Convert into assembly language code
Q: 0006
A: Solution - In the given question, we have to tell how many nodes are visited by searching node 15.
Q: What exactly is a virtual machine, sometimes known as a VM, and how does it function? In what ways…
A: As an operating system (OS) or application environment, a virtual machine (VM) imitates specialized…
Q: Is there a way to explain how a protocol moves from one OSI layer to another?
A: Protocols follow the OSI model in the following ways: On the target device, data is transferred from…
Q: What kind of systems lend themselves to agile development the most?
A: Adaptive Strategy To begin, SDLC is an acronym for the Software Development Life Cycle.An Agile SDLC…
Q: Answer the following sentences true or false 1. The body of a loop can contain more than one…
A: Explanation: 1. A loop can have several statements in its body. The curly braces are not required if…
Q: It is the absence of physical cords that makes wireless connections superior than their wired…
A: Inspection: In this section, we will discuss wireless connections and their wired equivalents and…
Q: Explain how UNIX/Linux and Windows apply the principle of least privilege differently.
A: Launch: Privileges are the authorization of computer resources that can only be accessed by those…
Q: You may take advantage of the high level of redundancy provided by a Hadoop installation. The fact…
A: The solution is as follows: EXPLANATION One of the benefits of a Hadoop system is the high level of…
Q: Q. Write a Java Program to reverse a string without using reverse() function?.
A: Answer the above questions are as follows
Q: Pascal's Triangle The Pascal triangle can be used to compute the coefficients of the terms in the…
A: The asked C program using nested for loops has been coded in the next step with explanatory…
Q: Could you please explain the Hardware and Software Equivalence Principle to me? If you want to be…
A: Software Equivalence: Because every function that can be done by software can also be performed by…
Q: Explain why conditional statements are used in your coding solution and how they will help you…
A: Conditional Statements: Conditional statements help you to make a decision based on certain…
Q: What does main return? Consider the following program:
A: #include <stdio.h>int f(int x,int y);int a = 3;int b = 2; int main(void){ int c = a + b; //…
Q: Decrypt the message MAXLJGTEAX which was encrypted using the affine cipher: f(p) = (5p+6) mod 2-
A: The answer is
Q: The omission of a data item from a data model raises the question: why is this the case?
A: A data model may be seen as an abstract model that organizes and standardizes data components,…
Q: What advantages and disadvantages does a relational database management system have?
A: Relational database management system is a database that stores data items and sets based on how…
Q: QIB Assume a=5, b-4, c=6 find the result of the following expressions? 1) Tl= (a c) || (b> a) &&(ac)…
A: answer along with output screenshot is given below
Q: . WAP to reverse string in Java by using while loop without reverse function.
A: The answer of this question is as follows:
Q: What output will be generated by this code public class FileClassExample { public static void…
A: If both text files, testfile.txt and testfile2.txt, do not exists in the directory ReadingFromFile?…
Q: Explain why conditional statements are used in your coding solution and how they will help you…
A: Conditional statements are the statement which contains some condition and a block. Inside the block…
Q: An Artificial Neural Network contains 2 neurons in the Input Layer (called neuron 0 and neuron 1), 2…
A: The answer is
Q: What are the similarities and dissimilarities of creating a webservice as against RMI in Java
A: Answer:
Q: In cryptography, how is the inverse of a matrix used? What exactly does it imply when you say that a…
A: The key matrix is used to encrypt the messages, and its inverse is used to decrypt the encoded…
Q: Discuss the difference between the two-tier and three-tier client/server architectures?
A: difference between the two-tier and three-tier client/server architectures?
Q: What kind of vision does e-mail conjure up for you? After it is transmitted, how does a message get…
A: Institution: A mental model is an intuitive idea that a user has or develops about how an…
Q: If prototyping is used in the design of user interfaces, do you think it will be possible to solve…
A: Prototyping permits visual inspection: Prototyping is an iterative process in which design teams use…
Q: A GSM system uses 124 channels and each channel is divided into 8 time slots. What is the maximum…
A: The answer is
Q: Explain what virtualization is as well as the distinguishing features of the different kinds of…
A: Please find the detailed explanation in the following steps.
