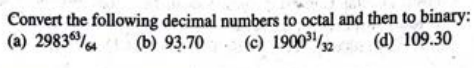
Convert the following decimal numbers to octal and then to binary: (a) 29836 (b) 93.70 (c) 1900/2 (d) 109.30
Q: The office hours for Professor X in Spring 2021 are as follows: Monday 3:00pm - 5:00pm Thursday…
A: Java Code
Q: What type of malware do you think is the most destructive: viruses, worms, Trojan programs, spyware,…
A: :: Solution :: Almost everyone is familiar with the term computer virus, but only a few might have…
Q: Which five uses for computer graphics are most prevalent
A: Given: We have to discuss Which five uses for computer graphics are most prevalent.
Q: Describe programming. Choosing a programming language: factors to take into account
A: Introduction: A method for instructing computers on what to do next is computer programming.…
Q: What role does documentation play in a successful criminal investigation? Make a list of all the…
A: Introduction Any communicable material used to describe, clarify, or provide instructions for…
Q: What effects does a data breach have on cloud security? What are a few of the potential defences?
A: A data breach can be denoted as a scenario in which sensitive information may be leaked to…
Q: If the computer has 32 kilobytes of memory and the storage location is the largest word (8 bytes),…
A: Introduction: A preliminary look at the archival repositoryShelf locations are components of a…
Q: Which JavaScript code using the jQuery library should be placed in the blank to make the boldbright…
A: The fadeIn() method gradually changes the opacity, for selected elements, from hidden to visible. It…
Q: What does the word "entity" mean? a real person, place, or thing.
A: A single person, place, or object that has information stored about them in a database is referred…
Q: Create a python program ROCK PAPER SCISSOR GAME
A: Python is a multipurpose language and one can do anything with it. Python can also be used for game…
Q: What distinguishes centralised version control software from distributed version control software?…
A:
Q: 5. Create a list letters, that contains all lowercase letters from a to e. a) Print the list. b)…
A: Python Code : my_list = ['a', 'b', 'c', 'd', 'e'] print(my_list) #1 # elements from index 2…
Q: What will the value of eax be after this sequence? O 8 09 O 10 mov eax, 10 push eax dec [esp] inc…
A: Answer: 10
Q: Write a C# program to implement the concept of arguments pass by reference using ref parameter.
A: ::Solution:: void Method(ref int refArgument) { refArgument = refArgument + 44; } int number = 1;…
Q: What advantages does this file system have over a sequential one?
A: Introduction: The sequential file access mechanism makes sorting very straightforward.
Q: What is the information that can be obtained from the status word of 8251?
A: In this question we have to understand what information we get from the status word of 8251 Let's…
Q: 1.
A: The unified process is an iterative process The answer is True Explanation The Unified Process is…
Q: You have been asked to deliver the project earlier than expected with the same resources as the main…
A: Introduction: Untrained developer risks software project Schedule risk: Time-related or project…
Q: Assume you are in charge of creating a university's examination system. Which documents are…
A: It's important to call out the files we need to use for the testing platform, as well as the…
Q: Kindly provide a COMPLETE and CLEAR solution *Answer should be typewritten*
A: If any code has positional weight, then it is known as weighted code.weighted code further divided…
Q: What are fiber-to-the-premises or fiber-to-the-business networks' benefits and drawbacks?
A: Fiber to the house is the installation and usage of optical fiber from a central location straight…
Q: . Write a Java program to print an American flag on the screen. Expected Output |||| |||| ||||||…
A:
Q: Not one of the optimised bubble sort's benefits over other sorts for sorted items.
A: Question. In the case of sorted items, the optimal bubble sort has a number of advantages over…
Q: Need help with this javascript assignment /* Although the track times appear correctly, the album…
A: In this question we have to code for JavaScript to convert string type variables containing values…
Q: Describe five security recommendations for online programmes.
A: Here in this question we have asked to describe five security recommendations for online programmes.
