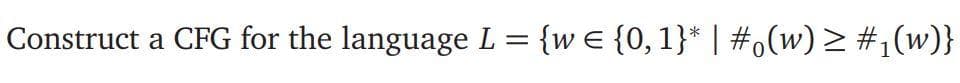
Construct a CFG for the language L = {w € {0, 1}* | #o(w) > #,(w)}
Q: At its heart, how does a prototype approach to software product design work?
A: Introduction: Prototyping: It is a system development method that entails building, assessing, and…
Q: Predict the output for the C++ program in Program Q2 it the input by the user at line 4 is as in…
A: Ans: As per the given code the output for the input is : #include <iostream> using namespace…
Q: IoT in Medical & Healthcare a. what are the Hardware components? b Software (Addresses areas of…
A: NOTE :- Below i explain the answer in my own words by which you understand it well. The…
Q: A signal can travel either forward (from port 1 to port 2) or backward (from port 2 to port 1) and…
A: Solution: Given, A signal can travel either forward (from port 1 to port 2) or backward (from…
Q: What criteria do we use to determsine whether or not an argument is valid?
A: Introduction: An argument is legitimate if and only if the following conditions are met:
Q: Which of the following constitutes a computer-based instrumentation system's four components?
A: The complete answer is given below
Q: example: ababaaa, babbbb,aaababababaaa, etc. Part(a) Give a NFA for L as a state transition diagram.…
A: The regular expression would be (a+b)*aba(a+b)* + (a+b)*bab(a+b)* + (a+b)*aba(a+b)*bab(a+b)* +…
Q: What are the factors that can work against linear scale up in a transaction processing system?
A: Transaction Processing System A Transaction Processing System (TPS) is an Information system that…
Q: Where can static routes come in handy for the network administrator?
A: Establishment: The fact that modems can convert the incoming signal from these many sources into a…
Q: What are the most important processor structural components, and how should they be described in a…
A: Answer PROCESSOR: A processor is a type of integrated electrical circuit that conducts the…
Q: What is the purpose of the "forward lookup zone" in the DNS?
A: Introduction: A DNS server refers to a huge network server holding a large number of IP addresses…
Q: 5) Write a Java program to get the difference between the largest and smallest values in an array of…
A: logic:- store first number from array to min variable store first number from array to max…
Q: What is the purpose of an object interface's "private" section? Why can't it be entirely hidden?
A: Introduction: The C++ compiler must be able to build code that uses a class based just on the class…
Q: Difference between the MATLAB strcmp and C's strcmp(), which returns e if the two strings are the…
A: Predefined functions are used to reduce che code complexity. Strcmp is also a predefined function…
Q: Code this in C program A set of integers 0..MAX may be implemented using an array of boolean…
A: Bitset Array Bitset array is also called bit array or bit map or bit vector which stores bit at each…
Q: Recognize, recognise, and define the six components of an information system.
A: Intro The six components of an information system -An information system is combination of six…
Q: Explain why public-key cryptography is required for IoT-enabled wireless networks.
A: The cryptography can be denoted as the process of encrypting the data at the sender's end and…
Q: Program 03 1. Winclude 2. using namespace std; 3. int main() 5. char select; 6. 7. do( 8.…
A: the program given below
Q: Can you think of a Linux package management system that you've used or plan to use?
A: Intro Software updates from specified Linux repositories (repos) may be installed, updated,…
Q: When and where was the first video camera invented?
A: Answer The first video camera was invented in 1888 by Louis Le Princes.
Q: SPEC's performance measurements are repeatable, but they're not reli
A: Lets see the solution.
Q: What are your opinions on the status of database technology now and in the future?
A: opinions on the status of database technology and in the future is explained in step 2:-
Q: Define the term "root authority." Describe how it is used.
A: When we are trying to use any website, it is always desired that the website should be a trusted…
Q: Who decides when and how data is used or handled in
A: Organization the executives is the specialty of joining people on a typical stage and enabling them…
Q: What is the primary distinction between services and software components?
A: Introduction the above question is about differences between services and software components
Q: Computer science What is the purpose of a buffer?
A: Introduction: The basic objective of a buffer solution is to resist pH changes so that the pH of the…
Q: Sound travels through the air because of collisions between the molecules in the air. The…
A: Here I have created an infinite loop. Inside the loop, I have taken input from the user and stored…
Q: Microsoft was working on an RDBS File System named WinFS at one point. What would the advantages of…
A: About:- WinFS stands for window future storage,and owned by Microsoft. The idea behind WinFS to…
Q: What are some real-world instances of how computers are being used?
A: INTRODUCTION: Here we need to give examples of how computer are being used.
Q: Based on the Program Q3 source code, modify the program by using the while loop. Prog 1. 2. 3.
A: The syntax of while loop is while(condition) { //statement to be executed }
Q: What is the relationship between cohesion and coupling in software development, and how are they…
A: Foundation: The relationship within the module is shown by cohesion. Coupling depicts the modules'…
Q: How about being able to find out who checked out a certain book or what books a given patron has on…
A: Given: The system should be able to find out who took a certain book or what books a particular…
Q: Would you rather an issue was discovered at runtime or during compilation?
A: The complete answer is given below
Q: re Te is the temperature of the air in degrees Celaiua and the velocity is in metera/second. Write a…
A: PROGRAM: #include <iostream>#include<bits/stdc++.h> using namespace std;float…
Q: Make a list of five things a layer can do.Is it possible that two (or more) layers could accomplish…
A: Introduction: `Five jobs that a layer can do
Q: Who was the person responsible for the creation of the hard drive?
A: Intro The credit for the invention of hard drives goes to Reynold B. Johnson who along with his team…
Q: cy for Facebook
A: A security policy is a set of normalized practices and techniques intended to shield a business'…
Q: Consider the five moral dimensions of information systems.
A: What is a moral dimension? the distinction between good and bad or right and wrong behavior. The…
Q: Consider the five moral dimensions of information systems
A:
Q: What is the mechanism through which data is transformed into information by computers?
A: Introduction: The input device should be used to get raw data from the user and convert it to a…
Q: What is a Web server, and how does it function?
A: Definition: A web server is a computer that runs sites. It's a Computer program that circulates…
Q: What is a load balancer? Why do we need a load balancing device?
A: Start: Load balancers are used to boost capacity, or the number of concurrent users on a network, as…
Q: Computer Science *Do you believe there's value in conducting a penetration test in your…
A: According to the PCI SSC-Payment Card Industry Security Standards Council, the goal of a penetration…
Q: Describe the Server List.
A: Server: - It is a device that has a specific set of program which provides different services. There…
Q: (C PROGRAMMING ONLY) 6. Finding the Impostor by CodeChum Admin There's this Dog game I played…
A: Answer in step 2
Q: Could you describe the distinction between a stack and a heap? Contains information on stack…
A: Intro Working on stack and heap Stack is used for storing local variables and order of method…
Q: What is a cyber-security policy for Facebook?
A: Cybersecurity: Cybersecurity is used to safeguard critical systems and sensitive data against…
Q: Justify why it is desirable to have accessors to private types rather than making the types public…
A: Introduction: In a nutshell, an accessor method restricts access to an attribute by allowing users…
Q: How does a computer's operating system function, and what are its two primary goals? What is the…
A: An Operating System is an interface between a computer user and computer hardware.
Q: scuss a monetization model that would work for the ap
A: A monetization model that would work for the app.
Step by step
Solved in 2 steps with 1 images


