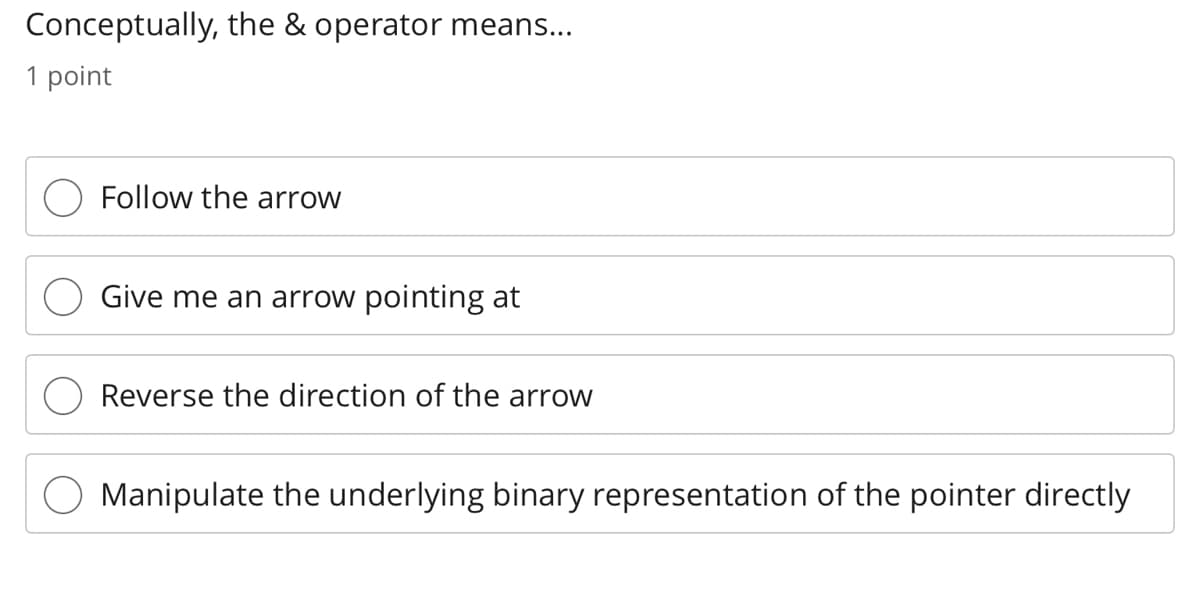
Conceptually, the & operator means... 1 point Follow the arrow Give me an arrow pointing at Reverse the direction of the arrow
Q: Give an explanation of how starting with a blank sheet of paper is different from utilising a…
A: A blank sheet of paper is different from utilizing a packaged data model for data modeling because…
Q: A path of length two is denoted by P2. If a graph G does not contain P2 as induced subgraph, then:…
A: Given: A path of length two is denoted by P2. If a graph G does not contain P2 as induced…
Q: Which sensors are compatible with MIT App Inventor? Is MIT App Inventor limited to a certain set of…
A: App Inventor by MIT It essentially enables the developer to create Android phone applications using…
Q: Explain the differences between supervised and unsupervised learning and why you value each kind of…
A: Supervised learning: Under supervision learning The learning process known as supervised learning…
Q: Which is better for collaboration: Office 365 or Google Docs?
A: To explain if Google Docs vs Office 365 is the superior option: Google docs: The online word…
Q: Give an explanation of how starting with a blank sheet of paper is different from utilising a…
A: A data model: A packaged data model makes the metadata of a consistent, industry-validated data…
Q: What do you mean by Data Terminating Equipment (DCE)?
A: Data terminal equipment (DCE) is:
Q: describe the data in the various operational systems?
A: Lets see the solution.
Q: What do you mean by Data Terminating Equipment (DCE)?
A: Lets see the solution.
Q: What distinguishes a text file from a binary file?
A: The solution is given in the next steps
Q: What does the term "l-value" mean? What does r-value mean?
A: L-value: L-value refers to the memory location that uniquely identifies an item. L-value can…
Q: How does information go across the layers of the Internet? model?
A: The answer for the above question is given in the below step.
Q: What does iteration in a loop really mean?
A: A loop is used to repeat a set of task multiple times.
Q: Consider the count-to-infinity issue in the distance vector routing. Can the count-to-infinity issue…
A: Distance vector routing is an asynchronous algorithm in which node x sends the copy of its distance…
Q: Is there a certain kind of object you need to make in order to read information from a text file?