Q: What are your thoughts on the company's operating system? Please respond in 50-100 words. What are…
A: INITIATION: The most beneficial program on a computer is the one that runs the rest. An operating…
Q: Show that xy' + yz' + x'z = x'y + y'z + xz'
A: This theorem of set theory that expresses that the complement of the association of two sets is…
Q: Q2. Define software quality ( . What is software ..)? Define unit testing and give an example…
A: Software quality The software quality means that the developed software should be error free that…
Q: Give at least three CSS terms from today's lesson. Explain how the three keywords you've picked are…
A: KEYWORDS IN CSS: CSS properties feature several particular keywords that are sometimes used as…
Q: The personal laptop computer is a product that has proven to be very reliable in spite of the fact…
A: The quality of performing consistently well is called reliability. It refers to the consistency of a…
Q: How do flow information works in OGDCL?
A: INTRODUCTION: Here we need to tell how do flow information works in OGDCL.
Q: Make sure you know the difference between an appliance and a gadget. Provide illustrative instances…
A: Given: The equipment employed has a very precise purpose, according to the inquiry. You'll be titled…
Q: How many distinct keys must be developed and how many different keys are really being utilized right…
A: Cryptography: Cryptography focuses on processes that allow only those who sent and received a…
Q: How may regions and availability zones be used to improve the cloud application's resilience,…
A: Cloud application's: Cloud computing is a technology that is used to offer computer services and…
Q: Two predicted virtualized operating system impacts should be identified and explained.
A: Virtualization on the operating systems: Operating system-based virtualization Virtualization is a…
Q: TOPIC IS FOR LOOPS (programming/python) You run a local girl's basketball league in your town. You…
A: Python programming language provides different types of loops to handle looping requirements. Python…
Q: In terms of machine learning or deep learning algorithms, how is today's artificial intelligence…
A: Artificial Intelligence (AI): Artificial Intelligence (AI) isn't going anywhere. Artificial…
Q: state and explain 3 useful algebraic laws obeyed by regular expression operators
A: The algebraic laws which are the laws which are used to minimise the logic function or to change the…
Q: Consider how vital wireless networks are in today's emerging nations. Wireless technology has…
A: INITIATION: Thanks to wireless communications, the Internet and the digital economy are now…
Q: What is the proof that technology and computer science have had an impact on our society? Give…
A: The following are few examples of the impact that technology has had on our society and the…
Q: Is there a link between data governance and data stewardship? What are the primary components of a…
A: Data stewardship and data governance go hand in hand, therefore let's talk about how they're…
Q: As a member of a bank's information system staff, you are required to do system maintenance tasks in…
A: Inspection: As a part of a banking system's information system personnel, you'll be asked to do…
Q: Determine if each function is injective, surjective or bijective. Give one counterexample for each…
A: Here in this question we have given a function f from {a,b,c,d} to itself, where f(a) = d, f(b) =…
Q: To transmit the data 1011000 to his friend using hamming code technique. Calculate (i) num
A: The answer is
Q: In contrast, most computer systems employ fewer layers than the OSI model requires. Why not reduce…
A: The Open Systems Interconnection (OSI) model lays out the guidelines for conducting communication.…
Q: Suppose you have a RISC machine with a 2.7 GHz clock (i.e., the clock ticks 2.7 billion times per…
A: The answer is
Q: Find the initial values the assembler will generate for each the directives given below: byte8 BYTE…
A: Byte8 will generate the values 00, 33, 2E, 5A for BYTE 51, 46, 90. byte9 will generate the values 05…
Convert into assembly language code
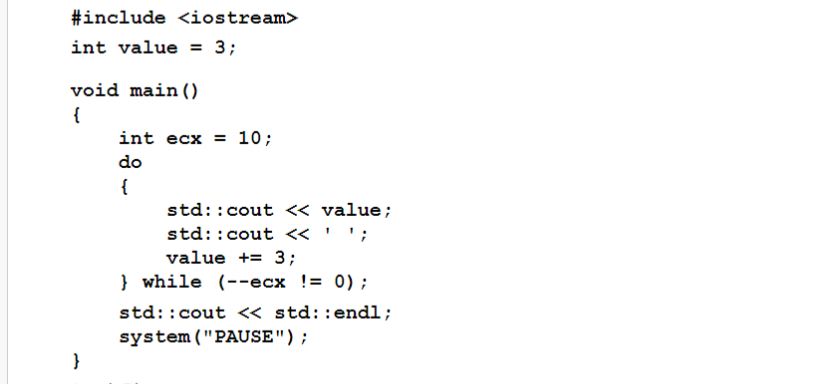
Step by step
Solved in 2 steps

- Input operations are supported by class__________________C++ ProgrammingActivity: Deque Linked List Explain the flow of the main code not necessarily every line, as long as you explain what the important parts of the code do. The code is already correct, just explain the flow. SEE ATTACHED PHOTO FOR THE PROBLEM INSTRUCTIONS int main(int argc, char** argv) { DLLDeque* deque = new DLLDeque(); int test; cin >> test; //Declarations int tempnum; int num; int sum; int count; bool addfirst = false; bool addlast = false; bool remfirst = false; bool remlast = false; switch (test) { case 0: //Implementation do{ cin >> num; if(num == 0){ break; } //Reset tempnum = num; count = 0; sum = 0; addfirst = false; addlast = false; remfirst = false; remlast =…Order check Write a program OrderCheck.java that takes four int command-line arguments w, x, y, and z. Define a boolean variable whose value is true if the four values are either in strictly ascending order (w < x < y < z) or strictly descending order (w > x > y > z), and false otherwise. Then, display the boolean variable value.
