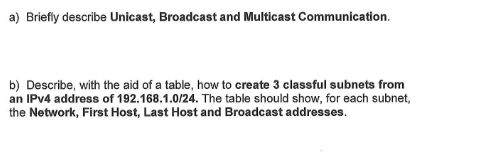
create 3 classful subnets f
Q: It is widely acknowledged that creating appropriate security policies and consistently enforcing…
A: Security policy A security policy is a record that states in writing the way in which an…
Q: John von Neumann's life and accomplishments have what significance?
A: Von Neumann, John: Mathematician John von Neumann was of Hungarian descent. He was born in Budapest…
Q: How can you use your knowledge of compressed zip files and folders to improve your career prospects?
A: ZIP files and folders with compression The files that combine one or more computer files into a…
Q: Using Excel, what does it imply when a cell has hashtags?
A: The answer of the question is given below
Q: What are the benefits and drawbacks of cloud storage?
A: Cloud Storage: Cloud storage has enabled clients to share and access records from a distance without…
Q: It is important to analyze and compare the concepts of virtual machines and virtual memory. What are…
A: Comparisons based on definitions: The virtual machine is meant to provide each operating system the…
Q: What may happen to a company's cybersecurity in the case of a data breach? Explain
A: A data breach occurs when unauthorised individuals get access to sensitive information that has been…
Q: The latency of accesses between various tiers of the memory hierarchy is decreased with the aid of…
A: Full jackknife computational complexity: The jackknife resampling method provides more accurate…
Q: With so much communication occurring on-line today in fact, it's not unusual to find people in…
A: 1. With so much communication occurring on-line today in fact, it's not unusual to find people in…
Q: List the distinctions between divide-and-conquer and dynamic programming.
A: Introduction: A set of instructions that instructs the computer on how to carry out specific…
Q: Which kind of program-level parallelism, control or data, is more appropriate for SIMD? What kind of…
A: Parallelism at the programme level: Program-level parallelism is the process of decentralizing a…
Q: The word "local area network" should be defined.
A: Definition: A local area network (LAN) is a network made up of a number of computers that are…
Q: What are the base tags of the following input (limit switch) and output (limit light) in…
A: The following solution is
Q: What are the best results in terms of healthcare data/cybersecurity breaches?
A: Introduction: Health informatics and other experts have a significant role in ensuring that medical…
Q: Your company's information systems may be malfunctioning. It is possible to cope with it in a…
A: Given: People, technology, and software make up management information systems (MIS), which aid in…
Q: Hi, can you please solve clearly? Thanks Use powers to rewrite these problems: a. xxxx b.…
A: Use powers to rewrite these problems: a. xxxx b. 6*6*6*6*sss*tt c. xx*xxx d. t*t*t*t
Q: Q3. Let Σ = {a, b}. Let BDFA = {(M) M is a DFA that accepts some string containing an equal number…
A: Here we have given solution for the given problem, You can find the solution in step 2.
Q: Clearly explain the CNSS security concept. What are the three dimensions of the object?
A: The CNSS security model is a three-dimensional model that was created in 1991 by John McCumbers.…
Q: What are some of the most recent trends in cybercrime to keep an eye out for? How prepared are you…
A: GIVEN: Which current trends in cybercrime should you be aware of? How should law enforcement respond…
Q: Write detailed description of how I/O devices work and how they are programmed ?
A: Computer System comprise of three components: Input Device: These device is use to enter user data…
Q: What are the possible repercussions of AI and robots in terms of social and ethical implications?…
A: Introduction: Artificial intelligence is a branch of computer science that involves developing…
Q: For a high-performance network, MPLS combines the richness of IP with the performance of ATM.
A: The Answer start from step-2.
Q: Q6 In Python implement a recursive function named test() that accepts an integer parameter. If the…
A: Student :- 1. I will provide the code 2. I will provide the output
Q: Develop a program that implements a function named largerThanN that accepts three arguments: an…
A: C++ Program: #include<iostream>using namespace std; // function named largerThanN that accepts…
Q: In a variety of methods, MicroStrategy produces intelligent cubes.
