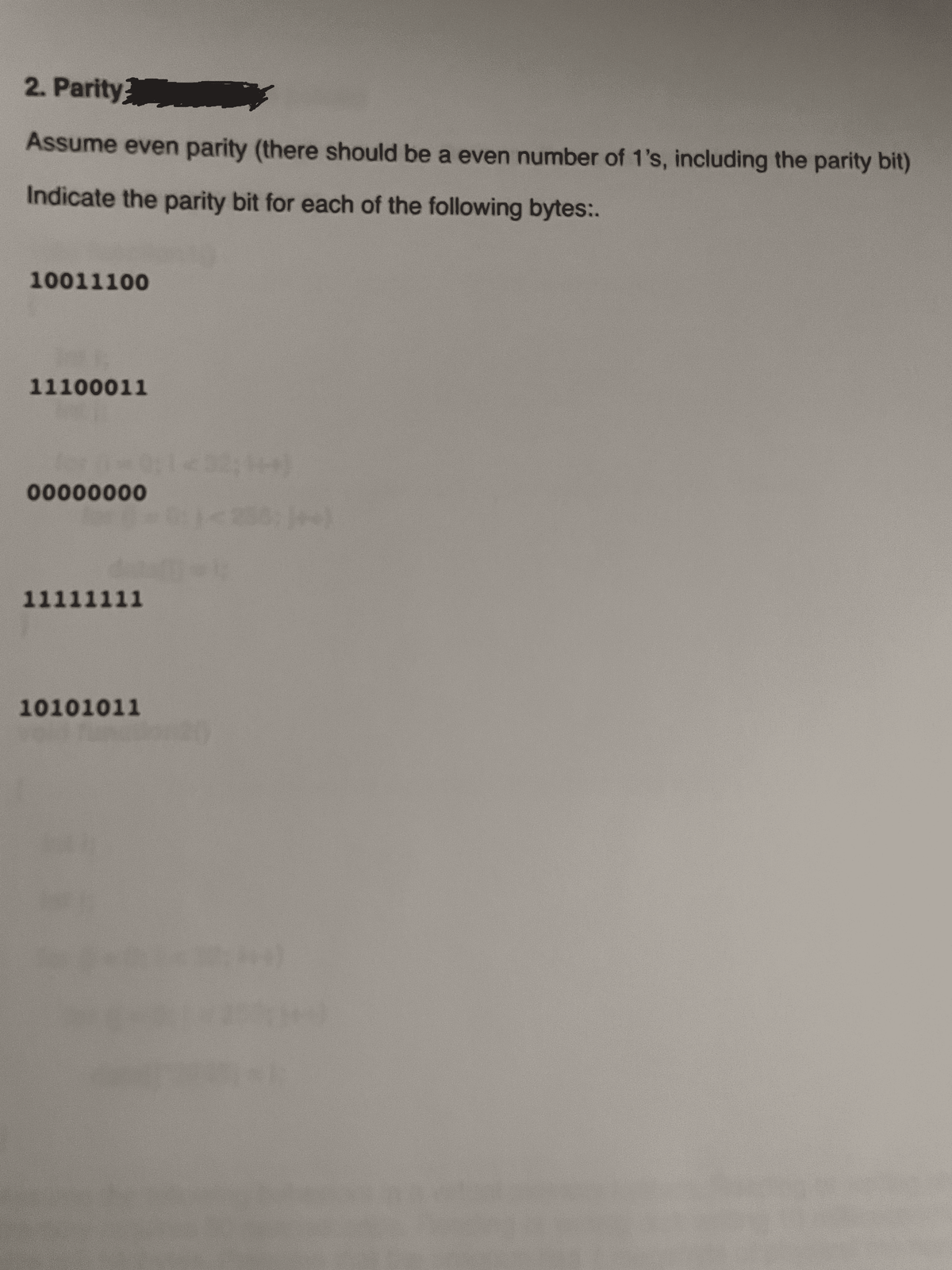
2. Parity Assume even parity (there should be a even number of 1's, including the parity bit) Indicate the parity bit for each of the following bytes:. 10011100 11100011 1432 00000000 11111111 10101011
Q: What is the definition of a self-referential data structure?
A: Intro Self Referential structures are those structures that have one or more pointers that point to ...
Q: Consider the following 2 transactions: T1: R(A); R(B); B=A+B; W(B) T2: R(B); R(A); A=A+B;...
A: Answer 1: In below , i am adding X lock and S lock. ================================================...
Q: Describe two processes that all queues must carry out.
A: Intro The queue is an abstract arrangement, somewhat just like Stacks. in contrast to stacks, a queu...
Q: Explain the concept of timeboxing as a hallmark of DSDM practice in a succinct manner.
