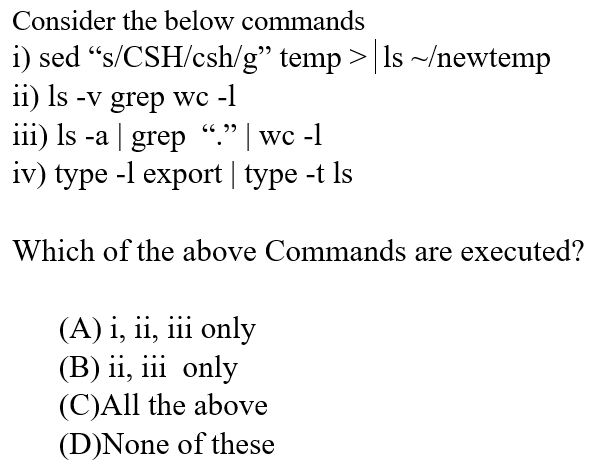
Consider the below commands i) sed “s/CSH/csh/g" temp >|ls ~/newtemp ii) Is -v grep wc -l iii) Is -a | grep “." | wc -1 iv) type -l export | type -t Is לל CG Which of the above Commands are executed? (A) i, ii, iii only (B) ii, iii only (C)All the above (D)None of these
Q: trix X = [1,2,3;4,5,6;7,8,9]. What does the ?command m = max(X) return اخترأحد الخيارات a. m = 6 15…
A: Max() is the function will find out the maximum data from the given matrix.
Q: 14. Which of the following operators does not require an Ivalue as its operand? a. address operator…
A: lvalue means for the given expression the left hand side variable should be defined to store the…
Q: Consider the below commands sed "s/CSH/csh/g" temp> Is ~/newtemp 11) Is -v grep wc -1 66 99 111) Is…
A: Answer :
Q: 4) Calculate 2ªd element of L1=[1,10,19,28] divided by 1* element of L2 = [5,14,23,32]. Use two def…
A: 1) Below is program to calculate divide element of list 1 and 1st element of list 2 with functions…
Q: Answer in C++ only order for Jon to win and be noticed by his favourite streamer Daenerys, he…
A: Coded using C++.
Q: Q12: Given x=[7 61 20-14 3-2 0] what are the commands that will execute the following operations: a.…
A: a. sets the negative values of x to zero. We can use the following comprehensions ,x=[0 if i<0…
Q: _four X please enter your function description here AssertionError: expected [ 0, 0, NaN ] to deeply…
A: It is showing assertion error
Q: Why My function browse () and order() don't work when I choose choice 2 or 6 ??? would you check it…
A: The problem that in the above code we donot have the cin so it will take the input Definition: CIN:…
Q: 1. A website requires a password that is 10 characters long and that contains at least 1 lower…
A: According to the information given:- We have to follow the instruction mentioned above.
Q: 2.2-4 Conditional HTTP GET. What is the purpose of the conditional HTTP GET request message? To…
A: Lets see the solution in the next steps
Q: **PYTHON PROGRAMMING** data = ''' Apr 12, 5:00, S=70% APR 14, 6:30, S=60% #Server restarts…
A: import re data = '''Apr 12, 5:00, S=70%APR 14, 6:30, S=60%#Server restartsApr 14, 6:35,…
Q: You are to write code for the Displaydata.hbs file for the given following route code in the…
A: The below code utilizes 'each' helper with @index variable in the Displaydata.hbs to display the…
Q: Why My function browse () and order() don't work when I choose choice 2 or 6 ??? Thanks #include…
A: 1. browse(): Before choosing case 2, case 1 should be executed for adding an entry so that the…
Q: Consider the below commands i) sed "s/CSH/csh/g" temp >|Is ~/newtemp 11) Is -v grep wc -1 111) Is -a…
A: Some operating systems used need commands to execute the functions unlike the operating system used…
Q: Consider the following functions: fix)=cos³(3x - 2) f2(x)=| 3 1 f3(x)=e 2x Write down Julia commands…
A: Julia commands
Q: Write a python script that will: 1. Load, normalize and concatenate the first 4 days as training…
A: Answer:
Q: WRITE 2 C FILE In this assignment you are required to follow the Unix domain server and client…
A: The dup() system call creates a copy of a file descriptor. It uses the lowest-numbered unused…
Q: Answer in C++ only order for Jon to win and be noticed by his favourite streamer Daenerys, he…
A: Coded using C++ language.
