Create a flowchart of the following C program.
Q: Use the following representation methods to convert the decimal number 30 to an 8-bit binary number:…
A: Given: The most straightforward method is to convert it to hex first. 7210 = 4816 = 10010002 since…
Q: What safeguards should a business use to prevent hackers from gaining access to customer…
A: Answer : Most important to use in every business is Firewall , every organization should have 5-6…
Q: What exactly is assembly language?
A: Introduction: An assembly language is a low-level programming language that can be used to directly…
Q: Computer science What is network protocol? Explain the following network protocols (in your own…
A: Introduction: A network protocol is a predefined set of rules that govern how data is delivered…
Q: Why is the public-key method of encryption so crucial in internet commerce?
A: IN ELECTRONIC COMMERCE, ENCRYPTION THAT USES THE PUBLIC KEY METHOD IS VERY IMPORTANT : For…
Q: Explain how the onion routing technique can help to improve communication anonymity.
A: Onion routing: Onion routing is a technique for anonymous communication over a computer network. In…
Q: how cybercrime manifests itself in several ways Is there a possibility to stop cybercrime via the…
A: Introduction: Many privacy issues develop when sensitive information is intercepted or disseminated…
Q: NAME and EXPLAIN in DETAIL the six (6) roles performed by the TCP?
A: TCP: Networking your computers improves their capacity to communicate, and most computers are used…
Q: The next section will discuss the distinctions between the two kinds of data flow charts. Without…
A: Introduction: A data flow diagram (DFD) displays the flow of data through a process or system.
Q: No such port Your uncle has given you a new computer monitor. When you try to connect it, none of…
A: Introduction
Q: What makes Chrome Os computers utilize less internal storage than competing desktop operating…
A: It's a non-Windows operating system for PCs. Linux is available in a variety of flavors, known as…
Q: Please design an algorithm to detect the fake coin
A: => Fake coin problem, we have N number of coins all of equal weight, out of them, one is fake and…
Q: Please explain how computers have grown so prevalent in the educational system over the previous…
A: This is because computers are so advanced. Please explain how computers have grown so prevalent in…
Q: Is the XDR capable of providing functionality in the Application Layer?
A: XDR: Extended Detection and Response (XDR) is a "SaaS-based, vendor-specific security threat…
Q: Should an essay be done on the importance of networking in information technology?
A: Answer: Importance of networking in information technology: In the world of Information Technology…
Q: "Beware of sites that contain bias or do not admit its bias freely" is related to which of the…
A: c. Objectivity
Q: What are the primary distinctions between a local-area network and a wide-area network when it comes…
A: Introduction: LAN A local area network (LAN) is a collection of computers and peripheral devices…
Q: Create a 6 by 8 array of random integer numbers ranged from -35 to 70, - Find how many -ve numbers…
A: C++ Program #include <iostream>#include <stdio.h>#include <stdlib.h>#include…
Q: Discuss and explain new cloud computing technologies that promote scalability and why they are…
A: Introduction Cloud Computing: Customers can use cloud computing to obtain comparable programmes…
Q: A. Convert the binary number 1010101101001.1110 to hexadecimal. B. Determine the power set of the…
A: Below is the answer to above question. I hope this will be helpful for you...
Q: Do you agree that using threading for loops will speed up execution time if we use loops?
A: Threading allows concurrent execution.
Q: How could an arbitrary value be multiplied by 40 without utilising a multiplication instruction?
A: The first thing that comes to mind is the successive addition of that number 40 time. Just use the…
Q: How can we identify a local-area network from a wide-area network based on the structure of a…
A: Answer:- key differences between a local-area network and a wide-area network are mentioned below.…
Q: what are the last two letters ( pronunciation of ed) of these verbs in the box.( hoped, missed ,…
A: Among the words - hoped, missed, laughed, begged, robbed, smelled, ended, presented
Q: Provide a complete examination of this network adapter's operation.
A: Introduction: Actually, given question regarding network adapter. This network adapter system…
Q: r) copy had an
A: In a database, replication alludes to the act of duplicating data from a solitary database to…
Q: The critical contrast between business intelligence and analytics is what distinguishes the two.
