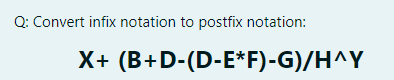
Convert infix notation to postfix notation: X+ (B+D-(D-E*F)-G)/H^Y
Q: What are the reasons behind the JUnit test writing requirements?
A: JUnit will treat the annotated public void method as a test case because of the Test annotation.…
Q: Write a program that takes a list of students" names and marks and calculates the average marks. You…
A: The Answer start from step-2.
Q: What different sorts of services are related with the different layers of the stack?
A: Start: The presence of many levels facilitates the communication inside the network. Each layer is…
Q: Please provide an example of a TuringEquivalent or TuringComplete machine/system or programming…
A: Introduction: The term "Turing equivalent" refers to a machine or system with a processing capacity…
Q: VM live migration is suitable for which of the following scenarios ? load balancing among datacenter…
A: Answer the above question are as follows
Q: Is it feasible to have the same MAC address on two distinct devices? Whether or whether this will…
A: MAC address : Media Access Control (MAC) addresses are hardware identifiers that uniquely identify…
Q: Some IT security professionals feel that their firms should hire ex-computer criminals to find holes…
A: Security for the infrastructure for an organisation is very important so as to protect its data and…
Q: We need to determine which four aspects of software development are considered to be the most…
A: Answer of the question given below
Q: Convert the following C codes into its equivalent assembly code: c. if (al>bl) && (bl=cl) x=1; d. if…
A: (c) if (al > bl) && (bl = cl) x = 1; Assembly code:
Q: Briefly describe the stack parameter.
A: The above question is answered in step 2 :-
Q: Say your customer has never used the internet before. Explain in simple terms what a network server…
A: Clients, sometimes referred to as service requesters, are pieces of computer hardware or server…
Q: Object Oriented Programming in C++ access specifiers are both public and private
A: This is true statement Public: All the class members declared under public will be available to…
Q: English cannot make. coffee", she thought leaving good. restaurant no article/the/the O an/ no…
A: Given:- English cannot make ______good_____*coffee’, she thought Leaving___ restaurant . Correct…
Q: What does it imply when the transport layer acts as the connecting point between the network support…
A: Introduction The Open Systems Interconnection (OSI) model describes seven layers that computer…
Q: Please provide an example of a Turing Equivalent or Turing Complete machine/system or programming…
A: Introduction: The Turing equivalent means that machine/system has the capability having…
Q: What function do design patterns serve in the field of software engineering, and how can one make…
A: We need to discuss functions of design patterns in the field of software engineering and it's types.
Q: Guice is a popular dependency injection library in the Java programming language. However, there are…
A: Answer: Dependency Injection handles difficulties like how an application or class can be…
Q: computer science - Describe the decision-making tools that are used in location analysis.
A: Introduction: Each organisation should use location planning strategies, according to computer…
Q: Find two ways of performing the same job, one of which is more technologically sophisticated than…
A: Introduction: Technological progression can be characterized as investigating and growing new…
Q: B-write a program to compute X 1+2+3+ +100 X= 1x2+2x4+3x6++100x200
A: Algorithm: Assigned the number of terms(n) to 100 Calculate the numerator as the sum of 100 natural…
Q: It is recommended they use SAP GUI for HTML. This allows you to integrate classic Dynpro-based…
A: ANSWER: True
Q: Assume you have access to your department's DNS servers' DNS caches.How would you go about…
A: Introduction: It's feasible to obtain access to the DNS (Domain Naming Server) server's cache. This…
Q: Consider the following code. How many times is the function rec_func_2() called in total? options: 0…
A: #lets trace the given code to find out how many times rec_fun2() called in total: def rec_func_2(n):…
Q: How are centralised and parallel/distributed databases different?
A: Answer to the given question: The main difference between centralized and parallel database is…
Q: When a piece of software fails, it may be quite inconvenient for the people who use it. Companies…
A: Definition: I've included points to verify before releasing the programme, as well as points that…
Q: It is not possible to assign several IP addresses to a single network connection in Windows. the…
A: IP addresses: An IP address, or Internet Protocol address, is a set of digits that uniquely…
Q: Differences between Harvard and von Neumann architectures may be summarized as follows:
A: Generally, any micro-controller is an arrangement of its CPU components, specifically RAM and ROM.…
Q: Make a difference between the three data modelling tiers.
A: The process of creation of data model so that it can be used to store data on the database is termed…
Q: What precisely do we mean when we refer to something as a computer network, regardless of whether or…
A: Computer Network: A computer network is a collection of linked separate frameworks that work…
Q: How do you know whether your MAC address is unique for each of your network devices? Is this the…
A: A data transfer policy for a network is known as a media access control (MAC), and it is responsible…
Q: Correct and comprehensive answers will be UP VOTED; otherwise, they will be DOWN VOTED. What…
A: Introduction: Scheduler Activation (SA): A scheduler activation is a call made to a process by the…
Q: When we hear the term "operating system," who or what do we infer? What are the two primary…
A: Operating System :- Operating System is software that works as an interface between a…
Q: When it comes to data backup and recovery, what are some of the most significant considerations?