Q: Question 20 What is the output of the following code segment? char news [3] [10] =…
A: Step 1-To give the output of the given program. Following program segment is provided: char…
Q: Euclideat Dis lists z and y c ented by x and ween the corre roject3 tance.py 5 -5 9 6 7 4 <en nt) as…
A: Step 1: Below the Program called distance.py that accepts n (int) as command-line argument, two…
Q: Let x = [3 16 9 12 -10 -12 9 6 1]. Provide the command(s) that the positive values of x to zero…
A: A) x=[3 16 9 -1 0 -12 9 6 1] x( x > 0 ) = 0 B) x=[3 16 9 -1 0 -12 9 6 1] I = rem(x, 3) == 0…
Q: The If-Modified-Since header can be used to check whether a cached page is still valid. Requests can…
A: Given: The If-Modified-Since header can be used to check whether a cached page is still valid.…
Q: Which line(s) of the following code fragment will cause a runtime error? int *ipl int *ip2 *ipl *ip2…
A: A pointer is a variable which stores address. Working on direct address improves execution time.…
Q: iven the definition void myFunc(i
A: Part 1) Call by reference The address of the parameter is passed in the function call, known as…
Q: QUESTION 3 a) Write a PHP program to calculate the total mark from the variable Smarkl and Smark2.…
A: Answer: PHP Source Code: a). <!DOCTYPE html><html><body><?phpfunction…
Q: 4) Calculate 2ªd element of L1 = [1,10,19,28] divided by 1t element of L2 = [5, 14, 23,32]. Use two…
A: Answer: def fun1(l1):return l1[1]def fun2(l2):return l2[0]
Q: Write a C program based on the following code: int p[2]; char *argv[2]; argv[0] = "wc"; argv[1]…
A: int p[2];char *argv[2]; argv[0] = "wc"; argv[1] = 0;pipe(p);if(fork() == 0) { close(0);…
Q: Which of the following statement is false? O The "finally" block executed only when exception is…
A: Question 1) option D ie both A and B is correct answer 2) option A ie 1,1,2,1,2 is correct answer…
Q: ) Using Matiab commands, answer Four of the following actions.(One ane co.mand) a) Draw a line…
A: Matlab is a numeric computing platform used by thousands of engineers for analyzing data, building…
Q: 3. The both the function and server above should accept requests such as add, sub, mul, div, pow,…
A: The solution for the above-given question is given below:
Q: #include #include #include #include #include #include #include #define max 80 #define port 8080…
A: Correct code-…
Q: // Program 4.4.1 #include using namespace std; int main () { int var = 20; // actual variable…
A: 20 value stored in var variable *ip is a pointer variable ip store address of var in pointer…
Q: Consider the below commands i) sed "s/CSH/csh/g" temp> Is ~/newtemp 11) Is -v grep wc -1 111) Is -a…
A: As per time boundation. Below is the correct answer. I hope this will help.
Q: Choose the correct option 1)Which functions allow to change the location of the get and put…
A: Given: Choose the correct option 1)Which functions allow to change the location of the get and put…
Q: can download; restadata.txt : https://dosyam.org/2D1j/restdata.txt restaurant.c…
A: It is defined as a powerful general-purpose programming language. It can be used to develop software…
Q: Modify the script below so that it can calculate multiple values of y in a single statement using…
A: Below I have provided a MATLAB program for the given question. Also, I have attached a screenshot of…
Q: Question 4 a) write a very basic server in c using sockets and a socket descriptor that listens,…
A: a) write a very basic server in c using sockets and a socket descriptor that listens, accepts and…
Q: VI. LABORATORY ACTIVITY 1. Create an anonymous block with the following specifications: a. In the…
A: Save the code name as : lab_02_01_soh.sql code below:…
Q: Write the output for d1, d2 and d3, UTM a) Given the following R commands: d1-seq (3,15,3) d2-…
A: Solution: seq(): It create linear/sequence of element inside Vector. which(): It is function which…
Q: 13. The following very complex subroutine moves the cursor down to the next line. What, if anything,…
A: According to the information given :- we have .ORIG x4000NEWLINE LD R0, CRLF…
Q: Use the man command to examine the Unix command sudo a) Create an option string for the following…
A: Basically first you can copy the data of man in mandatabase.txt file easily by below commands. Brief…
Q: Q12: Given x=[7 6120-14 3-2 0] what are the commands that will execute the following operations: a.…
A: Matlab is a matrix programming language which is used to solve the complex mathematical and…
Q: Which of these method of String class is used to obtain character at specified index i? a-…
A: java String charAt() method returns a char value at the given index number.
