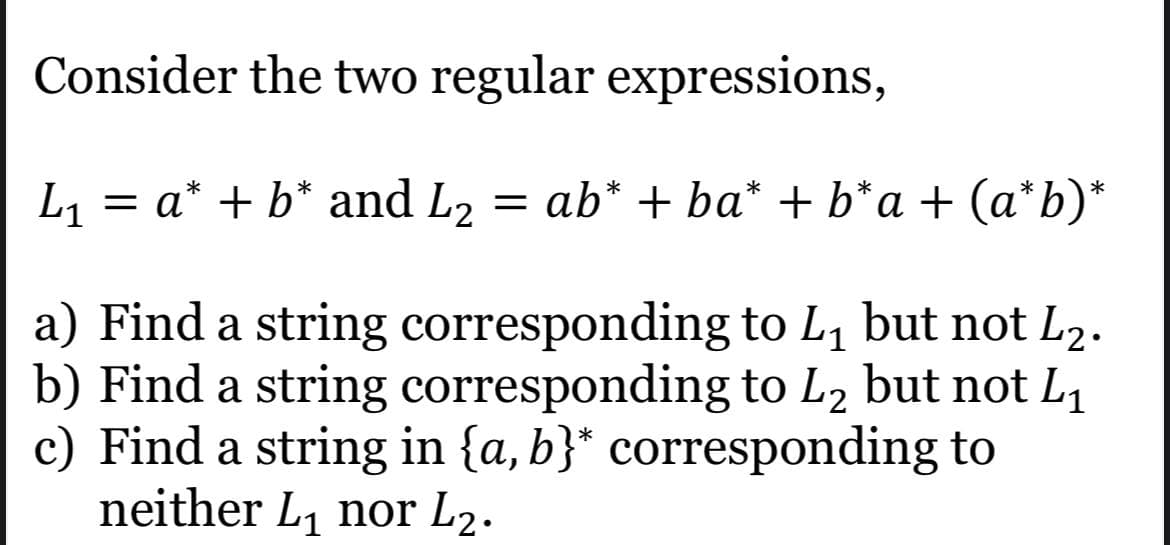
Consider the two regular expressions, L1 = = a* + b* and L2 = ab* + ba* + b*a + (a*b)* a) Find a string corresponding to L, but not L2. b) Find a string corresponding to L2 but not L1 c) Find a string in {a, b}* corresponding to
Q: ow to use a multidimension
A: Below how to use a multidimensional array
Q: Does the AND instruction require access to memory? It is possible that AND can access memory…
A: Answer: Option B: No, since we are using RISC processor, only LOAD and STORE instructions can access…
Q: If you have "many processes," what does it mean? Is there any way you could put it more succinctly?
A: MULTITHREADING: Multithreading is a programming approach that enables the creation of several…
Q: Wireless networks have a few difficulties that need to be addressed." Find three of these issues and…
A: It's infuriating when you're unable to connect to your wifi network. Worse still, the reasons for…
Q: Dynamic programming is a term that means something different to different people.
A: Dynamic programming is a term that means something different to different people.
Q: With the assistance of an example, explain IP fragmentation and reassembly.
A: IP fragmentation:- Broken pieces fit into network framings and can easily pass through a connection…
Q: Several concerns are raised by the basic properties of wireless networks. In addition to describing…
A: An overview of wireless networks: It is described as a computer network that uses Radio Frequency…
Q: Discuss the function of the business manager in determining the organization's computer hardware…
A: The business manager: They know how much money the organisation has, how big it can grow, what it…
Q: Distinguish between wireless networking challenges that may develop when two stations are visible at…
A: Wireless Networking Challenges: The fundamental difficulty is that everything, from smartphones to…
Q: The advantages and disadvantages of wireless networking must be taken into account. Should wireless…
A: Introduction: Wireless networks use radio waves to link devices such as laptops to the Internet, a…
Q: What are the various operators of pointer? Describe their u How will you declare a pointer in C++?
A: Lets see the solution.
Q: The following are the names of five recent studies that use machine learning techniques.
A: Machine learning (ML) is a sort of artificial intelligence (AI) that permits software applications…
Q: Learn about new wearable computing devices, such the Apple Watch and Android Wear, to see how they…
A: Answer we are introducing clothing as a way to think of new dimensions in the teaching structure of…
Q: State TRUE or FALSE for each of the following statement.. Q1 The C.I.A. triad consists of computers,…
A: This question comes from Information Security/ Cybersecurity which is a paper of Computer Science.…
Q: how they are related and how they differ; (2) how each affects the development of a system; (3) how…
A: Defining and discussing the terms methodology and technique. Including all of the following answer:…
Q: It's important to weigh the benefits and drawbacks of wireless networking before using it. Should…
A: Wireless local area networks (Lawns) transmit: We need to discuss whether or not wireless networking…
Q: List and discuss ten worldwide computer science and information technology organizations.
