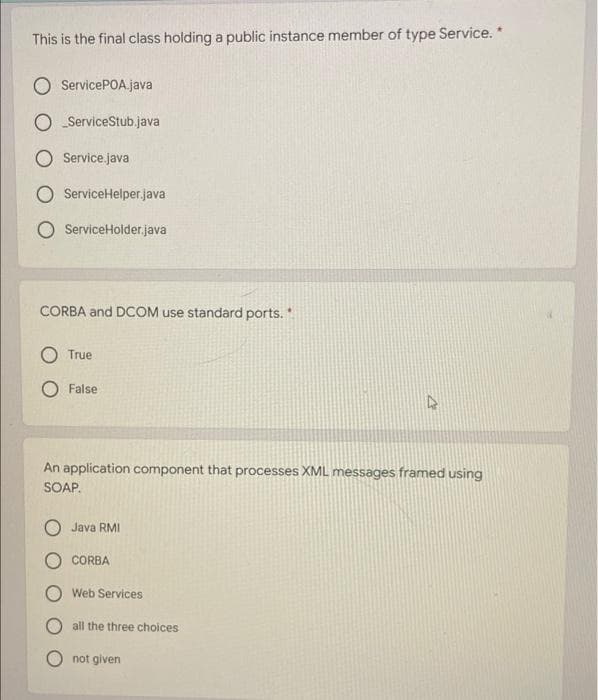
CORBA and DCOM use standard ports. True False 4 An application component that processes XML messages framed using SOAP. Java RMI CORBA Web Services all the three choices not given
Q: please i need run this code in posspile time import random import matplotlib.pyplot as plt def…
A: Python has a library for plotting called "matlablib". This library has several functions to plot the…
Q: Carrying out your own research, discuss the benefits and drawbacks of Apple transitioning to ARM-…
A: ARM processors are very friendly than Intel CPUs and they can be the future of cloud computing…
Q: True statement(s) about online form design * Possible many answers User participation will make the…
A: Which of the following claims about online form design efficiency is/are true?
Q: When talking about an operating system, what precisely does it imply when someone says they have a…
A: Given: RAID, or "Redundant Arrays of Independent Drives," is a technique for improving speed, data…
Q: Problem: Write a C++ program for discount computation that can be used in a store. However, only…
A: #include <iostream> using namespace std; int main() { int amount; double discount;…
Q: Provide me with the MATLAB code to swap the first and last row of the matrix given below, mat = 1111…
A: Provide me with the MATLAB code to swap the first and last row of the matrix given below, mat = 1 1…
Q: e the key differences and software designed between the development of for general-purpose…
A: Below the key differences between the development of software for embedded systems and software…
Q: Which of the following lambda expressions is/are correct for multiplying two numbers and returning…
A: Correct answer will be Option c.
Q: Q4: Sketch the state diagram for a Mealy sequential circuit which investigates a single input…
A: Answer is given below-
Q: the need for application virtualization
A: Given :- In the above question, the statement is mention in the above given question Need to…
Q: What types of calculations are expected to be carried out solely by artificial intelligence under…
A: Introduction: Not everyone was aware of what it was or how it might affect their firm. They were…
Q: What are some of the challenges that come with building software for embedded devices?
A: Overview: Embedded software development presents a number of obstacles, including security,…
Q: What are the various approaches to database master data management (MDM)?
A: Master data management (MDM) : It is the core process that is generally get to manage, centralize,…
Q: What is the difference between native and web-based apps in terms of software development?
A: A native app is one that is built for a specific platform such as iPhone or Android, using their…
Q: Only one-third of mobile development projects were effective in satisfying project objectives in…
A: Given: In today's businesses, mobile apps have become synonymous with easy communication and…
Q: Only one-third of mobile development projects were effective in satisfying project objectives in…
A: Given: In today's businesses, mobile apps have become synonymous with easy communication and…
Q: What is the difference between cloud computing and grid computing, and how do you choose between the…
A: Answer:
Q: Write a regular expression that describes the language accepted by this FSA (the alphabet is {a,…
A:
Q: Keeping in mind the various definitions of operating system, consider whether the operating system…
A: Introduction: An operating system serves as a bridge between a PC client and PC hardware.
