Computer Science c++
Q: Interpolation is the name given to the procedure that includes guessing the value of a function at a…
A: Interpolation is a mathematical technique used to estimate the value of a function between two known…
Q: Which development methodology—Agile or Waterfall—should be used to build an online registration…
A: The development methodology used to build an online registration system for university classes can…
Q: What qualities do you believe a business should possess in order to be considered a "offshore 'hot…
A: What does offshore location mean in business: The term "offshore hot location" was used to refer to…
Q: In order to keep a firewall operating at its optimal level of performance, what are some of the most…
A: A firewall is a network security device that monitors and controls incoming and outgoing network…
Q: Which computationally dependent career involves performing troubleshooting issues to help people…
A: The computationally dependent career that involves performing troubleshooting issues to help people…
Q: The term "Slack" refers to one of the many different types of memory that may be found in an 8086…
A: In the 8086 microprocessor, stack memory is a special area of memory that is used to store data…
Q: Why do we need a data model, and how will having one help us achieve this objective?
A: According to the information given:- We have to define why do we need a data model, and how will…
Q: In what ways may the end user possibly benefit from data mining?
A: In today's digital age, vast amounts of data are generated every second from various sources such as…
Q: Bob and Thelma think a customer-food tracking system for the evening delivery service will offer…
A: An Entity-Relationship (ER) diagram is a graphical representation used to model the relationships…
Q: Draw a truth table and the block diagram of a decoder for converting binary to octal code
A: Here's the truth table for a decoder that converts binary to octal code: Truth table: Input…
Q: What's the difference between a computer's organization and its architecture, and why is it so…
A: Computer organization refers to the way the hardware components of a computer are designed and…
Q: The structure of the file space's hierarchical organization is known.
A: A Hierarchical File System is a way to organize digital files on a computer using folders and…
Q: The field of software engineering makes use of a variety of data types. Consider the distinctions…
A: Essential Data Types Basic data types are the basic structure block in programming languages. They…
Q: If Lawyer, Secretary and Marketer are all subclasses of the superclass Employee, write a Java…
A: 1. Define a class named "EmployeeTest"2. Define the "main" method inside the "EmployeeTest" class3.…
Q: Please explain why it is vital to have controls in a software system.
A: Controls play a vital role in software systems as they provide the means for users to interact with…
Q: One of the most fundamental ideas that rules the practise of software engineering is called "divide…
A: According to the information given:- We have to define separation of concerns (SoC).
Q: What exactly does it imply when it says that a hard disc drive has reached its superparamagnetic…
A: The superparamagnetic limit refers to the point at which a hard disk drive (HDD) reaches the…
Q: Do you think that those who have disabilities may benefit from using the internet?
A: The Internet has open up various channels for populace with disabilities, enabling them to…
Q: To fully grasp the concept of "consideration," it is necessary to be familiar with its connotations.…
A: "Consideration" refers to the value or benefit that one party provides to another in exchange for…
Q: If there is such a thing as a relational model, what is the overarching name for attributes, and how…
A: Answer is given below
Q: There are several kinds of firewalls. What sets it apart from other things? The use of firewalls in…
A: In today's digital age, network security has become a major concern for businesses in all…
Q: Exactly what does the npm package consist of? Please explain what you mean using just your own…
A: NPM : The default package manager for JavaScript runtime Node.js is called "Node Package Manager."…
Q: Find out the reasons why firewalls for physical security are essential for an organisation.
A: Firewalls for physical security are an essential component of any organization's security…
Q: Can an object in a superclass be assigned to a subclass variable? Why?
A: Inheritance is a fundamental concept in object-oriented programming that enables classes to reuse…
Q: Please define the software development process's metrics. Should the issue be fully addressed?
A: What is software: Software is a set of instructions that tells a computer what to do. It includes…
Q: The display layer, the data management layer, and any other layer are always found on the client…
A: The application stack is a conceptual framework that describes the different layers that make up a…
Q: To a fellow student, what sort of storage medium would you recommend?
A: A storage media is a physical device in a computer that receives, stores, and retrieves electronic…
Q: What is the key distinction between a format and an instruction set?