A: Introduction: DSDM recommends gathering high-level needs early in the project. As the project procee...
Q: Hi I am having some difficulties with this problem, I am not sure why my code is giving an incorrect...
A: After adding some code, I have provided JAVA CODE along with CODE SCREENSHOT and OUTPUT S...
Q: Discuss the advantages and disadvantages of each type of typing.
A: Static typing: In static typing, type checker assign objects to particular type during compilation p...
Q: What is the Dynamic Web Development Environment?
A: In this problem, we will discuss a Dynamic web development environment. Introduction: In software an...
Q: What is the function of a broadband modem? List two modulation techniques you're familiar with
A: Introduction: A broadband modem enables users to connect to the internet through modem on their comp...
Q: What is the command for using the System File Checker to verify system files right away? To double-c...
A: Introduction: What is the command for using the System File Checker to verify system files right awa...
Q: What are the most prevalent multimedia file formats
A: Answer is given below-
Q: When does the compiler produce code for a function template?
A: Intro the above question is about When does the compiler produces code for a function template? ...
Q: For Java I need help I am to write a Java program that reads two integers then displays the sum,...
A: here in this question we have asked to write a Java program that reads two integers then displays t...
Q: Explain the three main methods of file structure.
A: Introduction: The organisation of data on a secondary storage device in such a way that access time ...
Q: The aim and objectives of prototyping in software engineering should be discussed.
A: Introduction: Prototyping Paradigm: In Software Engineering, a prototype ...
Q: What are your thoughts on Cybersecurity and Infrastructure Security Agency Act? Cite a source to sup...
A: Cybersecurity and Infrastructure Security Agency Act is also known the short name of CISA Act.
Q: Write a program that prompts for a file name, then opens that file and reads through the file DNSLis...
A: We have to program a prompt file name, open that file, read through the file. Python Program def re...
Q: What is the definition of a snooping protocol?
A: Introduction: A snooping protocol, sometimes known as a "bus-snooping protocol," maintains cache coh...
Q: 1. Write and run a C++ program to test the following function that returns the sum of the floats poi...
A: void swap (int *a, int *b);int main() { int m = 25; int n = 100; printf("m is %d, n is %d\n", m, ...
Q: in C programming Write a main function that declares an array of 100 doubles. In a for loop, assign...
A: #include <stdio.h>#include <stdlib.h> #include <time.h>int main(){double array[10...
Q: C++ PROGRAMMING Please implement these 2 methods for the node where: •int get_depth(): Returns th...
A: C++ program to get height and depth of the node
Q: What exactly is the Web Services Description Language (WSDL)?
A: Web services Description Language (WSDL) Web Services Description Language (WSDL) is an acronym for...
Q: How can a systems designer ensure a user that the interface is listening to him, or getting informat...
A: Introduction: to ensure that the interface is listening to or receiving information from the user:
Q: Apply Discrete Cosine Transform (DCT) to the following image : 1 2 2 1
A: DCT is also known as discrete cosine transform.
Q: In the field of data structures and algorithms, what is the binary tree, in which every node has eit...
A: Binary Tree is belongs to data structures,
Q: In terms of network security, what is cryptography?
A: Cryptography is a security measure/process in which important messages/information is transformed in...
Q: Provide examples of three intriguing new applications that are becoming feasible as a result of the ...
A: The Internet is a vast network that connects computers all over the world.
Q: High-level programming languages are used to provide English-like programs that are executed on comp...
A: ALGORITHM:- 1. Take input from the user for 3 numbers. 2. Find the sum and average of the numbers. 3...
Q: Create a pyton file which will compute the mean upon opening a certain txt file named numbers.txt wh...
A: l=list(map(int,input().split()))su=0for i in l: su+=i;print(su/len(l))
Q: What is CIDR exactly, and how does it work?
A: Classless Inter-Domain Routing(CIDR),it's an IP addressing method that improves IP address allocatio...
Q: Data warehousing services delivered using a cloud-based architecture provide several benefits.
A: Introduction What is cloud computing? Simply put, cloud computing is the delivery of computing serv...
Q: At the IT consulting firm where you work, there is a heated dispute going on. Some members of the te...
A: Introduction: Problems may develop at first due to reluctance to change, but strong analytical skill...
Q: What is the role of cryptography in network security?
A: Introduction: Do you recall what you do if you want to tell someone a secret of yours? Yes, you say ...
Q: Which of the following is NOT a walk from A to D? B E F Figure 1 O A) AEFEBCD В) АВCD O C) AFEBCD O ...
A: Answer the above questions are as follows:
Q: Which situations might warrant the use of a CNAME record?
A: Answer:
Q: can someone explain to me the logic and help me with this problem a.correct any syntax errors in th...
