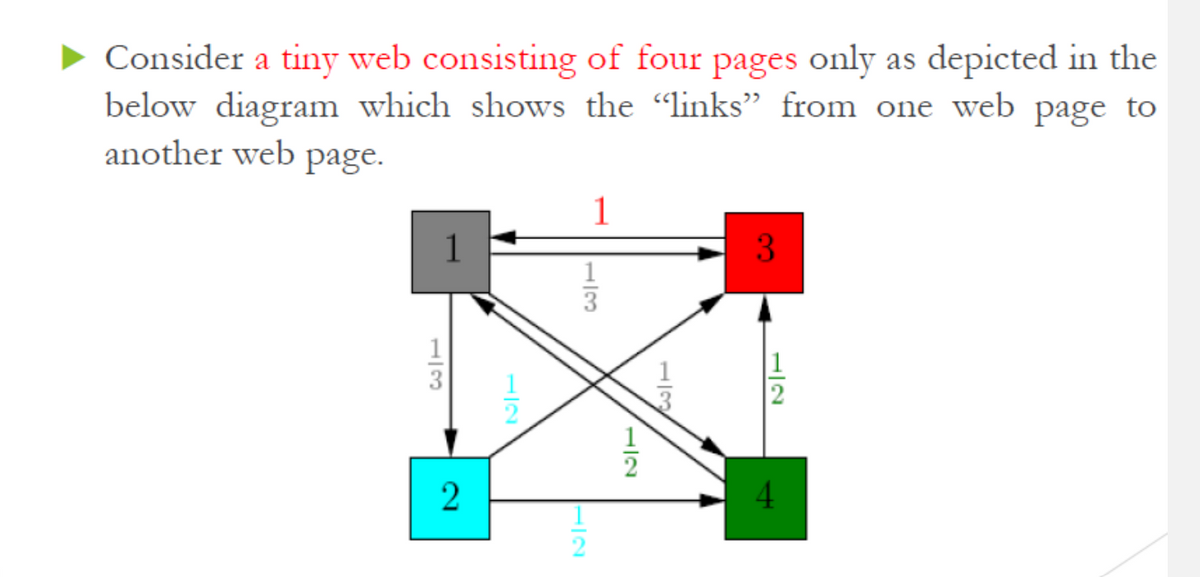
Consider a tiny web consisting of four pages only as depicted in the below diagram which shows the "links" from one web page to another web page. 1 1 3 4 1/2
Q: Is it because lists and sets are mutabl
A: nearly any type of value can be used as a dictionary key in Python. You can even use built-in items ...
Q: Why should we use a linker? Group of answer choices A. The linker can help you find errors in your p...
A: A linker is a program that takes one or more object files generated by a compiler and combines them ...
Q: What is an Internet of Things (IoT) and when may it be useful?
A: IOT is very very useful and widely spread domain across the world and computer industry . As we alr...
Q: Please don't use replace(inbuilt method). Th about the words list. Write a python program to remove ...
A: Code: print("Enter the String: ")text = input() print("Enter a Word to Delete: ")word = input() text...
Q: I can do the following transformation indicated by the arrow below using y rotation translation refl...
A: Please refer below for your reference Rotation is the process of changing the angle of the object wi...
Q: Write a complete C program that analyse the statistics of 5 YouTubers' debut video. The program shou...
A: Introduction Write a complete C program that analyse the statistics of 5 YouTubers’ debut video. T...
Q: PROVIDE PYTHON CODE: Use zero-through forth order Taylor series expansion to predict f(2.5) for ...
A: I have answer this question in step 2.
Q: Could you explain to me how the calculations are done using this code!? Sample output is hyp=5, oppo...
A: Cosine,sin,sin inverse,tan inverse formulas are used in the above code Inbuilt maths functions are t...
Q: Show the output of the following code: public class Test { public static void main(String[] args) { ...
A: As per the given question , below is the Output
Q: What are the claimed benefits of a comprehensive 5G infrastructure, and how do they differ from a 4G...
