constant printf("\nThank you for using nameage. Bye!\n"); error: expected identifier or return 0; error: expected declaration specifiers or A error: expected identifier or error: expected identifier or 1 before token before before string before token 1
constant printf("\nThank you for using nameage. Bye!\n"); error: expected identifier or return 0; error: expected declaration specifiers or A error: expected identifier or error: expected identifier or 1 before token before before string before token 1
Chapter7: Using Methods
Section: Chapter Questions
Problem 3RQ
Related questions
Question
Can someone help me I keep getting these errors trying trying to compile and run this C program
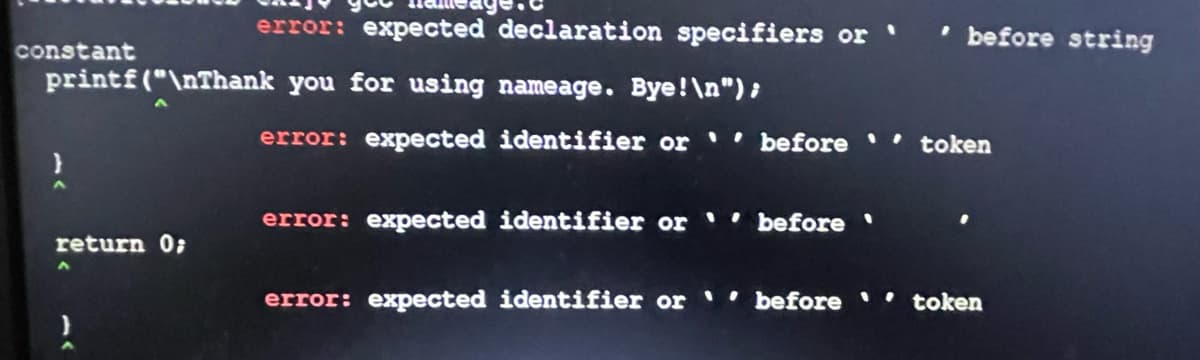
Transcribed Image Text:constant
error: expected declaration specifiers or
printf("\nThank you for using nameage. Bye!\n");
return 0;
error: expected identifier or before token
error: expected identifier or before '
before string
error: expected identifier or
'before '' token
![main ()
name [50];
age, years_left;
printf("Welcome to name age\n\n");
printf("Please enter name:");
scanf("%s", name);
printf("Please enter your age:");
scanf("%d", &age);
if (age < 0) {
Printf("please enter a valid age.\n");
return 0;
}
if (age == 67) {
printf("Hi %s. You shouyld retire now. \n", name);
}
else if (age > 67) {
printf("Hi %s. You should already be retired. \n", name);
I
}
else{
int years_left = 67 - age ;
printf ("Hi %s. Ypu have %d years left for retirement.\n", name, years_left);
}
)
printf ("Thank you for using nameage. Bye!\n");
)
return 0;](/v2/_next/image?url=https%3A%2F%2Fcontent.bartleby.com%2Fqna-images%2Fquestion%2F25de04cf-e2a5-404e-a320-bf8f0014cf68%2F2a26791c-61cd-4d54-99d0-c6c9d53dd72a%2Fg8zp9wzm_processed.jpeg&w=3840&q=75)
Transcribed Image Text:main ()
name [50];
age, years_left;
printf("Welcome to name age\n\n");
printf("Please enter name:");
scanf("%s", name);
printf("Please enter your age:");
scanf("%d", &age);
if (age < 0) {
Printf("please enter a valid age.\n");
return 0;
}
if (age == 67) {
printf("Hi %s. You shouyld retire now. \n", name);
}
else if (age > 67) {
printf("Hi %s. You should already be retired. \n", name);
I
}
else{
int years_left = 67 - age ;
printf ("Hi %s. Ypu have %d years left for retirement.\n", name, years_left);
}
)
printf ("Thank you for using nameage. Bye!\n");
)
return 0;
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT