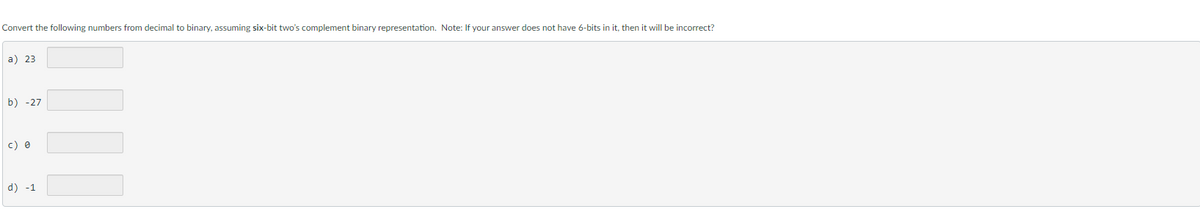
Convert the following numbers from decimal to binary, assuming six-bit two's complement binary representation. Note: If your answer does not have 6-bits in it, then it will be incorrect? a) 23 b) -27 c) 0 d) -1
Q: Consider a system with 13 dedicated devices of the same type. All jobs currently running on this…
A: The solutions is an given below :
Q: How can cloud security employ the shared responsibility paradigm with identity and access management…
A: The shared responsibility paradigm is a cloud security model that defines the roles of both the…
Q: What are some of the benefits that may be obtained via the use of virtualization?
A: Given: So, what are the benefits of virtualization? Answer: Virtualization's advantages include:…
Q: How exactly do you go about connecting two personal computers to a network that runs on Unix, and…
A: An operating system is a group of applications that serves as the interface between computer…
Q: Are we utilizing technology properly as a society?
A: The answer for the above question is given in the following step for your reference.
Q: Python's widespread use on the cloud demonstrates why it is such a powerful language. Can you…
A: Why is Python so popular in cloud computing? Python is currently used to power some of the most…
Q: Which system development life cycle should we utilize to build an online learning management system…
A: Administrators may do the following using an LMS portal: and content suppliers to build, roll out,…
Q: Which three cryptographic procedures are the most fundamental?
A: Cryptography: Cryptography employs encryption to safeguard private information from unauthorised…
Q: When computers become more powerful, this happens. How may computers' importance in education can be…
A: Introduction Computers are becoming increasingly important in education, as they provide students…
Q: What is peer-to-peer communication in the OSIM?
A: Introduction Communication: "communication" refers to the exchange of data, information, or…
Q: llaborative human-computer interaction application
A: Human computer interaction Human-computer interaction (HCI) is the study of how people interact…
Q: Description: In a hypothetical class, students take two midterms and an optional final. If a student…
A: Here's the code for a function that takes the midterm1 score, midterm2 score, and comprehensive…
Q: Is it at all feasible to standardize the Agile software development processes?
A: Introduction: Agile techniques are a sort of project management methodology used in software…
Q: How does one interpret the host portion of an IPv6 address? If you needed the host part of an IPv6…
A: According to the information given:- We have to define one interpret the host portion of an IPv6…
Q: 20. (A) Explain the differences between a class, an abstract class and an interface in Java. 21. (B)…
A: Let's understand this one by one What is the class ? The class is the concept of the object…
Q: Explain database procedure. Data warehousing uses what software?
A: An ordered collection of data or information that is often saved electronically on a computer…
Q: Just what is an IMIS, and how does it help businesses, globally?
A: Marketers utilise Marketing Information Systems (MIS) to assess information requirements, produce…
Q: What are some of the governance difficulties that should be kept in mind while moving from…
A: Charity administration employs an IaaS deployment approach to handle its data centres. Cloud…
Q: Assume you are NOT in your homedirectory. You want to change permissions of /etc/abc.txt What would…
A: Command Computer's text interface is called the command line. It is a programme that receives…
Q: What is the concept of cloud computing in computer science, and how is it used to provide on-demand…
A: The answer is given below step.
Q: How does agile's iterative and incremental approach connect to the system development lifecycle?
A: The answer to the question is given below:
Q: Show how the local/global nexus will affect web-based application interfaces for various cultural…
A: Web application planning issues: 1. Set clear objectives. Your web app's success depends on how well…
Q: What is the absolute bare minimal number of keys that are required to be utilized when putting…
A: Introduction: In Public key encryption, deciphering the information requires a separate key or set…
Q: In C++ You have a class called Fraction, which uses the heap. The constructor for the class is…
A: Introduction Constructor: When an object of a class is formed, a function Object() { [native code]…
Q: Wireless networks' influence on emerging countries should be examined. Why are wireless networks…
A: Introduction: Wireless networks are a special kind of computer network in which communication…
Q: THE FUTURE OF WIRELESS NETWORKING Explain how wireless communication technologies outperform wired…
A: There are several advantages to using a wireless communication system over a wired one, but the most…
Q: You must create (in C++) two Crosswalk Signal objects from the class shown below to prove that your…
A: C++ is a general-purpose programming language as an extension to the C programming language. It is a…
Q: In what way did the collaboration between Facebook and Cambridge Analytica lead to a data breach?