A: Format vs. Instruction Set: Definitions Format refers to how data is organized, stored, and…
Q: Where exactly should the individual literals that make up a string be placed?
A: In computer programming, a string is a sequence of characters. Strings are commonly used to…
Q: Show the function header for a void function that takes a 2-dimensional character array of 3 rows…
A: MULTI DIMENSIONAL ARRAYS Multi-dimensional arrays are a data structure that allows you to represent…
Q: make a code seizure in visual studio. Note: explaining the steps
A: In today's fast-paced world, the development of efficient and reliable software is essential for a…
Q: Data that has been previously accessed may reap the benefits of "spatial locality" and "temporal…
A: For quick and effective functioning, computer systems depend on quick access to data. Caching, which…
Q: Solve the following codes below and discuss how array, stack, and queues are used in each problem.…
A: Explanation : In this program the array created is of the size N and then this array is being…
Q: Was the hierarchy of the file space something that arose by chance, or was it intentional from
A: Files are arranged in a tree-like structure of folders and subfolders, which is the hierarchy of the…
Q: What kind of changes have been brought about by the internet in the way that systems are designed?
A: The internet is a global network of interconnected computer networks that allows people to access…
Q: Give some specific examples of the features that the Just in Time system possesses.
A: Just-in-Time (JIT) is a system used to improve efficiency and reduce waste in manufacturing and…
Q: Explain the differences that exist between control buses, data buses, and address buses.
A: In computer architecture and digital electronics, buses are used to transfer data between various…
Q: In this video, I will discuss why I believe that people and information systems are the fundamental…
A: Information technology has been progressing rapidly over the past few decades, and it has changed…
Q: What exactly is meant by the term "input data validation"?
A: Input validation, which is also known as data validation, checks the appropriateness of any input…
Q: O Using an array, ask user to input 5 integers (ranging from 1-10). Print how many values are…
A: Start Initialize an empty array to store the 5 integers. Ask the user to input an integer (1 to 10)…
Q: result
A: Investigate the challenges that data systems face as a result of their reliance on technology and…
Q: Question 1 The following is an interrace for a class FlightNode: class FlightNode /* attributes */…
A: I assumed that the Date object is referring to java.util.Date and that the format of the toString()…
Q: Discuss in some detail the primary reasons why it is often more cost effective, over the course of…
A: There are several primary reasons why it is often more cost-effective to develop software systems by…
Q: Include specifics on the client/server architecture, such as the number of tiers, a cost/benefit…
A: Client/server architecture is a distributed computing model that is widely used in modern software…
Q: In what ways did the existence of resident monitors contribute to the enhancement of computer…
A: Here is your solution :
Q: When it's required to do so, large computer processes and software may be broken down into smaller…
A: Breaking down large computer processes and software into smaller subsystems can offer several…
Q: You have an array of n real numbers and another integer s. Find out whether the array contains two…
A: The algorithm to solve this problem with better than quadratic time efficiency is as follows:…
Q: In what ways is it necessary for the process of developing software to make use of a range of…
A: Software testing is a dangerous aspect of software expansion that aims to spot and rectify issue,…
Q: Explain? is someone who inspires technical experts to reach their potential.
A: An individual who inspires technical experts to reach their potential can be described as a leader…
Q: Let A ={a1,...,an} and B ={b1,...,bm} be two sets of numbers. Consider the problem of finding their…
A: A=a1,...,an B=b1,...,bm Set C of all the numbers that are in both A and B.