A: Given: In Micro Strategy, intelligent cubes can be created by selecting either a public folder or a…
Q: Why is a company's cyber security vulnerable, and what are the risks and repercussions?
A: We need to discuss the causes of company's cyber security vulnerability.
Q: Please explain if the following passwords are suitable options or not: Aristotle, Washington,…
A: Describe Washington, D.C. Rather of being a state, Washington, DC is a district. DC is an…
Q: When and by whom was the first tablet computer developed?
A: The initial tablet: In addition to being necessary for personal computing, a portable or handheld…
Q: What is the effect of switching costs on the danger of buyer power?
A: The bargaining power of buyer is a part of porters 5 forces analysis, it is the power which buyer…
Q: What various types of programming paradigms are there? So why are there so many different paradigms?…
A: Programming paradigms classify languages based on their properties. There are several linguistic…
Q: It is necessary to briefly describe and define the fundamental structural elements of a computer.
A: The question has been answered in step2
Q: What is artificial intelligence's (AI) ultimate goal? Give two instances to highlight the importance…
A: Intelligent machines: The functions of human intelligence are mimicked by artificial intelligence…
Q: Is there a date when 3D printing was first introduced?
A: Definition: Early 1980s Japan saw the development of 3D printing in its earliest known forms. Hideo…
Q: What different artificial intelligence approaches are there? Give a clear explanation of your ideas…
A: Artificial intelligence approaches? There are 4 different types of approach: Reactive machines.…
Q: What are some benefits that may be obtained by employing dynamic programming?
A: Lets understand the dynamic programming benefits by using a simple example: let f(n) be function…
Q: In a variety of methods, MicroStrategy produces intelligent cubes.
A: Introduction: This is the most frequently mentioned MicroStrategy inquiry question. Shrewd 3D…
Q: What is the purpose of wear leveling in SSDs?
A: Leveling of wear: Wear levelling is a technique for distributing erase-write operations uniformly…
Q: When it comes to protecting consumer data from unauthorized access, what measures should businesses…
A: Introduction:Since the prevalence of remote work, digitization, and cybersecurity concerns is on the…
Q: Google Docs vs. Office 365: Which is better?
A: to discuss whether Google Docs or Office 365 is superior. Google Documents A web-based word…
Q: What exactly is intellectual property, and how does it affect the legality of software development?
A: The solution to the given question is: Information Technology Information Technology is used to…
Q: Write a python program that takes two lists, merges the two lists, sorts the resulting list, and…
A: HERE IS COMPLETE PYTHON PROGRAM REGARDING YOUR PROBLEM :
Q: In the following series of problems, suppose we have a virtual memory system with the following…
A: We are given page size, number of physical memory pages, number of page table entries in a single…
Q: B 1 A 7 с 2 N E F 10 G
A: We are given a graph with 7 vertices and it contains edges with weights in it. We are going to draw…
Q: Q5. Let XDFA = {(A)| A is a DFA and L(A) is an infinite language}. Show that XDFA is decidable.
A: Answer :-
Q: CUSTOMER PK CUS CODE CUS LNAME CUS FNAME CUS INITIAL CUS AREACODE CUS PHONE CUS BALANCE HE generates…
A: Below I have provided the SQL query of the given question:
Q: Why do ICMPv6 Neighbor Solicitations seem to be transmitted as multicasts as opposed to broadcasts?
A: Solution: All stations connected to the network receive messages provided with a broadcast address.…
Q: Explain the differences between a random forest and a decision tree in one or a few words at most.…
A: Introduction: Decision trees and random forests Forest tree at random: A random forest tree is just…
Q: Definitions of acidosis and alkalosis are provided. In this system, what role do buffers play?
