Convert -30 (decimal) to hexadecimal.
Q: List local and remote software acquisition techniques.
A: Software gaining refers to the procedure of obtain software. This force involve increasing the…
Q: We DFS the directed graph Gd, where G is the depths-first tree/forest. G will be cycle-free if all…
A: Directed graphs are essential data structures in computer science that model a wide range of…
Q: Which server operating systems are most popular, and what are their pros and cons?
A: Running organizations (OS) are crucial components of computer systems. They manage ironware…
Q: However, the OSI model calls for a greater number of layers than are often present in modern…
A: Modern computer networks are complex systems that allow multiple devices to communicate and share…
Q: Determine the stack's performance when free.
A: Evaluating the performance of a stack when it is free or not in use provides insights into its…
Q: Over time, the Internet has built its technological infrastructure.
A: The Internet is the most potent instrument and prominent resource nearly everyone on Earth utilizes.…
Q: Explain I/O. Explain how input and output devices work, including what they send and receive, what…
A: What is input and output devices: Input and output devices are components used in the interaction…
Q: What makes a vertical-coding control unit?
A: Vertical coding in control units refers to a methodology employed in computer architecture for micro…
Q: Explain how to avoid network security issues from failing systems.
A: What is failing systems: "Failing systems" refers to computer systems or components that experience…
Q: NW_Q3) IP addressing operates at the network layer (Layer 3) of OSI, IP addresses must be able to…
A: Given IP address is, 196.10.10.0It is a class C network and the required hosts per subnet are 55,…
Q: Share software development statistics. Breakdown every process.
A: Metrics for the Software Development Process. Efficiency and effectiveness in the software…
Q: Write a C# Sharp program to swap two numbers. Test Data: Input the First Number : 5 Input the Second…
A: For swapping, we will use a temporary variable to store the value before updating any of the…
Q: Which server operating systems are most popular, and what are their pros and cons?
A: There are several widely used wine waiter OS in the technology business nowadays, each with unique…
Q: Routers do network functions that switches cannot:
A: Routers perform network functions that switches cannot.They handle IP addressing and routing,…
Q: How do the six DBLC stages affect the data dictionary?
A: Analysis - This stage involves understanding the business requirements and identifying the data that…
Q: Managing non-unique search keys required a search key characteristic. How does this affect B+ tree…
A: When managing non-unique search keys, the characteristics of the search key have a direct impact on…
Q: Explain how General Motors used IT to increase global cooperation. How did General Motors encourage…
A: General Motors (GM), one of the world's largest car manufacturers, have used IT tactically to…
Q: Firewalls affect network and internet security. Define the phrase, then use facts and examples to…
A: => A firewall is a network security device or software that acts as a barrier between an…
Q: Action Taking: Create a simple chatbot for corporate use. In this case, your work will be titled…
A: Chatbots are clever virtual assistants that appreciate and interact in usual language and Are used…
Q: python
A: # import the turtleimport turtle# make the turtle objectt = turtle.Turtle()# make the turtle speed…
Q: If the data is too large for the cache, a write buffer will return it to the CPU from main memory.…
A: In this question we have to understand the next steps after If the data is too large for the cache,…
Q: Which is the biggest difference between analytics and business intelligence?
A: Business Intelligence (BI) and Analytics often overlap in many aspects but are fundamentally…
Q: Please outline the AIT labs' IT issues, their causes, and your proposed remedies. Discuss the…
A: AIT Labs, like any other organization, may encounter various IT issues that prevent its lab from…
Q: Explain why object-oriented programming relies on encapsulation.
A: Encapsulation is a fundamental concept in object-oriented programming (OOP).
Q: Explain the first-to-fifth generations of computer technology in as few words as possible.
A: Computer technology has evolved significantly over the years, progressing through five generations…
Q: Explain how the spiral model works with software development methods.
A: The spiral model is a software development process model that combines the iterative development…
Q: Do you see apps replacing the web? Please justify your choice.
A: Let us explore this topic and delve into the possibilities and potential justifications for such a…
Q: Let p and q represent, respectively, "Sharks have been spotted close to the shore" and "Swimming at…
A: What is implieces use in programming: In programming, the "implies" operation, often represented by…
Q: Is cloud-based collaboration technology deployable in various settings? How can cloud collaboration…
A: Cloud-based collaboration technology refers to the use of cloud computing platforms and tools to…
Q: Compare popular server OSes.
A: Operating systems are vital server infrastructure components as connection points for hardware and…
Q: Event viewer logs sort server events. Pick two.
A: What is event viewer logs: Event Viewer logs are records of events and activities that occur on a…
Q: orage uses just magnetic disc outer tracks. "Hot spots," or regions of high activity, define this…
A: In the realm of data storage, hard disk drives (HDDs) have been a longstanding technology. These…
Q: The question at hand is about the exact difference between computer design and computer…
A: The computer is a device that accepts information and manipulates it for some result based on a…
Q: How many more questions do you need answered before deciding whether database as a service is right…
A: Whether DB as a Service (DBaaS) suits a library, depends on multiple factor. First, a clear…
Q: Average interruption length? How does this affect context switching?