A: Ten worldwide organizations for information technology and computer science: Association for…
Q: List and discuss ten worldwide computer science and information technology organizations.
A: The solution to the given question is: Working in information technology entails working with both…
Q: Is it the vendor's or your organization's obligation to follow external rules and norms if the data…
A: Two security protocols that should be part of the vendor's data operation are : Privacy policies…
Q: What does the computer science acronym FDDI stand for?
A: computer science acronym FDDI stand for?
Q: this code is in java. Consider a program which can evaluate strings of DNA code. DNA code is a…
A:
Q: Describe how ICMP ping messages may flow across various networks. (Enter your response here.) What…
A: How ICMP ping messages may flow across various networks. Need to write command to deactivate…
Q: What is your favorite editing function that you will utilize on a frequent basis, according to you?…
A: Actually, the information that has been provided is as follows: What, in your opinion, is the most…
Q: Find the minimum for this list of numbers 65 90 2 3 99 71 64 14 69 28 70 7 9 19 47
A: #include <bits/stdc++.h>using namespace std; int getMin(int arr[], int n){ int res =…
Q: What are the benefits of using vectors instead of arrays in a programming context?
A: Array and vector Array and vectors are used to store the multiple data items together. But array…
Q: Threads are regarded to be "lightweight" processes for a variety of reasons. In order to start a new…
A: When a thread is formed, it does not require any additional resources to run instead, it shares the…
Q: What is the significance of Bitcoin Block Integrity, and how does it relate to data integrity and…
A: Given: Data saved in Blockchain is immutable and cannot be edited or destroyed, therefore meeting…
Q: Task(2): Write a MATLAB code that generates Unit Step Function.
A: Dear learner , hope you are doing well , I will try my best to answer this question. According to…
Q: Is it necessary to understand the fundamental principles of web design? What is the reason for this…
A: In web design, pages are created; anyone with access to the internet can view that. Rather than…
Q: Because of their inherent features, wireless networks face a broad variety of challenges. Three of…
A: Explanation: In order to operate efficiently and successfully, industrial companies now rely on…
Q: Write a structure to enter the title, author, subject and book id’s of 3 books
A: Write a structure to enter the title, author, subject and book id’s of 3 books we created a…
Q: In which of the following does the CricketFan class correctly inherit from the PartyAnimal class?
A: Option (D) class CricketFan(PartyAnimal) is right option cricketFan inherits from the PartyAnimal.…
Q: In the context of IT Projects, What is Significance of the following quality aspects: functionality,…
A: We need to discuss the significance of the quality aspects: functionality, system outputs,…
Q: Create a c++ program using any conditional statements that will determine the zodiac sign of your…
A: Given: We have to write a c++ program using any conditional statements that will determine the…
Q: A process' memory use is directly related to the number of threads it has started. What is the…
A: Given:During the course of a program's execution, the amount of memory used by the programme is…
Q: 9. Prove, using induction, that 3 divides n* + 2n whenever n is a positive integer. (a) State and…
A: The n3+2n divides by 3 for every positive integer n. proof by induction Basic step : n=1…
Q: To build shared memory between two processes, explain why system calls are necessary. Do you need to…
A: Intro Justify the need of system calls in establishing shared memory between two processes. Is it…
Q: Again, the adaptive playout delay approach has been chosen to remove jitter at the destination.…
A: Playout delay The playout delay on a frame represents the amount of delay added to a frame the…
Q: Distinguish between different kinds of polymorphism. Disagreements in their respective stances on…
A: Polymorphism: Polymorphism is a key characteristic of OO languages. It is a name with various forms.…
Q: What is the proof that technology and computer science have had an impact on our society? I'd want…
A: What are the ramifications of computer: science, as well as the supporting evidence that technology…
Q: What are some characteristics of TCP? Reliable Less overhead than UDP Congestion control…
A: TCP is reliable Protocol. so, First Option is CORRECT. TCP has less overhead than UDP . so, Second…
Q: A file named ClassData.txt contains records of several students. Each record contains student's name…
A: import java.util.Scanner;import java.io.*; public class Main { static double…
Q: What are the criteria for selecting an appropriate SPI approach for the company and project context?…
A: SPI HAS THE FOLLOWING ADVANTAGES: The primary benefit of employing the SPI is its ease of…
Q: QUESTION 4 Which of the following statements is incorrect about the following code? A. The…
A: Here we have given correct option for the mentioned code. you can find solution at step 2.