- LANGUAGE: C++ This is good practice with classes. You are going to create a race class, and inside that class it has a list of entrants (so a list of entry objects) for that race. To test the program you will make an array of three races (so an array of race objects). Populate each race with time and list of entry objects. Print out the schedule. Create a race class that has The name of the race as a character string, ie “RACE 1” or “RACE 2”, The time of the race An array list of entries for that race Create a race array of 3 (or 4) of those race objects, For the list of entries for a particular race that you need above, make a horse entry class (the building block of your array list) you should have The horse name The jockey name The jockey weight Now you need to Populate the structure (ie set up the three races on the schedule, add 2-3 horses entries to each race. You can hardcode the entries if you want to, rather than getting them from the user, just to save the…Explain the values of int data type.(Card Shuffling and Dealing) Create a program to shuffle and deal a deck of cards. Theprogram should consist of class Card, class DeckOfCards and a driver program. Class Card shouldprovide:a) Data members face and suit of type int.b) A constructor that receives two ints representing the face and suit and uses them to initialize the data members.c) Two static arrays of strings representing the faces and suits.d) A toString function that returns the Card as a string in the form “face of suit.” Youcan use the + operator to concatenate strings.Class DeckOfCards should contain:a) An array of Cards named deck to store the Cards.b) An integer currentCard representing the next card to deal.c) A default constructor that initializes the Cards in the deck.d) A shuffle function that shuffles the Cards in the deck. The shuffle algorithm shoulditerate through the array of Cards. For each Card, randomly select another Card in thedeck and swap the two Cards.e) A dealCard function that returns the next…
- Term by CodeChum Admin (JAVA CODE) Construct a class called Term. It is going to represent a term in polynomial expression. It has an integer coefficient and an exponent. In this case, there is only 1 independent variable that is 'x'. There should be two operations for the Term: public Term times(Term t) - multiplies the term with another term and returns the result public String toString() - prints the coefficient followed by "x^" and appended by the exponent. But with the following additional rules: if the coefficient is 1, then it is not printed. if the exponent is 1, then it is not printed ( the caret is not printed as well) if the exponent is 0, then only the coefficient is printed. Input The first line contains the coefficient and the exponent of the first term. The second line contains the coefficient and the exponent of the second term. 1·1 4·3 Output Display the resulting product for each of the test case. 4x^4C++ simple friend function.Create a C++ class called cube that calculates the volume of a cube. Use appropriate accessors (getters) and mutators (setters), constructors, etc. Your program must also include a friend function that will sum the volume of two cube class instances.Output the individual volumes of each of the two cube classes and then the total volume from the friend function. Example of friend funtion #include <iostream> using namespace std; class Box { double width; public: friend void printWidth( Box box ); void setWidth( double wid );}; // Member function definitionvoid Box::setWidth( double wid ) { width = wid;} // Note: printWidth() is not a member function of any class.void printWidth( Box box ) { /* Because printWidth() is a friend of Box, it can directly access any member of this class */ cout << "Width of box : " << box.width <<endl;} // Main function for the programint main() { Box box; // set box width…In C++ Create a class called Pencil. Pencil has a type. Create another class called Customer. The customer class should have a ID number, array (using pointers) called purchases, and a Pencil variable. Make sure to create the purchases array in the constructor. Create a function to fill in purchase amount. Create a way to output all the information about a customer, including all the details about their type of pencil.
- Briefly explain default argument initializerTrue or False Structure objects can be passed into a method only by reference.In C++ QUESTION 14 class rectangleType { public: void setLengthWidth(double x, double y); //Sets the length = x; width = y; void print() const; //Output length and width double area(); //Calculate and return the area of the rectangle (length*width) double perimeter(); //Calculate and return the perimeter (length of outside boundary of the rectangle) private: double length; double width; }; Write the function definition for the function perimeter





