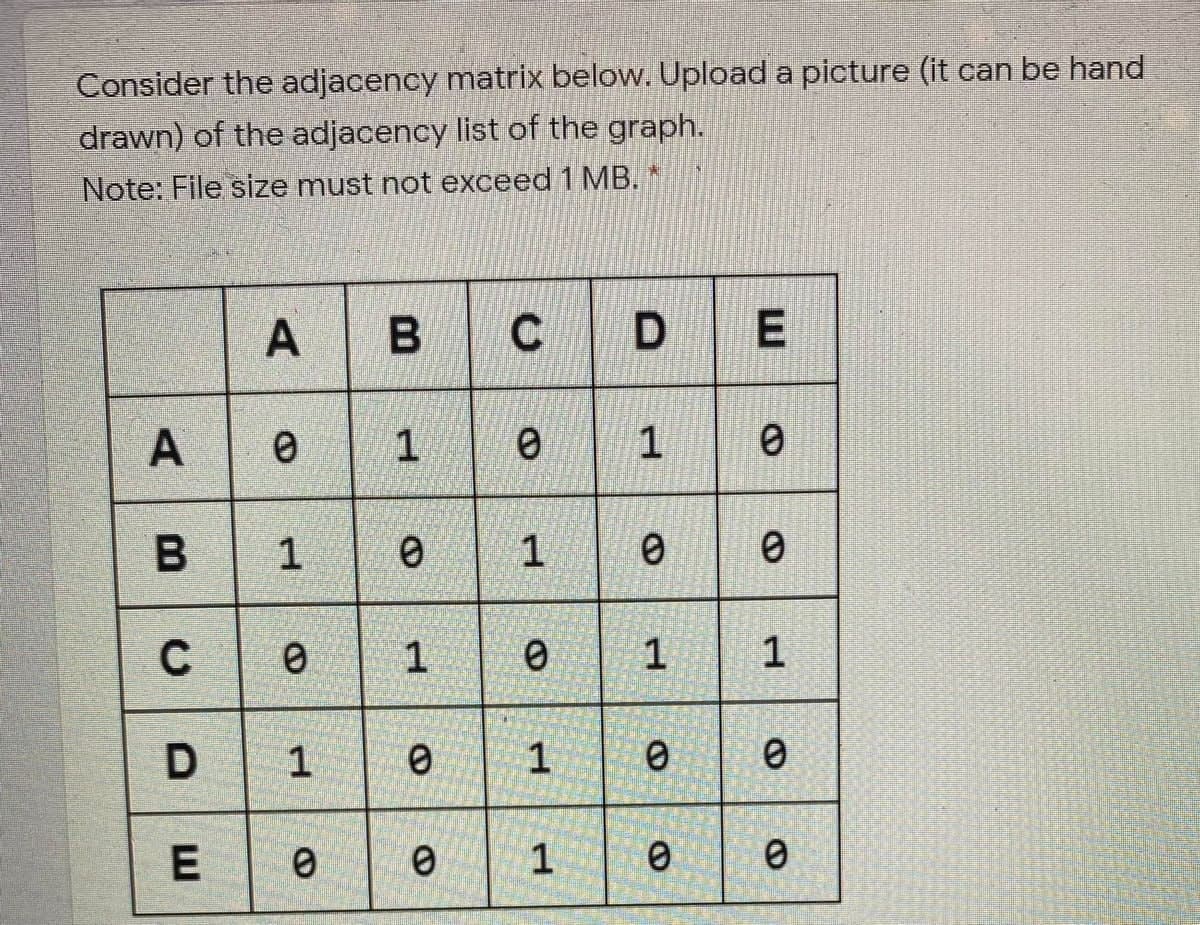
Consider the adjacency matrix below. Upload a picture (it can be hand drawn) of the adjacency list of the graph. Note: File size must not exceed 1 MB. A B C D E A 0 1 0 1 0 B 1 0 1 0 0 C 0 1 0 1 1 DE 1 0 1 0 0 0 0 1 0 0
Q: Despite the OSI reference model's seven, there may be more. Why use less layers if we can? Are fewer…
A: One reason we might try to use fewer layers is to simplify network design and implementation, which…
Q: A FIQ interrupt method must start at the specified offset in the Interrupt Vector Table in order to…
A: => FIQ (Fast Interrupt Request) is a type of interrupt in some ARM-based microprocessors…
Q: Write an 8086 assembly program to will take in two strings from the user as an input and concatenate…
A: An assembly program is a low-level programming language that uses mnemonic codes to represent…
Q: It is preferable to use a computer that has logical partitions in addition to physical ones. Several…
A: Logical partitions provide a layer of data protection by isolating the files from each other. If one…
Q: 1. Splitting your worksheet will undo the _______ ______ command. 2. ______ _______ can be helpful…
A: What is data: Data refers to information, facts, or statistics that are stored in a digital format,…
Q: Any computer setup from the past, present, or future may be seen here.
