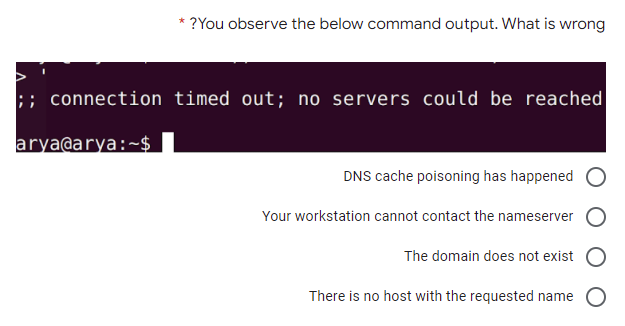
conhection timed out; no servers la bè Pea @arya:~$ DNS cache poisoning has happem Your workstation cannot contact the nameser The domain does not e:
Q: Write a program that will take this dictionary: gradePoints = {"A":4,"B":3,"C":2,"D":1,"F":0} and ...
A: The average of the academic is determined by dividing the total amount of quality points earned for ...
Q: Write a program in Matlab that can read 33 numbers Then it prints the numbers that are divisible by ...
A: MATLAB CODE: a=33; disp('Given number is divided by 5' + a); number = 1; while number<=a if mo...
Q: Design a signed n-bit multiplier.
A: Design a signed n-bit multiplier.
Q: arn about the benefits and drawbacks of batch and online data input approaches. A demonstration of s...
A: Intro Compare and contrast the benefits and drawbacks of batch versus online data input methods. The...
Q: Should organizations use software service providers for all their software needs? Why or why not? Wh...
A: answer is
Q: a. Encryption is used when it wished to prevent unauthorized users exploiting or tampering with the ...
A: two techniques used in encryption are-
Q: 2. In the following graph (Write code in C) F A E D H J I (i) Traverse using Depth First Search algo...
A: The Answer is
Q: As part of your introduction to engineering class's term project, make a PowerPoint presentation wit...
A: Given: If your introduction to engineering class includes a term project, create a PowerPoint presen...
Q: Assume a company's authentication system is Kerberos. What happens if the AS (authentication server...
A: Introduction: Kerberos is an authentication protocol that operates across a client/server network. I...
Q: e user to enter the marks of a student in a subject. If the marks entered are greater than 70 then p...
A: Below a C Program that asks the user to enter the marks of a student in a subject. If the marks ent...
Q: Draw the Enhanced Entity–Relationship (EER) model and the relational schema for the case study below...
A: Answer: There are total 6 Entities which are: Entities: branch, supervisor, staff, member, rent, vid...
Q: Find the equivalent Being a life is a sufficient condition for it to ma imnortant.
A: Lets see the solution.
Q: Write a description of the eight most important concepts in computer architecture.
A: EXPLANATION AND ANSWER: The Eight Great Ideas in Computer Architecture are as follows: Design for Mo...
Q: Create a device for the output.
A: Device for generating output: The term "output device" refers to a device that allows the user to se...
Q: (C PROGRAMMING ONLY) 4. Pyramid Schemes by CodeChum Admin They said pyramids were created by alien...
A: Program Approach:- 1. Include header file 2. Create the user-defined function whose name is void gen...
Q: How can I find out which thread models my operating system (Windows 7) uses (one-one, one-many, or m...
A: Introduction : There are four basic thread models : Single Thread Model at the user level: Model fo...
Q: Code a C program of input an x integer and display is divisible by 3 or not
A: #include <stdio.h> int main(){ int x = 0; printf("Enter an integer: "); scanf("%d", &...
Q: reate a sample distributed database in oracle where Applications in multiple sites will use the que...
A: A Distributed Database Management System (DDBMS) manages the distributed database and provides the d...
Q: Consider two advantages of employing linear search rather than binary search in your research
A: Introduction : Significant Distinction Binary Search should be used to sort the input data, not Line...
Q: Java Programming - Using a nested loop, create a program that produces the following output: d.) ...
A: First loop: i: 3-1 Nested loop- j: 3-i
Q: The full name of A. I is
A: In computer science, when we use the term A. I A stands for Artificial = Something that is not natur...
Q: List the eight most important design principles for user interfaces. How would you rank them in term...
A: Eight fundamental rules for user interface design, ranked in order of importance.
Q: How to write a function that imports a data from a text file and load it into 5 parallel arrays For...
A: How to write a function that imports a data from a text file and load it into 5 parallel arrays Answ...
Q: Describe a high-level programming language in your own words.
A: High-level programming language:- Many dialects of the importance level are intended for use by huma...
Q: Computer Science A) If the values of c and d are given and the function Euclid(c,d) below is execute...
A: Code of Euclid GCD is in next Step.