A: Introduction: The issues that business intelligence and business analytics are designed to answer…
Q: This is because computers are so advanced. Please explain how computers have grown so prevalent in…
A: Computers: Computers(Pc) have come a long way in the decades since they were first invented. Many…
Q: Why is the public-key method of encryption so crucial in internet commerce?
A: Public-Key: A public key is a huge numerical number used to encrypt data in cryptography. A software…
Q: Name Posiion Rate Hours Worked Total Deductions Gross Pay Net Pay ---- Albert Einstein Manager Sales…
A: // Code #include<stdio.h>#include <stdlib.h>typedef struct memeber{ char eName[100];…
Q: In multilevel inheritance one class inherits More than one class O Only one class O As many classes…
A: In the inheritance, one class can inherit the properties of other class. There are different types…
Q: choose the correct verb from the following sentences Susie ( watched / was watching ) a film when…
A: Here, we are asked the correct verb for the given sentences. I have provided the correct verb in…
Q: Do database designers need to be aware of any specific technique that, when used in certain…
A: Introduction: As certain that the system has the ability to expand in tandem with your data:
Q: Will in-house systems analysts become obsolete as more organizations outsource system development?…
A: Outsourcing is providing your organization's information to an external resource in order to fulfill…
Q: The information revolution is centered on T. However, the function and impact of IT might be…
A:
Q: administr
A: Data system is a term used to allude to an organized assortment of symbols and cycles that may be…
Q: The design of a distributed database is influenced by the differences between a local area network…
A: Local area network: A LAN, or local area network, is a network that spans a limited geographic…
Q: fraud in computers: kinds and outcomes What can be done to stop cybercrime?
A:
Q: An essay about the importance of networking to the development of information technology?
A: Employees to share ideas more easily and work more efficiently: It not only helps you locate new…
Q: Which one of the following is FALSE for architecture design?
A: which one of the following is false for architechture design?
Q: 2. Convert the following English statements into FOPL (i) Every apple is either green or yellow…
A: The FOPL fot the above questions are solved in step 2:-
Q: Trying to figure out what makes computers so powerful. On average, which four features of today's…
A: The following are the key qualities of today's computer that are most noticeable in the educational…
Q: What distinguishes PHP-powered websites from those built using HTML, CSS, and JavaScript?
A: Introduction: PHP(Hypertext preprocessor) is a server-side scripting language i.e. used for web…
Q: In the context of computer language design, define orthogonality.
A: Introduction: The attribute orthogonality means that "changing X does not impact Y."
Q: th-bit longitudinal parity is determined; the s is calculated and kept for all Oth bits, a second…
A: A parity bit, or actually take a look at bit, is a piece added to a line of binary code. Parity bits…
Q: In multilevel inheritance one class inherits More than one class O Only one class O As many classes…
A: Inheritance: The mechanism in which one class inherits the property of other class is called as…
Q: Define information security governance and propose five principles for successful information…
A: Disclaimer: “Since you have asked multiple question, we will solve the first question for you. If…
Q: This is because computers are so advanced. Please explain how computers have grown so prevalent in…
A: Computer advancement has a significant impact on schooling and it is a part of the school curriculum…
Q: Why should we care about the information management and technology aspects of our information…
A: Information management and technology plays very important role in maintaining a information system.
Q: Why should the enhanced assignment operator functions return a reference?