Q: What kind of security system does an DPS resemble the most? In what respects do these two systems…
A: An Intrusion Detection and Prevention System (IDPS) monitors network traffic for indications of an…
Q: A wrist watch is one of the most visible objects on the globe. Determine how each of the following…
A: In the above situation, Object: the watch is a kind of object. In programming, an object may let you…
Q: Side-effect-free programming is a topic of debate.
A: Side-effect-free programming: When a function depends on or affects anything outside of its…
Q: What makes threads "light-weight" processes? When a new thread is started, what system resources are…
A: light-weight: These lightweight programmes have their own stack but may access shared data. Because…
Q: distinction between processes and threads.
A: The answer is below-
Q: Describe the problem including input and output in your own words.) Design: (Describe the major…
A: Problem: Let the rectangle with the vertices a,b,c,d. a = (-2.5, 5) b = (-5, -2.5) c = (5, -2.5) d =…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Write a program in C++ to take input 5 strings and concatenate them in reverse order of their input, the string entered last should be present at start in the concatenated string. Print the string formed in output. Input: "A" "B" "C" "D" "E" Output: "EDCBE"PLEASE US SCHEME IN DRRACKET: In the language of an alien race, all words take the form of Blurbs. A Blurb is a Whoozit followed by between zero or more Whatzits. A Whoozit is the character 'x' followed by between one or more 'y's. A Whatzit is a 'q' followed by either a 'z' or a 'd', followed by a Whoozit.-The program should ask the user to “Enter an alien word:”, read the input as a string, and check whether or not it is a valid word (Blurb). If it is valid, it prints "The word is fine.", otherwise it prints "The word is a mess!". -The program should loop and ask the user for new input until they enter a valid blurb.Example code structure for how to find the total number of characters in 2 seperate strings at once using c. eg; string 1 = ''i eat pie'' and string 2 = ''i eat chocolate''. excluding spaces
- Hello, can someone helo me write a pig Latin converter in the C language? These are the two rules that it mist follow: Rule 1: If the string begins with a vowel (that is begins with 'a', 'e', 'i', 'o', or 'u') add "yay" to the end of the string. Rule 2: Otherwise, find the first occurrence of a vowel, then move all the letters before the vowel to the end of the word and add "ay". Note: "y" should be considered a vowel in this context.2. Write a program in C to separate the individual characters from a string. Sample I/OInput the string: Programming Expected Output : The characters of the string are : P r o g r a m m i n gGiven a char variable ch and list of strings lStr in python, write a program to print all strings whose last character is same as the given char variable.
- Correct answer will be upvoted else downvoted. Computer science. section grouping is a string containing just characters "(" and ")". A standard section succession is a section grouping that can be changed into a right number juggling articulation by embedding characters "1" and "+" between the first characters of the arrangement. For instance, section successions "()()" and "(())" are normal (the subsequent articulations are: "(1)+(1)" and "((1+1)+1)"), and ")(", "(" and ")" are not. You need to find a string b that comprises of n characters to such an extent that: b is a standard section grouping; in the event that for some I and j (1≤i,j≤n) ai=aj, bi=bj. As such, you need to supplant all events of 'A' with a similar kind of section, then, at that point, all events of 'B' with a similar sort of section and all events of 'C' with a similar sort of section. Your undertaking is to decide whether such a string b exists. Input The primary line contains a solitary…A string is a palindrome if it reads the same from front to back as it does from back to front (e.g. "kayak", "rotator" and "noon" are palindromes). When determining whether an alphanumeric string is a palindrome, we often ignore spaces, punctuation and case in the string (e.g. "A man, a plan, a canal --Panama!" is also considered a palindrome). Write a complete C program to read a string, echo it to the screen, determine whether it is a palindrome, and write a message indicating whether it is or isn't. Your main function should prompt for the string, read the string, print it, call the clean function (to remove all spaces, punctuation, and turn uppercase letters into lowercase letters), print the new string, then call the reverse function (to place the characters into reverse order) and print the new string resulting. In the final step, you will compare the result of the reverse function with the original string and print a message if the string is a palindrome or not. The clean…Write C++ program to print the number of alphabets in alphanumeric string. String contains only alphabets Example output for string: abl23cd is 4.
- 3. Write a program in C++ to find the Greatest Common Divisor (GCD) of two numbers iteratively.Sample Output:Input the first number: 12Input the second number: 8The Greatest Common Divisor is: 4• R7.17Consider the following code that repeats a C++ string three times. string a = "Hello"; string b = a + a + a; Suppose s is a C string, and t is declared as char t[100]; Write the equivalent code for C strings that stores the threefold repetition of s (or as much of it as will fit) into t.Write C program to search for a pattern in a given string and show number oftimes it is found in the given string. For Example:Input: “AB CD EF 123 AB Good Bye”Pattern: “AB”Output: “AB” found 2 times