A: Explanation: Planning is done during the data backup and recovery process to keep track of vital…
Q: When it comes to data backup and recovery, what are some of the most significant considerations?
A: Answer: Data backup: Deciding what data is most important and The most important areas to consider…
Q: B-write a program to compute X 1+2+3++100 X= 1x2+2x4+3x6+-+100x200 Matlab
A: The required code for the Matlab program has been coded in the next step with comments for…
Q: Q4/ Convert the following algebraic expressions into expressions in Mat lab: 121 13) c = √2-a² + b²…
A: Answer:
Q: Describe eight of the most crucial computer architecture concepts.
A: Introduction: Moore's law One of Intel's founders, Gordon Moore, estimated that integrated circuit…
Q: Describe the waterfall model of development.
A: Introduction: Winston Royce purchased the Waterfall Model in the year 1970. It is a…
Q: What function do design patterns serve in the field of software engineering, and how can one make…
A: Introduction: A design pattern is a reusable, generic solution to a common issue in software…
Q: What's the difference between computer architecture and management?
A: Computer Architecture is concerned with the interconnection of hardware components to construct a…
Q: Using your own words, walk us through how each of these activities may be accomplished on a computer…
A: System Programming and Application Programming: The major distinction between application…
Q: The read position advances towards the end of the file when items from the file are read. the report…
A: The question is to find the given statement is true or false.
Q: What role does Model-View-Controller (or MVC) have in the development of internet applications in…
A: Answer: Model-View-Controller(MVC): -> MVC separates the business logic from the presentation…
Q: Describe the basic stages of the waterfall development model.
A: Introduction: A sequential software development model, the waterfall model is a sequential software…
Q: B-write a program to compute X 1+2+3+-+100 1x2+2x4+3x6+-+100x200 Matlap
A: I give the code in Matlab along with output and code screenshot
Q: Consider y as a 1000-by-1000 matrix. Which of the following statements will extract the maximum…
A: In this question we have to give the choose correct answer for MATLAB question, where we have a 1000…
Q: For people who work in the technology industry, understanding the fundamentals of basic electronics…
A: The internet of things, or IoT, is a system of interrelated computing devices, mechanical and…
Q: How feasible is batch processing? What's the reason, if any?
A: -- Batch processing is the processing of transactions in a group or batch. - No user interaction is…
Q: A push down automata is different than :finite automata by Its memory (stack) O Number of states…
A: To recognize patterns finite automata is generally used. There are two types of finite automata…
Q: Explain the use of standard functions in programming.
A: Usage of standard functions Standard functions are used to accomplish a certain activity.
Please provide step by step solution
Step by step
Solved in 3 steps with 1 images

- Topic: Binary Operation True or False The identity element of a * b = a + b is 1.NOTE: *String means (array of characters).*Ways to define string in data segment:1. Str1 DB “ MIcroprocessor lab“2. Str1 DB 'M','I','c', 'r', 'o', 'p','r','o','c','e','s','s ','o','r',' ','l','a','b'Topic: Binary Operation True or False The operation a * b = a + b − 1 on the set of integers has no identity element.
- (True/False): A function ending with the letter W (such as WriteConsoleW) is designed towork with a wide (16-bit) character set such as UnicodeTopic: Binary Operation True or False The identity element of an addition is 1 while the identity element of multiplication is 0.Translate the infix string a*b/c+e/f-g+h to postfix notation.
- P5.Js coding to program thisC program A decimal number between 0 and 32 exclusive can be expressed in binary system as x4x3x2x1x0, where xi ’s are either zero or one. Write a C program that accepts (from the terminal) a decimal number in the above range and prints out the equivalent binary representation.This is for R studio
- Write a program to Find ASCII Value of a Character. Use C++ language to write a code.function triangular_number() { echo "Enter the range of numbers (start end): " read start end even_count=0 odd_count=0 echo "------------------------------------------" for (( i=$start; $i<=$end; i++ )) do triangular=$(( (i*(i+1))/2 )) if [[ $triangular -gt $start && $triangular -lt $end && $((triangular%2)) -eq 0 ]]; then ((even_count++)) echo $triangular elif [[ $triangular -gt $stat && $triangular -lt $end ]]; then ((odd_count++)) fi done echo "------------------------------------------" echo "Total even triangular numbers found: $even_count" echo "Total odd triangular numbers found: $odd_count" } Make a flowchart with this code No hand written and fast answer with explanationWhat is equivalent to 4s