Q: e potential of artificial intelligence in light of its current developments
A: in the following section we will be discussing about the potential of artificial intelligence in…
Q: We must create test cases in order to test a collection of functions. The original paper may assist…
A: Introduction: Testing for security Using a tried-and-true security testing methodology gives a…
Q: Considerations for system architecture design will be challenged by the expanding number of mobile…
A: Introduction: A local area network (LAN) called a wireless local area network (WLAN) links various…
Q: Write a program in python which will read an integer k from standard input. Use the list function…
A: k = int(input("Input:"))#readinput and converting it to integerl = list(i for i in range(-10,k+1) if…
Q: Consider your home in today's world. Protecting it is vitally important. Identify and discuss two…
A: Every year, organizing investigators spread out their innovation expectations for the following…
Q: research "primary and foreign keys" and summarize your findings. In your writing be sure to answer:…
A: Primary Key: What are they? An primary key is a field in a table which extraordinarily recognizes…
Q: Consider yourself the Authentication Manager of an IT organization, and you see that things were…
A: Here is the logic behind setting hacker-resistant passwords. When you're asked to create a password…
Q: You and a coworker often participate in online role-playing games. Someone recently used malware…
A: Introduction: Three Identity theft hazards when playing: Online gaming is a common danger. Users…
Q: Suppose you are using a jQuery animation to make an element change color when the user clicks on it,…
A: Correct Option is " a " a => Pass the function in as the first argument to the animate()…
Q: Write a Java program to take nth number from the user. So your code have to print the Fibonacci…
A: Java:- Java is an object-oriented language as its concept is based on OOPS, it also supports…
Q: What are the four various E-R diagram types that are produced during conceptual data modelling, and…
A: E-R Diagram Types: The rectangle, oval, and diamond are the three fundamental symbols that are used…
Q: Find the error in this code from math import exp, sin def f(x, m, n, r, s): return expsin(x, r, m) +…
A: In this question, we have to define expsin function before the f function in order to make it work…
Q: 1) What is data security so important now? 2) What occurs if an information system is improperly…
A: Data is a valuable asset that generates, acquires, saves, and exchanges for any company. Protecting…
Q: Asap only code.
A: Code: <?php echo "Enter value of w: "; $w = (int)fgets(STDIN); echo "Enter value of x:…
Q: We think Flynn's taxonomy has to be elevated one level. What sets advanced computers apart from…
A: Enhanced computers have been in use for decades now, but the use of advanced algorithms and software…
Q: What are the different type of networking / internetworking devices
A: Local Region Networks, Metropolitan Area Networks, and Wide Area Networks are the three basic kinds…
Q: Describe the effects on a DBA's workload of pairing each of the eight cost estimation algorithms…
A: Estimating Strategies: To examine the reasonableness of solutions, students must apply estimate…
Q: What is the most important technique database designers may use to affect the performance of…
A: Answer: In many cases, developers, database administrators and data analysts face poor application…
Q: What impact does "Race Condition" have on the operating system of a computer?
A: Introduction: When a computer or system tries to do two or more things at the same time, but they…
Q: A SNAP container called Bind is being utilised. Because of this, when you attempted the command…
A: Remote name daemon control: It's a name server control tool. This name server control tool allows…
Q: Determine and describe the process model used by application software.
A: Explanation: Programming applications: Booking tickets online (for anything from a concert to a…
Q: What distinguishes an Intel Celeron from a Pentium in terms of processors?
A: What is the difference between a Pentium and a Celeron? While both CPUs are from the Intel family,…
Q: Write a program to print multiplication table of a given number by user in C#.
A: Here in this question we have asked to write a Program in C# to print a multiplication table of a…
Q: Why is it possible that when you look at a folder's properties, the Security tab is missing from the…
A: The folder is protected from being accessed by unauthorized users and from having modifications made…
Q: Given the context Free Grammar G = {{S}, {a, b, +, x), P, S} where P consists of the following…
A: Hi please find the solution below and I hope it would be helpful for you.
Kindly provide a COMPLETE and CLEAR solution
*Answer should be typewritten*
Step by step
Solved in 3 steps

- A(n) __________ is an integer stored in double the normal number of bit positions.Q10.13) Convert the following decimal numbers to their hexadecimal and binary equivalents: A)16 B)80 C)2560 D)3000 E)62,5004. Convert the following floating point numbers to decimals using the 64 bit normalization. 0 01100111111 0101001100000000000000000000000000000000000000000000
- Convert the following number into binary numbers to octal and then to decimal.a. 11011100.101010b. 01010011.010101c. 10110011Convert the following decimal number into 8 bits signed binary and also hexadecimal numbers. Decimal Number: -1Answer the following questions. 1) Convert base 16 hexadecimal number 1111.116 to base 10 decimal number. 2) Convert base 2 unsigned binary number 0111 0101.10102 to base 10 decimal number.
- how many bits are required to represent the following decimal numbers? (a) 68 (b) 81 (c) 114 (d) 132 (e) 205Represent each of the following integers as 10-bit two’s complement binary numbers.i) -18510 ii) 15610 iii) -20510 iv) 16910How many bits are required to represent the following decimal numbers? a. 17b. 68c. 132d. 12e. 121