A: Introduction: If you return a reference, you've completed the most of the task.The values of one…
Create a flowchart of the following C
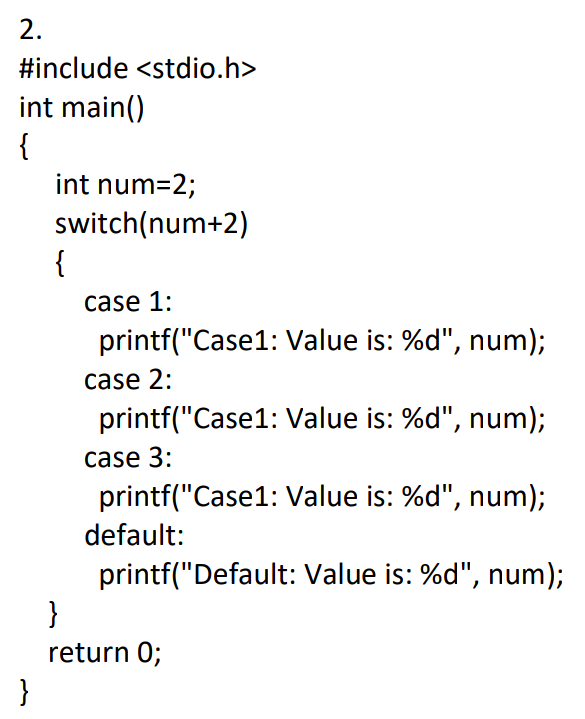
Step by step
Solved in 2 steps with 1 images

- Problem Description: The international standard letter/number mapping found on the telephone keypad is shown below: Write a pseudocode and program that reads a letter and displays its corresponding digit. 2 3 1 ABC DEF 4 5 6 GHI JKL MNO 7 8 9 PQRS TUV WXYZ 0 Write a pseudocode on how you would solve the problem in your own word. Write a java program called Phone considering the following directions. Practice here first then write answer on the answer sheet. Also, make sure distinguish high and low caps as Java is case – sensitive. Import and declare a Scanner class Ask user for an Upper – case letter Use the switch statement along with case and break Use the System.exit(1) in the default to terminate the program Print the corresponding digitRock, Paper, Scissors Game Create a application using (C#) in Microsoft Visual Studio that lets the user play the game of Rock, Paper, Scissors against the computer. The program should work as follows.1. When the program begins, a random number in the range of 1 through 3 is generated. If the number is 1, then the computer has chosen rock. If the number is 2, then the computer has chosen paper. If the number is 3, then the computer has chosen scissors. (Do not display the computer’s choice yet.)2. The user selects his or her choice of rock, paper, or scissors. To get this input you use clickable PictureBox controls displaying some of the artwork that you will find in the student sample files.3. The computer’s choice is displayed.4. A winner is selected according to the following rules: •If one player chooses rock and the other player chooses scissors, then rock wins. (Rock smashes scissors.)•If one player chooses scissors and the other player chooses paper, then scissors wins.…Assignment Description This program will simulate part of the game of Yahtzee! This is a dice game that involves rolling five dice and scoring points based on what show up on those five dice. The players would record their scores on a score card, and then total them up, and the player with the larger total wins the game. A Yahtzee score card has two portions: The upper portion has spaces for six scores, obtained by adding up all of the 1's, 2's, 3's, etc. The lower portion has special scores for various combinations: Three of a kind -- at least 3 dice are the same number;the score is the sum of all five dice Four of a kind -- at least 4 dice are the same number;the score is the sum of all five dice Small straight -- four consecutive numbers are represented, e.g. 2345;the score is 25 points Large straight -- five consecutive numbers are represented, e.g. 23456;the score is 30 points Full House -- three of one kind, two of another; the score is 30 points Yahtzee! -- five of a kind; the…
- Following code in C using random Name Reg no and highschool name Use switch case in C language to do the following: Create a restaurant with the name “Your Name - Reg_No – Name of your highschool” The restaurant should come with the options of delivery and take away and the choice should be displayed as “Delivery – Registration No” and “Takeaway – Name” Each option should have the same menu and an extra 15% charge be included if a customer wants home delivery Both menus should have two items that are customizable, such as a burger can have chillies removed, cheese added and extra mayonnaise. The user should have the option of choosing multiple items with multiple quantity. Print a bill in the end.Computer Fundamentals and Programming 2 Write a program that determines a student’s grade. The program will accept 3 scores and computes the average score. Determine the grade based on the following rules: - If the average score is equal or greater than 90, the grade is A. - If the average score is greater than or equal to 70 and less than 90, the grade is B. - If the average score is greater than or equal to 50 and less than 70, the grade is C. - If the average score is less than 50, the grade is F. Source Codes and Print Screen of the OutputUsing C# in Microsoft Visual Studio create an application that lets the user play the game of Rock, Paper, Scissors against the computer. The program should work as follows:1. When the program begins, a random number in the range of 1 through 3 is generated. If the number is 1, then the computer has chosen rock. If the number is2, then the computer has chosen paper. If the number is 3, then the computer has chosen scissors. (Do not display the computer’s choice yet.)2. The user selects his or her choice of rock, paper, or scissors. To get this input you can use Button controls, or clickable PictureBox controls displaying some of the artwork that you will find in the student sample files.3. The computer’s choice is displayed.4. A winner is selected according to the following rules:• If one player chooses rock and the other player chooses scissors, then rock wins. (Rock smashes scissors.)• If one player chooses scissors and the other player chooses paper, then scissors wins. (Scissors…
