convert to binary,
Q: How do you use pattern matching and guards in haskell? example?
A: These question answer is as follows
Q: Question 4 solve this postfix expression 1 2 3 4 - 8 4 + * / 4 * + Full explain this question and…
A: Solution: Given, solve this postfix expression 1 2 3 4 - 8 4 + * / 4 * +
Q: public class EmployeeDiagram private String name; private double payRate; private final int…
A: Program Approach:- Step 1: Class declared with the name of EmployeeDiagram Step 2: private…
Q: and what is the application will be?code?
A: The Simple desktop application created here is for showing text in the event of the click of a…
Q: Suppose that %edx stores decimal value 5 and %eax stores decimal value 3. Find the value in hex that…
A: Answers:- value are %al will be the stored as 0x01 in hex. The result of cmpl…
Q: Write a Java program that computes the depth of a binary tree
A: code for the depth method would be as follows: depth(TreeNode root){…
Q: What will the following code print assuming infile is a file object that has been just opened for…
A: The above question is solved in step 2 :-
Q: The Magic 8-Ball is a plastic sphere, made to look like an eight-ball, that is used for…
A: Here you have to create an application/program simulating the magic ball. I have provided the class…
Q: How do I code a Python program where get request to / should return index.html, get request to…
A: The question has been answered in step2
Q: Question 34 A The process or idea of asking questions of the teams upstream from your position…
A: The above question is solved in step 2 :-
Q: arent's message buffer, what happens normally?
A: The answer is
Q: Which of the following is correct code to open the file input.txt for reading? outfile =…
A: Answer:
Q: Que 4 Use less and more to view the content of the file top in fedora? full text typing work only
A: Fedora:- Software developers and community members can create specialized solutions for their…
Q: What is the difference between “continue” and “break” statements in C#?
A: HI THEREI AM ADDING MY ANSWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: Practices Charlie has a large book collection. He was keeping track of it in a spreadsheet, but it…
A: 1. If this layout will goes directly to the database then the title of the book is not appropriate…
Q: Prove: For all integers n, if n² is odd, then n is odd. Use a proof by contraposition, as in Lemma…
A: For all integers n, if n² is odd, then n is odd. Use a proof by contraposition ?
Q: pact of global sourcing on glob e example to support your an
A: Solution - In the given question, we have to specify the impact of global sourcing on global supply…
Q: Q.30 Explain how ElGamai scheme generate and verify the digital signature.
A: ElGamal signature scheme The ElGamal signature scheme is a digital signature scheme considering the…
Q: 1 2 3 4 5 6 12345 1234 123 12 1
A: The code is given below for the above-given question:
Q: s the language L={we{a,b,c}* :|w|=3na(w)} regular? (Hint: 2na(w) = n₂(w) + nc(w).)
A:
Q: When we solve the Greatest Common Divisor problem, we w of this method? The Unique Prime…
A: Dear Student, The correct answer for your question is given below -
Q: IN JAVA Given an array, write a program to print the array elements one by one in a new line. If…
A: I have done it in java language:
Q: Which is the best definition for lambda expression? the Church-Turing thesis X a function with some…
A: Lambda Expression:- The lambda expression is short block of the code which takes in parameters and…
Q: Q.3 What are the security approaches used to implement security policy?
A:
Q: Explain 1 data modeling approach that can be used to evaluate data, how to explain a business…
A: Data Modeling: The process of creating a framework that outlines the data relationships…
Q: Input The first line of the input contains two integers n and m separated by a single space. n…
A: As the programming language is not mentioned we are using JAVA The JAVA Code is given below with…
Q: I need help writing a method that implements the following specification. I want to name the method…
A: Solution: Given, When num is: | changeItUp returns*…
Q: Prove:Church’s thesis: The class of computable functions is equal to the class of intuitive…
A: The inference () is obvious. Each programme of a TM may be performed step by step (for example, by…
Q: ACTIVITY The cost to ship a package is a flat fee of 75 cents plus 25 cents per pound. 1. Declare a…
A: Program code: import java.util.Scanner; public class ShippingCalculator {…
Q: What is the binary encoding of the following RISC-V assembly instruction? Please write your answer…
A: The above question is solved in step 2 :-
Q: Write short notes on: Ridge regression.
A:
Q: - Find (49.3) -(00110110.0010) BCB (?) with BCD weight (8421) BCD 1
A: Convert (49.3)10 into BCD with weight (8421) is (01001001.0011)BCD ,Then
Q: 4. What are the amplitude, frequency, period, and phase of the following sinusoid signal? s(t) = 7…
A: We need to find the amplitude, period, frequency, and phase shift of the given signal.
Q: Baby Names: Each year, the government releases a list of the 10,000 most common baby names and their…
A: Java purpose: A research initiative to create cutting-edge software for numerous network…
Q: What global or local technologies are emerging that could be used to solve a current problem in…
A: Technology is the application of scientific knowledge to the practical purposes of human life, or,…
Q: b) Using the Product class above write a controller method called Index that Passes the title…
A: Here is the way to do it Create the controller method called as the index public ActionResult…
Q: A multicore processor is said to be sequentially consistent if all loads and stores appear to occur…
A: A core can be defined as the necessary registers and circuits that are required to perform a…
Q: Write a program that receives a list of integers and prints out that list after removing prime…
A: Python:- Python was created by Guido van Rossum and is an interpreted, object-oriented, high-level…
Q: python code
A: Given :- In the above question, the statement is mention in the above given question Need to use…
Q: write a javascript code to get the coordinates of mouse.