Q: What are the names of the three operations that are the most fundamental in the field of…
A: Cryptography-: Cryptography is the investigation of secure interchanges strategies that permit just…
Q: What is Password, and what are the many ways to get it?
A: What exactly is Password, and what are the many ways to it? Answer: What is a password? A password…
Q: When it comes to computer systems, what precisely differentiates architecture from computer…
A: Computer Architecture: Computer architecture specifies what a computer can accomplish, while…
Q: Describe the differences between structured and unstructured data. Explain structured data in a…
A: Introduction: Data is critical in making business decisions. The ability of a corporation to gather…
Q: TRUE OR FALSE 1. It is possible to traverse the elements of a Set without using an Iterator? 2.…
A: NOTE :- Below i explain the answer in my own words by which you understand it well. Answer ( 1…
Q: It is essential to have a solid understanding of what an IP address is as well as the role it plays…
A: Introduction: IP (Internet Protocol) address: An IP address, often known as a unique address, is…
Q: is meant by the term "dyna e, and how can its perform.
A: Dynamic scoping is a surprising perspective on dialects. Lexical scoping is the kind of scoping that…
Q: What are the benefits of using programming methodologies that operate in an asynchronous fashion?…
A: Given: Asynchronous programming is a parallel programming method in which little portions of…
Q: What do you think are the most significant factors to take into account when selecting an operating…
A: Given: Things to take into account while picking an operating systemA high degree of dependability…
Q: What are two of virtualization's expected operating system ramifications?
A: Before establishing an image deployment process for physical servers, administrators must consider…
Q: The seven design considerations for object-oriented languages that were covered in this chapter may…
A: Introduction Procedures for Security: Every business has something that others desire. Someone may…
Q: It is essential to have a solid understanding of the many challenges that are faced by embedded…
A: Given: Embedded software development presents a number of obstacles, including security,…
Q: In terms of throughput speed, wireless networks are faster than wired networks; nevertheless, the…
A: Wired networks are faster than wireless networks: Wired connections transmit more data than Wi-Fi…
Q: The MetaData component of the architecture is the one that is considered to be the most important…
A: Definition: In response to the question The database is built on the central webpage. RDBMS…
Q: What exactly is meant by the term algorithmic cost modeling? What makes this method distinctive in…
A: A mathematical technique known: As algorithmic cost modelling is used to make cost projections for…
Q: In the context of computer graphics, please explain what is meant by "local" and "global" lighting,…
A: Start: Global lighting includes reflections, refractions, and shadows. One object's modeling impacts…
Q: What is the importance of linux partitioning?
A: What is the importance of linux partitioning?
Q: Clarify the meaning of the term "fuzzy logic." Could you provide me an example from the field of…
A: The following is the rule for the input-output table: To determine the equivalent output number,…
Q: In a few phrases, explain what a star schema is and how it is used in data architecture for business…
A: Intro SCHEMA DES STARS - Star schema is a mature modeling technique or methodology that is commonly…
Q: What is open source in computer science?
A: The correct answer is given below with explanation and example
Q: Discuss numerous approaches to initialising a 1D array in C. Discuss their memory representations as…
A: Intro An array is a collection of one or more values of the same type. Each value is called an…
Q: Why isn't "store-and-forward network" technology used in general communications any longer? Also,…
A: Solution: Store and forward packet-switching ensure high-quality data packet delivery. Because…
Q: 3. Which of the following is a SQL aggregate function a) AVG b) LEN c) LEFT d) JOIN
A: SQL aggregate functions
Q: used for declaration for all forms global O dim form
A: used for declaration for all forms
Q: What is open source in computer science?
A: here in the question ask what is the open source in computer science.
Q: When you refer to "fuzzy logic," can you perhaps explain precisely what you mean by that?