A: The answer of the question is given below
Q: When making decisions about cyber security, network protocols and communication are crucial factors…
A: Computer security, network security, or information technology security is the protection of…
Q: What does having a digital envelope entail? Can you describe how it operates?
A: Electronic envelope: A sort of encryption known as a "digital envelope" ensures the integrity of the…
Q: Why should you utilise an Open and/or Save As dialogue box in an application that deals with files?…
A: The Common Item Dialog has replaced the Open and Save As common dialogue boxes.
Q: In a few phrases, describe how embedded systems are used.
A: Given: The term "embedded system" refers to a particular kind of computer system that is composed of…
Q: Effective practises are needed while choosing a career. These are a few of the foundational elements…
A: Given: CDue to the fact that there are a number of questions that have been asked, we will just…
Q: In only a few phrases, describe UTF-8.
A: UTF-8 (UCS Transformation Format 8) is the most prevalent character encoding on the World Wide Web.…
Q: Describe the operation of wireless LANs and demonstrate your familiarity with their setup and…
A: The answer to the question is given below:
Q: Explain the differences between supervised and unsupervised learning and why you value each kind of…
A: presented data is Explain the differences between supervised and unsupervised learning and why you…
Q: The capabilities of various requirements engineering CASE systems will be identified and explained…
A: The automation of all or a portion of the systems development process is what is referred to as…
Q: Does a method that accepts an array as an argument really have access to the original array, or is…
A: I am considering Java programming language to prove the above statement.
Q: An overview of Visual Studio should be provided.
A: Given: To create GUIs, websites, web apps, mobile apps, etc., Visual Studio is a popular IDE.The…
Q: When is it important to do a type conversion run-time check?
A: The following are the conditions for a type conversion: When a user works with float data type and…
Q: Is there a certain kind of object you need to make in order to read information from a text file?
A: Object of a file A file object is a kind of object that is connected to a particular file and gives…
Q: Which is better for collaboration: Office 365 or Google Docs?
A: Introduction In this question, we are asked Which is better for collaboration Office 365 or Google…
Q: Give an explanation of how starting with a blank sheet of paper is different from utilising a…
A: Data model: A rakaged data model makes the metadata of a consistent, industry-verified data model…
Q: What use is a sorting algorithm if it can't locate the information you need?
A: NOTE :- Below i explain the answer in my own words by which you understand it well. An sorting…
Q: n explanation of how starting with a blank sheet of paper is different from utilising a packaged…
A: Lets see the solution.
Q: There are several factors to take into account while discussing attribute inheritance.
A: An inheritance attribute is defined as the one that inherited from the parent class so that changes…
Q: Give a brief explanation of sign extension.
A: Sign extension: Sign extension is the operation, in computer arithmetic,…
Q: Explain the differences between supervised and unsupervised learning and why you value each kind of…
A: Introduction: In the fields of artificial intelligence and the computer science, there is a subfield…
Q: Does a method that accepts an array as an argument really have access to the original array, or €140
A: Answer: An Array is passed by reference UNLESS it is altered inside the method/function you're…
Q: inside the OS 1. What are the advantages of having both kernel and user modes? 2. How is a new…
A: The requirement for two modes in the OS User mode and kernel mode are the two OS configurations. The…
Q: How does information go across the layers of the Internet? model?
A: Introduction: If you use an Internet Protocol (IP) and TCP packet routing network, then it works…
Q: Give a brief explanation of conditional transfer.
A: The micro operation transfer among the registers is represented by RTL i.e. Register Transfer…
Q: The capabilities of various requirements engineering CASE systems will be identified and explained…
A: A central repository will include standard information in a CASE tool. They are the tools and…
Q: alk to your peers and the lecturer about the concepts of "data pre-processing," "data…
A: Answer : Data pre processing : In this process the raw data or any data which has no meaning or from…
Q: Which sensors are compatible with MIT App Inventor? Is MIT App Inventor limited to a certain set of…
A: App Inventor by MIT: It essentially enables the developer to create Android phone apps using a web…
Q: Look through the method header below, then, as an example, write a call to the method. an internal…
A: Example of calling the specified method An access modifier, method name, return type, and…
Q: What does having a digital envelope entail? Can you describe how it operates?
A: To be determine: Describe about digital envelope Digital Envelope: A digital envelope is a kind of…
Q: What Makes Up a Computer System's Components? Give a succinct explanation.
A: What Makes Up a Computer System's Components? Give a concise explanation. Every computer system…
Q: The question was: What are the methods and difficulties for using blockchain in the banking…
A: A blockchain is made up of discrete data blocks connected in chronological order, each containing a…
Q: Briefly describe the command queue.
