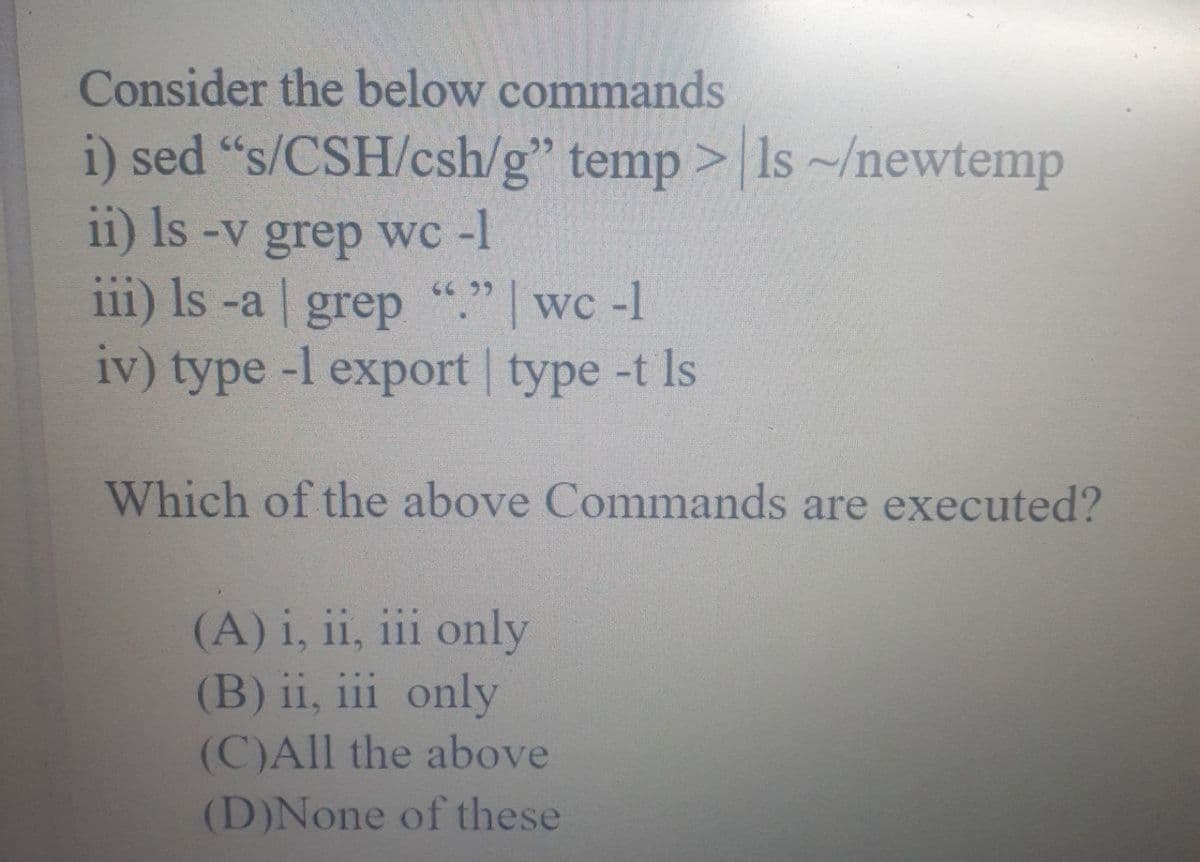
Consider the below commands i) sed "s/CSH/csh/g" temp >|Is ~/newtemp 11) Is -v grep wc -1 111) Is -a grep "." wc -1 6699 iv) type -l export type -t Is
Q: Octal String: 010 110 101 010 101 111 010 111 111 101 011 011 011 011 010 100 1. Hex String: 1. Base...
A: Octal to hex is. 0B557AFEB6D4
Q: You can find out how many seconds have elapsed since Jan 1, 1970 using the time() function. #includ...
A:
Q: Procedure 1. Define a function named procedurel () that will be called from main () function, the fu...