Q: count=readFile(); CODEChecker (0,count); } else { printf("\nVaccine Name: "); fflush(stdin); gets…
A: Note: The definition of count and vacc is not given so count is considered as a variable, and vacc…
Q: in bash shell scripting Write a regular expression that matches a comma separated list of 4 strings…
A: In this program we have to write a bash script which have a array of list as the elements. Taking…
Q: How to modify exitstatus.sh to print a message for each of the three exit statuses described in man…
A: How to modify exitstatus.sh to print a message for each of the three exit statuses described in man…
Q: Please do not use a python code already on the internet. The following code must be written in…
A: the code is given below:
Step by step
Solved in 2 steps

- 15. Consider the following function:def f(aList):print(aList)alist.append(3)Suppose that function f() has been defined and that you are executing the belowsequence of commands in the IDLE shell:lst = [1]f(lst)f(lst)f(lst)What is printed when the code is executed?Show the contents of lst after all the above code has run:Question 40. Consider the following code chunk: import random x=0while(x < 4): x = random.choice([1, 2, 3]) print(x) It is not a good idea to run these lines because...a) x is an invalid argument to print().b) the condition x < 4 is never violated.c) the function random.choice() does not exist. d) x is initialised with the wrong type.Compliant/Noncompliant Solutions The following code segment was provided in Secure Coding Guidelines for Java SE: void readData() throws IOException{ BufferedReader br = new BufferedReader(new InputStreamReader( new FileInputStream("file"))); // Read from the file String data = br.readLine();} The code is presented as a noncompliant coding example. For this assignment, identify two compliant solutions that can be utilized to ensure the protection of sensitive data. Provide a detailed explanation of factors, which influence noncompliant code and specifically how your solutions are now compliant. Your explanation should be 2-3 pages in length. Submit the following components: Word document with appropriate program analysis for your compliant solutions and source code in the Word file. Submit your .java source code file(s). If more than 1 file, submit a zip file.
- IN SCALA PLEASE COULD YOU COMPLETE THE CODE OF FUNCTIONS: get_csv_url, process_ratings, process_movies, groupById, favourites, suggestions and recommendations import io.Source import scala.util._ // (1) Implement the function get_csv_url which takes an url-string // as argument and requests the corresponding file. The two urls // of interest are ratings_url and movies_url, which correspond // to CSV-files. // // The function should ReTurn the CSV-file appropriately broken // up into lines, and the first line should be dropped (that is without // the header of the CSV-file). The result is a list of strings (lines // in the file). def get_csv_url(url: String) : List[String] = ??? val ratings_url = """https://nms.kcl.ac.uk/christian.urban/ratings.csv""" val movies_url = """https://nms.kcl.ac.uk/christian.urban/movies.csv""" // testcases //----------- //: //val movies = get_csv_url(movies_url) //ratings.length // 87313 //movies.length // 9742 // (2) Implement two functions that…The following code must be written in python for this HW assignment. I will provide a skeleten for the code and you must write some lines of code to satisfy the objective of the prorgram. You will develop a web server that handles one HTTP request at a time. Your web server should acceptand parse the HTTP request, get the requested file from the server’s file system, create an HTTP responsemessage consisting of the requested file preceded by header lines, and then send the response directly tothe client. If the requested file is not present in the server, the server should send an HTTP “404 NotFound” message back to the client. Put an HTML file (e.g., HelloWorld.html) in the same directory that the server is in. Run the serverprogram. Determine the IP address of the host that is running the server (e.g., 128.238.251.26). Fromanother host, open a browser and provide the corresponding URL. For example:http://128.238.251.26:6789/HelloWorld.html‘HelloWorld.html’ is the name of the file you…In this final submission, you will build on checkpoint B to load the database and DNA sequence from files. There will be two databases and several sequences that will be available for download below. Example of the database is the file small.txt: name,AGATC,AATG,TATC Alice,2,8,3 Bob,4,1,5 Charlie,3,2,5 Example of the sequence is the file 1.txt: AAGGTAAGTTTAGAATATAAAAGGTGAGTTAAATAGAATAGGTTAAAATTAAAGGAGATCAGATCAGATCAGATCTATCTATCTATCTATCTATCAGAAAAGAGTAAATAGTTAAAGAGTAAGATATTGAATTAATGGAAAATATTGTTGGGGAAAGGAGGGATAGAAGG Implement/modify the following functions: Modify the function readData, which will now take an additional parameter: a string representing the filename containing the database of individuals and their STR counts. It will also return a bool indicating if opening the file was successful or not: bool readData(string filename, vector<string>& nameSTRs, vector<string>& nameIndividuals, vector<vector<int>>& STRcounts) Update the function…