A: Introduction: The fifth-generation cellular technology, known as 5G, was implemented in 2019.
Q: Compute the selector sets. Make a table. For each of production A a: give the first set of o; if a 6...
A: Here we find all first and follow and also mention that is LL1 or not? =============================...
Q: 2- Convert NFA to DFA for following NFA Convert this NFA to a DFA: 0.1
A: Below is the answer to above question. I hope this will meet your requirements.
Q: Write a Python application that accepts a string from the user and checks it against the list below ...
A: python programming: The Python developed by Python language software. Python Is an High-Level progra...
Q: Which SQL function below puts data into programmer-defined categories? NTILE() statements CASE () st...
A: - We need to select the SQL function which puts data into programmer defined categories. - The opt...
Q: Please don't use replace(inbuilt method). Think about the words list. Write a python program to remo...
A: Required:- Please don't use replace(inbuilt method). Think about the words list. Write a python prog...
Q: al intelligence application in details with examples Appliction of Artif
A: Artificial intelligence application in detail
Q: Subject: computer organization Title:12th Generation Intel Core i9 Processors. Requirements: 1-inro...
A: Processor: Processor is the electrical circuitry that executes a computer program's instructions. Th...
Q: A neural network of 2 convolutional layers each with 16 filters, kernel size = 2, stride = 1, and va...
A: A neural network is a network made up of neurons and perceptron’s. They have layers of three types n...
Q: Why would you want to put two power supply in a server that is mission-critical?
A: Why would you want to put two power supply in a server that is mission-critical?
Q: What intangible advantages may a company get from the creation of an IS?
A: Introduction: A formal, sociotechnical, organizational system designed to gather, process, store, an...
Q: write a script that will format the result of x = 5410 * 5; y = x/2 into a bank format.
A: Code: x=5^10*5;y=x/2;bankText=cur2str(y,2) Note: cur2str(Value,Digits) returns the given value, ro...
Q: What exactly are smart pointers? What function do they serve?
A: Introduction: A Smart Pointer is a pointer wrapper class that has operators like * and -> overloa...
Q: Make an algorithm and a flowchart that will output the Fibonacci series up to a given number. Use 10...
A: Step 1: Start Step 2: Declare variable x, y, sum, n, iStep 3: Initialize variable x=0, y=1 and i=2 ...
Q: Q: Draw the tree for the following sequence of keys using postorder traversing. D,H,E,F,B,I,J,G,C,A ...
A: for unique binary tree, we need : (1) inorder + postorder OR (2) inorder + preorder NOTE...
Q: Give a counterexample to the following claim and justify it: Claim: If a directed graph G contain...
A:
Q: IL State and describe different components of grammar that need to be checked for a formal communica...
A:
Q: • From the employee database below give the answers for all following questions: Employee(person_nam...
A: According to our guidelines we solve only first three questions: ================================== ...
Q: Write a python code (i) code to interface A0 of NodeMCU with MQ-02. (ii) Initialisation steps for ...
A: # import module import os # scan available Wifi networks os.system('cmd /c "netsh wlan show networks...
Q: Use Common Table Expressions (CTE) to write a query that displays the sum of all purchase orders and...
A: Common Table Expression (CTE) Common Table Expression is nothing but a temporary result set. We can ...
Q: The process provides interaction between users and designers, between users and evolving tools, and...
A: Designers should ask users: Is the product satisfactory, or does it require redesign or rework?Was u...
Q: Consider the main memory with capacity of 3 frames assume that the page of process are referred in t...
A: We are given page references and capacity of main memory frame as 3. We will find out which algorith...
Q: 9.A. A transmitter and receiver packaged together is called a/an A. transducer. B. transceiver. C. r...
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any ...
Q: Question 5 What is the size of op-s(R)? Tuples Blocks: Question 6 What is the size of oc-30 AND D-sS...
A: It is defined as a group of one or more contiguous chars ("bytes" - see note) of (real or virtual) m...
Q: When are DML changes made permanent in database tables?