A: Definition: Fuzzy logic is a method of variable processing that allows for the processing of…
Q: What are the names of the three operations that are the most fundamental in the field of…
A: The cryptography can be denoted as the study of techniques for secure communication in the presence…
Q: Various data centers are now using cloud computing architectures such as Big Data Cluster for their…
A: Big data refers to the information that contains more prominent varieties, showing up in expanding…
Q: 1. Which SQL statement inserts data into a table called Projects? a) INSERT Projects ('Content…
A: Introduction: Structured Query stands for Structured Query Language. Language is a programming…
Q: In an online class, what are the drawbacks that come along with a lack of technology capabilities…
A: In this question we have to understand what are all the drawbacks that come along with the lack of…
Q: In what cases would you advocate the use of assembly language code in the creation of application…
A: Introduction: Mnemonic codes, analogous to English words, are used in assembly language. Although…
Step by step
Solved in 2 steps

- Java Programming: Below are BooleanCompareNode.java, VariableReferenceNode.java, IfNode.java, RepeatNode.java, & WhileNode.java. Attached is an image where it's circled in blue all the methods that must be implemented in the java files that are presented below: BooleanCompareNode.java public class BooleanCompareNode extends Node {enum CompareType { eq, ne, lt, gt, le, ge }; CompareType type; Node left; Node right; public BooleanCompareNode(CompareType type, Node left, Node right) { this.type = type; this.left = left; this.right = right; } public String ToString() { return left.toString() + type.toString() + right.toString(); } } VariableReferenceNode.java public class VariableReferenceNode extends Node{String name; Node arrayIndex; public VariableReferenceNode(String name) { this.name = name; this.arrayIndex = arrayIndex; } public String ToString() { String indexString = (arrayIndex == null) ? "" : "[" + arrayIndex.toString() + "]"; return name + indexString; } public…Can i please have help with this question in java, please . Java is the language java kind regars Create a class called Citizen with the following attributes/variables:String citizenID ,String citizenName ,String citizenSurname ,String citizenCellNumber ,int registrationDay ,int registrationMonth ,int registrationYear Create a class called Node with the following attributes/variables:Citizen citizen , Node nextNode Create a class called CitizenRegister with the following attributes/variables:a. Node headNodeb. int totalRegisteredCitizens Add and complete the following methods in CitizenRegister: a. head() i. Returns the first citizen object in the linked listb. tail() i. Returns the last citizen object in the linked listc. size() i. Returns the totalRegisteredCitizend. isEmpty() i. Returns the boolean of whether the linked list is empty or note. addCitizenAtHead(Node newNode) i. Adds a new node object containing the citizen object information before the…How do I write this code in groovy: Also kindly share any material or tool that allows one to convert his java code to Groovy:@Component public class RequestResponseLoggingInterceptor implements ClientHttpRequestInterceptor { private final Logger log = LoggerFactory.getLogger(this.getClass()); private Tracer tracer; RequestResponseLoggingInterceptor(Tracer tracer){ this.tracer = tracer;} @Override public ClientHttpResponse intercept(HttpRequest request, byte[] body, ClientHttpRequestExecution execution) throws IOException {Span span = tracer.currentSpan(); HttpHeaders headers = new HttpHeaders(); headers.set("X-B3-Traceid", span.context().traceId()); headers.set("X-B3-SpanId", span.context().spanId()); headers.set("X-B3-ParentSpanId", span.context().parentId()); request.getHeaders().addAll(headers); ClientHttpResponse response = execution.execute(request, body); return response; }}
- Design a program using Java - Apache NetBeans. With the following enum class:public enum Day {SUNDAY, MONDAY, TUESDAY, WEDNESDAY,THURSDAY, FRIDAY, SATURDAY}Create a second class called enumDayMood with a void method call telDayMood ().This method contain a switch case as follows:switch (day) {case MONDAY:JOptionPane.showMessageDialog (frame, "Mondays are bad.");break;case FRIDAY:JOptionPane.showMessageDialog (frame, "Fridays are better.");break;case SATURDAY: case SUNDAY:JOptionPane.showMessageDialog (frame, "Weekends are best.");break;default:JOptionPane.showMessageDialog (frame, “Midweek days are so-so.");break;}Create a method that will ask the user to enter a day of a week and the program should tell the mood of the day. If the user enter a wrong value the program should exit with 0. Use Apache NetBeans to create this program and submit all screenshots of your program output and the java codeDesign a program using Java - Apache NetBeans. With the following enum class:public enum Day {SUNDAY, MONDAY, TUESDAY, WEDNESDAY,THURSDAY, FRIDAY, SATURDAY}Create a second class called enumDayMood with a void method call telDayMood ().This method contain a switch case as follows:switch (day) {case MONDAY:JOptionPane.showMessageDialog (frame, "Mondays are bad.");break;case FRIDAY:JOptionPane.showMessageDialog (frame, "Fridays are better.");break;case SATURDAY: case SUNDAY:JOptionPane.showMessageDialog (frame, "Weekends are best.");break;default:JOptionPane.showMessageDialog (frame, “Midweek days are so-so.");break;}Create a method that will ask the user to enter a day of a week and the program should tell the mood of the day. If the user enter a wrong value the program should exit with 0. Important: Use Apache NetBeans to create this program and submit all screenshots of your program output and the java codeWrite a class encapsulating the concept of a student, assuming student has the following attributes: a name, a social security number, and a GPA (for instance 3.5). Include a constructor, the accessors and mutators, and methods toString() and equals(). Write a client class to test all the methods in your class.