A: Instruction Queue A structure that contains instructions and acts as a source for the processor to…
Q: How does information go across the layers of the Internet? model?
A: Information on the Internet travels in packets. Packets are like letters in an envelope: they have…
Q: Give a brief explanation of sign extension.
A: Sign extension :- In computer arithmetic, the process of raising a binary number's bit count while…
Q: In just a few phrases, describe ALIGN.
A: Alignment relates to the placement and arrangement of text. Microsoft Word's default defaults align…
Step by step
Solved in 2 steps

- In C++ Create an array of head pointers, statically allocated of size 101 of that type: Now, create a pointer that can point to the first element: Show how to dynamically allocate an array of 101 elements of head pointers: Write the code to initialize each element to NULL: Rewrite the code to initialize each element to NULL using pointer arithmetic:Specify the problems with the pointer's layout. Although there are exceptions, most computer languages only allow pointers to refer to a single kind of variable.C PROGRAMMING Differentiate the output of the two programs. a. struct node {int x;node *next;};int main(){node *root; // This will be the unchanging first noderoot = new node; // Now root points to a node structroot->next = 0; // The node root points to has its next pointer// set equal to a null pointerroot->x = 5;} // By using the -> operator, you can modify the node// a pointer (root in this case) points to. b.struct node {int x;node *next;};int main(){node *root; // This won't change, or we would lose the list in memorynode *conductor; // This will point to each node as it traverses the listroot = new node; // Sets it to actually point to somethingroot->next = 0; // Otherwise it would not work wellroot->x = 12;conductor = root; // The conductor points to the first nodeif ( conductor != 0 ) {while ( conductor->next != 0)conductor = conductor->next;}conductor->next = new node; // Creates a node at the end of the listconductor = conductor->next; // Points to…
- A pointer int *p is declared, it is able to hold addresses of double type values as well.. Single choice. True FalseThis lab will exercise your understanding of some of the concepts covered in Chapter 14: pointers and linked lists 1. Declare an integer pointer variable intPointer. Initialize it to point to an int variable named someInt. Assign the value 451 to someInt and output (cout) the variable someInt and output (cout) the value pointed to by intPointer. Write an assignment statement that indirectly stores 900 into the value pointed to by intPointer. Output (cout) the value pointed to by intPointer and output (cout) the variable someInt, 2. Declare a pointer variable charArrPointer and initialize it to point to the first element of a three-element char array named initials. Write assignment statements to store 'A', 'E', and 'W' into the first three elements of the array POINTED to by charArrPointer. Do NOT store any values directly into the array named initials. 3. Output (cout) the data in array charArrPointer and the data in array initials. 4. Copy the following code into your program above…“Array name can act as a constant pointer”. Justify the given statement by distinguishing array name with pointer variable and suitable examples.Explain in C programming language.
- List 3 properties of a pointerUSING C LANGUAGE COMPLETE THE PROBLEM USING POINTERS AND ARRAYS #include <stdio.h> int main(){} char letters[26]; char *pc1 = letters; /* Equivalent pointer values. */ char *pc2 = &letters; char *pc3 = &letters[0]; letters[4] = "e"; /* Equivalent indexes. */ pc1[4] = ’e’; *(letters + 4) = "e"; *(pc2 + 4) = "e"; pc3 = &letters[10]; /* Equivalent addresses. */ pc3 = &pc1[10]; pc3 = letters + 10; pc3 = pc2 + 10; }What is a variable pointer? What follows? It is a variable array. Why are pointers and dynamic arrays problematic?
- How difficult is it to move shared references into another array while using the C++ programming language? Create a list of potential solutions to the problem. Are shared pointers able to move the objects over which they have control? What gives?C++ Pointers must be used to solve the following problem. Write a function createPassword() with no return value to randomly select 8 capital letters from the alphabet. The function receives the address of the first characters of the password string as parameter. Hint: Declare a characters string that contains all the capital letters of the alphabet and use the index values of the characters in the string for random selection of characters, e.g.char alpha [27] = “ABCDEFGHIJKLMNOPQRSTUVWXYZ”;char *pAlpha = alpha; Display the password from the main() function. Write a function replaceVowels() with no return value to replace all the vowels (A, E, I, O, U) that have been selected with a symbol from the list ($ % @ # &). That is, A must be replaced by $, E replaced by %, I mustbe replaced by @, O replaced by #, and U must be replaced by &. The function receives the address of the first characters of the password string as parameter. Display the password agin from the main()…When moved swiftly, the pointer submarines.