A: Data manipulation language statements add, change and delete Oracle Database table data.
Q: 1) Prompts thc user to cnicr from the keyboard two numbers of type float for variables a and b. 2) C...
A:
Q: How l can open files txt in my computer
A: We can open txt file in Microsoft wordPad or Microsoft Notepad. To open the file first click on wind...
Q: c++ Create a class Employee that shall have multiple attributes i.e., name, salary, experience, des...
A: I have Explained the code in comments of the code: 1. create a class with necessary variables 2. cre...
Q: Create an algorithm and a flowchart that will output all the prime numbers between 2 numbers. Use th...
A: Algorithm for Prime Number between two number i.e. Prime number are those number which has only two...
Q: the Root Bridge is elected in Spanning Tree Protocol. b) Explain how the root port (RP) is selecte...
A: Unnecessary links are used to provide a backup copy where one link goes down but the Inactive link c...
Q: What are the prerequisites for using Conventional Encryption securely?
A: Introduction: Conventional encryption entails converting plaintext messages into ciphertext messages...
Q: how do you undone concatenation. for example lets say i have the following encryption algorithm: E...
A: assuming that the limit is based on the size of allocated memory, concatenation causes undefined beh...
Q: In Python I want the user input to only accept the values 2, 7, 11. How can I achieve this? If the u...
A: In given program we have to accept only integer 2, ,7, 11 So in this program, I accept integer numbe...
Q: Consider a channel with a 1 MHz capacity and an SNR of 63. a. What is the upper limit to the data ra...
A: Given :- Consider a channel with a 1 MHz capacity and an SNR of 63.a. What is the upper limit to the...
Q: Which IP addressing technique subnets a subnet to make smaller subnets?
A: INTRODUCTION: The internet protocol address (IP address) is a numerical identifier that is connecte...
Q: Create a java program to compute the area and perimeter of a rectangle given the length and width (i...
A: Java is one of the languages, which is considerably used in many sectors of Computer. In older time...
Q: Explain the Software Life Cycle using the CSc101 lecture note by Walter Savitchas a basis. Enumerate...
A: The software life cycle contains all phases of a software product's development, implementation, and...
Q: Question 23 How many subnets will you get if the original IPV6 prefix is /52 and the new prefix id /...
A: Answer the above questions are as follows:
Q: Prove that the language L = {{M,N): M, N are TMs such that (M) E L(N) iff (N) E L(M)} is undecidable...
A: The language L = {(M, N): M, N are TMs such that (M) ε L(N) iff (N) ε L(M)} is undecidable. M is in...
Q: You are a software developer for a large online retailing site with a cloud-based IT infrastructure ...
A: Let's see the solution in the next steps
Step by step
Solved in 2 steps

- Consider the link structure of 6 websites in the diagram attached d) Compute the PageRank scores for two iterations (the initial values are 1/6). e) What is the adjacency matrix, L, used in the HITS algorithm f) Compute the authority and hub scores for one iteration (the initial values are1’s).Draw a block diagram using Word, Draw.io, or other drawing tool, that illustrates how HTTP protocol, the client-side web pages with HTML forms, and server-side code are all used together to build powerful business applications.In your own words, explain as follows: a.) What are static and dynamic web pages? b.) How a web server processes a dynamic web page?
- Can a definitive differentiation be established between the notions of "Internet" and "World Wide Web" (WWW)?The Internet as we know it has undergone a radical transformation as a result of wireless communications. Internet use has evolved dramatically during the last several years. As an example, give us a scenario.In this paper, we will use real-world examples to discuss the key distinctions between a web server and a web client.
- How does the Hypertext Transfer Protocol (HTTP) operate in network applications? Is there anything else absolutely necessary for a Web service?Q1: Draw a diagram showing the HTTP protocol stack associated with web browsing. Include in your diagram a stack of web client, name server and a web server. Also include the directions of HTTP request/response messages and DNS query response messages.1. What makes HTTP an example of a protocol but not HTML?

