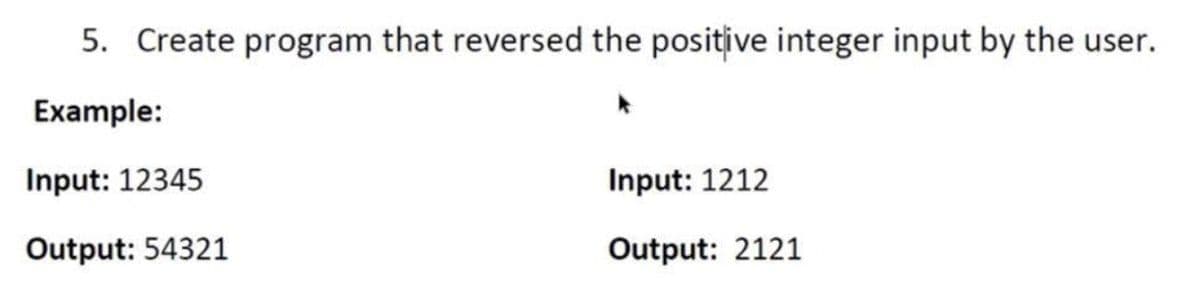
Create a C# program that reversed the positive integer input by the user
Q: What are the advantages of cloud computing in comparison? What are the potential drawbacks and…
A: Answer: Rapid Scaling takes into consideration speed and license availability, and is particularly…
Q: Which two strategies do you believe are the most effective in terms of database security?
A: Introduction: Database security refers to a set of techniques intended to protect database…
Q: This program inputs ten integers into an array (a) and then create a new array (b) that represent…
A: 1-InputBox("a") 2-For i = 10 to 1 3-b(i) = a(11 - i)
Q: i need the answer quickly
A: Brother what you want to ask? Please mention question
Q: How important are flowcharts and technical drawings to you, as a student, in the maintenance of…
A: Introduction: Flowcharts are commonly used in technical analysis and programming to help with…
Q: This code calculate the SUM of elements in each column of array T(5,3) and stored in array K(3). For…
A: Answer: The right choice for the given code snippet is option D. 1-For J = 1 To 5 2-Sum = 0 3-For I…
Q: The conditions that advise the database designer to make advantage of supertype and subtype…
A: When a generic object is associated with several subtypes, it is referred to as a supertype. A…
Q: OUTPUT char arr [3] [3] = { {'A', 'H', 'B'}, {'T', 'K', 'N'}, {'D', 'I', 'G' } }; for (int k=1;…
A: According to the information given:- we have to explain how the code is traverse and give the…
Q: de segment elements for the array M(10) using input box, then calculate the product (the result of…
A: Option(4) is correct. Firstly a variable P is initialized as 1. Then we multiply array elements if…
Q: The design of systems has been impacted by personal computers and the internet. Use examples to…
A: Launch: System architecture is influenced by two technical advances: Internet \computer As a…
Q: Network O Data Storage O All of above O Other: Highly trained, writers of the software instructions…
A: let us see the answer: 1) The correct option is All of the above. 2) The correct option is…
Q: What are some of the advantages of utilising cloud computing? The usage of cloud computing is not…
A: Intro For over two decades, cloud computing has been accessible: Despite data demonstrating…
Q: Do you want to discuss Big Data, how businesses utilize it today, and the motivations for doing so?
A: Definition: Big data is a collection of organized, semi structured, and unstructured data that may…
Q: In order to teach dynamic programming, you should use examples from the actual world.
A: Dynamic programming examples from the actual world:- We use dynamic programming in travelling…
Q: A rising number of firms are starting to use big data today. Discuss it, as well as the business's…
A: The following is based on the information provided: We must define Big Data in terms of how and why…
Q: DNS records must be ordered in descending order by record type. Please provide a simplified…
A: Intro DNS Records: DNS records (also known as zone files) on authoritative DNS servers give a…
Q: How does edmodo employ texting to entertain.