Q: 1. What are the different number system? Briefly discuss each.
A: The solution for the above given question is given below:
Q: Draw a single diagram that illustrates how the following concepts are related: • Data • Database • D...
A: Database, data, or information is organized in such a way that allows for quick access and retrieval...
Q: Why is it important to categorized Network based on their size?
A: We are going to understand why we have categorised Network based on their sizes like LAN,MAN,WAN etc...
Q: Which entities in 5G cellular can request a retransmission of received information? Explain the rati...
A: 5G cellular: The fifth generation of cell towers, or 5G, is predicted to be one of the most advanced...
Q: Choose from the list below the expression that corresponds to Bernoulli's Principle (Worksheet 3, Q2...
A: According to me Option C is correct. Kinetic energy+pressure energy=constant
Q: What are the difficulties that a simultaneous multithreading architecture must handle in an operatin...
A: Simultaneous multithreading (SMT) is a method that uses hardware multithreading to improve the overa...
Q: ) Let us assume that we have a program of 100,000 instructions. Each instruction is independent from...
A: Here, we are going to find out the number of CPU cycles needed to execute the program. In pipeline p...
Q: Using SQL, develop and execute the following queries:
A: 1. select sname,sid from student where gpa>2.5 AND gpa<=3.5; 2. select s.sname,c.cname from ...
Q: Draw & Describe WIMAX, 1G to 5G, Leo,Meo,Geo & draw 16.1,2,6.
A: WiMAX: It stands for Worldwide Interoperability for Microwave Access (WiMAX) based on IEEE 802.16 se...
Q: 1. What do the abbreviations CPU and RAM stand for? 2. Is the RAM a component of the CPU? If yes, wh...
A: Introduction: The Central Processing Unit is abbreviated as CPU. Random Access Memory (RAM) is a kin...
Q: Consider the system of linear equations = x. In the following, let A denote the coefficient matrix i...
A:
Q: Explain concurrency and then discuss four design and management considerations that arise as a resul...
A: Concurrency: Concurrency means execution of multiple processes at same time. The running processess ...
Q: ation may be inputted directly into the system, saving time by eliminating the need for an intermedi...
A: Lets see the solution.
Q: Explain how the facts, dimensions, and characteristics are used in the star schema to make it more e...
A: Star schema is the major schema among the data store schema and it is least difficult. This schema i...
Q: Distinguish between User-visible registers and Control and status registers in a omputer system; and...
A: Introduction: Distinguish between User-visible registers and Control and status registers in a omput...
Q: gnetic disk.
A: given - Create a definition for magnetic disk.
Q: Problem 2. Show that the code given by the table below is not uniquely decodable Symbol A Encoding 0...
A: The encoding can be defined as the process of changing data into a specific format with the help of ...
Q: Create a C++ program that will check if the string or group of text is a palindrome or not. For exa...
A: PROGRAM EXPLANATION Include the header file. Define the main function. Take a string as input from ...
Q: Add a JTextField and a JTextArea to the frame. Initialize the field to an empty string and the text ...
A: Add a JTextField and a JTextArea to the frame. Initialize the field to an empty string and the text ...
Q: how to design a KMS system in any organization so that employees can utilize it but not rely on it
A: Knowledge management system: Knowledge management system deals with the storage and administration ...
Q: System software should be defined.
A: Computer software is classified into two broad categories: system software and application programme...
Q: Write a program that displays the employees Ids together with their first and last names. Use two cl...
A: Note:-As per policy, we are entitled to answer the first question only. 2). Program Approach:- 1. Cr...
Q: Given a positive integer n, the following rules will always create a sequence that ends with 1, call...
A: 1)Read the n value using int(input()) function 2)print n value 3)repeat while until n!=1 4) chec...
Q: Write a Python function that returns the position of the element in a vector of numbers nearest the ...
A: To implement vectorMeanPos(), list are used. For finding position of element in a vector of number n...
Q: What is the procedure for encrypting a file in S3?
A: Server-side encryption is data encryption at rest—that is, Amazon S3 encrypts your data as it upload...
Step by step
Solved in 2 steps with 1 images

- Perform the following tasks: a) Write the command to install ssh on Ubuntu. Say you want to login to a remote server named cent07 having an IP address 192.168.2.13, what is the ssh command to use? To copy files between hosts on a network? Which command is needed? Give the appropriate example. How to start/stop/restart SSH service on Ubuntu. LinuxMCQ: Which of the following statement is TRUE? InetAddress is used by other network classes like Socket and ServerSocket to identify hosts. There are public InetAddress() constructors. Using InetAddress, arbitrary addresses may be created. InetAddress class represents as Port address.On a basic Linux server following services are required Assign a dynamic IP address to a client on interface eth0 Find out the path of the packet to the server on (172.16.10.19), put your system in promiscuous mode. Apply forsetgid and sticky permissions on /home/Ali/programming Rename file present on Desktop from “file.txt” to “newfile.txt” Find out the number of IP addresses used by google.com Display all user accounts and groups in a Ubuntu system Display all files in /opt/ starting with s and have a .txt extension.