A: Intentional or accidental disclosure of private information to an unauthorised person constitutes a…
Q: ce cloud securit
A: Data breach When private, sensitive information that ought to have been kept private has been…
Q: Unlike the OSI model, most computer systems have fewer layers. Why not decrease layers? What are the…
A: Reducing layers in a computer system can reduce flexibility,make troubleshooting harder, increase…
Q: In computing gcd(125, 332) using Euclid's GCD algorithm, the pair (j[0], [0])= (125, 332) is…
A: Euclid's algorithm is an ancient algorithm used to find the greatest common divisor (GCD) of two…
Q: What is the absolute bare minimal number of keys required to utilize public key cryptography?
A: In this question we need to determine the absolute bare minimal no of keys which are required to use…
Q: Typical process description tools include _____. a. context diagrams b. decision trees…
A: According to the information given:- We have to choose and define Typical process description tools…
Q: How does a computer differ from other devices?
A: This questing will describe a number of the defining characteristics of a computer, including:…
Q: Can you please answer the following question. Program in Python. It needs to looks EXACTLY like the…
A: Code: def state_count(states_dict): return len(states_dict) states = {'FL': 'Tallahassee', 'GA':…
Q: What's the difference between cryptography's private and public keys?
A: In cryptography, private and public keys are two different types of cryptographic keys used for…
Q: Two arguments justify software engineering.
A: Your answer is given below.
Q: A database table's "transitive dependence" definition? A non-key trait relies on another. B: C:…
A: It seems like the text you provided is not a clear and coherent sentence or question. However, based…
Q: Memory that can only be read has compression already built in. Memory that can only be erased…
A: An EEPROM, which stands for electrically erasable programmable read-only memory, is a kind of…
Q: The capacity to juggle many responsibilities at once is what we mean when we talk about…
A: Multitasking can take place when someone tries to perform two tasks simultaneously, switch . from…
Q: Wireless networks are crucial in developing countries. Wireless technology has replaced LANs and…
A: The advent of wireless communications has made it possible for billions of people to access the…
Q: The functional capabilities of a user interface that are essential for successful navigation should…
A: answer:-The practical capacities of a UI that are fundamental for fruitful route can differ…
Q: Explain computer cable kinds.
A: Analyzing the Issue: Coaxial, twisted, fibre, USB, series, parallel, and crossover cables are just…
Q: Define software quality. What is software testing? Define unit testing and give an example. Define…
A: Software quality refers to the degree to which software meets its intended purpose and user…
Q: The process of keeping Internet Banking Security Systems up to date is impacted, in some manner, by…
A: The process of developing and implementing newer emerging technologies has a significant impact on…
Q: Compute the following: (80 +135) (mod 8) = (80-135) (mod 8) =
A: First, we need to calculate the sum of 80 and 135: 80 + 135 = 215 Then we need to find the remainder…
Q: Write a function in C++ that accepts a single number, calculates the number of positive odd numbers…
A: According to the information given:- We have to follow the instruction in order to get desired…
Q: In the context of cloud computing security, what does the term "shared responsibility paradigm"…
A: In cloud computing, the shared responsibility paradigm refers to the division of security…
Q: Explain how credit card numbers in electronic transfers might compromise your financial information.
A: Introduction: The act of sending money electronically from one account to another is referred to as…
Q: Software engineering is necessary for two reasons.
A: As the requirements of users and the environment in which the programme runs change at a quicker…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

- A(n) __________ is an integer stored in double the normal number of bit positions.___________ occurs when the result of an arithmetic operation exceeds the number of bits available to store it.Add the following numbers in binary using 2's complement to represent negative numbers. Use a word length of 6 bits (including sign) and indicate if an overflow occurs. Repeat using 1's complement to represent negative numbers. (If overflow occurs, enter OVERFLOW.)
- Add the following numbers in binary using 2's complement to represent negative numbers. Use a word length of 6 bits (including sign) and indicate if an overflow occurs. Repeat for parts (a), (c), (d), and (e) using 1's complement to represent negative numbers. (Include the leading one for negative numbers in your answers. If overflow occurs, enter OVERFLOW.)Perform the following hexadecimal additions and subtractions. Assume the numbers are stored in 32-bit 2’s complement binary numbers. Indicate the sign of the answer and whether overflow occurs. Show all your work. BBCA270C + AE2234641.7 Add the following numbers in binary using 2's complement to represent negative numbers. Use a word length of 6 bits (including sign) and indicate if an overflow occurs. (a) 21 + 11 (d) (−12) + 13 (e) (−11) + (−21) Repeat the question using 1's complement to represent negative numbers.
- Convert the following decimal numbers to binary 4-bit two’s complementrepresentations, or explain why the conversion is not possible.a. 3 b. -5 c. -10Add the following numbers using 4-bit representation using 2’s complement addition. State whether the result is positive, negative, or overflow.Perform the following hexadecimal additions and subtractions. Assume the numbers are stored in 32-bit 2’s complement binary numbers. Indicate the sign of the answer and whether overflow occurs. Show your work. E9B20F5D – FE605C8D
- Evaluate the following by converting to decimal, performing the arithmetic operation, and converting to binary to express the results. Please note. the answer must be expressed in binary to be correct! when bertormina number conversion. use a precision of eight (8) fractional bits.Please add the following numbers in binary using 2’s complement to represent negative numbers.Use a word length of 6 bits (including sign) and indicate if an overflow occurs:(-11) + (-4) = ?11 + 9 = ?(-10) + (-6) = ?Show the numbers given below according to the decimal system in both binary and hexadecimal order by using the two's complement representation in 32 bits. a) 482 b) -280