A:
Q: Write 10 user stories for stock trading bot software
A: Lets see the solution in the next steps
Q: public class A { public void funl () ( System.out.println ("Al"); public class B extends A { @Overri...
A: A class is a group of objects which have common properties. Inheritance is an OOP concept in which ...
Q: Indicate the ASCII and EBCDIC code for the following: The letters A, B, C, D, E and the numbers 1, ...
A: Let us see the answer:- ASCII value Number/alphabet ASCII value ...
Q: a) Two-dimensional array of integers named scores with 3 rows and 4 columns was defined by using the...
A: Answer a. Table 1: Elements of scores array 0 x[0][0] 1 x[0][1] 0 ...
Q: Doing a trillion floating point operations in one second is called a .. ...... O petaflop teraflop m...
A: The above question that is given trillion floating point operation in one second is answered below
Q: Suppose a program has runtime proportional to nlogn, where n is the input size. If the program take...
A: Let, runtime for input n be T(n) Given, T(n) ∝ nlog(n) Let the proportionality factor be k. We have,...
Q: Returns the number of times item appears in aList.
A: Python is a popular programming language among developers used for data analysis and predicting mode...
Q: e VIN, make, model, year, color, asking price, number of miles, number of collisions, tire age, and ...
A: ERD for given database: No of entities : 1)SalesPerson entity : Attributes are { salespersonID ,name...
Q: 1. Convert 82ADH to decimal. 2. Convert 11101b to decimal. 3. Convert 2BD4H to decimal.
A: “Since you have asked multiple questions, we will solve the first question for you. If you want an...
Q: (c) Find the sum-of-products expansion of the following Boolean function: f(a,b,c) = a(b+ €) + ab + ...
A:
Q: When to use internal and external javascript code?
A: The answer is
Q: find the simplified circuit
A:
Q: This Access Control Principle states that no single individual should have so many privileges that t...
A: Information security is an intricate, multi-layered discipline based upon numerous essential princip...
Q: Convert the given DFA into Regular Expression notation using Arden's Theorem ob 92 91 q3
A: Regular Expression to DFA- The following are common approaches for converting a DFA towards its re...
Q: help me write these functions for a vending machine
A: Below i have given the program:
Q: Please explain why this code has program output: **********
A: The solution to the given problem is below.
Q: Alice and Bob use the ElGamal scheme with a common prime q= 131 and a primitive root a = 6. Let Bob’...
A: The answer is
Q: Develop a PL/SQL block that would go through all the employees from EMPLOYEES table who work in depa...
A: Solution SELECT * FROM departments where department_id =90; BULK COLLECT Clause for Selecting Multip...
Q: fferentiate a browser from a search engine: Enumerate examples of the following: Browser Search ...
A: I have answered the first two questions. For accessing the internet we make use of browsers. If yo...
Q: C# Language You are tasked with writing a program to process students’ end of semester marks. For e...
A: Solution :- Code is implemented in C++ language. For clear understanding of code, programming commen...
Q: Computer Science Use Assembly programming language to solve the following problems using: • Uses im...
A: ADDRESS MNEMONICS COMMENTS 0400 MOV CX, [0500] CX <- [0500] 0404 MOV AX, 0001 AX <- 0001...
Q: How can I create a flowchart that can identify whether a number is prime or composite without using ...
A: The flow chart is the pictorial representation that gives a chart about the program and the logic be...
Q: I need help creating the printAnimal() method that prints from the menu, I keep getting errors and I...
A: Actually, Java is a high level programming language. And also object oriented .It. Is a platform f...
Q: Procedure 2. - Define a function named procedure2 () that will be called from main () function, the ...
A: #include <stdio.h> void procedure2(int N){ for(int i = 1; i <= N; i++) { for(i...
Q: Try to use the Foreach method on the list and also use the Lambada print statement instead of simple...
A: Required:- Try to use the Foreach method on the list and also use the Lambada print statement instea...
