Create a ctass with a statie main that tests the ability to resolve and prist a Path: • Create an instance of a Filesystem elass, • Resolve an Instance of a Path interface from a directory path and filename. • Print the constructed Path with System.out.printn method.
Q: Write a shell script to input two numbers as command line arguments. If the first number is minimum,…
A: Lets consider my current working directory is /home/sdpteam/Documents/Test Following is structure…
Q: Suppose the current denial state of a file in NFS is WRITE. Is it possible that another client can…
A:
Q: you delete a file by accident and then later decide that you want it back, what teps should you…
A: Answer is given below-
Q: XCOPY, like CACLS, has been deprecated, so we should avoid using it in a batch file. Group of answer…
A: Please find the answer in the next step:
Q: Hard links must be on the same filesystem as the destination, but symbolic links may be on any…
A: A symbolic connection (likewise symlink or delicate connection) is a word utilized in figuring to…
Q: السؤال to format a partition 1 of disk 2 we use the command الاجابات mkfs –t vfat /dev/sdb2 mkfs…
A: Correct Answer: mkfs -t vfat /dev/sdb1
Q: Python 3.8.5 Shell File Edit Shell Debug Options Window Help Python 3.8.5 (tags/v3.8.5:580fbb0, Jul…
A: In This Program You are importing a package with is Not installed. Firstly Run Command on the Shell…
Q: Suppose the file nums.txt contains the following data: 15 9 -11 22 -7 -18 21 20 -19 12 Suppose…
A: This program read the line of data from the file nums.txt which contain the following data : 15…
Q: In UNIX-based operating systems, opening a file using a file handle can be done only in the kernel.…
A: Please check the solution below
Q: Code a hbs file named fruits.hbs that utilizes Handlebars placeholders and Handlebars helpers to…
A: fruits.hbs <!-- HANDLEBARS FRUITS TEMPLATE --> <h1>Fruits</h1> <!-- CREATING A…
Q: I WANT A CODE IN C++. PLEASE DO NOT COPY AND PASTE FROM THE ALREADY PRESENT AWNSER!!! i have…
A: PROGRAM CODE: #include <stdio.h> #include <unistd.h> #include <string.h>…
Q: Create an Access Matrix for the following scenario based on the Protection Mechanism in an Operating…
A: d:/project/A.ppt Bushral exam.class Quiz.txt DVD Ali read, write Bushra switch…
Q: using java: Write a Server-Client application hosting several methods on the Server-side while the…
A: Solution :: Below find the solution for part 1 !! //Server.java import java.net.*; import…
Q: Help with Python coding issue The Linux operating system is a very popular server OS. A network…
A: the answer is given below:-
Q: Suppose that only file descriptors 1 (stdout), 3 (a read connection from filel ) and 4 (a write…
A: dup(): The dup() system call duplicates an open file descriptor and returns the new file descriptor.…
Q: With DISKPART, we must first select a disk/partition/volume before we can work on the selected…
A: The select command is used to select the disk or the volume. After writing the command diskpart,…
Q: A program holds a mandatory write lock on an entire file, but a user is still able to edit that…
A: Mandatory locking? Mandatory locking is kernel enforced file locking, as opposed to the…
Q: How we can check execution permission of users for all the directories listed in a path using c…
A: Use the command line with the -la arguments to see the permissions for all files in a directory.…
Q: setAttribute(PDO::ATTR_ERRMODE, PDO::ERRMODE_EXCEPTION);} ?> Assume a user has logged in…
A: Shopping cart is an online shopping site where the customer buy an item and add them into cart to…
Q: Write a shell script to input two numbers. If the first number is maximum, display all the files in…
A: Code: echo "Enter number1: "read n1echo "Enter number2: "read n2if [ $n1 == $n2 ]then echo…
Q: When a child exits is returns a number in response to the parents having called wait(&status). If…
A: Below i have answered:
Q: Is each of the following an absolute pathname, a relative pathname, or a simple filename?
A: Multiple questions are asked so the first question will be answered. Please upload another question…
Q: How to write a rule in YARA that iterates over sections in a PE file? In this rule I need to confirm…
A: It is easy to write and understand YARA rules since they have a syntax similar to C. This is the…
Q: Are these system specifications consistent? “If the filesystem is not locked, then new messages will…
A: By reading it you can totally figure out that its a Discreet Mathematics question. and we can…
Q: Q4. Develop a shell-script that reads the name of a file from user and prints out if such file…
A: #!/bin/sh#Using -d option we are checking whether the first argument is a directory or not.#$1…
Q: Simply redirecting nothing into a log file will clear it. Is this statement true or false?