Computer Science
c++
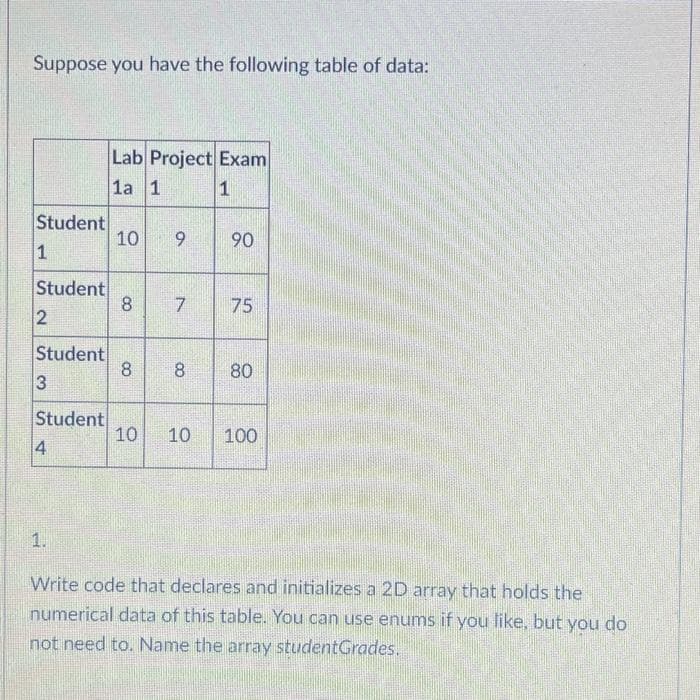
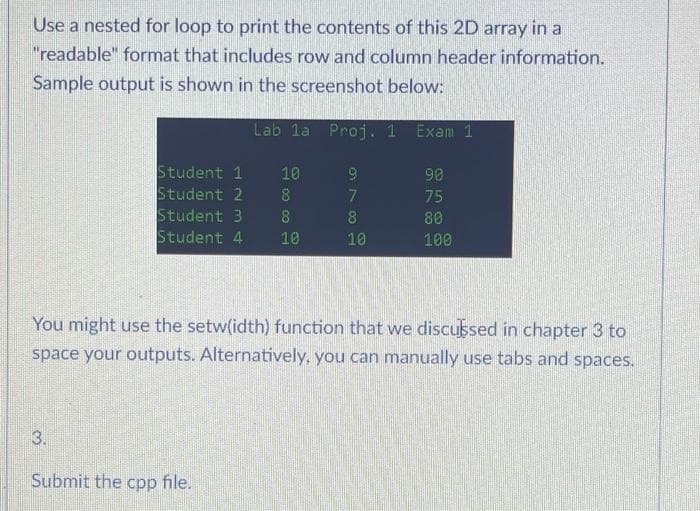
Step by step
Solved in 4 steps with 2 images

- ScenarioI want to create an INDEXCEPTION value of the unique vowels and unique consonants that the name that was given to you can create.InputA string of the name that was GIVEN TO YOU. CASE SENSITIVE.ProcessStep 1: For every unique vowel of a name, you need to get the first index of that vowel from the original string.Step 2: For each vowel index you get from step 1, you will get the unique consonant from that position. if the index is out of scope of the consonant array, ignore that vowel index.Step 3: For each unique consonant that you get from step 2, you need to get the first index of that consonant from the original string.Step 4: Get the value of indexception by adding all index you get from step 3.OutputTO BE DISPLAYED- 2 lists that consists of unique vowels and unique consonants- The vowel, the vowel index, the consonant, the consonant indexFINAL OUTPUT- The total indexception value of the name that was given to you.Create a program that allows you to create a fantasy football roster based on the existing list of available players. Your team can only have 5 players, so create an array that can store 5 possible players. Prompt the user to pick 5 players to add to their team. If the player is available in the list of availablePlayers, then add that player to the users array, and remove that player from the availablePlayers list. Then prompt the user to pick another player. Once all five players have been added, then print the list in the console. Create a search method to find the index at which the player is located in the availablePlayers list so you can remove the player, and make sure that they are an eligible pick. Here is a sample run of the program: Enter Player you would like on your team: Cam Newton Great! That player is added to your team! Enter Player you would like on your team: Travis Kelce Great! That player is added to your team! Enter Player you would like on your team: Alvin Kamara…javascript 7. Create a function that filters out negative numbers In this challenge, you'll have a function that takes an array as an input and returns an array. But if all goes according to plan, it'll remove the negative numbers. This is another example of a task that'll be useful when combing through data and looking for clever ways to eliminate "bad data."