Q: For the word count example, for the input of the Map function, keys are document IDs and values are...
A: For the word count example, for the input of the Map function, keys are document IDs and values are ...
Q: onnecting more peripherals to a computer is made possible by the .
A: CPU is the brain of the system.
Q: Write a small snippet of Nios II assembly code to implement the C code below. Assume that all of the...
A: Here we are asked to convert the given program in C to Nios II assembly language. As we know C is a ...
Q: Write two address instructions to evaluate first six terms of Fibonacci sequence. Compare with zero ...
A: The computer works on the instructions provided to it. The instructions provided to the computer con...
Q: What is the runtime (using big-O notation) of a search operation in a balanced binary search tree wi...
A: First lets understand what balanced binary search tree mean: in balanced binary search tree, at ever...
Q: Computer Science c++ Design an ID recognizer (a simple lexical analyzer) that reads in the string: ...
A: Lexical Analysis: Read the source code and generate a token list ("linear" analysis) We...
Q: The ISA of a processor has four classes of instructions: arithmetic, store, load and branch with CPI...
A: Complementary of 2: Half duplicate of value inside the registry R2 is collected throughout this mini...
Q: #include #include int main(){ int i; printf("before fork, my pid is %d\n" , getpid()); ...
A: The Answer is in Below Steps
Q: -ampground reservations, part 6: Filter campsites by multiple criteria his is the last challenge. Yo...
A: Answer:- 1. It is hard to reserve a spot system work depends on a few attributes of the restaurant a...
Q: In java
A: Java code is giving below-
Q: 'Rabenstein code was used to send a message with 4 information bits, you receive 100110001, if you c...
A: The answer is
Q: PHP program to create Login and Logout using sessions.
A: The Answer is in below Steps
Q: email validation, use regular expression to check javascript format is @., it needs to follow the f...
A: I give the code in Javascript along with code and output screenshot
Q: Create a program called staffSalary using GUI Java and add a class named Staff that will determine t...
A: The given program is a GUI based JAVA program which determines staff salary calculated based on sev...
Q: Question: Design 8 subnets for a company with the site address 201.75.38.0. What is the network mas...
A: Below is the answer to above questions. I hope this will be helpful for you..
Q: In order to make an informed decision, it's important to compare procedural versus object-oriented p...
A: Procedural and Object-Oriented Programming: Introduction Procedural programming is structured arou...
Q: s writing an after-action report on a security breach that took place in his institute. The attacker...
A: Lets see the solution.
Q: A friend sends an email to your business email address and includes an electronic card (e-card). You...
A: Please find the detailed answer in the following step.
Q: The Google Android operating system has over an 80 percent share of the worldwide smartphone operati...
A: The answer is
Q: Q.1. Implement insertion sort using C++ STL with following constrain and write a program : The inse...
A: Note- As per the Bartley policy we have to attempt only one question. Program Explanation- Insert...
Q: Reduce the following Boolean expressions to the indicated number of literals. (x'y' + z)' + z xy + w...
A:
Q: define Software Licence
A: A software license is a document that outlines the developer's and user's rights in relation to a pi...