A: To be determine: Simply redirecting nothing into a log file will clear it. Is this statement true or…
Q: Is each of the following an absolute pathname, a relative pathname or a simple file name?a.…
A: Absolute path specifies the location of a directory or file from the root directory including a…
Q: ld -melf_i386 question.o -o answer ./answer here question is code file name and answer is
A: The coding is given as,
Q: allow just a portion of a file to be resent are session layer check points? Why?
A: Given that: allow just a portion of a file to be resent are session layer check points? Why?
Q: The file phonenumbers.txt is in the phone directory (a subdirectory of the /contacts directory).…
A: The "phone directory" is the "phone number directory". The directory has several subdirectories…
Q: You have an integer file descriptor correponding to an already open I/O channel on the operating…
A: Solution:-A file descriptor is different than a normal open file in that it is simply an integer…
Q: Modify rnfile such that it will keep a copy of the old existing file (if available) before the…
A: Given: Modify rnfile such that it will keep a copy of the old existing file (if available) before…
Q: A fictitious command madeup reads lines of input from the console until the end-of-file (EOF)…
A: Question:
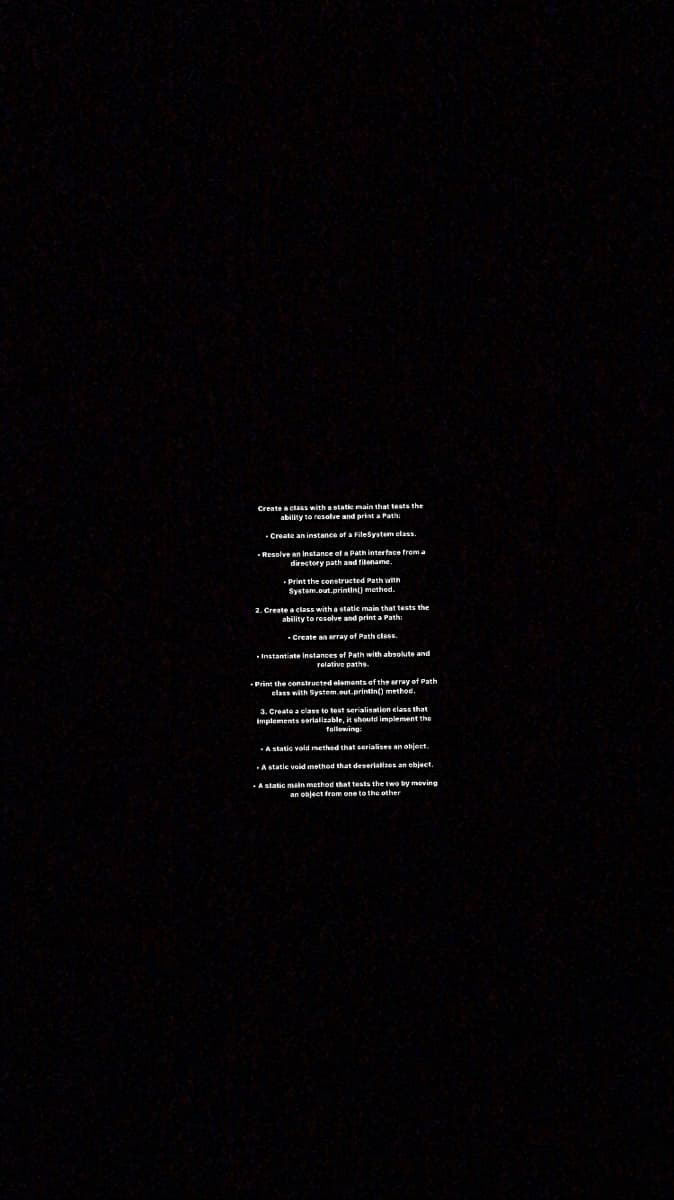
Q: Create a class with a static main that tests the ability to resolve and print a Path: • Create an…
A: Sorry for the inconvenience as for our rules we can answer only one question at a time please post…
Q: Write a set of commands (they should be piped) can find only all link files in the entire file…
A: Task : Write the command that finds all the files whose names start with the xyz.
Q: FAT32 provides the capability to assign access rights to a file and directory a. True b. False
A: FAT32 (File Allocation Table):
Q: Suppose a file is on a filesystem using a 1K block size. This file is maintained on the disk using…
A: Below i have answered:
Q: Is with no command-line options The 1s command prints all files/directories in the current working…
A: The ls command is one of the many Linux commands that allow a user to list files or directories from…
Q: The ReadableByteChannel instance allows us to read from the Buffers in Datagram Socket using its…
A: The answer is...