A: Definition: Edmodo's all-in-one LMS, communication, collaboration, and Zoom video conferencing…
Q: In C++ only Today is the birthday of Rajesh. He wants to buy sweets for his friends so he went to…
A: Please note that for the sake of a better display of output, I have mentioned a 'cout<<"no of…
Q: Which metrics are most important to take into account while creating embedded systems for your…
A: Definition: The inquiry seeks information on five criteria related to embedded systems that should…
Q: What is the length of the polar curve below? 3π r = 6 cos (0) for 0 ≤ 0< 4
A: The arc length of polar curve is given by :- ∫αβ (r2+(dr/dθ)2 )1/2 dθ Now, r=6cosθ => r2=36cosθ2…
Q: When assembling a software development team, a number of variables must be considered. What are the…
A: Answer: We need to write most effective strategies duties among several individuals while software…
Q: Which kinds of problems lend themselves particularly well to the use of dynamic programming, and why…
A: Given: Under what conditions can dynamic programming become more successful, and why do we choose…
Q: How can you utilize heuristics to improve the design of your system?
A: The Use of Heuristics in Design: System standing visibility By showing status information on the…
Q: What is the current status of the literature review on social media rumor?
A: Intro: A literature review looks for and examines the existing literature on a certain topic or…
Q: It is possible to develop and construct HTML-based apps to demonstrate the Search Tree Structures…
A: Introduction: No, using HTML to create and construct applications to show the usage of the Search…
Q: As you construct the framework, it is important to evaluate the problems and obstacles that may…
A: Start: The term "cloud computing" refers to a model in which computer resources, including as…
Q: Embedded systems are distinguished by a variety of properties.
A: Given: In the following paragraphs, I will describe the solution using my own words so that you will…
Q: Q4/ write a program to calculate and print the area and circumstance for any circle (the radius must…
A: 1. declaring radius circumference and area of float type. 2. initializing the value of pi as 3.14.…
Q: In the field of automotives, what exactly is the function of an embedded system, and do you have any…
A: Embedded system: An embedded system's adaptability and flexibility make it vital in autos. An…
Q: It's possible that the phrase "embedded system" causes confusion. There are many different…
A: Embedded system: An embedded system is a set of computer hardware and software that is intended to…
Q: In C++ only Today is the birthday of Rajesh. He wants to buy sweets for his friends so he went to…
A: Input/Output Details First line contains T, the number of testcases. Each testcase contains a single…
Q: What models constitute the Software Development Life Cycle?
A: Given that : SDLC model is an organised development process with continual product improvement. SDLC…
Q: What are the ramifications of seeing human rights as just aesthetic moral components of scientific…
A: Intro What do we mean when we talk about human rights? In everyday life, human rights are nothing…
Q: This program inputs ten integers into an array (a) and then create a new array (b) that represent…
A: Answer: 1-a(i) = InputBox("a") 2-For i = 10 To 1 Step -1 3 - b(i) = a(10 - i)
Q: As a software engineer, you're asked to create a hospital patient control app. Proposed process…
A: Introduction: The fundamental goal for developing hospital management systems was to help hospitals…
Q: Describe the actions that are typically associated with the design and implementation services…
A: Answer: While designing and implementation services provided by the DBA's some point kept in mind so…
Q: Question 1 R can connect to which of the following types of relational databases? O MySQL All…
A: In the given question R can connect to All listed,plus more types of relational databases.
Q: An engineer has designed a FAT-like system and he has used 24 bits for each entry. For a 32-GB disk,…
A: The size of each entry:-24 bits Size of the disk:-32 GB
Q: Given network: 101.202.0.0 Design three subnetworks: N1, N2 and N3. N1 needs 900 ip addresses for…
A: As per our guidelines, only one question will be answered. So, please repost the remaining question…
Q: What criteria should be addressed while creating an effective Disaster Recovery plan?
A: The checklist for the disaster recovery plan includes identifying critical IT systems and networks,…
Q: i need the answer quickly
A: What you want to ask?
Q: When it comes to social media and online communication, there are more options to deceive people in…
A: Introduction: Communication and relationships are increasingly centered on technology and media in…
Q: What are the three choices that could be used in a project based on your decision tree structure?…
A: The above question is solved in step 2 :-
Q: Do relational databases and relational algebraic models have any kind of relationship with one…
A: Introduction: A relational database is a collection of data elements that are linked by predefined…
Q: What percentage of people use Wi-Fi and cellular networks?
A: Introduction: Cellular networks are mobile networks used to access a network across a large region.…
Q: *What are the key distinctions between verilog and system verilog? What sets a structural module…
A: System Verilog has been referred to be the first hardware description and verification language…
Q: What are the key differences between dynamic programming and traditional programming?
A: The above question is answered in step 2 :-
Q: Please include a description of the user training that will be a part of this implementation…
A: The user training component of this implementation strategy will be described: It is crucial to…
Q: What is the state of the literature evaluation on social media rumor?