A: Given c program contains 3 variables i, n and p. The first for loop iterates from 1 to 5. The inner ...
Q: What exactly is an operating system? Name a few popular operating systems.
A: Intro Operating System (OS) is a visual interface between a computer user and computer hardware. An ...
Q: Description of the SQLiteOpenHelper and SQLiteCursor classes, with emphasis on their utility in exec...
A: Introduction: Android has a class called SQLiteOpenHelper for handling database-related tasks. All d...
Q: What is the location and name of the Windows paging file for virtual memory?
A: Introduction: The virtual memory, which is the windows page file, is accessed in the same manner as ...
Q: Problem: Write a Python code that determines whether or not a given positive number is a multiple of...
A: n = int(input())list = []c = 2while(n > 1): if(n % c == 0): list.append(c) n = n / c else: c =...
Q: What is it about documentation that is so critical to a successful criminal investigation? Make a li...
A: The following is the response: The Importance of Documenting Criminal Investigation ProceduresWhile ...
Q: Explain how a botnet is built and how it is used in a DDoS attack.
A: Introduction: The attacker who wants to construct a botnet continues to monitor host networks for vu...
Q: operation will relinquish those resources. A function that implements a blocking read of a UART will...
A: If you haven’t already been introduced to the concept, computing defines “blocking” and “non-blockin...
Q: Which of the following best explain what a batch program is? A. Batch program typically are progr...
A: Answer: A. Batch program typically are program that automatically executes its instruction once its ...
Q: Create a Python statement that opens a text file named someStuff.txt for output and saves the conten...
A: Algorithm: Start Set filename="someStuff.txt" and readfile="demo.txt" Open filename file in write m...
Q: Get three exam grades from the user and compute the average of the grades. Output the average of the...
A: NOTE: Programming language is not mentioned so I am doing in C++ In this question, we are asked to w...
Q: Computer science Explain the relevance of information systems and how they are used in various corp...
A: Introduction Explain the relevance of information systems and how they are used in various corporate...
Q: In the field of data structures and algorithms, what is the binary tree, in which every node has eit...
A: Binary tree is a tree where every node has a maximum of two child nodes There are various types of b...
Q: Why is sliding window flow control preferable than stop and wait? Implement sliding window flow cont...
A: Intro With the employment of multiple frames for one message, the stop-and-wait protocol doesn'tperf...
Q: How to hack via the wps security?
A: WPS is one of the most common safety standards for a wireless home network that enables the users of...
Q: function 2: series_generator2(int n); // n is the number of elements to display // series: 19683 656...
A: Code for given function is: void series_generator2(int n){ // n is the number of elements to displa...
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- A(n) __________ is an integer stored in double the normal number of bit positions.___________ occurs when the result of an arithmetic operation exceeds the number of bits available to store it.1. Using even parity, add parity bits to the following bit patterns: a. 0110 100 b. 1011 011 c. 0000 000 2. Using odd parity, add parity bits to the following bit patters: a. 0110 100 b. 1011 011 c. 0000 000
- Convert each of the following bit patterns into real numbers. Assume the values are stored using the floating point bit model. 00111111100000000000000000000000 = 11000001000101101011100001010010 =What bit pattern is stored for the following characters assuming an 8-bit byte? a. A b. a c. 8 d. % 2. What character is represented by the following bit patterns? a. 0011 0000 b. 0100 0011 c. 0111 1000 d. 0010 1010Using even parity, add parity bits to the following bit patterns 0110 100 1011 011 0000 000 Using odd parity, add parity bits to the following bit patterns 0110 100 1011 011 0000 0000
- a) Use the two’s complement binary representation to represent each of the following integers as 10-bit binary numbers. i) -13710 ii) 14510 iii) -15810 iv) 16710 v) -11510 b) If an 8-bit binary number is used to represent an analog value in the range from 0 to 100kg, what does the binary value 011001002 represent?Show Steps Please 8. Decode the following ASCII message, assuming 7-bit ASCII characters and no parity: 1001010 1001111 1001000 1001110 0100000 1000100 1001111 1000101What are the 16-bit 1’s and 2’s complements of the following binarynumbers? a. 10000
- 271. In Return to Zero (RZ), the signal changes not between bits but a. before the bit b. after the bit c. doesn d. during the bitCharacter P is encoded as 1010000 in a computer. Usually, a parity bit will be sent together with a character. What is the odd parity bit for character P?2. What is the 2s complement of the following binary numbers? a. 01100 b 10001 3. Add the following 5-bit signed binary numbers together. Please indicate if overflow occurs. a. 00100 + 11000 b. 01010 + 01000 c. 11010 + 10011