- Change the calendar printing program so it starts the week on a Sunday. Also make it print a newline at the end (but only one). This program had to utilize the code from page 61 and make the necessary changes for printing it. The code itself would display the calendar and you would not have to use the println function as you would have to do that for every single month and year. The program would grab the month a year you selected and display it. import java.time.DayOfWeek;import java.time.LocalDate; public class Calendar { public static void main(String[] args) {// TODO Auto-generated method stubint month = 0;int year = 0;LocalDate date= LocalDate.of(year, month, 1);while (date.getMonthValue() == month) {System.out.print(date.getDayOfMonth());date = date.plusDays(1);}DayOfWeek weekday = date.getDayOfWeek();int value = weekday.getValue();for (int i = 1; i<value; i++);System.out.print(" ");int value1 = date.getDayOfWeek().getValue(); import calendar;y = int(input("Input the years…Order check Write a program OrderCheck.java that takes four int command-line arguments w, x, y, and z. Define a boolean variable whose value is true if the four values are either in strictly ascending order (w < x < y < z) or strictly descending order (w > x > y > z), and false otherwise. Then, display the boolean variable value.Note: The code is written you can just tell the explanation what is happening in the code Explain in English.Just explain the whole code. #include <iostream>using namespace std;class PrimeNumberGenerator{private:int counter;public://ConstructorPrimeNumberGenerator() : counter(0){}//Function to reset countervoid reset(){counter = 0;}int getCounter(){return counter;}//Function to return next prime number after currentPrimeint getNextPrime(){if(counter == 0){counter = 2;}else{for(int i = counter + 1; ; i++){if(isPrime(i)){counter = i;break;}}}return counter;} //Function to check if a number is prime or notbool isPrime(int num){for(int i = 2; i <= num/2; i++){if(num % i == 0)return false;}return true;}}; int main() {int option;PrimeNumberGenerator gen;cout << "Enter 1 if you want to reset\n";cout << "Enter 2 if you want to get next prime number\n";cout << "Enter -1 to quit: ";cin >> option;while(option != -1){if(option == 1){gen.reset();cout <<…
- C++ Visual 2019 A particular talent competition has five judges, each of whom awards a score between 0 and 10 to each performer. Fractional scores, such as 8.3, are allowed. A performer's final score is determined by dropping the highest and lowest score received, then averaging the three remaining scores. Write a program that uses this method to calculate a contestant's score. It should include the following functions: void getJudgeData() should ask the user for a judge's score, store it in a reference parameter variable, and validate it. This function should be called by main once for each of the five judges. void calcScore() should calculate and display the average of the three scores that remain after dropping the highest and lowest scores the performer received. This function should be called just once by main and should be passed the five scores. The last two functions, described below, should be called by calcScore, which uses the returned information to determine which of the…HangmanAA.java For this program, you will create the game Hangman. (If you are unsure of how to play Hangman, Google it.) The game will start by asking player 1 for a word or phrase (can be multiple words). Then player 1 will be asked how many missed guesses are allowed by player 2. Once this information is received, player 2 will take over. (Have the program print many blank lines of space so that player 2 can’t see what player 1 entered.) The instructions should be displayed for player 2 as well as the number of misses they’re allowed to make before they lose the game. The screen should also output dashes or underscores to represent each letter of player 1’s secret word/phrase. Player 2 should guess one letter at a time. Case should not matter. Typing x or X should give the same result. If that letter is present in the mystery phrase, then it should be displayed. (It will replace the dash/underscore in that spot. Spaces, punctuation, and all other non-alphabetic characters should…In C++, a reference variable is a variable type that refers to another variable. Example: “int& maxValRef” declares a reference to a variable of type int.