Step by step
Solved in 2 steps

- The following code must be written in python for this HW assignment. I will provide a skeleten for the code and you must write some lines of code to satisfy the objective of the prorgram. You will develop a web server that handles one HTTP request at a time. Your web server should acceptand parse the HTTP request, get the requested file from the server’s file system, create an HTTP responsemessage consisting of the requested file preceded by header lines, and then send the response directly tothe client. If the requested file is not present in the server, the server should send an HTTP “404 NotFound” message back to the client. Put an HTML file (e.g., HelloWorld.html) in the same directory that the server is in. Run the serverprogram. Determine the IP address of the host that is running the server (e.g., 128.238.251.26). Fromanother host, open a browser and provide the corresponding URL. For example:http://128.238.251.26:6789/HelloWorld.html‘HelloWorld.html’ is the name of the file you…Modify the program 11-10 from pages 753-755 as follows: 1. To Length class files (Length.h and Length.cpp) add the operator overload for stream insertion (<<) and stream extraction (>>) from page 759. You should not use the modified version of class Length from page 759 because it contains more operator overloads. Instead of typing you can use copy/paste from Length1.h and Length1.cpp respectively. 2. In main() replace the lines 11-16 with appropriate usage of stream extraction overload (>>) to change "first" and "second" objects with values inputted by the end user. 3. In main(), replace the output on lines 21,22 and 25,26 with appropriate usage of stream insertion (<<) operator. The resulting output should be identical with the unmodified version of the program. 11-10: // This program demonstrates the Length class's overloaded // +, -, ==, and < operators. #include <iostream> #include "Length.h" using namespace std; int main() { Length first(0),…modify minishell.c to run who, ls, and date with option. who will show the count of users, ls will list files in long listing format and date will show UTC time. Modify this file so the shell can run commands with options.*/#include <stdio.h>#include <unistd.h>#include <sys/types.h>#include <sys/wait.h>#include <stdlib.h>#include <fcntl.h> int main(int argc, char *argv[]){ char *cmd[] = {"who", "ls", "date"}; int i; while(1){ printf("0=who 1=ls 2=date : "); scanf( "%d", &i ); if(i<0 || i>2) continue; pid_t result= fork(); if(result==0) { /* child */ execlp( cmd[i], cmd[i], (char *)0 ); printf("execlp failed\n"); exit(1); } else if (result >0){ /* parent */ int status; wait(&status); } else{ //handle error } } return 0;}
- #1 A) Write a program to print all alphabets from A to Z. You will be using the JSR putchar command. B) Write a program to print the hexadecimal equivalents of all alphabets from A to Z. You will be using the JSR out2hex command in the previous question instead of JSR putchar.Problem Given the target file f0 and candidate files f1-f20, there is an identical copy of f0 among the files f1-f20. Write a python program to perform the following tasks: · Read in each file and calculate the hex hash values by using SHA3 function with the length of 512 for all the given files f0, f1-f20. · Save the hex hash values of each file as a new line in a .txt file named hash.txt file. · Read hash values from hash.txt and compare them to find the identical copy of f0 among f1-f20. · Write the finding result (the matched file name) back to hash.txt Submission • Name your project fileHash.py and submit both fileHash.py and hash.txt on Blackboard. • The program should be properly documented. • The program should have user friendly Input/Output design • Duplicate work (or obviously similar one) will result in an F grade in the course. Grading 1. Include comments as specified in the course syllabus. (10%) 2. Source code and results. · Correctness (70%) · User-friendliness…/* Filename: logserver.c *//*******************************************************************************************modify this program to log the message from clients to a log file. ******************************************************************************************/#include<stdio.h>#include<sys/ipc.h>#include<sys/shm.h>#include<sys/types.h>#include<string.h>#include<errno.h>#include<stdlib.h> #define BUF_SIZE 1024#define SHM_KEY 0x1234 struct shmseg {int cnt;int new;int complete;char buf[BUF_SIZE];}; int main(int argc, char *argv[]) {int shmid;struct shmseg *shmp;shmid = shmget(SHM_KEY, sizeof(struct shmseg), 0666|IPC_CREAT);if (shmid == -1) {perror("Shared memory");return 1;}// Attach to the segment to get a pointer to it.shmp = shmat(shmid, NULL, 0);if (shmp == (void *) -1) {perror("Shared memory attach");return 1;}/* Transfer blocks of data from shared memory to log file if the message from client set shmp->complete ==1, the we…