- Below I have a sample class written in java and have several methods. I have only written the skeleton code for sample. Implement a simple proxy design pattern using java so that clients should only have access to very basic methods, while administrators of the system should have access to all methods public class Student { private name; private ID; private Grade; public double getname () {} public string getID () {} public double calculateGrade() {} }Create a Triangle class that extends the SimpleGeometricObject class in Eclipse, followingthe below UML diagram. Use the following formula to calculate the area of a triangle:A = 1/2 × base × height the SimpleGeometricObject code is below in link and picture https://liveexample.pearsoncmg.com/html/SimpleGeometricObject.html the ending part of the code that didnt appear in the picture } /** Return a string representation of this object */ public String toString() { return "created on " + dateCreated + "\ncolor: " + color + " and filled: " + filled; } }Write something about all of the following JAVA research: TDD JUnit Annotations such as @Test @BeforeClass @AfterClass @After @Before JUnit Assertions such as assertEqual assertTrue The resource: The link: Why it's great:
- Create a class FacebookLikeManager with three public methods. The purpose of this class is to ingest this users.txt file and process it as to later provide information about those users. users.txt Mike: Kristen, Sara, Nate, Anthony, Randy Kristen: Mike, John, Steve, Bill Bill: Sara, Nate Sara: Nate, Anthony A line in the file will look something like this: Mike: Steve, John, Tony This line represents that the users Steve, John, and Tony have liked the user Mike. The three public methods will be: a public List<String> getAllUsers() This will return a unique list of all users that appeared in the file. Note: All names in the file are users. Even if a user only appears when liking someone, they will be present in the List returned by getAllUsers. b public List<String> getLikes(String user) This will take a String representing a user (like “Mike”) and return a unique List containing all of the users that have liked the user…Can i please have help with this question in java, please read the intructions and write down the code not to post a picture Java is the language java kind regars Create a class called Citizen with the following attributes/variables:String citizenID ,String citizenName ,String citizenSurname ,String citizenCellNumber ,int registrationDay ,int registrationMonth ,int registrationYear Create a class called Node with the following attributes/variables:Citizen citizen , Node nextNode Create a class called CitizenRegister with the following attributes/variables:a. Node headNodeb. int totalRegisteredCitizens Add and complete the following methods in CitizenRegister: a. head() i. Returns the first citizen object in the linked listb. tail() i. Returns the last citizen object in the linked listc. size() i. Returns the totalRegisteredCitizend. isEmpty() i. Returns the boolean of whether the linked list is empty or note. addCitizenAtHead(Node newNode) i. Adds a new node object…The three java files (source code) pasted below associated with this question. Any help will be greatly appreciated!! QUESTION (using Eclipse and default Junit package that came with it): Create a Junit 4 test case for the Hourly class. Your test should use these methods from class org.junit.Assert: assertEquals to test the getJob() method assertEquals to test the getPayRate() method assertTrue to test the hours attribute Admin.java package ch44extra; import java.time.LocalDate; public class Admin extends Person { private String dept; private String office; private double salary; //private double budget;removed to simplify class public Admin(String name, LocalDate date, int id, String dept, String office, double salary) { super(name, date, id); this.dept = dept; this.office = office; this.salary = salary; } public Admin() { super(); // TODO Auto-generated constructor stub } public String getDept() { return dept; } public void setDept(String dept) { this.dept = dept; }…











