2 1 - Σ 1 112
Q: The number of available processors, both specialized and general-purpose, may be gleaned from the…
A: A processor is a logical circuit or chip used to run a computer. It processes and reacts to basic…
Q: Can you give me a high-level summary of the compiler and elaborate on why testability is so crucial?
A: Tips for Examinability: This concludes the complete testability tip. Use tactics for nonverbal…
Q: Consider the language L of strings over the alphabet Σ = {a, b} which contain an equal number of a’s…
A: Introduction A formal grammar called context-free grammar is used to produce every conceivable…
Q: ect information both while in motion and when stored? In addition, which security method provides…
A: In your view, what measures should be taken to protect information both while in motion and when…
Q: Don't just argue that deep access is preferable because it's faster; provide some concrete reasons…
A: Only when a procedure can be sent as an argument to a function does deep/shallow binding make sense.…
Q: Don't just cite performance gains when arguing in favor of deep access over shallow access; instead,…
A: Introduction: From the standpoint of a programmer, provide a defenses for using deep access as…
Q: Question 1: You have been assigned the role of a project manager for the following project: "An…
A: The SWOT analysis of An airport taxi reservation app is given in the below step
Q: Represent the following complex numbers in polar coordinate Z= 2 + 5j Y=-3-3j D=-2 +6j
A:
Q: This article will examine four distinct logical security methods that, if put into place, would…
A: Introduction: Logical security measures are those that limit system users' access rights and prevent…
Q: Let a1 = = 3, a2 = 4, and an+1 = 3≤an ≤ 4. (2an + an-1) for all n ≥ 2. Prove that for all positive…
A: Introduction In a kind of induction known as strong induction, we make the assumption that the…
Q: Please describe the ideal candidate for your role and the skills they must possess.
A: Introduction: The following is a list of skills that should be had by an employee in order for them…
Q: How likely is it that not only will the compiler be introduced, but that its importance to…
A: Introduction: Full testability hint below. Nonverbal communication. BNF the grammar. Explain how to…
Q: Examine the parallels and distinctions between Governance and Management as they pertain to the…
A: Introduction: In the context of information system auditing, contrast governance and management.…
Q: Thoroughly explain why it is preferred to use an external stylesheet instead of an internal style…
A: Thoroughly explain why it is preferred to use an external stylesheet instead of an internal style…
Q: Discuss the following about Import: (For Python) Provide a code example of an Import. Describe what…
A: Dear Student, The answer to your question is given below
Q: C++ Print numbers 0, 1, 2, ..., userNum as shown, with each number indented by that number of…
A: C++ (or “C-plus-plus”) is a general-purpose programming and coding language. C++ is used in…
Q: There are several considerations that must be made for a compiler to generate good and efficient…
A: A compiler is a special program that translates a programming language's source code into machine…
Q: Can you list the numerous factors that must be considered while building a compiler that generates…
A: Teaching principlesCompiler authors receive instruction set notions. These concepts help writers…
Q: What specific kind of computer architecture do smartphones and other mobile devices typically…
A: Dear Student, The answer to your question is given below -
Q: Having this error message when I try to open one of the files in my project on Eclipse: Could not…
A: The following solution is
Q: The Internet has developed into a vital instrument for expressing one's free speech, and it is…
A: Introduction: Internet is a computer-to-computer network. Millions of smaller networks transfer data…
Q: How can we define "system security" in its simplest terms?
A: System Security: System security is how an organisation protects its networks and resources against…
Q: In your opinion, what tasks fall primarily under the Compiler Phases' purview? Give some specific…
A: Passes are the number of times the compiler explores the source code. Compilers help with this.…
Q: When do you think it's best to keep everything on-premises, and when do you think it's better to…
A: Introduction On-premises software and cloud computing vary in one key sense. In an on-premises…
Q: Growth in technology means continuous transformation. Give an overview of the present status of…
A: Rapid technological change is inevitable. Discuss five computer or communication patterns that…
Q: Is it possible to completely switch the interface of one of the views inside the…
A: Model View Controller Architecture: This layout example inspires advanced programming agencies by…
Q: Create the GET_CREDIT_LIMIT procedure to obtain the full name and credit limit of the customer whose…
A: From the above given question we have to write an SQL query that take the Customer ID as input and…
Q: If there was no system of checks and balances or mandatory vacation policies, what security measures…
A: Introduction Malware is software that attacks computer systems with the intention of harming,…
Q: 2. Write a program that asks the user to input a number (n) and display the sum of first n integers…
A: Dear Student, The source code, implementation and expected output is given below -
Q: be done. You should only add one line of code. #include #include #include using namespace…
A: Dear Student, You just need to add the below given line - //Add line: double…
Q: Can you give me a high-level summary of the compiler and elaborate on why testability is so crucial?