- In this final submission, you will build on checkpoint B to load the database and DNA sequence from files. There will be two databases and several sequences that will be available for download below. Example of the database is the file small.txt: name,AGATC,AATG,TATC Alice,2,8,3 Bob,4,1,5 Charlie,3,2,5 Example of the sequence is the file 1.txt: AAGGTAAGTTTAGAATATAAAAGGTGAGTTAAATAGAATAGGTTAAAATTAAAGGAGATCAGATCAGATCAGATCTATCTATCTATCTATCTATCAGAAAAGAGTAAATAGTTAAAGAGTAAGATATTGAATTAATGGAAAATATTGTTGGGGAAAGGAGGGATAGAAGG Implement/modify the following functions: Modify the function readData, which will now take an additional parameter: a string representing the filename containing the database of individuals and their STR counts. It will also return a bool indicating if opening the file was successful or not: bool readData(string filename, vector<string>& nameSTRs, vector<string>& nameIndividuals, vector<vector<int>>& STRcounts) Update the function…IN SCALA PLEASE COULD YOU COMPLETE THE CODE OF FUNCTIONS: get_csv_url, process_ratings, process_movies, groupById, favourites, suggestions and recommendations import io.Source import scala.util._ // (1) Implement the function get_csv_url which takes an url-string // as argument and requests the corresponding file. The two urls // of interest are ratings_url and movies_url, which correspond // to CSV-files. // // The function should ReTurn the CSV-file appropriately broken // up into lines, and the first line should be dropped (that is without // the header of the CSV-file). The result is a list of strings (lines // in the file). def get_csv_url(url: String) : List[String] = ??? val ratings_url = """https://nms.kcl.ac.uk/christian.urban/ratings.csv""" val movies_url = """https://nms.kcl.ac.uk/christian.urban/movies.csv""" // testcases //----------- //: //val movies = get_csv_url(movies_url) //ratings.length // 87313 //movies.length // 9742 // (2) Implement two functions that…Review the following program: import urllib.request, urllib.parse, urllib.error fhand = urllib.request.urlopen('http://data.pr4e.org/romeo.txt') counts = dict() for line in fhand: words = line.decode().split() for word in words: counts[word] = counts.get(word, 0) + 1 print(counts) 3.1 Provide an explanation for EACH line of the following program. 3.2 Run the above program and include a full window screenshot with system time and date in the answer. 3.3 Run the above program with https://www.py4e.com/code3/romeo-full.txt and include a full window screenshot with system time and date in the answer.
- WRITE 2 C FILE In this assignment you are required to follow the Unix domain server and client example done in the classroom. After this point, you need to setup the server in a way that it will process the data sent by the client and send back the processed data. You must read at least two set of data, and send back at least a piece of information. For instance, client might send two numbers and the server will send the summation back. This is only an example, please do something a little more complicated. I do not want to see same operation over and over again in the assignments. You can use scanf and printf with dup2 to obtain numbers. Alternatively, you could read the text and use sscanf and sprintf. You could also perform text based operations. It is up to you. You must perform all error checks.PROGRAM IN PLAIN C PLEASE! Write a void function that will merge the contents of two text files containing chemical elements sorted by atomic number and will produce a sorted file of binary records. The function’s parameters will be three file pointers. Each text file line will contain an integer atomic number followed by the element name, chemical symbol, and atomic weight. Here are two sample lines: 11 Sodium Na 22.99 20 Calcium Ca 40.08 The function can assume that one file does not have two copies of the same element and that the binary output file should have this same property. Hint: When one of the input files is exhausted, do not forget to copy the remaining elements of the other input file to the result file.Hello, I am having an error and cannot figure out how to solve this question. Could someone please assist? Please be advised, I am using PostgreSQL as that is what was used in class. Thus, I must use PLPGSQL Code CREATE OR REPLACE FUNCTION Moreno_03_bankTriggerFunction()RETURNS TRIGGERLANGUAGE PLPGSQLAS$$CREATE TRIGGER Wise_12_bankTriggerAFTER DELETE ON accountFOR EACH ROW EXECUTE PROCEDURE Moreno_15_bankTriggerFunction();