A: The development of networking in the 1970s led to the development of smaller, cheaper computers used…
Q: types (Lan
A: Virtualization is the process of creating a virtual representation of something, such as a computer…
Q: Binary information stored in the main memory might be converted into coded hole patterns on a paper…
A: Process of converting binary information stored in the main memory into coded hole patterns on a…
Q: A modem is an accessory used to link a phone to a modem. Why would you need this thing?
A: In the modern era of technology and connectivity, it is crucial to understand the devices that play…
Q: Create a skip list and search for keys that are available or unavailable in the list using a…
A: We have to create a python program for skip list and search for keys that are available or…
Q: Consider the challenges you'll face when building the framework, then examine each solution's…
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!!
Q: On an ordered list, use the binary search and Fibonacci search algorithms. Search for the components…
A: To use the binary search and Fibonacci search algorithms, we first need to sort the list L in…
Q: A data structure known as a drop-out stack functions exactly like a stack, with the exception that…
A: A drop-out stack is a data structure that works similarly to a regular stack, with the exception…
Q: Multiple packets may be transmitted over a host-to-host connection. Please outline the actions…
A: In computer networking, it is common to transmit data over a host-to-host connection in the form of…
Q: 4. Consider the following mutual authentication protocol, where KAB is a shared symmetric key. "I'm…
A: Let's first understand what is the scenario here and then we can think of the attacks we can made on…
Q: Cyber insurance is a field that looks like it will decrease in the future Group of answer choices…
A: Here is your solution -
Q: q2- What is the minimum number of bits in a PN sequence if we use Frequency Hopping Spread Spectrum…
A: Frequency Hopping Spread Spectrum (FHSS) is a wireless communication protocol that spreads the…
Q: Explain why you like four continuous event simulation features.
A: Explain why you like four continuous event simulation features.
Q: When comparing the Iterative Waterfall Model to the Traditional Waterfall Model, the question of…
A: Introduction The decision on which model is better, the Iterative Waterfall Model or the Traditional…
Q: Is there more than one step involved in making a website? Explain why you think each step is…
A: In today's digital age, web applications have become an essential part of our daily lives. They are…
Q: How should we approach the myriad ethical issues raised by widespread use of digital technologies…
A: The widespread use of digital technologies such as computers, information networks, and the internet…
Q: Justify the rationale of C# Windows Forms delivering cross-platform desktop applications for other…
A: Using C# Windows Forms to produce cross-platform desktop apps for other platforms gives programmers…
Q: If your disc uses soft segments, the first sector may be included in the Index. Explain?
A: In computer science, a disc is a storage device used to store digital information. It is divided…
Q: What separates public cloud services from private? Why would you advocate another option?
A: Cloud computing has become an increasingly popular option for businesses and individuals looking to…
Q: import java.util.LinkedList; public class IntTree { private Node root; private static…
A: Define a helper function sizeOddHelper that takes a node as input and returns the number of nodes…
Q: class Student: def __init__(self, id, fn, ln, dob, m='undefined'): self.id = id…
A: Define a Student class with properties like ID, first name, last name, date of birth, and major.…
Q: Which VLAN is intended to provide administrative access to network devices?
A: The Answer and detailed explanation are provided below. Please check.
Q: Why would organizations not share data about attacks? A)to engage in risk avoidance B) to establish…
A: A security system is a set of measures and mechanisms designed to protect people, assets, and…
Q: Write a C program containing a recursive function that will get the whole number quotient result of…
A: Step 1: StartStep 2: Declare variables n, m, and quotientStep 3: Read value of n and mStep 4: Call…
Q: Analyse the impact Web Engineering has had on various markets. Think about how much effort it takes…
A: Web engineering is a branch of software engineering that deals with the development, design,…
Q: In C# write a program to implement the logical operators such as not, xor, boolean and, boolean NOT…
A: In this question we have to write a C# program to implement the logical operators such as not, xor,…
Q: Write a program that will undertake a range search of all elements lying within limits a, b along a…
A: To implement a range search in a k-d tree, we can follow the following steps: begin at the tree's…
Q: When it comes to email security, do network administrators have any moral or ethical considerations?