- Below you will find code blocks necessary to insert a value into an ordered array given a position (index) to insert. Be careful! Some lines are not needed. first line COMPLETED: bool insertElement(char array[ ], int& numElems, int &capacity, in position, char value) { last line COMPLETE: bool insertElement(char array[ ], int numElems, int capacity, in position, char value) {Please Help Write a program to ask the user for the number of arrays he wants to maintain and then populate eacharray by taking elements from the user. Merge all these arrays in another array and finally remove duplicateelements from the merged array.A personal phone directory contains room for first names and phone numbers for 30 people. Assign names and phone numbers for the first 10 people. Prompt the user for a name, and if the name is found in the list, display the corresponding phone number. If the name is not found in the list, prompt the user for a phone number, and add the new name and phone number to the list. Continue to prompt the user for names until the user enters quit. After the arrays are full (containing 30 names), do not allow the user to add new entries. Use the following names and phone numbers: Name Phone # Gina (847) 341-0912 Marcia (847) 341-2392 Rita (847) 354-0654 Jennifer (414) 234-0912 Fred (414) 435-6567 Neil (608) 123-0904 Judy (608) 435-0434 Arlene (608) 123-0312 LaWanda (920) 787-9813 Deepak (930) 412-0991
- A personal phone directory contains room for first names and phone numbers for 30 people. Assign names and phone numbers for the first 10 people. Prompt the user for a name, and if the name is found in the list, display the corresponding phone number. If the name is not found in the list, prompt the user for a phone number, and add the new name and phone number to the list. Continue to prompt the user for names until the user enters quit. After the arrays are full (containing 30 names), do not allow the user to add new entries. Using Scanner.input to prompt user, Use the following names and phone numbers: Gina (847) 341-0912 Marcia (847) 341-2392 Rita (847) 354-0654 Jennifer (414) 234-0912 Fred (414) 435-6567 Neil (608) 123-0904 Judy (608) 435-0434 Arlene (608) 123-0312 LaWanda (920) 787-9813 Deepak (930) 412-0991A personal phone directory contains room for first names and phone numbers for 30 people. Assign names and phone numbers for the first 10 people. Prompt the user for a name, and if the name is found in the list, display the corresponding phone number. If the name is not found in the list, prompt the user for a phone number, and add the new name and phone number to the list. Continue to prompt the user for names until the user enters quit. After the arrays are full (containing 30 names), do not allow the user to add new entries. Use the following names and phone numbers:A personal phone directory contains room for first names and phone numbers for 30 people. Assign names and phone numbers for the first 10 people. Prompt the user for a name, and if the name is found in the list, display the corresponding phone number. If the name is not found in the list, prompt the user for a phone number, and add the new name and phone number to the list. Continue to prompt the user for names until the user enters quit. After the arrays are full (containing 30 names), do not allow the user to add new entries.
- A personal phone directory contains room for first names and phone numbers for 30 people. Assign names and phone numbers for the first 10 people. Prompt the user for a name, and if the name is found in the list, display the corresponding phone number. If the name is not found in the list, prompt the user for a phone number, and add the new name and phone number to the list. Continue to prompt the user for names until the user enters quit. After the arrays are full (containing 30 names), do not allow the user to add new entries. Use the following names and phone numbers: Name Phone # Gina (847) 341-0912 Marcia (847) 341-2392 Rita (847) 354-0654 Jennifer (414) 234-0912 Fred (414) 435-6567 Neil (608) 123-0904 Judy (608) 435-0434 Arlene (608) 123-0312 LaWanda (920) 787-9813 Deepak (930) 412-0991 import java.util.*; class PhoneNumbers { public static void main(String[] args) { // Write your code here } }Below you will find code blocks necessary to insert a value into an ordered array given a position (index) to insert. Be careful! Some lines are not needed.can you show me the screen shot of the out put INCLUDE Irvine32.inc .DATAarray DWORD 10h, 20h, 30h, 40harraySize = ($ - array) / TYPE array .CODEmain PROC ; Display the array values before shifting CALL DumpMem CALL Crlf ; Rotate the elements of the array forward one position MOV EAX, array[arraySize - 1] ; Save the last element of the array in EAX MOV ECX, arraySize - 1rotateLoop: MOV EDX, array[ECX - 1] ; Move the previous element into EDX MOV array[ECX], EDX ; Move the previous element into the current element LOOP rotateLoop MOV array[0], EAX ; Move the last element into the first element ; Display the array values after shifting CALL DumpMem CALL Crlf CALL WaitMsg RETmain ENDP END main