- Hello, I am having an error and cannot figure out how to solve this question. Could someone please assist? Please be advised, I am using PostgreSQL as that is what was used in class. Thus, I must use PLPGSQL Code CREATE OR REPLACE FUNCTION Moreno_03_bankTriggerFunction()RETURNS TRIGGERLANGUAGE PLPGSQLAS$$CREATE TRIGGER Wise_12_bankTriggerAFTER DELETE ON accountFOR EACH ROW EXECUTE PROCEDURE Moreno_15_bankTriggerFunction();Choose the correct option 1)Which functions allow to change the location of the get and put positions ?a)sg() and sp()b)sekg() and sekp()c)gog() and gop()d)seekg() and seekp() 2)Which of the following operator is used to release the dynamically allocated memory in CPP?a) removeb)freec)deleted)both b and c 3) Local variables are stored in an area called ___________a) Heapb) Permanent storage areac) Free memoryd) Stack 4)Choose the correct option?#include<iostream>using namespace std;class Base {};class Derived: public Base {};int main(){Base *bp = new Derived;Derived *dp = new Base;}a. No Compiler Errorb.Compiler Error in line “Base *bp = new Derived;”c. Compiler Error in line ” Derived *dp = new Base;”d. Runtime Error 5)When the inheritance is private, the private methods in base class are __________ in the derived class (in C++).a. Inaccessibleb.. Accessiblec.. Protectedd. PublicProblem Given the target file f0 and candidate files f1-f20, there is an identical copy of f0 among the files f1-f20. Write a python program to perform the following tasks: · Read in each file and calculate the hex hash values by using SHA3 function with the length of 512 for all the given files f0, f1-f20. · Save the hex hash values of each file as a new line in a .txt file named hash.txt file. · Read hash values from hash.txt and compare them to find the identical copy of f0 among f1-f20. · Write the finding result (the matched file name) back to hash.txt Submission • Name your project fileHash.py and submit both fileHash.py and hash.txt on Blackboard. • The program should be properly documented. • The program should have user friendly Input/Output design • Duplicate work (or obviously similar one) will result in an F grade in the course. Grading 1. Include comments as specified in the course syllabus. (10%) 2. Source code and results. · Correctness (70%) · User-friendliness…
- In C#: Create a function that takes in one argument: The url to an API endpoint. The function should make the API call and pull the data in, convert it to a dictionary, and pull out the number of kills from the last 7 games the user played. The function should return the sum of the top five number of kills from these games. Call Of Duty API: https://rapidapi.com/elreco/api/call-of-duty-modern-warfareWrite a function which takes in a pandas dataframe and returns a modified dataframe that includes two new columns that contain information about the municipality and hashtag of the tweet. Function Specifications: Function should take a pandas dataframe as input. Extract the municipality from a tweet using the mun_dict dictonary given at the start of the notebook and insert the result into a new column named 'municipality' in the same dataframe. Use the entry np.nan when a municipality is not found. Extract a list of hashtags from a tweet into a new column named 'hashtags' in the same dataframe. Use the entry np.nan when no hashtags are found. Hint: you will need to mun_dict variable defined at the top of this notebook. ```--& 10. Create a function based on the following information: Your mission is to encrypt a secret message (text only, without special chars like "!", "&", "?" etc.) using Caesar cipher where each letter of input text is replaced by another that stands at a fixed distance. For example ("a b c", 3) == "d e f" Input: A secret message as a string (lowercase letters only and white spaces) and number to move text Output: The same string, but encrypted Return: The same string, but encrypted.