A: We have to explain that, when it comes to email security, do network administrators have any moral…
Q: Sentiment analysis accuracy? How do you usually do this?
A: Sentiment analysis accuracy depends on the techniques and tools used,and the quality of training…
Q: Big O notation indicates how hard an algorithm may have to work to solve a problem. In relation to…
A: Big O notation is a way of describing the performance of an algorithm or the growth rate of a…
Q: 4 Write a program that reads the student information from a tab separated values (tsv) file. The…
A: 1. Create a file object and open the file.2. Initialize mid_marks1, mid_marks2, final and…
Q: You are writing some software that will take information from your website and store it in a…
A: Protecting confidential information is of paramount importance to any organization. Safeguarding…
Q: Discuss the four main continuous event simulation insights from your reading.
A: Continuous event simulation is a powerful tool used to model and analyze complex systems. Through…
Q: How to find the minimum value, maximum value, and average while the text file in the c# program and…
A: To find the minimum value, maximum value, and average from a text file in a C# program, you can use…
Q: How does an email appear in your head? What's the best way to get an email across? Take notes on…
A: In today's digitally connected world, email has emerged as a popular and essential mode of…
Q: Focus on: Basic list operations, methods, use of functions, and good programming style Part 1.…
A: Part 1 ALGORITHM: Step 1: Import the random module Step 2: The function 'user_input' is defined, it…
Q: Explain what a Web app consists of and how information moves through it.
A: A web application (web app) is an application program that is stored on a remote server and…
Q: Fill in the blank; In Java, recursion can be used to solve different problems such as factorial of…
A: Java: Java is a high level, general purpose,class based object oriented programming language. It is…
Q: Learn about several types of virtualization and its implications on language, OS, and hardware.
A: Virtualization is the process of creating a virtual version of something, such as a…
Q: Algorithm to illustrates the procedure for Fibonacci search. Here n, the number of data elements is…
A: The Fibonacci search algorithm is a search algorithm that works on sorted arrays. The algorithm…
Q: Intelligent modems are able to initiate phone calls as well as receive and return calls. Who or what…
A: Intelligent modems are communication devices that can transmit and receive data over a telephone…
Q: Calculate AS° for NH3(g) + HCI(g) → NH₂Cl(s).
A: In this question we have to calculate standard entropy change (ΔS°) for the given reaction Let's…
Q: /** * Returns the value associated with the given key in this symbol table. * Takes…
A: The question provides a code snippet for a method called get() in a symbol table implementation, and…
Q: Differentiate the two fields. Please compare and contrast project management with software…
A: Project Management: It is the utilization of information, abilities, instruments, and procedures to…
Q: a display or search ad campaign D) ensure the emails bypass spam f
A: Coordinating a successful email campaign is a complex process that involves several steps, from…
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 2 images

- Assume we wish to resize an existing hash table because the current hash table is becoming too small for the application. Without writing code briefly describe the process of resizing a hash table by "copying" the old data to the new hash table. What is the expected complexity of your process using Big-O notation. Justify your complexity measure. An example of a hash table before resizing is given.Write a Python script that implements the CHF (the Casual Hash Function.) The input data should be split into blocks of 32 bits. If the last block is smaller than 32 bits, the remaining bits should be filled with 1 followed by as many zeros as required. A and B are 2 buffers with specific values (see below). Each block in the message should be combined as shown in the image below. All resulting blocks (i.e. FBI) should be combined with "&" to produce the digest. The size of the digest is 64 bits. Calculate the digest for the string: "Alright, but apart from the sanitation, the medicine, education, wine, public order, irrigation, roads, the fresh-water system, and public health, what have the Romans ever done for us?" steps on how are in the attached picturesWrite a Python script that implements the CHF (the Casual Hash Function.) The input data should be split into blocks of 32 bits. If the last block is smaller than 32 bits, the remaining bits should be filled with 1 followed by as many zeros as required. A and B are 2 buffers with specific values (see below). Each block in the message should be combined as shown in the image below. All resulting blocks (i.e. FBI) should be combined with "&" to produce the digest. The size of the digest is 64 bits. Calculate the digest for the string: "Alright, but apart from the sanitation, the medicine, education, wine, public order, irrigation, roads, the fresh-water system, and public health, what have the Romans ever done for us?"