A: Buffers:- A buffer is solution that resists pH changes when an acid or base is added to it. It may…
Q: What advantages and disadvantages come with formal methods? There should be at least four good…
A: The formal method is worried about the utilization of a numerical procedure to plan and execute the…
Q: Assume that every 18 months, the number of cores that are available on a new generation of CPUs…
A: According to the described scenario, the CPU's core count will double once every 18 months (or one…
Step by step
Solved in 2 steps with 3 images

- 57- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; What will be the range of usable (assignable) host addresses in Subnet C? Select one: A. 192.168.15.64 to 192.168.15.128 B. 192.168.15.97 to 192.168.15.110 C. 192.168.15.140 to 192.168.15.191 D. 192.168.15.128 to 192.168.15.139 E. 192.168.15.193 to 192.168.15.25458- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method What will be the network address of Subnet D? Select one: A. 192.168.15.232 B. 192.168.15.191 C. 192.168.15.112 D. 192.168.15.24053- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; and What will be the network address of Subnet B? Select one: A. 192.168.15.64 B. 192.168.15.0 C. 192.168.15.32 D. 192.168.15.1
- 56- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; What will be the subnet mask of Subnet C? Select one: A. 255.255.128.255 B. 255.255.192.0 C. 255.255.255.240 D. 255.255.255.192 E. 255.255.255.12852- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; What will be the subnet mask of Subnet A? Select one: A. 255.255.255.192 B. 255.255.128.255 C. 255.255.255.128 D. 255.255.192.192 E. 255.255.192.060- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; What will be the range of usable (assignable) host addresses in Subnet D? Select one: A. 192.168.15.224 to 192.168.15.255 B. 192.168.15.113 to 192.168.15.118 C. 192.168.15.192 to 192.168.15.254 D. 192.168.15.193 to 192.168.15.240 E. 192.168.15.192 to 192.168.15.239
- 13.9 What is the purpose of an IP address mask? Suppose an IP address is identified as 222.44.66.88/24. What is the network address in this case? What is the host address? How many hosts can this network address support? Repeat this exercise for the IP address 200.40.60.80/26. 13.10 Explain the concept of a DHCP lease. How is it obtained? How is it used? What does it provide? 14.5 In recent years, much of the storage and communication of data has been in digital form, even if the source data is actually analog. Even most television is now transmitted digitally. What benefits and advantages are gained by using digital storage and signaling?1-In a network based on the bus topology, the bus is a non-shareable resource for which the machines must compete in order to transmit messages. How is deadlock controlled in this context? 2-Using 32-bit Internet addresses was originally thought to provide ample room for expansion, but that conjecture is not proving to be accurate. IPV6 uses 128-bit addressing. Will that prove to be adequate? Justify your answer’ (for example, you might compare the number of possible addresses to the population of the world).8. Answer the questions below based on the given network topology: (a) How many collision domains are there? (b) How many broadcast domains are there? (c) What type of cable (straight-through or crossover) is required to connect PCO and Switch0? (d) What type of cable (straight-through or crossover) is required to connect two PCs? (e) If PCO wishes to discover the MAC address of PC1, which network protocol should be utilized?
- 1.0. Suppose that Internet routing in the US used geographical routing, and the first 12 bits of every IP address represent a geographical area similar in size to a telephone area code. Megacorp gets the prefix 12.34.0.0/16, based geographically in Chicago, and allocates subnets from this prefix to its offices in all 50 states. Megacorp routes all its internal traffic over its own network. (b). Now suppose each office has its own link to a local ISP, but still uses its 12.34.0.0/16 IP addresses. Now what is the route of traffic between the San Diego office and its neighbor?3.1 An end device was given the IP address of 198.168.4.35/28. Consider this address and indicate: 3.1.1 The network ID/address to which the host belongs. 3.1.2 The network broadcast address to which the host belongs. 3.1.3 The total number of hosts available in the network. 3.1.4 The total number of networks. 3.2 Consider two neighbours, Alice and Bob. Each have wireless IPv4 routers with integrated NAT. Each neighbour connects their laptop to their own wireless router, and each uses appropriate utilities to examine the IP address of each laptop. They realise the laptops have the same IP address. 3.2.1 How is that possible? 3.2.2 Justify one reason that wide-spread deployment of IPv6 would remove the need for the NAT devices.42. Though there are practical reasons why we don't complicate our lives this way in the real world, from a theoretical perspective we could borrow non-consecutive bits for subnetting. So, when borrowing the first host bit, the second host bit and the last two host bits (counting from the left of the host bit field) from 172.1.0.0 can you determine the following: a. subnet maskb. network address for 0th subnet, 1st subnet and 2nd subnet?c. total number of subnets and number of useable subnets?