A: The average disruption length refers to the standard length of an intermission in a procedure. In…
Q: Should databases be ethically assessed? Employee income and benefits information (such as medical…
A: Databases, which store big amounts of data, have the possible to impact folks and culture…
Q: OS Questions: How might big-endian/little-endian CPU designs increase inter-process communication?…
A: What is computer architecture: Computer architecture refers to the design and organization of a…
Q: Please use words to describe "application security."
A: Application security refers to the practice of protecting software applications from unauthorized…
Q: Who oversees US hacking policy?
A: In the United States, the oversight of hacking policy and related cybersecurity matters is divided…
Q: How do you see the most obvious signs that a laptop's operating system has been tampered with?
A: One of the most understandable signs that a laptop's in commission system has be altered or…
Q: Cloud advantages? Reduce cloud computing risks? Doesn't cloud computing overcome its drawbacks?…
A: Cloud computing is the provision of computing services such as servers, storage, databases,…
Q: What are "technical papers"? Name four key differences between technical and user documentation.
A: Technical papers are formal documents that present research findings, describe new technologies, or…
Q: Illustrate the computing cycle.
A: Hello studentGreetingsThe computing cycle, also known as the fetch-decode-execute cycle or…
Q: INT, INTO, INT 3, and BOUND are software interrupt commands. They work how?
A: INT, INTO, INT 3, and BOUND are software interrupt commands that are used in low level programming…
Q: Maintaining virtual computer security might be confusing.
A: Virtual Computer SecurityVirtual computer security refers to the measures and precautions taken to…
Q: BI implementation issues?
A: Implementing Business Intelligence (BI) systems is a complex undertaking that organizations face in…
Q: Give me an authentication example. Each authentication mechanism has pros and cons.
A: Authentication mechanisms play a crucial role in verifying the identity of users or devices. Each…
Q: Compiler and interpreter differences?
A: In the world of programming, two essential components play a crucial role in executing software:…
Q: Implement a __setitem__ function that also supports negative indices. For example: W = L2(Node(10,…
A: Start.Define a class Node with attributes data and next.Define a class L with an attribute head and…
Q: Define "technical documentation" first. Is there a table comparing and contrasting the four most…
A: Technical documentation refers to the written materials that provide detailed information about a…
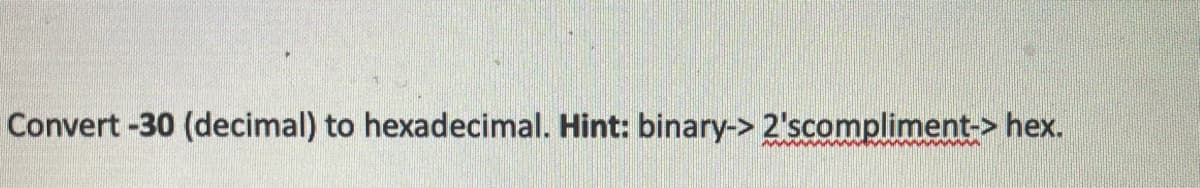
Step by step
Solved in 4 steps

- Examples of 8-bit binary representations of the decimal value 30 are shown below. definition a) the opposite of a term; b) Excess-M;?Consider the decimal number (-48.325). Write down binaryrepresentation of this number using the IEEE 745 single precision format. Clearly specify “Sign”, “Exponent” and “Mantissa” fields of the single precisionrepresentation.Hexadecimal to Binary BEHA1F
- Write down the binary representation of the decimal number 63.25 assuming it was stored using the single precision IBM format (base 16, instead of base 2, with 7 bits of exponent).Construct a trace table for the following algorith that Convert an integer number in decimal (Base 10) to its binary (Base 2) equivalent.For a binary floating point representation of 6.75, what is the mantissa and exponent?
- Write the 8-bit binary representation of letter p.with the given positive integer, find the all n-digit binary numbers, along with the their decimal representation in C++ VS example: Input: nDigits = 4Output:0000 -> 00001 -> 10010 -> 20011 -> 30100 -> 40101 -> 50110 -> 60111 -> 71000 -> 81001 -> 91010 -> 101011 -> 111100 -> 121101 -> 131110 -> 141111 -> 15How can binary values be converted into unsigned and signed integers?
- Draw a line from each hexadecimal value to its binary equivalent on the rightRepresent the following numbers to its 6-bit binary representation and perform binary subtractionusing 2’s compliment representation 50-30?1) 0xBEAD (in hex) can be written in decimal (base 10) as: 2) 23.2578125 (decimal) is expressed in binary (base 2) as: Do no use any spaces within your representation. Use 8 bits to represent the integer part, and an additional 8 bits to represent the fractional parts (i.e., 8 bits before the radix point and after the radix point).