A: Examinability Tips: This brings us to the end of the testability tip. Use nonverbal communication…
Q: To what extent can Deadlock Prevention only function if certain conditions are met?
A: Vital Factors To achieve standstill, it is necessary to meet the following four conditions: Mutual…
Q: 2. Using FCM toolbox in Matlab to cluster any dataset (at least 100 data) downloaded from public…
A: Fuzzy c-means (FCM) which refers to the one it is a data clustering technique in which a data set it…
Q: ctors, also being able to cho
A: How can I make a pentagon in java using constructors, also being able to choose its area and…
Q: As opposed to creating their own text files, why do most companies use a DBMS to store data?
A: DBMS: A Database Management System (DBMS) is application programming that permits clients to…
Q: With the tools we have now, it is possible to achieve this goal. When did computers start appearing…
A: Since their debut, computers have been essential, but they are now widely used. Due to their…
Q: A linked list can be single, double or _______ A: circular B: cylinder C: triangular D:…
A: Let's see the answer:
Q: Find out what the purpose of a file's extension is and how it affects the file you're now editing.…
A: File's: All computer programmes and data are "written" into and "read" from files. A folder can be…
Q: plified expression for the Boolean function ariable X, Y, and Z: Use capital letters. Use X
A:
Q: . What is the difference between a smooth model and a layered model when it comes to VES modeling?
A: The smooth model and the layered model are the two varieties of models that may be used in the…
Q: If a tree with a single node has a height of 1, how many nodes may there be in a balanced binary…
A: If the height of a tree with a single node is 1, then the resulting binary tree is five levels tall…
Q: Create three more classes that inherit from Crew. Unless noted otherwise, each of these classes has…
A: At the point when a vessel expects fixes to harmed gear or to the body it is fundamental for the…
Q: In the QuickSort algorithm, what is the time complexity (in Big-O notation) of the best case,…
A: Dear Student, The answer to your question is given below -
Q: Explain the idea of copy-on-write to me.
A: When a parent process creates a kid' Not all parent process pages must be replicated. Only…
Q: How relevant are rules about who can and cannot enter a certain area, anyway, in the modern world?…
A: Introduction: Access control is a security method that limits who or what may access resources. in…
Q: To create a mutually exclusive relationship between RadioMenuItem controls, you must group them in a…
A: Solution:-
Q: At the same time as you're developing the framework, you should be identifying and assessing the…
A: When it comes to the design of an information system, there are a few challenges that need to be…
Q: Which features should a compiler have to guarantee that the code it produces is valid and efficient?…
A: Compiler writers have instructions. These factors assist compiler developers construct a reliable…
Q: How is it decided what image from the ImageList will be shown in the PictureBox, and what value is…
A: The problem is based on the basics of lists and indexing in lists.
Q: Your company's outgoing CIO has put your name forward for consideration as a member of the search…
A: THE NEW COO SHOULD HAVE THE ABILITY TO HIRE A VARIETY OF NEW EMPLOYEES AS ONE OF HIS…
Step by step
Solved in 3 steps with 2 images

- Convert each of the following to the other canonical form: F ( A , B , C , D ) = Π ( 3 , 5 , 8 , 11 )Convert the following to the other canonical form: (a) F(x, y, z) = Σ (1, 3, 7) (b) F(A, B, C, D) = Π (0, 1,2,3,4,6,12)Q 3 Using the floating point format described in problem 5.19 of your text, convert the binary number -10011101001100.101001011 to the floating point representation. Please show work clearly Full explain this question and text typing work only thanks
- 9.9oi Convert the following NFA's to DFA's:Please please don't copy Computer Science for BCH (16,12). when input is (0, 4, 14, 14, 4, 4, 15, 2, 4, 2, 15, 13), what are the check digits?Develop a single-bit error-correcting Hamming code for 16-bit data string of your name’s first two alphabets in capital with respect to ASCII codes and then conversion it into binary in 8 bits with all necessary steps and also verify at the receiver.
- Convert each of the following to the other canonical form: F ( x , y , z ) = Σ ( 1 , 3 , 5 )1. If given the code 1001, how is it encoded with Hamming(7,4)? 2. Check if code 1101001 has errors and if so, indicate the position of the error and correct it, otherwise specify that it does not.Create a Hamming code (k, n) = (7,4) for the detection and correction of errors in word codes
- 1.19 C++ Given two input integers for an arrow body and arrowhead (respectively), print a right-facing arrow. Ex: If the input is: 0 1 the output is: 1 11 00000111 000001111 00000111 11 1Please solve and show all work. Thank you. Write down the binary representation of the decimal number 63.75, assuming the IEEE 754 single precision format.Define the binary operator :) by: aa :) b=8a+4b+9b=8a+4b+9 Find each of the following: 55 :) 33 = 66 :) 66 33 :) 55 = ww :) ss =