- Execute the following commands in Linux and write their output1. ping :This command is used to test connectivity between two nodes. Ping use ICMP (Internet Control Message Protocol) to communicate to other devices. You can ping host name or ip address using below command.Example: ping www.google.com$ping <server-ip-address>Output:$ping localhostOutput:$ping <other-ip-in-network>Output: 2. hostnameGives the host name of the computer they are logged into. To set the hostname permanently use /etc/sysconfig/network file.$hostnameOutput : 3. traceroute traceroute is a network troubleshooting utility which shows number of hops taken to reach destination also determine packets traveling path $traceroute ip-addressOutput 4. netstatNetstat (Network Statistic) command displays interfaces, connection information, routing table information etc. $netstatOutput : Execute it with the following options and write the output:netstat –t netstat –s –t netstat -i 5. ifconfigifconfig is used for…Step 1: Write a script to find and print your local IP address Use the following code: import socket hostname = socket.gethostname() local_ip = socket.gethostbyname(hostname) print(local_ip) Step 2: Write a script to find and print your OS platform and release (for example, "Windows version 10") Use the following code: import platform print(platform.system ()) print(platform.release ()) Step 3: Write a script to find and print a "ping sweep"? Use the following code: import os my_ip="192.168.10.103" # sub your ip address os.system('ping -n 4 {}'.format(my_ip)) Step 4: Write a script to find and print current day and time import time now = time.localtime() print(time.strftime("%m/%d/%Y %I:%M:%S %p", now)) Extra Credit: Add code to Step#4 which prints a greeting, either "good morning", "good afternoon", "or good evening", depending on the current time.In this Open-ended lab, you are supposed to develop one client and two servers. The client registers(sets username and password) itself on server1. Server1 passes this information to Server2. Nowclient can login to Server2 and perform a full-duplex chat. Note: Only username and passwordcombination set at Server1 can be used for login at Server2. 1) Create Login Information at Server12) Communicate Login Information at Server23) Login to Server2 using the login information created at step (task) 1.4) Perform a full-duplex chat with Server25) Enable this task for multiple logins/multiple clients
- You have successfully configured Windows Server 2019 as a VPN server using SSTP tunnel type. You allowed another user to dial-in to the server. The user reported that there wasn't any ask for credentials and they were connected automatically with the current user account. How can you explain this behaviour? The VPN profile is has“UseWinlogonCredential” parameter enabled. The admin added machine certificate on the client computer. The admin added user certificate on the client computer. The admin enabled VPN roaming profile on the client computer.Write a PHP script that could be used to connect to MYSQL database named gctudb running on a web server with IP address "192.168.10.100". Assume the user name is nuksoft and the password is makadcode. Remember to close your connection explicitly.Which of the following is recommended practice regarding the three versions of SMB. Leave all three versions of SMB on for backward compatibility Do not use SMB 3 because it is incompatible with non-MIcrosoft servers NFS is preferred over SMB in Microsoft environments Disable SMB 1 and 2 because they have security vulnerabilities (True/False) The Microsoft DNS server concept of Traffic Management provides for clients to resolve DNS queries to the nearest DNS server to the client.
- On servers with Linux operating system, access logs are kept under which of the following directories by default?A) /var/log/B) /var/log/auth/C)/log/D)/log/auth/ Which of the following would an attacker prefer to run operating system-level code with MSSQL?A) MSSQL cannot run code at the operating system level.B) MSSQL agentC) xp_cmdshellD) There are no options. As a network administrator, you want to reduce the attack surface on your systems. Which of the following helps?A) Creating shared folderB) Make sure that only the necessary services are activeC) To record access activitiesD) monitor network traffic Which of the following products can an institution prefer to use if its antivirus software is up-to-date on the computers in its network?A) FirewallB) DLPC) Web ProxyD) NAC When John enters the mobile banking app on his smartphone, he sees his account balance is decreasing. What would it be better for John to do first to fix this situation?A) Closing and reopening the mobile…1. Which of the following tools belong to the SMTP Analysis category in Kali Linux? nbtscan enum4linux swaks smbmap 2. True or False - You can perform a scan without using the ping command by executing the following: nmap -sn 192.168.0.0/24 True FalseWhich of the following is the most likely cause for missing resource records in a secondary zone? Group of answer choices Zone transfer issues An invalid entry in the DNS cache Zones that allow dynamic updates Manual DNS cache flushing