A: Introduction: There is a good impact on business politics and socializing, as well as some negative…
Q: +CC Q1/ Write a program to enter two number then enter one of the arithmetic operations(+,-,*,%),…
A: Code in step 2
Create a C# program that reversed the positive integer input by the user.
Step by step
Solved in 4 steps with 3 images

- Create a program that will get 2 numerical inputs and output if the first number is greater or lesser than or equal to the second numberWrite a program that reads integers between 1 and 100 and counts the occurrences of each. Assume the input ends with 0. Write a program that reads integers between 1 and 100 and counts the occurrences of each. Assume the input ends with 0. Here is a sample run of the program: Enter integers from 1-100 (input 0 value to end inputs): 2 5 6 5 4 3 23 43 2 02 occurred 2 times3 occurred 1 time4 occurred 1 time5 occurred 2 times6 occurred 1 time23 occurred 1 time43 occurred 1 timeCreate a program that takes a value as an input from the keyboard and outputs the factorial of that number; the factorial of an integer n is: n *(n - 1) *(n - 2) *... *3 *2 *1. For instance, the factorial of 4 is: 4 *3 *2 *1, or 24. The values entered by the user are integers.
- Write a Little Man Computer program that converts a given Little Man number into a number using the base-10 number system. . For example, if the user provides the inputs 0, 0, 0, 1, 2, 2, then this will be the equivalent of XVVII.Write a program which repeatedly reads several people's height numbers in cm(centimeter) until the user enters "done". Once "done" is entered, print out the max, min, and average of the height numbers. Correct height data should be number between 50cm and 250cm. If the user enters number out of the range, or anything other than a number, detect the mistake and print an error message and skip to the next number. Sample input and output: Enter a height: 300 Invalid input Enter a height: 10 Invalid input Enter a height: 200 Enter a height: good Invalid input Enter a height: 180 Enter a height: 165 Enter a height: done Max: 200.0 Min: 165.0 Average: 181.67Print "Censored" if userInput contains the word "darn", else print userInput. End with newline. Ex: If userInput is "That darn cat.", then output is: Censored Ex: If userInput is "Dang, that was scary!", then output is: Dang, that was scary! Note: If the submitted code has an out-of-range access, the system will stop running the code after a few seconds, and report "Program end never reached." The system doesn't print the test case that caused the reported message. #include <iostream>#include <string>using namespace std; int main() {string userInput; getline(cin, userInput); /* Your solution goes here */ return 0;} Please help me with this problem using c++.
- Print "Censored" if userInput contains the word "darn", else print userInput. End with newline. Ex: If userInput is "That darn cat.", then output is:Censored Ex: If userInput is "Dang, that was scary!", then output is:Dang, that was scary! Note: If the submitted code has an out-of-range access, the system will stop running the code after a few seconds, and report "Program end never reached." The system doesn't print the test case that caused the reported message.Create a program that outputs the average of three input numbers. Let the values of the three input numbers be, 10, 20 and 45. The expected screen output is, Please help how to fix this issue?Question 4. Write a Program to check any number is SPY number or not ?HINT: A spy number is a number where the sum of its digits equals the product of its digits. For example:1124 is a spy number, because the sum of itsdigits is 1 + 1 + 2 + 4 = 8 andthe product of its digits is 1 * 1 * 2 * 4 = 8 is equal.Difficulty Level : EasySample Input: 2114 Output: Given number is spy numberDM your c.
- This is a segment of program, when it executed with multiple values for n and s the program displays the value of f, choose which output of f values are wrong answersWrite a program that reads a person’s name in the following format: first name, then middle name or initial, and then last name. The program then outputs the name in the following format:last name, first name. middle initial.For example the inputMary Average User should produce the outputUser, Mary A.Your program should work the same and place a full stop after the middle initial even if the input did not contain a full stop. Your program should allow for users who give no middle name or initial. In that case, the output of courses contains no middle name or initial. For example, the inputMary User should produce the outputUser, MaryYour program should also accept names in lowercase, uppercase or a mix of lowercase and uppercase, and display that in the correct format, e.g. if the input ismArY average USERshould produce the outputUser, Mary A.Use C-strings and assume that each name is at most 20 characters long.Hint: it may be easier to use 3 C-strings.Write a program that reads in two numbers typed on the keyboard and dividesthe first number by the second number. The program should output the dividend,divisor, quotient, and remainder on the screen.