A: Introduction: The X and Y coordinates for the top left corner of the screen are (0, 0), which means…
Q: Provide ms SQL query to get branch name with employee name from below two tables using inner join…
A: CREATE TABLE employee_details( emp_id VARCHAR(8), emp_name VARCHAR(20),…
Q: Multiple choice questions. Choose correct answer i) Data mining may help scientists in A)…
A: We need to find the correct option regarding data mining statements.
Q: The BST can still store keys of the same value, in this case, we put a key that is less than a node…
A:
Q: Singly, Circularly, and Doubly Linked Lists
A: Given singly, circularly and doubly linked lists,
Q: What is the binary encoding of the following RISC-V assembly instruction? Please write your answer…
A: Solution : slli is an abbreviation for shift left logical immediate. So the instruction is x2 = x4…
Q: ALD G BI Understandability Manifestation Dimensionality Non-linearity Coupling Velocity…
A: The question has been answered in step2, according to bartleby guidelines we are supposed to answer…
Q: Q.32 Explain role of key distribution centre in symmetric system.
A: In cryptography, a key distribution center (KDC) is a system that distributes keys to users of a…
Q: Longest Common Subsequence: Example LCS for input Sequences “ABCDGH” and “AEDFHR” is “ADH” of length…
A: In this question we need to write a Java program to find the length of Longest Common Subsequence…
Q: Question 4 Which of the following Windows PowerShell commands enables an administrator to…
A: Remote Access Service in windows: RAS (Remote Access Service) allows remote access to client…
Q: What will be the output of the print statements below? String str1 = "Welcome"; String str2 = str1;…
A: Java programming language : On billions of devices, including laptops, smartphones, gaming consoles,…
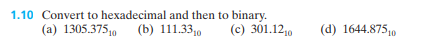
part C D
just convert to binary, don't bother with hex
Step by step
Solved in 2 steps with 3 images

- 31 Convert the hexadecimal IEEE format floating point single precision number 0x40200000 to decimal: First convert hex to binary (Provide a space between four bit groups. Example 111 1010 not 1111010) Sign bit Exponent in decimal after removing excess 127. Just the exponent. Example 3 not 23 Mantissa or Significand (Provide a space between four bit groups. Example 111 1010 not 1111010) Put it together and convert to decimalCalculate (3.41796875 *10-3 * 6.34765625 *10-3) by hand, assuming each of the values arestored in the 16-bit half precision format described in in the textbook. Assume 1 guard, 1 roundbit, and 1 sticky bit, and round to the nearest even. Show all the steps, and write your answer inthe 16-bit floating point format.Calculate (4.41762275 *10-3 + 6.34225625 *10-3) * 1.05225 * 102 by hand, assuming each of the values are stored in the 16-bit half precision format described in in the textbook. Assume 1 guard, 1 round bit, and 1 sticky bit, and round to the nearest even. Show all the steps, and write your answer in both the 16-bit floating point format and in decimal.
- 98. Usually, it takes 10-bits to represent one character. How many characters can be transmitted at a speed of 1200 BPS? a. 12 b. 120 c. 1200 d. 12000Calculate (3.41700875 *10-3 + 6.34005625*10-3)* 1.25625* 102 by hand, assuming each of the values are stored in the 16-bit half precision format describedin in the textbook. Assume 1 guard, 1 round bit, and 1 sticky bit, and round to thenearest even. Show all the steps, and write your answer in both the 16-bit floating point format and in decimal.1. List the octal and hexadecimal numbers from (16)10 to (32)10.2. Convert the following numbers with indicated bases to decimal.(a) (4310)5(b) (123)8(c) (2F A)16(d) (212)33. What is the largest binary number that can be expressed with:(a) 8 bits,(b) 10 bits,(c) 16 bits.In each case, write their decimal and hexadecimal equivalents.4. Determine the base of the numbers for the following operation to be correct: 54/4 = 135. Convert the hexadecimal number 68BE to binary, and then convert it from binary to Octal.6. Convert the decimal number 431 to binary in two ways:(a) Convert directly to binary.∗Engr. Sheraz Ali Khan, PhD 1 (b) First convert it into hexadecimal and then from hexadecimal to binary. Which is faster in youropinion?7. Express the following numbers in decimal:(a) (10110.0101)2(b) (26.24)8(c) (F AF A.B)168. Solve the following conversion problems:(a) Convert the decimal number 27.315 to binary.(b) Calculate the binary equivalent of 2/3 to eight places after the binary point.…
- Question5) Given Two Integers 11 and 9 how many binary bits are required to represent the larger one?A. How many bits are needed to represent 214(octal) in binary?B. Show the 2’s complement binary (10 bits) representation of (-246)(10)C. Convert the following 2’s complement binary number to decimalrepresentation:10010010a) Use the two’s complement binary representation to represent each of the following integers as 10-bit binary numbers. i) -13710 ii) 14510 iii) -15810 iv) 16710 v) -11510 b) If an 8-bit binary number is used to represent an analog value in the range from 0 to 100kg, what does the binary value 011001002 represent?
- 1. Assume numbers are represented in 8-bit two's complement Show the calculation of the following: a) 5 + 10 b) 5 – 10 c) -5 + 10 d)-5 – 10 2. Represent the following decimal numbers or values according to the given requirements: a) +4 in both binary sign/magnitude and two's complement b) -6 in both binary sign/magnitude and two's complement c) -85 in two's complement d) +52 in two's complement 3. Find the following differences using twos complement arithmetic: a) 001000 – 110111 b) 10100101 – 011110 c) 100100001011 – 101010110011 d) 10011011 – 10100101given the 16 bit value 1001101011001101 . what operation must be performed in order to see to 1 the last eight bits?What decimal value does the 8-bit binary number 10010110 have if it is represented using Excess-M representation? a) If high-order interleaving is used, where would address 37 (base 10) be located? b) If low-order interleaving is used, where would address 28 (base 10) be located