- you need to design, analyze, and implement algorithms to read in a sequence of characters from standard input and maintain the characters in a linked list with no duplicates. When you read in a previously unseen character, insert it at the front of the list. When you read in a duplicate character, delete it from the list and reinsert it at the beginning. The program implements the well-known move-to-front strategy which is useful for caching, data compression, and many other applications where items that have been recently accessed are more likely to be re-accessed. Requirements: The program should read a sequence of characters. The program should insert unseen character at the front of the list. The program should check if the character is not in the list to be inserted at the front of the list. The program should delete a duplicate character and delete it from the list and insert it at the beginning of the list. The program should check if the character is already in the list and…Suppose we are building a B-Tree. Pages are 4008 bytes. A key value takes 8 bytes, and a pointer to a tree node or a record takes 8 bytes. a) What is the maximum number of keys in each node? b) Calculate the maximum number of pages N, which can be indexed with anindex file with height, h=2 and m keys (m is calculated in part a)? c) How many I/O operations are required for searching through N pages using a sorted file (N is calculated in part b)?.implement a python code that is a filesystem using a tree data structure. If the specific path does not exist, disregard that file using the code template given in this pastebin link: https://pastebin.com/NuPaPAFT The input format is as follows, the first line is the name of the root directory second line is the number of subdirectories that follows For the next files that follows, the format is: Filename-root node,next path,next path,... Please note the output format. Sample input 1: C12Users-CWindows-CProgramFiles-CAdobe-C,ProgramFilesSteam-C,ProgramFilesferdie-C,Usersjohn-C,Usersguest-C,UsersFirmware-C,WindowsSystem-C,WindowsDocuments-C,Users,ferdieDownloads-C,Users,ferdie Output: C Users ferdie Documents Downloads john guest Windows Firmware System ProgramFiles Adobe Steam
- Store a dictionary of a limited set of words as a hash table. Implement a spell check program that, given an input text file, will check for the spelling using the hash table-based dictionary and in the case of misspelled words will correct the same.Suppose you have a hash table with seven entries (indexed 0 through 6). This table uses open addressing with the hash function that maps each letter to its alphabet code (a = A = 0, etc.) modulo 7. Rehashing is accomplished using linear-probing with a jump of 1. Describe the state of the table after each of the letters D, a, d, H, a, and h are added to the table.Can you please help update this? //A6Utilities.java import java.io.IOException;import java.nio.file.Files;import java.nio.file.Paths;import java.security.SecureRandom;import java.util.List;import java.util.TreeMap;import java.util.function.Function;import java.util.stream.Collectors;public class A6Utilities {/*** Returns the corresponding letter grade. Don't modify this method, simply use it when converting single* grades to their equivalent letter grade** @param grade the integer grade to convert* @return the letter grade equivalent to the integer grade*/private static char letterGrade(final int grade) {if (grade < 0) return '?';else if (grade < 60) return 'F';else if (grade < 70) return 'D';else if (grade < 80) return 'C';else if (grade < 90) return 'B';else if (grade <= 100) return 'A';else return '?';}/*** The method uses Java Streams only. Don't use any looping structures, conditional statements are OK (IF, TERNARY, SWITCH)* <p>* Generates a list of secure…
- Implement a blog server in C 1. Implement get of all posts (GET /posts), and individual post (GET /post/1) 2. Implement creation of post (POST /posts). Allow the user to enter their name, but check that they are a valid user in db. Do error checking! The user should not specify the post id; that should come from the database. 3. Write three html files to test this; serve them with the blog server: index.html shows the list of posts with a link to each. post.html shows a post. publish.html allows the creation of a new post. Link these together as a user would expect!In Python, implement a hashing table data structure of size 20, which can cope with collisions. Thus, you must implement the closed collision system in its three modes: Linear scanQuadratic scanDouble hashing scan. For halt use halt(k)= (k mod (m - 1)) + 1, where m is the size of the table. The data to be managed are students from a certain university who have a 5-digit registration number and it is unique. In addition, the student has a name, age and address. Create a .txt file with 10 students (one for each line) and have them loaded into your program. Build a menu of options where you can: - Find a student and print his data if found and position in the table. Otherwise print a "Not Found" message.In Python, implement a hashing table data structure of size 20, which can cope with collisions. Thus, you must implement the closed collision system in its three modes: Linear scanQuadratic scanDouble hashing scan. For halt use halt(k)= (k mod (m - 1)) + 1, where m is the size of the table. The data to be managed are students from a certain university who have a 5-digit registration number and it is unique. In addition, the student has a name, age and address. Create a .txt file with 10 students (one for each line) and have them loaded into your program. Build a menu of options where you can: - Enter a new student. For this option, that only allows entering the 5-digit license plate and that random data is automatically generated for the name, age and address. Return the position where it was entered and if it is not possible to enter it, print a message that explains why the entry was not obtained.