Q: Q-2: Write a shell script which can read all the lines from a file, and this should able to delete…
A: use vi bash.sh echo enter filename read f awk ‘NR % 2 == 0’ $f
Q: find The find command takes a pattern as a command-line argument and recur- sively searches through…
A: The find command in UNIX is a command line utility for walking a file hierarchy. It can be used to…
Q: If two links to an existing file are created in the same directory as the original (using the link…
A: If two links to an existing file are created in the same directory as the original how many inodes…
Q: UNIX, how would you remove the directory test and all files and subdirectories (recursively) in it?…
A: Here have to determine correct option for removing directory.
Q: Write a shell script that contains a hashpling and comments. It should perform thefollowing tasks:a.…
A: The hashpling starts with “#!” to tell the program loader the following line is hashpling. The…
Q: cd /bin/user/directory/abc is an example of relative pathname. True or false.
A: Q. cd /bin/user/directory/abc is an example of relative pathname. True or false.
Q: Give the line(s) of code required to create a scanner object that will read text from a file called…
A: There are several ways to read a file in java.We can use Scanner, FileReader, FileInputStream and…
Q: ain the file permission method in the Linux syst
A: Explain the file permission method in the Linux systems with suitable example.
Step by step
Solved in 3 steps with 1 images

- Which example uses the SOLID SRP principle correctly and does not violate it? (A or B) A. public class DatabaseParser { ParseDirectoryMapFile(); // parse directory map fileParsePasswordFile(); // parse user fileParseReviewDataFile(); // parse review data fileParseTeamFile(); // parse team CalculateGrade(); CalulateRelativeGrade(); } B public class DatabaseParser { ParseDirectoryMapFile(); // parse directory map fileParsePasswordFile(); // parse user fileParseReviewDataFile(); // parse review data fileParseTeamFile(); // parse team file} // seperately with the following: public class Calculator{ CalculateGrade(); CalulateRelativeGrade(); }Rewrite the program in Example 3-1. DigestThread class to output the result of each file on an output file for each one by assigning a new name for the output file. The language is Java Example 3-1. DigestThread import java.io.*; import java.security.*; import javax.xml.bind.*; // for DatatypeConverter; requires Java 6 or JAXB 1.0 public class DigestThread extends Thread { private String filename; public DigestThread(String filename) { this.filename = filename; } @Override public void run() { 56 | Chapter 3: Threads www.it-ebooks.info try { FileInputStream in = new FileInputStream(filename); MessageDigest sha = MessageDigest.getInstance("SHA-256"); DigestInputStream din = new DigestInputStream(in, sha); while (din.read() != -1) ; din.close(); byte[] digest = sha.digest(); StringBuilder result = new StringBuilder(filename); result.append(": "); result.append(DatatypeConverter.printHexBinary(digest)); System.out.println(result); } catch (IOException ex) {…1) Create a daemon in C in the Unix environment, your daemon must create a text file called aitDaemonLog.txt and populate it with 1000 lines of a string each line must be written after 10 seconds, the string must end with the count of the string;. 2)Create a shell script that lists all the files in the present working directory in long format name this file listMyFiles.sh. Write a c program that uses the system() function and uses it to run listMyFiles.sh 3)Write a c program to write a string of your own choosing into shared memory then read the contents of the shared memory created in 4)demonstrate in a c program how to use a fork to create a child process, using pipes let this child process send a message which is read by the parent process 5) Write a c program that shows the PID, PPID, UID and GID of a running process, let this process fork thus creating a child process, let the parent process count from 0 to 50 and the child process from 0 to 25 each process showing while counting…
- Modify rnfile such that it will keep a copy of the old existing file (if available) before the renaming operating. Assume that apple.txt will be renamed as orange.txt. When the command “./rnfile apple.txt orange.txt” is executed, the script will first check whether orange.txt exists under the given path or not. If the file exists then orange.txt will be renamed as orange.txt_old before renaming apple.txt as orange.txt. Make rnfile an executable shell script; try to rename a file to a filename that already exists. Show your shell program and its output to the instructor.Question 5: findWrite a simple version of the Linux find program: find all the files in a directory tree whose namematches a string.Some hints:·Look at ls.c to see how to read directories.·Don’t try to find any files in the “.” and “..” directories.·Changes to the file system persist across runs of QEMU; to get a clean file system run makeqemu.Your solution is correct if produces the following output (when the file system contains a file a/b):$ make qemu ...init: starting sh$ echo > b$ mkdir a$ echo > a/b$ find . b./b./a/b$2. Start with an empty buffer pool of size 4 pages again. This time use this access pattern:♯SAGLIKLIMUTLUBAYRAMLAR♯. At the end of accessing all the pattern, what is the content ofthe buffer pool (write in alphabetical order)? Use the LRU algorithm as the buffer replacementpolicy.
- How can I fix the error and complete my code? In Java. LeagueDriver.java: import java.io.File;import java.io.FileNotFoundException;import java.util.Scanner; public class LeagueDriver {public static void main(String[] args) {Scanner sc = null;try {sc = new Scanner(new File("Players.txt"));} catch (FileNotFoundException e) {System.err.println("No such file");System.exit(-1);} League l = new League();while(sc.hasNext()) {String temp[] = sc.nextLine().split(", ");l.addPlayer(new Player(temp[0],temp[1],Integer.parseInt(temp[2])));}l.printLeague();System.out.println();l.printAverageScore();}} Player.java: public class Player {private String name,team;private int score;public Player(String n,String t,int s) {setName(n);setTeam(t);setScore(s);}/*** @return the name*/public String getName() {return name;}/*** @param name the name to set*/public void setName(String name) {this.name = name;}/*** @return the team*/public String getTeam() {return team;}/*** @param team the team to set*/public void…Java Program ASAP ************This program must work in hypergrade and pass all the test cases.********** I have provided the code instructions and the text files below. The test cases are located in Hypergrade. Down below is a working code. Dont add any import libraries in the program just modify the rest of the code so it passes the test cases. import java.io.BufferedReader;import java.io.FileReader;import java.io.IOException;import java.util.HashMap;import java.util.Map;import java.util.Scanner;public class MorseCodeConverter { public static void main(String[] args) { Map<String, String> morseCodeMap = readMorseCodeTable("morse.txt"); Scanner scanner = new Scanner(System.in); System.out.print("Please enter the file name or type QUIT to exit:\n"); do{ String fileName = scanner.nextLine().trim(); if (fileName.equalsIgnoreCase("QUIT")) { break; } try { String…Close the virtual machines now and close the virtual box. Use your real machine to respond to the following : Use notepad to create a txt file containing the following : hello how are you 1234567890!? compute the MD5 hash of this file. Write the hash here …........................................................................................................... what is the size output of MD5 ? …........................................................................... what would be the MD5 size output if you change the input file to be: ello how are you 1234567890!? ….............................................................................. give also the MD5 output of this modified file …..................................................................................... I have changed the last symbol in step 1 (which is the symbol “?”) by a mystery symbol that you need to figure it out. I have only used numbers symbols. What is this mystery symbol if I…
- Compliant/Noncompliant Solutions The following code segment was provided in Secure Coding Guidelines for Java SE: void readData() throws IOException{ BufferedReader br = new BufferedReader(new InputStreamReader( new FileInputStream("file"))); // Read from the file String data = br.readLine();} The code is presented as a noncompliant coding example. For this assignment, identify two compliant solutions that can be utilized to ensure the protection of sensitive data. Provide a detailed explanation of factors, which influence noncompliant code and specifically how your solutions are now compliant. Your explanation should be 2-3 pages in length. Submit the following components: Word document with appropriate program analysis for your compliant solutions and source code in the Word file. Submit your .java source code file(s). If more than 1 file, submit a zip file.enlarge.py """ File: enlarge.py Project 7.11 Defines and tests a function to enlarge an image. """ from images import Image def enlarge(image, factor): """Builds and returns a copy of the image which is larger by the factor.""" def block_copy_pixel_to(image, row_index, line, pixel_to_copy, factor): for x in range(factor): for y in range(factor): image.setPixel(row_index + x, line + y, pixel_to_copy) old_height = image.getHeight() old_width = image.getWidth() new_height = old_height * factor new_width = old_width * factor new_image = Image(new_width, new_height) nhi = 0 # new height index for ohi in range(old_height): # original image height index # new left & right indices nli = 0 nri = new_width - 1 # original left & right indices oli = 0 ori = old_width - 1 # Copy blocks of the same pixel to the new image while oli < ori: old_left_pixel = image.getPixel(oli, ohi) block_copy_pixel_to(new_image, nli, nhi, old_left_pixel, factor) old_right_pixel =…AVA PROGRAM ASAP Please modify this program ASAP BECAUSE it does not pass all the test caseswhen I upload it to hypergrade. Its says 0 out of 3 passed when i upload it to hypergrade. The program must pass the test case when uploaded to Hypergrade. import java.util.HashMap;import java.io.BufferedReader;import java.io.FileReader;import java.io.IOException;import java.util.Scanner;public class MorseCodeConverter { private static HashMap<Character, String> morseMap = new HashMap<>(); public static void main(String[] args) { loadMorseCodes(); Scanner scanner = new Scanner(System.in); System.out.println("Please enter a string to convert to Morse code:"); String input = scanner.nextLine().toUpperCase(); String morseCode = convertToMorse(input); System.out.println(morseCode); } private static void loadMorseCodes() { try (BufferedReader reader = new BufferedReader(new FileReader("morse.txt"))) { String line;…

